Blog
Read the fastest Web3 blog
Search via tags
Top 10 On-Chain Threat Detection Tools in 2026
On-chain threat monitoring is one of the most important disciplines in blockchain security today. As ecosystems grow more complex, as DeFi protocols become more interconnected, and as the value at stake continues to climb, the cost of inadequate…
Using Real-Time On-Chain Data for Fraud Prevention in DeFi
DeFi moved over $100 billion in value last year. And fraudsters followed every rupee, every dollar of it. The blockchain is transparent. Everything is recorded. Yet somehow, exploits still happen within seconds. Flash loans drain liquidity pools. Rug…
Smart Contract Exploit Detection: Real-Time On-Chain Methods
Introduction In 2024, over $2.3 billion was lost to smart contract exploits across DeFi and Web3 protocols. Most of these attacks did not happen in hours. They happened in seconds. Sometimes in a single transaction. This is the…
Real-Time On-Chain Analysis: Detecting MEV and Flash Loan Attacks
The blockchain ecosystem moves fast. Very fast. In the time it takes to read this sentence, hundreds of transactions have been submitted, validated, and settled on-chain. And somewhere in that chaos, there are bad actors looking for a…
The Complete Guide to Real-Time Blockchain Threat Monitoring
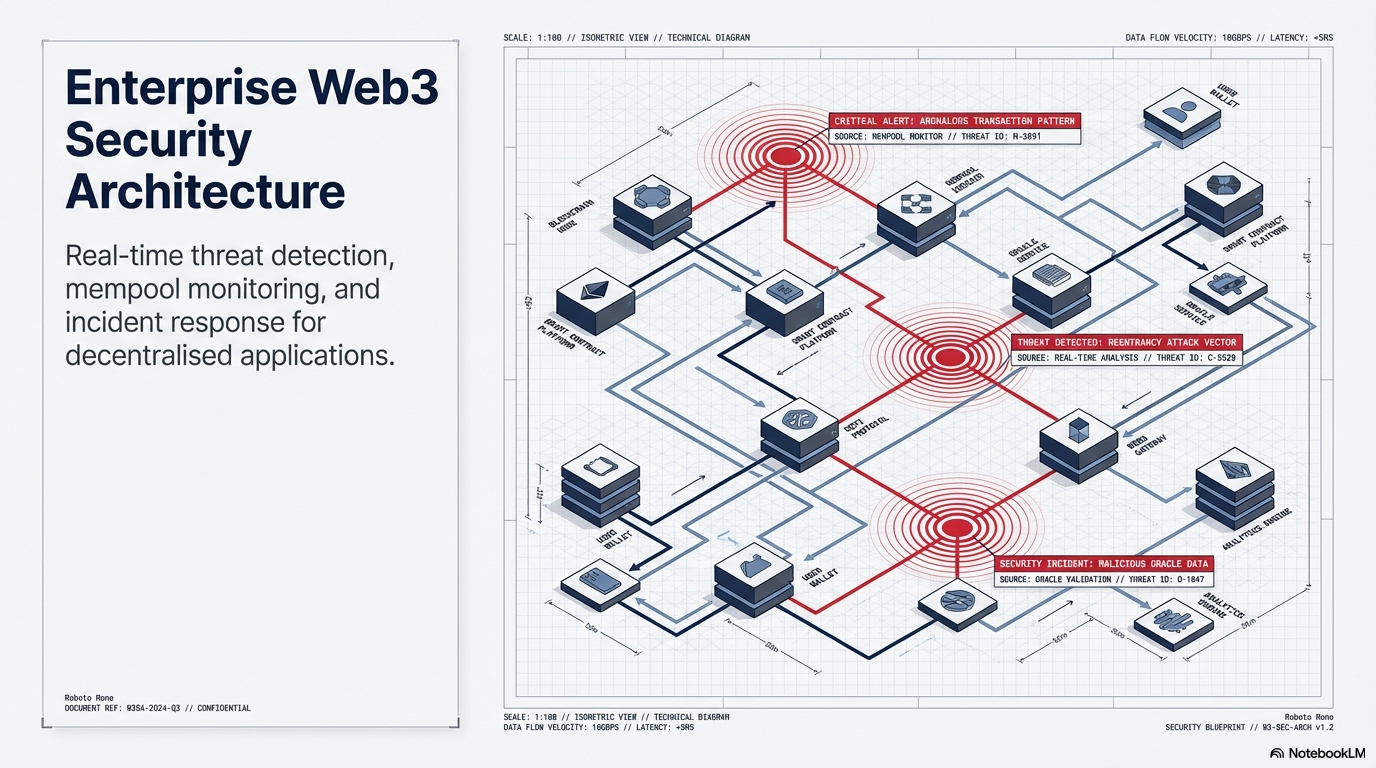
Blockchain security has matured significantly from its early days of ad hoc audits and manual incident response. The sophistication of on-chain attacks has forced a corresponding evolution in how teams think about security operations. Real-time blockchain threat monitoring…
On-Chain Transaction Monitoring vs Off-Chain Security Measures: Which One Actually Protects Your Protocol?
Introduction: The Question Every Protocol Founder Gets Wrong Most Web3 teams pick a security approach the same way they pick a cloud provider. They go with what they already know. That instinct is expensive. In 2024 alone, over…
How to Monitor Blockchain Transactions in Real-Time: Step-by-Step Guide
Introduction: Why Real-Time Blockchain Threat Monitoring Matters Blockchain is transparent by design. Every transaction is on-chain. Everyone can see it. But here is the uncomfortable truth most projects and users are watching nothing. They only find out about…
Blockchain Forensics: From Investigation to Compliance
Blockchain forensics began as a specialized tool for law enforcement agencies investigating crypto-related crime. It has become a core organizational capability for any team operating seriously in the digital asset space. The distinction matters because it changes where…
DeFi Security: Real-Time On-Chain Threat Detection Strategies
In 2023, over $1.8 billion was drained from DeFi protocols through on-chain exploits. Most of those attacks were not silent. They left signals, moved through mempools. And also triggered unusual state changes. The problem was not a lack…
Blog
Read the fastest Web3 blog
Search via category
Blog
Read the fastest Web3 blog
Search via tags
Top 10 On-Chain Threat Detection Tools in 2026
On-chain threat monitoring is one of the most important disciplines in blockchain security today. As ecosystems grow more complex, as DeFi protocols become more interconnected, and as the value at stake continues to climb, the cost of inadequate monitoring becomes…
Using Real-Time On-Chain Data for Fraud Prevention in…
DeFi moved over $100 billion in value last year. And fraudsters followed every rupee, every dollar of it. The blockchain is transparent. Everything is recorded. Yet somehow, exploits still happen within seconds. Flash loans drain liquidity pools. Rug pulls leave…
Smart Contract Exploit Detection: Real-Time On-Chain Methods
Introduction In 2024, over $2.3 billion was lost to smart contract exploits across DeFi and Web3 protocols. Most of these attacks did not happen in hours. They happened in seconds. Sometimes in a single transaction. This is the brutal reality…
Real-Time On-Chain Analysis: Detecting MEV and Flash Loan…
The blockchain ecosystem moves fast. Very fast. In the time it takes to read this sentence, hundreds of transactions have been submitted, validated, and settled on-chain. And somewhere in that chaos, there are bad actors looking for a window. MEV…
The Complete Guide to Real-Time Blockchain Threat Monitoring
Blockchain security has matured significantly from its early days of ad hoc audits and manual incident response. The sophistication of on-chain attacks has forced a corresponding evolution in how teams think about security operations. Real-time blockchain threat monitoring is at…
On-Chain Transaction Monitoring vs Off-Chain Security Measures: Which…
Introduction: The Question Every Protocol Founder Gets Wrong Most Web3 teams pick a security approach the same way they pick a cloud provider. They go with what they already know. That instinct is expensive. In 2024 alone, over $2.3 billion…
How to Monitor Blockchain Transactions in Real-Time: Step-by-Step…
Introduction: Why Real-Time Blockchain Threat Monitoring Matters Blockchain is transparent by design. Every transaction is on-chain. Everyone can see it. But here is the uncomfortable truth most projects and users are watching nothing. They only find out about a hack,…
Blockchain Forensics: From Investigation to Compliance
Blockchain forensics began as a specialized tool for law enforcement agencies investigating crypto-related crime. It has become a core organizational capability for any team operating seriously in the digital asset space. The distinction matters because it changes where in the…
DeFi Security: Real-Time On-Chain Threat Detection Strategies
In 2023, over $1.8 billion was drained from DeFi protocols through on-chain exploits. Most of those attacks were not silent. They left signals, moved through mempools. And also triggered unusual state changes. The problem was not a lack of data.…