Blog
Read the fastest Web3 blog
Search via tags
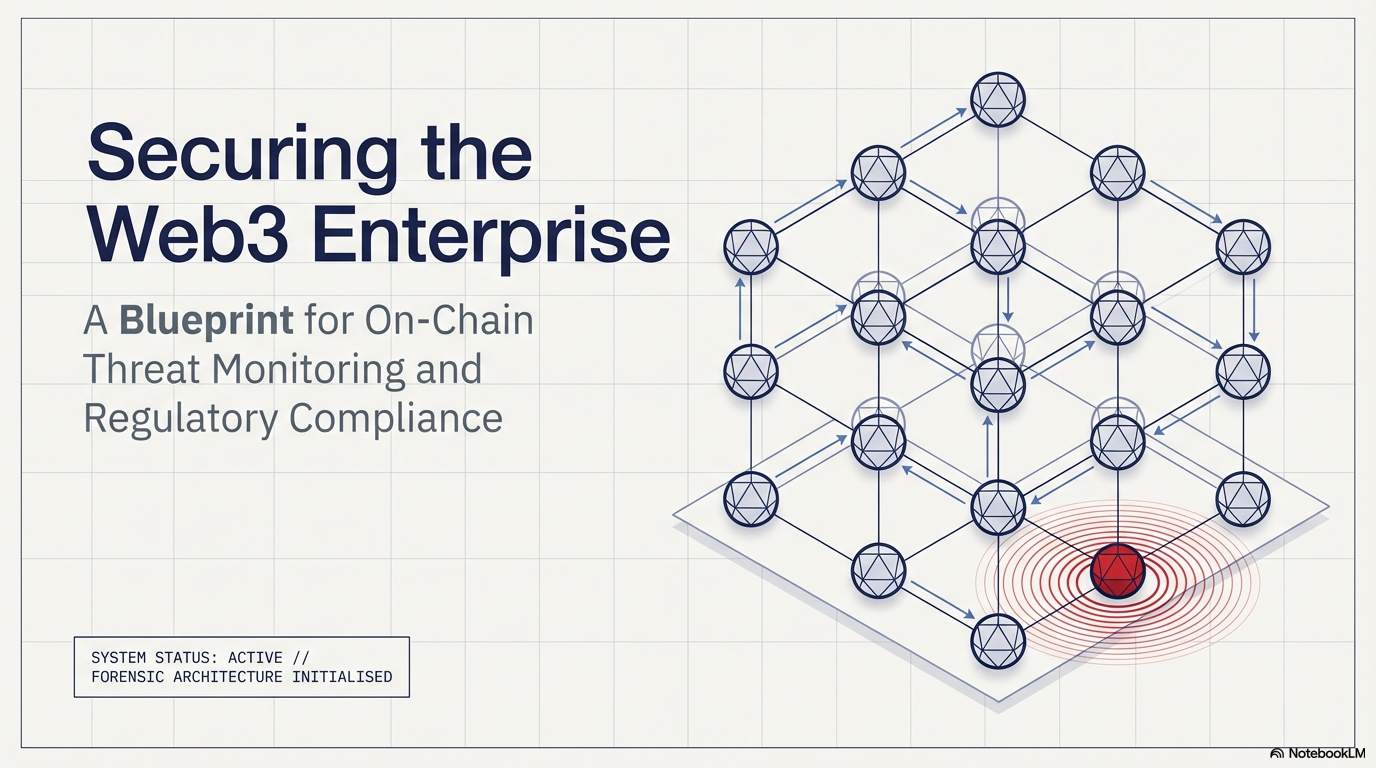
On-Chain Monitoring Solutions: Detecting Threats as They Happen
In 2023 alone, over USD 1.8 billion was lost to DeFi exploits and on-chain attacks. Most of those losses had one thing in common: the threat was visible on-chain before any damage was done. Nobody was watching. Real-time…
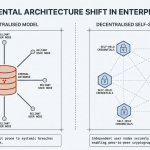
Enterprise Guide to Self-Sovereign Identity
In 2023, a major European financial services firm discovered that a significant portion of its customer identity data had been sitting in a vendor database it had not actively monitored in over fourteen months. The vendor had been…
Real-Time On-Chain Threat Monitoring: Complete Implementation Guide
Why Reactive Security No Longer Works in Web3 In 2023 alone, over $1.8 billion was lost to on-chain exploits globally. Flash loan attacks, rug pulls, and contract draining events most happened within minutes. By the time teams discovered…
Real-Time Blockchain Threat Alert Systems: Complete Overview
In 2023 alone, blockchain exploits drained over $1.8 billion from DeFi protocols. Most of these attacks were not sudden. They had on-chain signals: hours before funds moved. The difference between the projects that survived and those that lost…
Real-Time Threat Monitoring for Blockchain: Complete Framework
Blockchain attacks don't wait. They execute in seconds, drain funds in a single block, and disappear across chains before most teams even notice. This guide breaks down exactly how real-time threat monitoring for blockchain works, why traditional audits…
How Institutions Protect Against Threats With Real-Time Monitoring
Blockchain-based institutions face threats that evolve by the minute. Traditional security models were not built for this speed. They rely on periodic audits and manual reviews. That approach leaves critical windows of exposure open. Real-time blockchain threat monitoring…
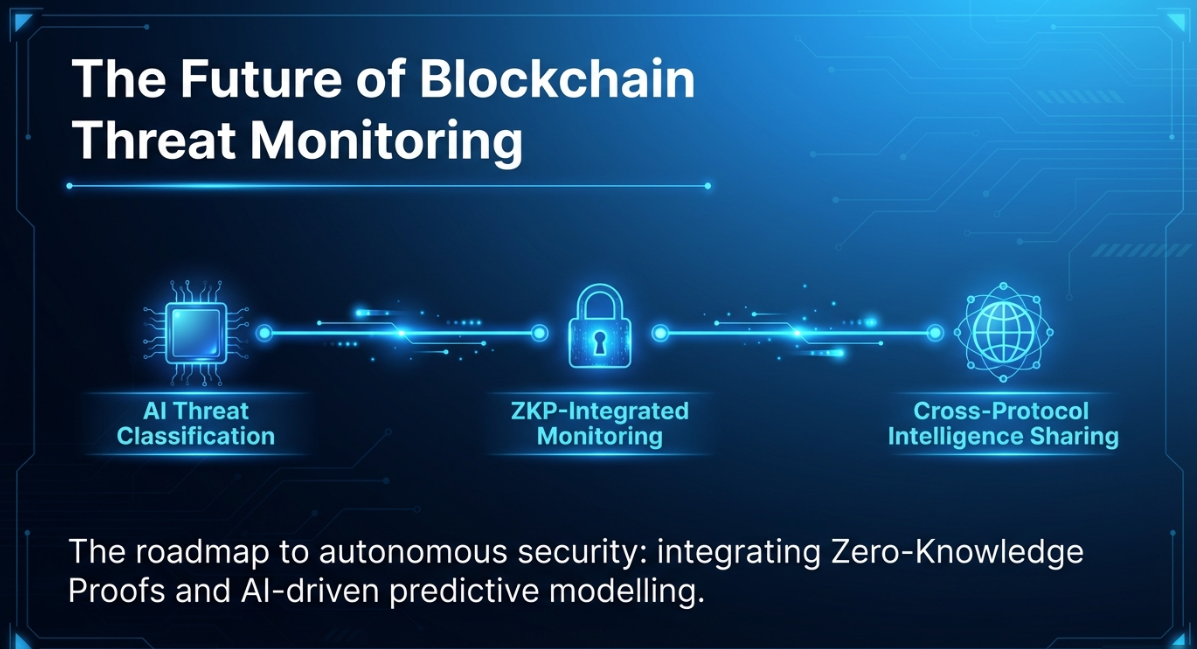
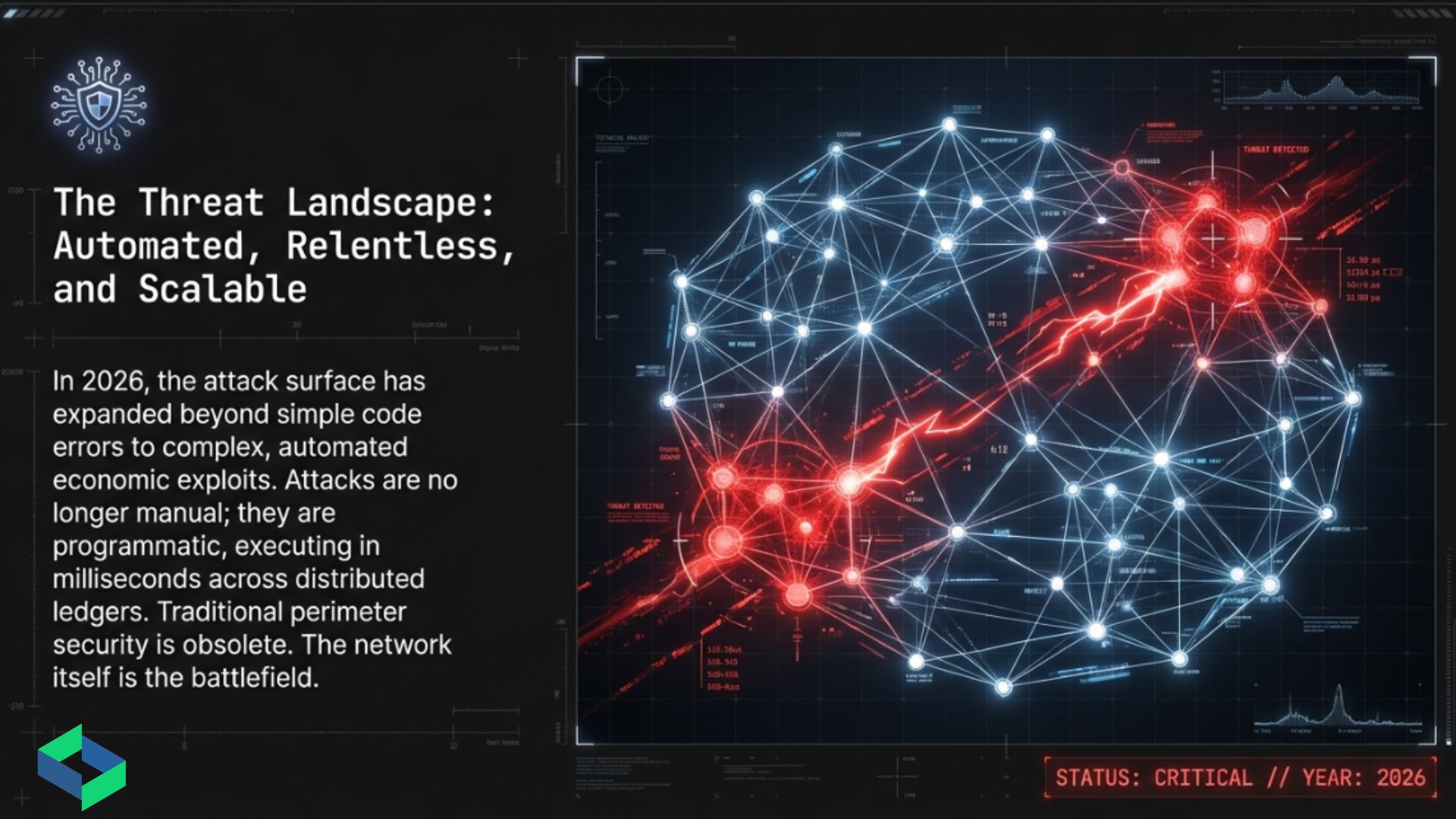
The Ultimate Guide to Blockchain Security in 2026
The Ultimate Guide to Blockchain Security in 2026 covers the full Web3 threat landscape and how to defend against it. Blockchain security is uniquely challenging because code is immutable and attacks are irreversible. The article breaks down common…
Smart Contract Security: Real-Time Monitoring Best Practices
Introduction Billions of dollars in crypto assets sit inside smart contracts right now. Every second, those contracts are exposed to bad actors. The problem isn’t just writing secure code. It’s knowing when something goes wrong in real time.…
Real-Time Blockchain Anomaly Detection: Advanced Techniques
Introduction Blockchain networks are not immune to threats. In 2024 alone, on-chain exploits cost the industry over $2.3 billion. Traditional security tools simply cannot keep pace. The speed of decentralized transactions demands something faster and smarter. This is…
Blog
Read the fastest Web3 blog
Search via category
Blog
Read the fastest Web3 blog
Search via tags
On-Chain Monitoring Solutions: Detecting Threats as They Happen
In 2023 alone, over USD 1.8 billion was lost to DeFi exploits and on-chain attacks. Most of those losses had one thing in common: the threat was visible on-chain before any damage was done. Nobody was watching. Real-time blockchain threat…
Enterprise Guide to Self-Sovereign Identity
In 2023, a major European financial services firm discovered that a significant portion of its customer identity data had been sitting in a vendor database it had not actively monitored in over fourteen months. The vendor had been breached. The…
Real-Time On-Chain Threat Monitoring: Complete Implementation Guide
Why Reactive Security No Longer Works in Web3 In 2023 alone, over $1.8 billion was lost to on-chain exploits globally. Flash loan attacks, rug pulls, and contract draining events most happened within minutes. By the time teams discovered the breach,…
Real-Time Blockchain Threat Alert Systems: Complete Overview
In 2023 alone, blockchain exploits drained over $1.8 billion from DeFi protocols. Most of these attacks were not sudden. They had on-chain signals: hours before funds moved. The difference between the projects that survived and those that lost everything? Real-time…
Real-Time Threat Monitoring for Blockchain: Complete Framework
Blockchain attacks don't wait. They execute in seconds, drain funds in a single block, and disappear across chains before most teams even notice. This guide breaks down exactly how real-time threat monitoring for blockchain works, why traditional audits fall short…
How Institutions Protect Against Threats With Real-Time Monitoring
Blockchain-based institutions face threats that evolve by the minute. Traditional security models were not built for this speed. They rely on periodic audits and manual reviews. That approach leaves critical windows of exposure open. Real-time blockchain threat monitoring closes those…
The Ultimate Guide to Blockchain Security in 2026
The Ultimate Guide to Blockchain Security in 2026 covers the full Web3 threat landscape and how to defend against it. Blockchain security is uniquely challenging because code is immutable and attacks are irreversible. The article breaks down common smart contract…
Smart Contract Security: Real-Time Monitoring Best Practices
Introduction Billions of dollars in crypto assets sit inside smart contracts right now. Every second, those contracts are exposed to bad actors. The problem isn’t just writing secure code. It’s knowing when something goes wrong in real time. Real-time blockchain…
Real-Time Blockchain Anomaly Detection: Advanced Techniques
Introduction Blockchain networks are not immune to threats. In 2024 alone, on-chain exploits cost the industry over $2.3 billion. Traditional security tools simply cannot keep pace. The speed of decentralized transactions demands something faster and smarter. This is where real-time…