Blog
Read the fastest Web3 blog
Search via tags
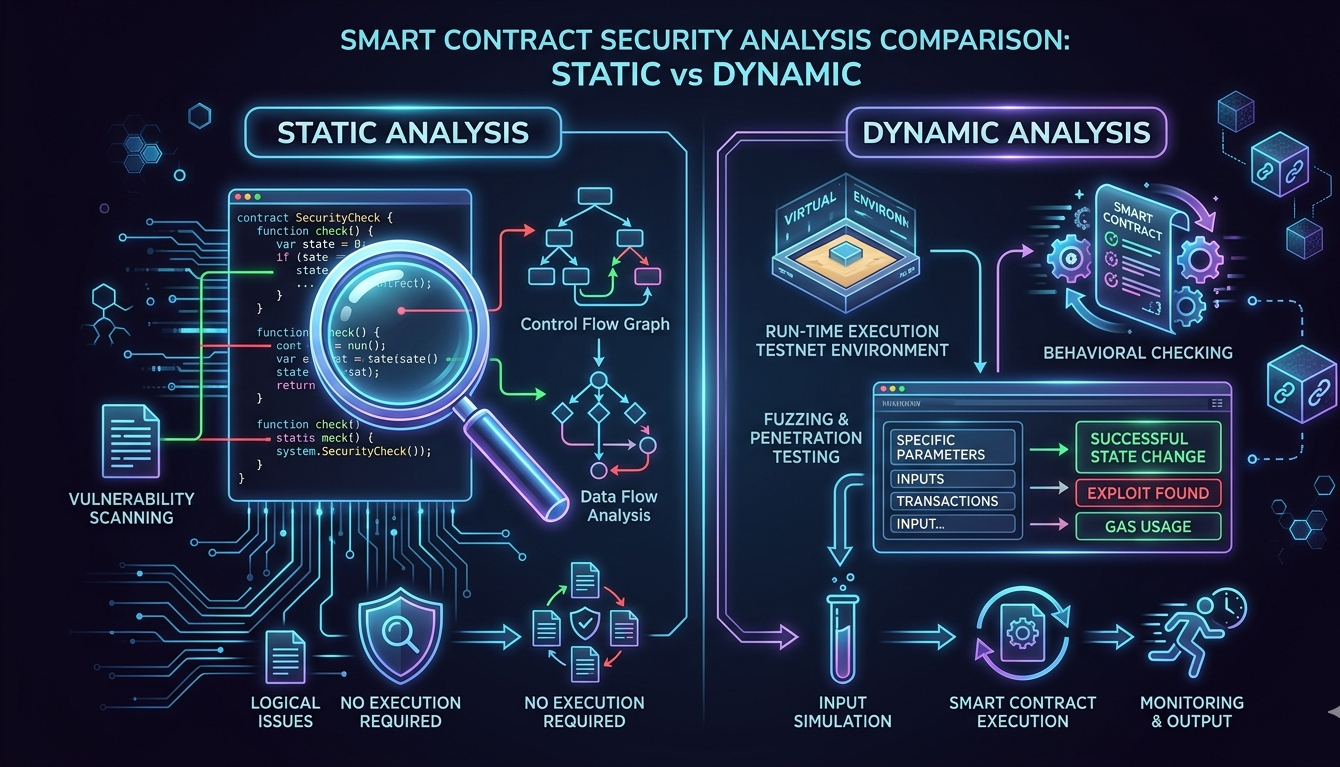
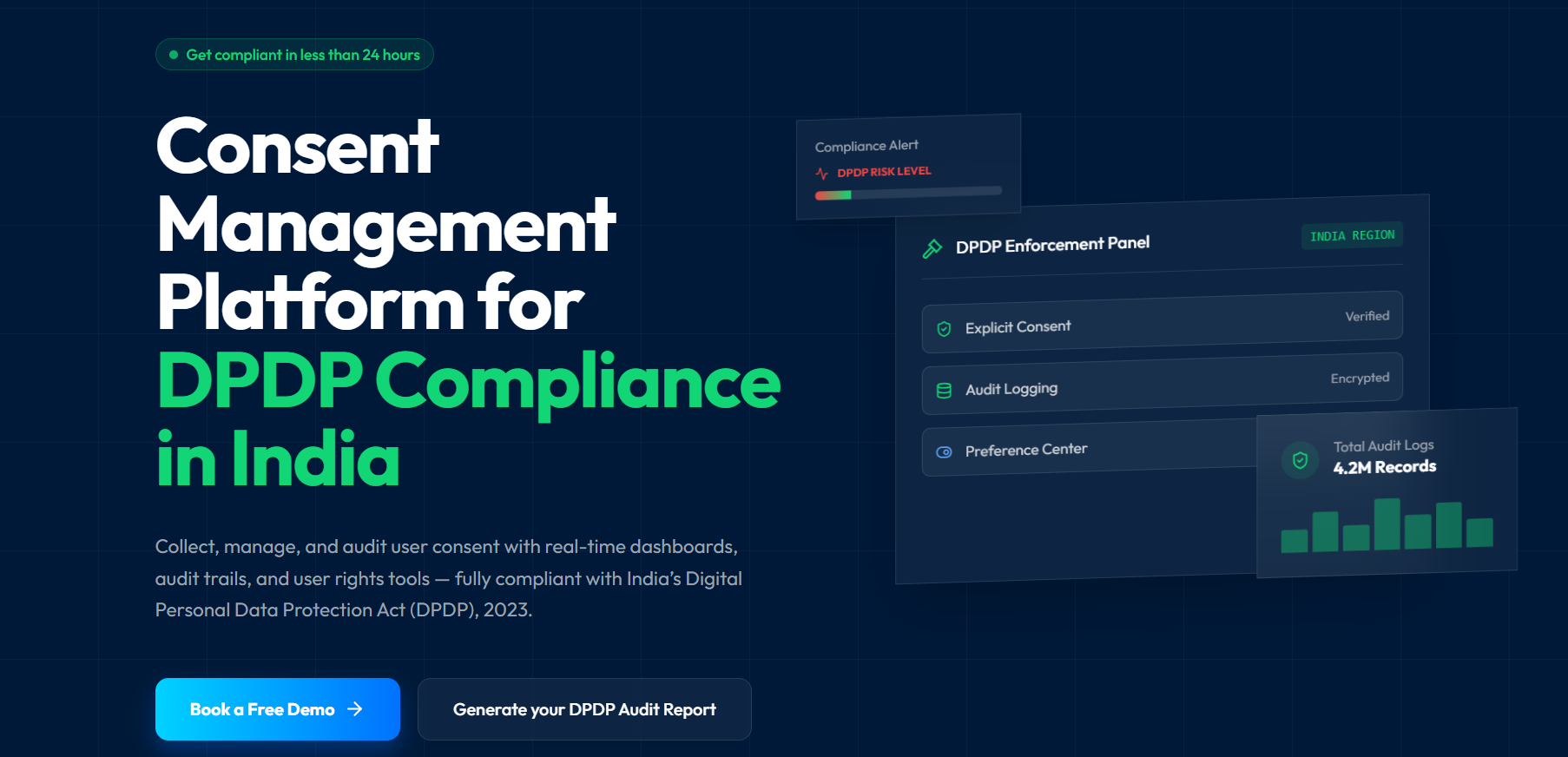
Static vs Dynamic Analysis in Smart Contract Security Testing
Security testing is not a single activity. It is a collection of techniques, each designed to reveal a different class of vulnerability in a different way. For smart contracts, the distinction between static and dynamic analysis is foundational.…
What Is Post-Quantum Cryptography and Why Indian Enterprises Must Prepare Now
The Encryption You Trust Today Is Already Being Targeted Somewhere right now, a well-funded adversary is downloading your encrypted data. They are not trying to break it today. They are storing it and waiting, patiently, for the day…
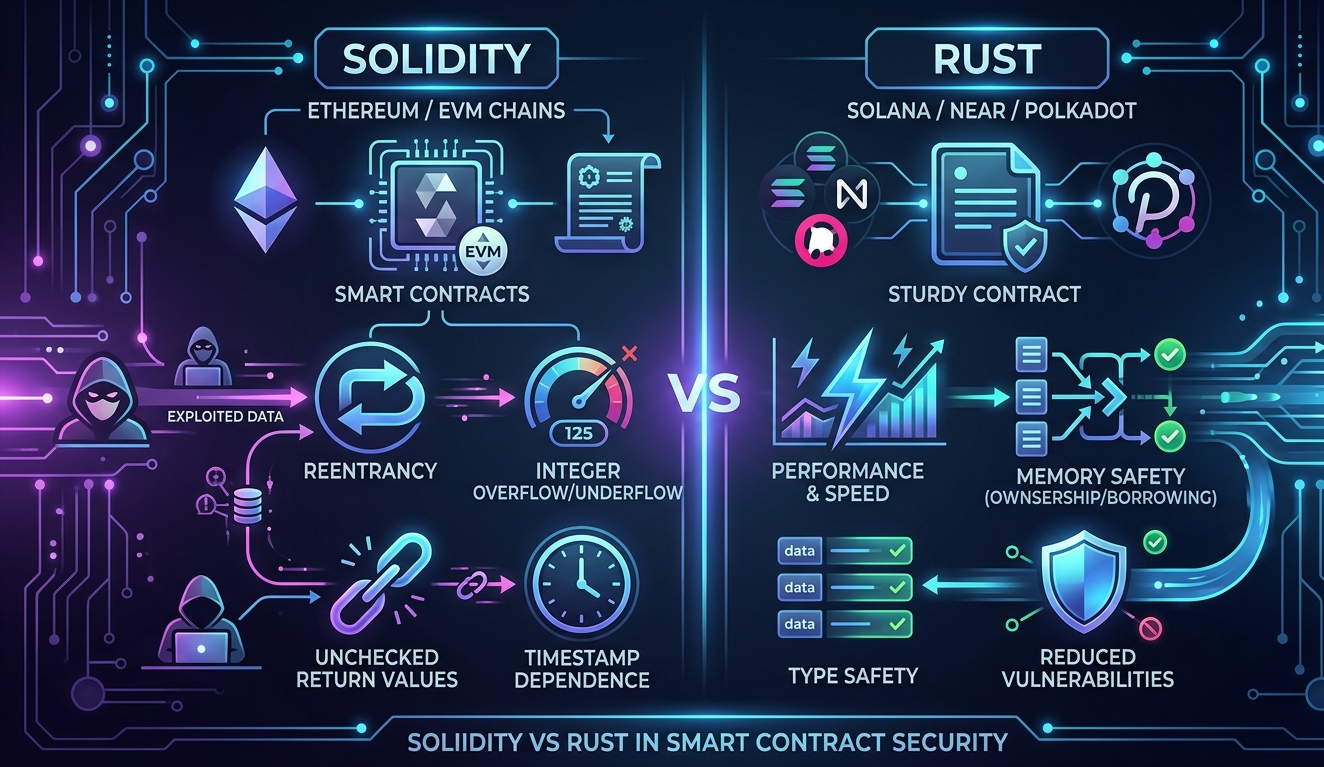
Solidity vs Rust: Which Offers Better Smart Contract Security?
For teams choosing between ecosystems today, the practical security advantage lies with Solidity and EVM due to the maturity of the defensive ecosystem. The vulnerabilities are better understood, the tooling is more advanced, and the community knowledge is…
What Is a Hardware Security Module and How Does It Protect Your Enterprise Data?
Every enterprise stores secrets. Not secrets in the metaphorical sense but cryptographic secrets: private keys, signing certificates, session tokens, authentication credentials, and encryption material that undergird the entire security posture of the organisation. These secrets protect financial transactions,…
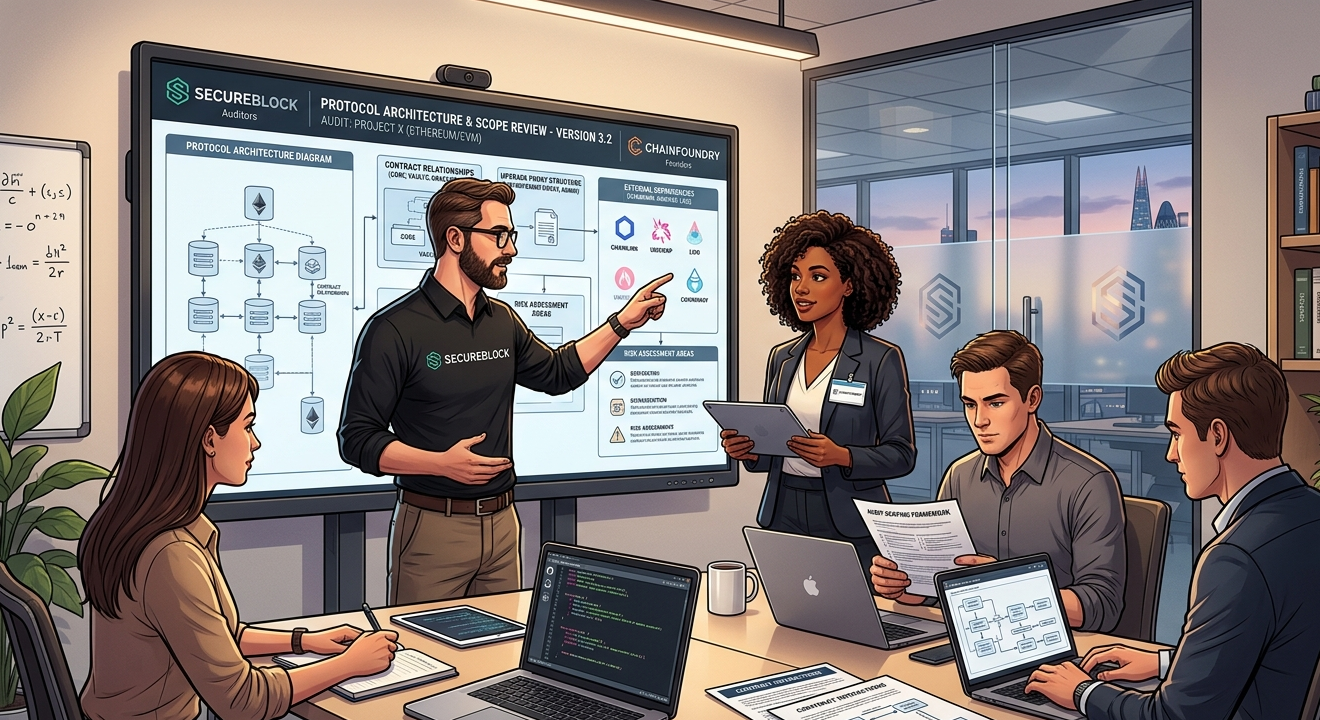
Smart Contract Security Audit Checklist for Founders
Build a development culture that treats security as integral to the engineering process, not external to it. Use Solidity Shield throughout your development cycle to maintain continuous visibility into your codebase's vulnerability profile. Treat each audit as a…
Staking Pool Security Through Real-Time On-Chain Monitoring
Introduction: The Security Problem No One Talks About Enough Staking pools are quietly becoming the backbone of Proof-of-Stake blockchain networks. Millions of dollars in validator rewards flow through them every single day. But here is the uncomfortable truth…
What Is a Hardware Security Module and How Does It Protect Your Enterprise Data?
Every enterprise stores secrets. Not secrets in the metaphorical sense – but cryptographic secrets: private keys, signing certificates, session tokens, authentication credentials, and encryption material that undergird the entire security posture of the organization. These secrets protect financial…
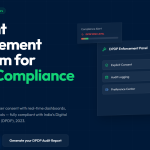
Top 5 DPDP Consent Management Platforms in India (2025): Protect Your Business Before It’s Too Late
India's data privacy landscape changed permanently on August 11, 2023. The Digital Personal Data Protection Act arrived, and with it came a reality that businesses can no longer sidestep: if you collect personal data from Indian users, you…
What Is a Consent Management Platform and Why Does India Need One Now
India's Digital Personal Data Protection Act, commonly known as DPDP, has fundamentally changed the rules. Businesses that collect, process, or store personal data of Indian citizens now face a clear legal obligation: obtain explicit, informed, and purposeful consent…
Blog
Read the fastest Web3 blog
Search via category
Blog
Read the fastest Web3 blog
Search via tags
Static vs Dynamic Analysis in Smart Contract Security…
Security testing is not a single activity. It is a collection of techniques, each designed to reveal a different class of vulnerability in a different way. For smart contracts, the distinction between static and dynamic analysis is foundational. Understanding what…
What Is Post-Quantum Cryptography and Why Indian Enterprises…
The Encryption You Trust Today Is Already Being Targeted Somewhere right now, a well-funded adversary is downloading your encrypted data. They are not trying to break it today. They are storing it and waiting, patiently, for the day quantum computers…
Solidity vs Rust: Which Offers Better Smart Contract…
For teams choosing between ecosystems today, the practical security advantage lies with Solidity and EVM due to the maturity of the defensive ecosystem. The vulnerabilities are better understood, the tooling is more advanced, and the community knowledge is deeper. Solidity…
What Is a Hardware Security Module and How…
Every enterprise stores secrets. Not secrets in the metaphorical sense but cryptographic secrets: private keys, signing certificates, session tokens, authentication credentials, and encryption material that undergird the entire security posture of the organisation. These secrets protect financial transactions, medical records,…
Smart Contract Security Audit Checklist for Founders
Build a development culture that treats security as integral to the engineering process, not external to it. Use Solidity Shield throughout your development cycle to maintain continuous visibility into your codebase's vulnerability profile. Treat each audit as a milestone in…
Staking Pool Security Through Real-Time On-Chain Monitoring
Introduction: The Security Problem No One Talks About Enough Staking pools are quietly becoming the backbone of Proof-of-Stake blockchain networks. Millions of dollars in validator rewards flow through them every single day. But here is the uncomfortable truth most pool…
What Is a Hardware Security Module and How…
Every enterprise stores secrets. Not secrets in the metaphorical sense – but cryptographic secrets: private keys, signing certificates, session tokens, authentication credentials, and encryption material that undergird the entire security posture of the organization. These secrets protect financial transactions, medical…
Top 5 DPDP Consent Management Platforms in India…
India's data privacy landscape changed permanently on August 11, 2023. The Digital Personal Data Protection Act arrived, and with it came a reality that businesses can no longer sidestep: if you collect personal data from Indian users, you need their…
What Is a Consent Management Platform and Why…
India's Digital Personal Data Protection Act, commonly known as DPDP, has fundamentally changed the rules. Businesses that collect, process, or store personal data of Indian citizens now face a clear legal obligation: obtain explicit, informed, and purposeful consent before doing…