Blog
Read the fastest Web3 blog
Search via tags
NFT Marketplace Security: Real-Time On-Chain Protection
Introduction: The Marketplace Is Only as Safe as Its Chain NFT marketplaces handle billions of dollars in digital asset transactions every year. They are not just trading platforms. They are ecosystems where ownership, identity, and value converge on-chain.…
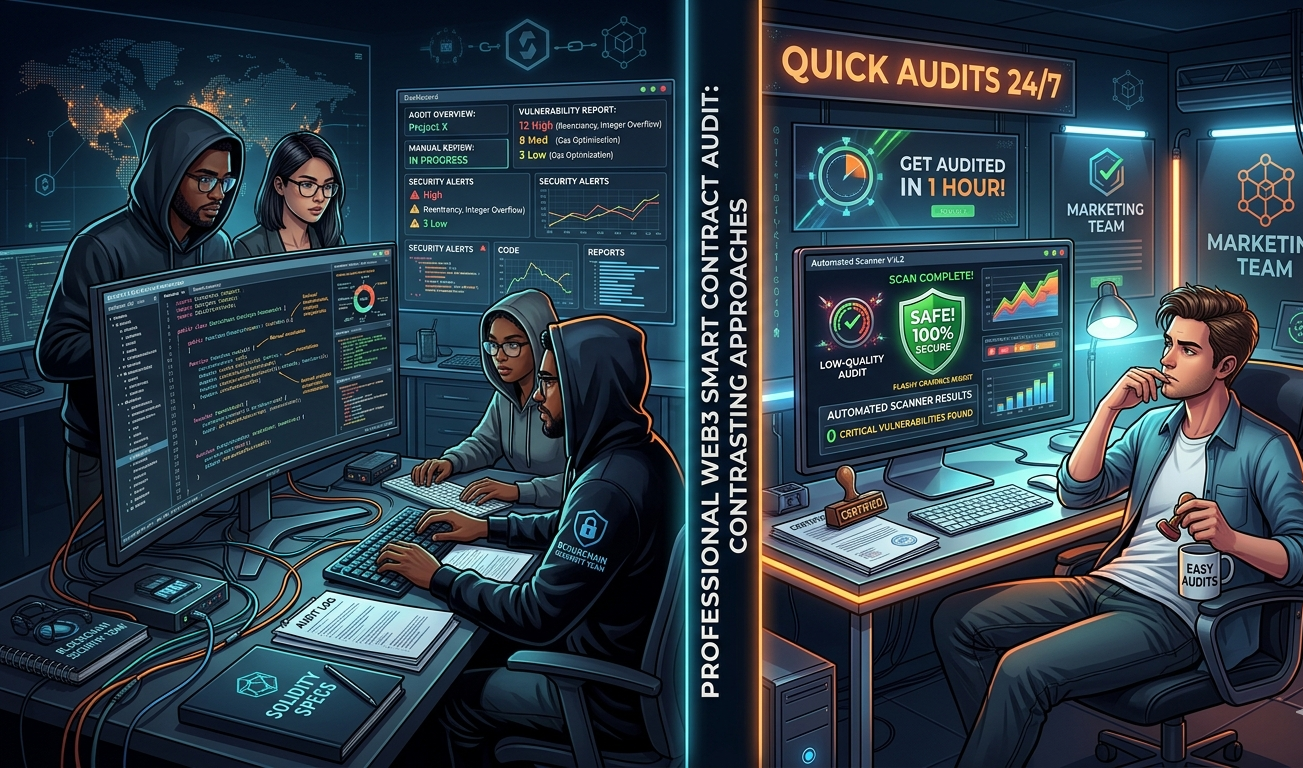
Red Flags to Watch Before Hiring a Smart Contract Auditor
The best time to build smart contract security into your protocol is before you ever engage an audit firm. Solidity Shield from SecureDApp gives development teams continuous automated vulnerability detection throughout the development process, not just at the…
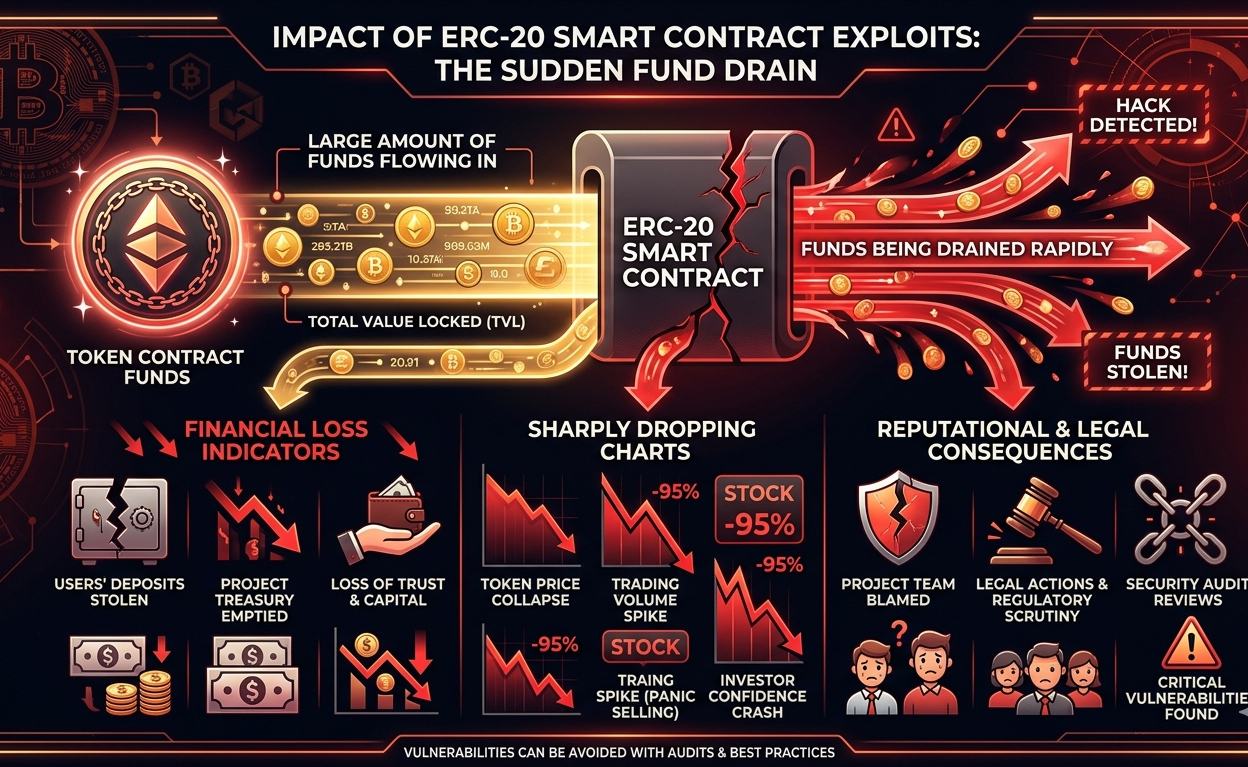
How to Audit ERC-20 Smart Contracts for Security Risks
Auditing ERC-20 smart contracts is not a single step. It is a structured process that combines automated scanning, manual code review, formal verification, and economic analysis. Each layer catches what the others might miss. Together, they form a…
API-Based Real-Time On-Chain Monitoring: Architecture & Setup
Blockchain networks generate thousands of transactions every single minute. Each transaction touches a smart contract, modifies state, or moves assets. If something malicious slips through unnoticed, the damage can be irreversible. This is exactly why real-time blockchain threat…
Token Movement Tracking: Real-Time On-Chain Monitoring Explained
Introduction: When Every Transaction Is a Potential Risk Picture this. It is 2:00 AM in Mumbai. A DeFi protocol sitting on Ethereum holds over $80 million in liquidity. Nobody is watching. A hacker begins silently draining tokens through…
Using Real-Time On-Chain Data for Fraud Prevention in DeFi
Introduction: The DeFi Security Problem No One Wants to Talk About Decentralised finance has unlocked genuine financial freedom for millions. But it has also become one of the most exploited environments in the history of digital assets. In…
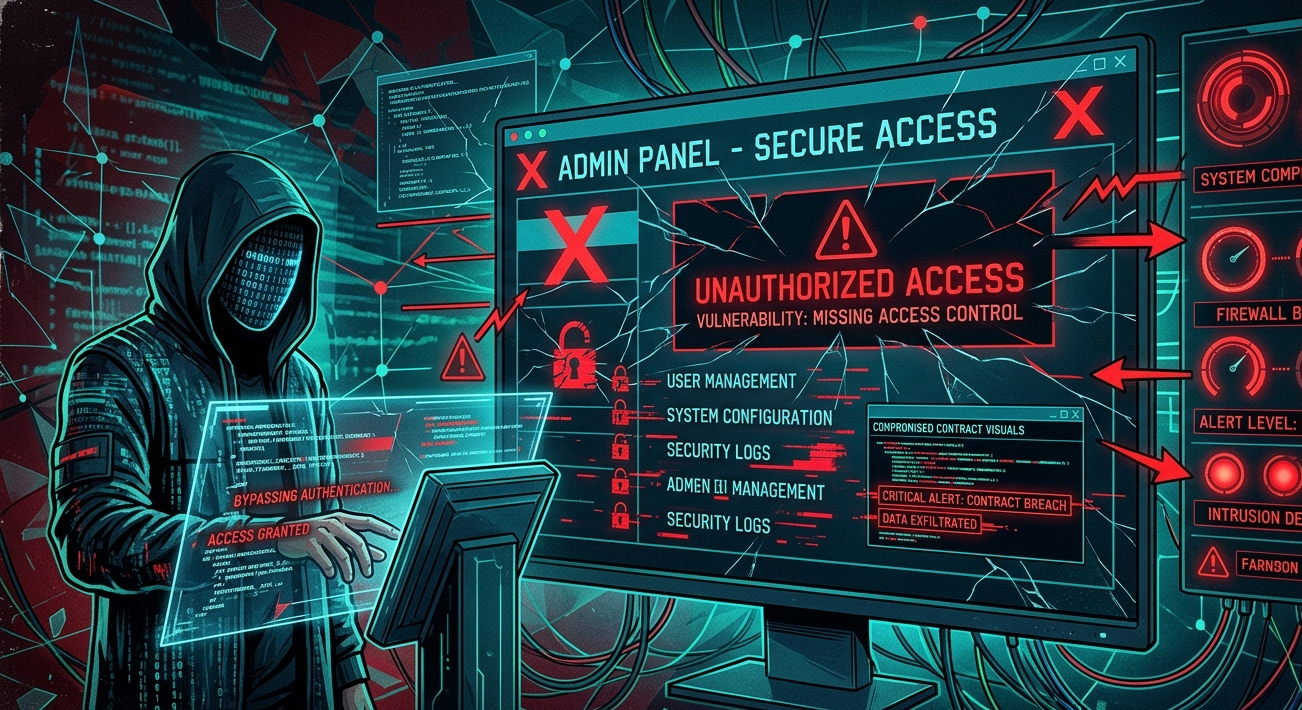
Smart Contract Security: Common Vulnerabilities & Solutions
Smart contracts were built on a simple promise: trustless execution. Once deployed, they run exactly as written, without the need for intermediaries, lawyers, or manual oversight. That promise has powered an entirely new financial ecosystem worth hundreds of…
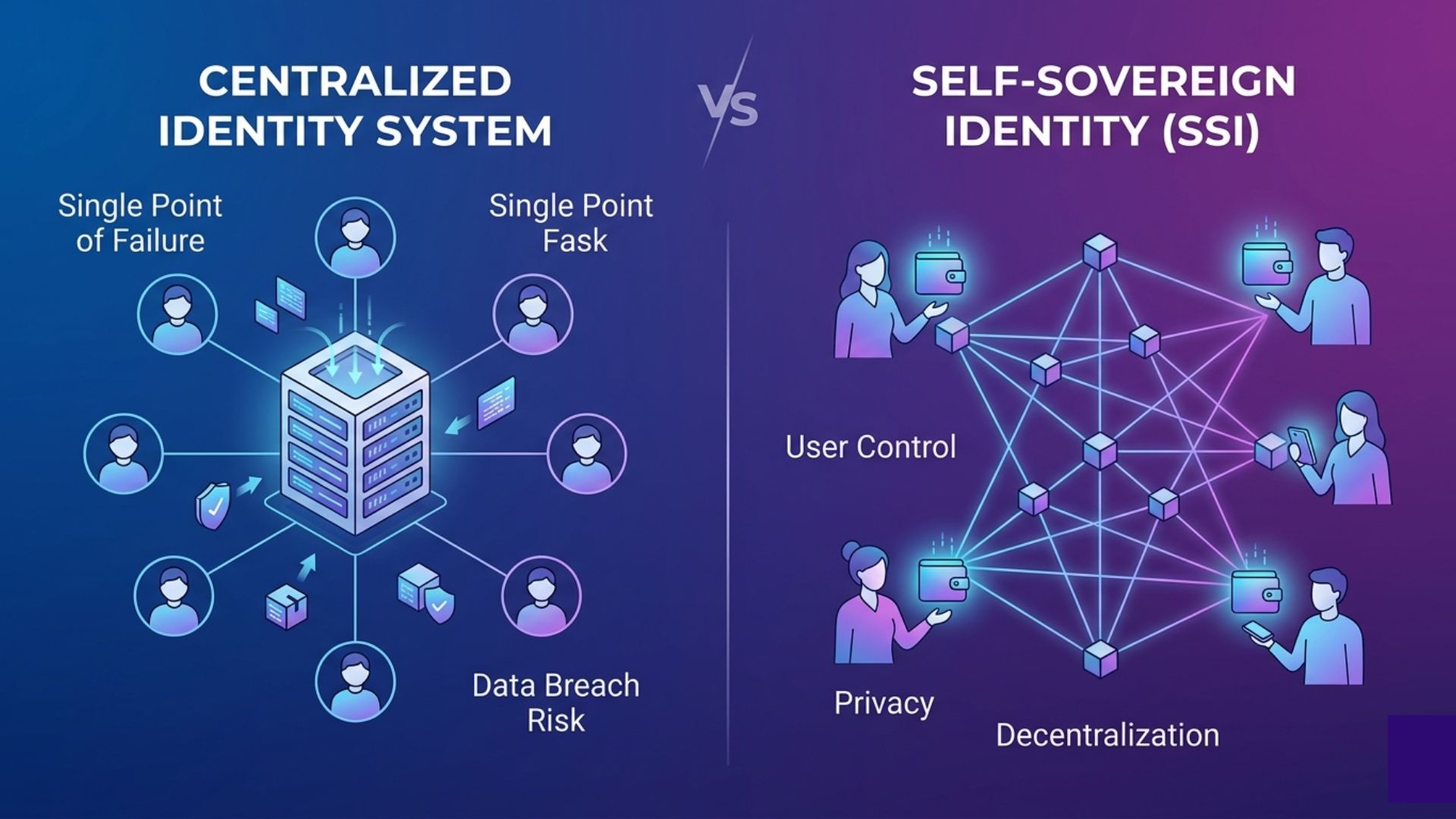
Self-Sovereign Identity: Enterprise Implementation Guide
Self-Sovereign Identity represents a fundamental shift in how enterprises think about digital trust. It moves identity from a centralized service that organizations control to a distributed capability that individuals and entities hold directly. That shift has profound implications…
How to Conduct a Blockchain Forensic Investigation
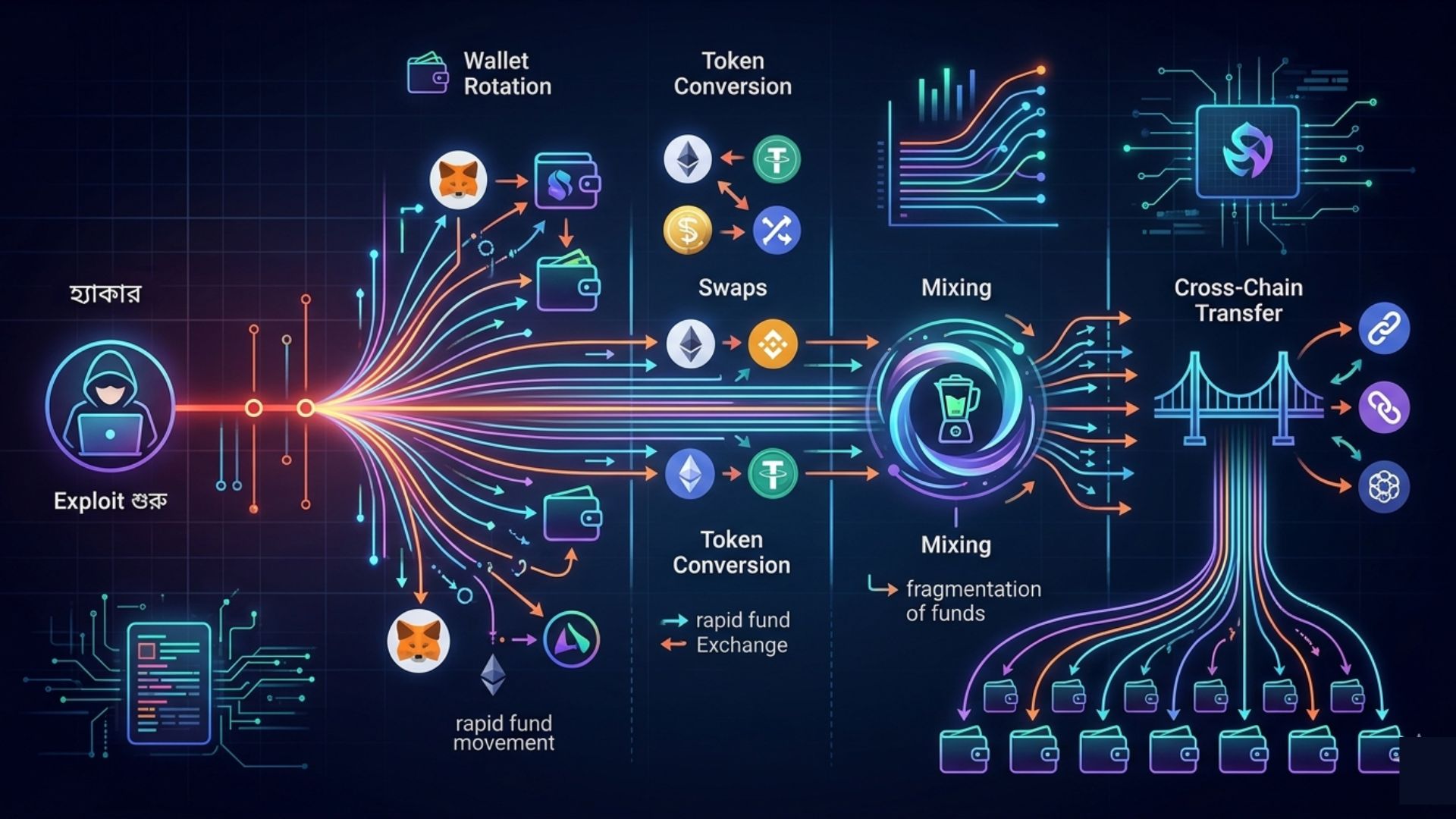
A blockchain forensic investigation is a structured discipline that requires clear methodology, appropriate tooling, and a realistic understanding of what on-chain evidence can and cannot establish in both technical and legal contexts. The teams that achieve the best…
Blog
Read the fastest Web3 blog
Search via category
Blog
Read the fastest Web3 blog
Search via tags
NFT Marketplace Security: Real-Time On-Chain Protection
Introduction: The Marketplace Is Only as Safe as Its Chain NFT marketplaces handle billions of dollars in digital asset transactions every year. They are not just trading platforms. They are ecosystems where ownership, identity, and value converge on-chain. But here…
Red Flags to Watch Before Hiring a Smart…
The best time to build smart contract security into your protocol is before you ever engage an audit firm. Solidity Shield from SecureDApp gives development teams continuous automated vulnerability detection throughout the development process, not just at the end. By…
How to Audit ERC-20 Smart Contracts for Security…
Auditing ERC-20 smart contracts is not a single step. It is a structured process that combines automated scanning, manual code review, formal verification, and economic analysis. Each layer catches what the others might miss. Together, they form a defense that…
API-Based Real-Time On-Chain Monitoring: Architecture & Setup
Blockchain networks generate thousands of transactions every single minute. Each transaction touches a smart contract, modifies state, or moves assets. If something malicious slips through unnoticed, the damage can be irreversible. This is exactly why real-time blockchain threat monitoring has…
Token Movement Tracking: Real-Time On-Chain Monitoring Explained
Introduction: When Every Transaction Is a Potential Risk Picture this. It is 2:00 AM in Mumbai. A DeFi protocol sitting on Ethereum holds over $80 million in liquidity. Nobody is watching. A hacker begins silently draining tokens through a re-entrancy…
Using Real-Time On-Chain Data for Fraud Prevention in…
Introduction: The DeFi Security Problem No One Wants to Talk About Decentralised finance has unlocked genuine financial freedom for millions. But it has also become one of the most exploited environments in the history of digital assets. In 2023 alone,…
Smart Contract Security: Common Vulnerabilities & Solutions
Smart contracts were built on a simple promise: trustless execution. Once deployed, they run exactly as written, without the need for intermediaries, lawyers, or manual oversight. That promise has powered an entirely new financial ecosystem worth hundreds of billions of…
Self-Sovereign Identity: Enterprise Implementation Guide
Self-Sovereign Identity represents a fundamental shift in how enterprises think about digital trust. It moves identity from a centralized service that organizations control to a distributed capability that individuals and entities hold directly. That shift has profound implications for security…
How to Conduct a Blockchain Forensic Investigation
A blockchain forensic investigation is a structured discipline that requires clear methodology, appropriate tooling, and a realistic understanding of what on-chain evidence can and cannot establish in both technical and legal contexts. The teams that achieve the best outcomes from…