Security testing is not a single activity. It is a collection of techniques, each designed to reveal a different class of vulnerability in a different way. For smart contracts, the distinction between static and dynamic analysis is foundational. Understanding what each approach reveals, where each has blind spots, and how they interact is essential to building a robust pre-deployment security posture.
This is not an academic distinction. The choice between static and dynamic analysis, or more precisely, the decision about how to combine them, has direct consequences for what vulnerabilities you catch before deployment and what attack surfaces remain exposed when your contract goes live.
Defining Static Analysis in Smart Contract Context
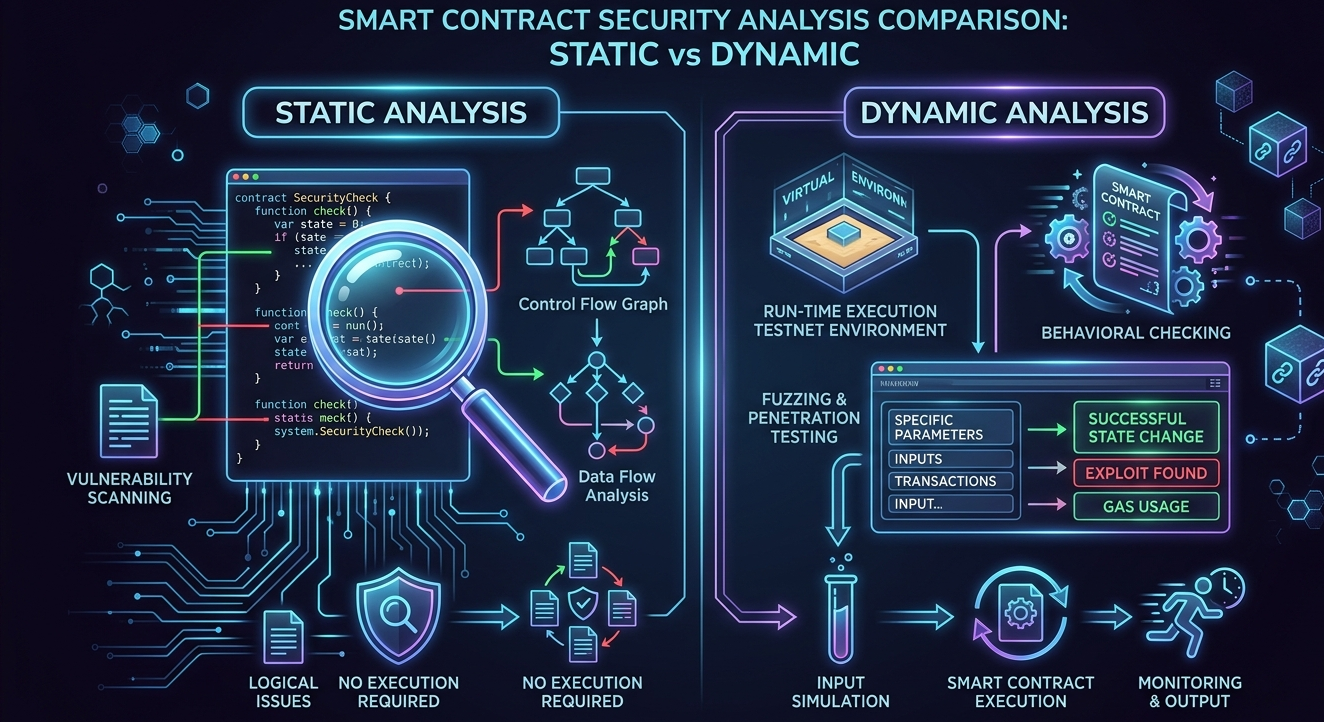
Static analysis examines smart contract code without executing it. The analysis tool reads the source code or bytecode, constructs a model of the program’s structure and data flow, and applies a set of rules or patterns to identify potential vulnerabilities.
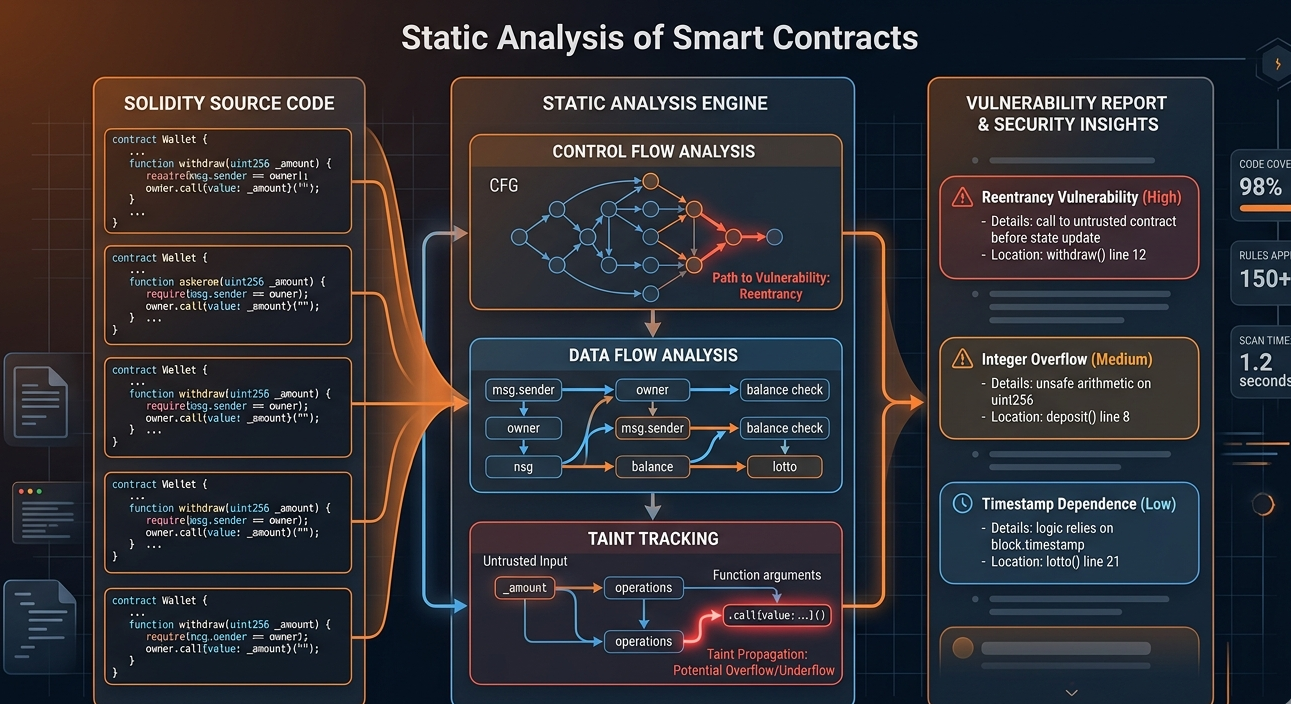
Common static analysis techniques include control flow analysis, data flow analysis, taint analysis, and symbolic execution. Each approaches the code from a different angle. Control flow analysis maps every possible execution path through the contract. Data flow analysis tracks how data moves through the contract, identifying points where untrusted input reaches sensitive operations. Taint analysis specifically follows user-controlled data to detect where it can influence critical contract state or behaviors.
The primary advantage of static analysis is coverage speed. A static analyzer can examine an entire codebase in seconds, checking every function and code path without the overhead of actually executing transactions. This makes it highly practical for integration into development workflows where fast feedback is essential.
What Static Analysis Finds Reliably
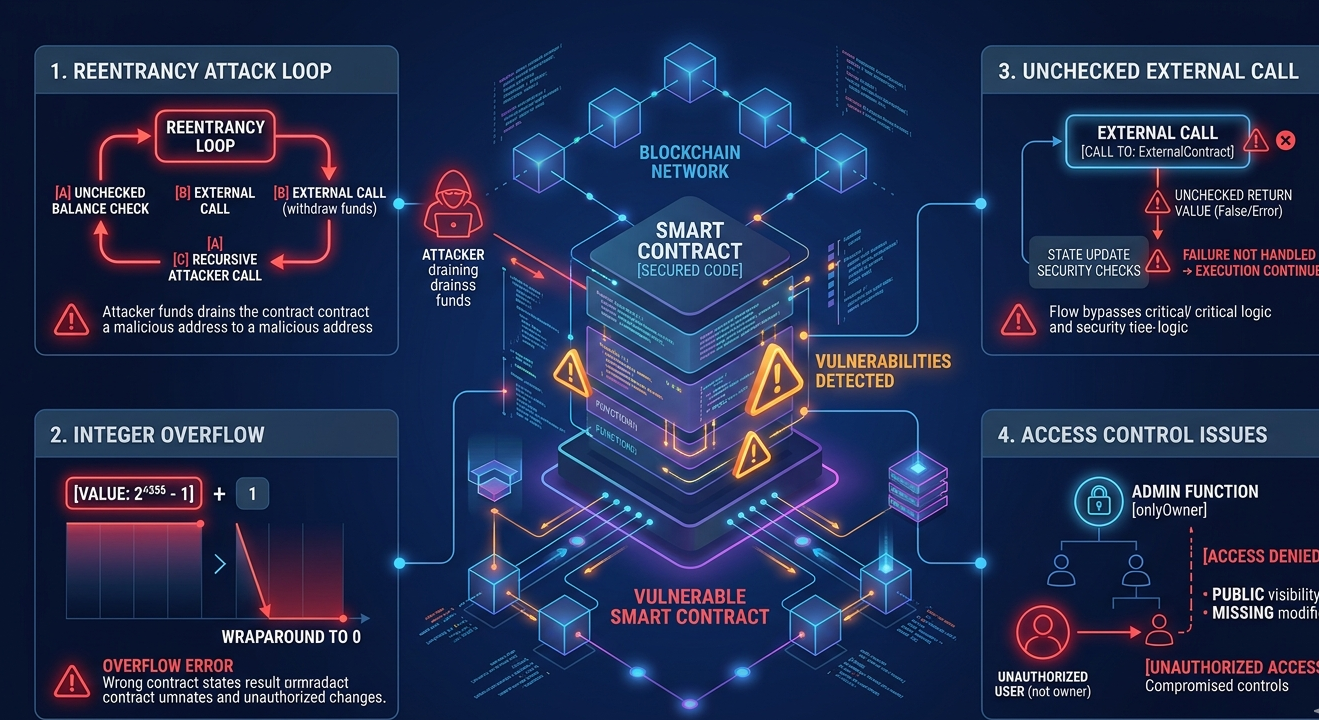
Static analysis has proven consistently effective at identifying a well-defined set of vulnerability classes in Solidity contracts. Reentrancy vulnerabilities, where an external call allows a malicious contract to call back into the original function before the first invocation completes, are detectable through control flow and state analysis. Integer overflow and underflow issues, unchecked return values from external calls, use of deprecated or dangerous functions, and improper access control patterns all fall within the reliable detection range of mature static analysis tools.
For these categories, static analysis provides near-deterministic results. If the pattern is present in the code, the tool will find it. This consistency makes static analysis an excellent first-pass filter, ensuring that well-understood vulnerability classes do not make it to deployment.
Tools like Mythril, Slither, and the analysis engine within Solidity Shield use static analysis as their foundation. They maintain libraries of known vulnerability signatures and apply them systematically across every contract they analyze. The result is consistent, reproducible detection of the vulnerability classes where static analysis excels.
The Limitations of Static Analysis
The challenge with static analysis is that it analyzes code structure, not runtime behavior. It cannot observe how a contract behaves when interacting with real state, real values, and real external contracts. This creates a meaningful gap in coverage.
False positives are a known issue with static analysis. Because the tool reasons about potential execution paths rather than actual ones, it sometimes flags code that is technically reachable in an analysis model but unreachable in practice due to invariants maintained elsewhere in the system. Managing false positive noise requires experienced reviewers who can distinguish genuine findings from analytical artifacts.
More critically, static analysis cannot detect vulnerabilities that only manifest under specific runtime conditions. A flash loan attack that destabilizes a protocol’s price oracle cannot be identified by examining the code structure alone. The vulnerability is economic, not syntactic. Similarly, access control issues that emerge from the interaction of multiple contracts deployed in sequence may be invisible to any single-contract static analysis.
Understanding Dynamic Analysis
Dynamic analysis tests smart contracts by executing them. This category includes fuzzing, where random or semi-random inputs are generated and applied to contract functions to identify unexpected behavior, and property-based testing, where the tester defines invariants that should always hold and systematically searches for inputs that violate them.
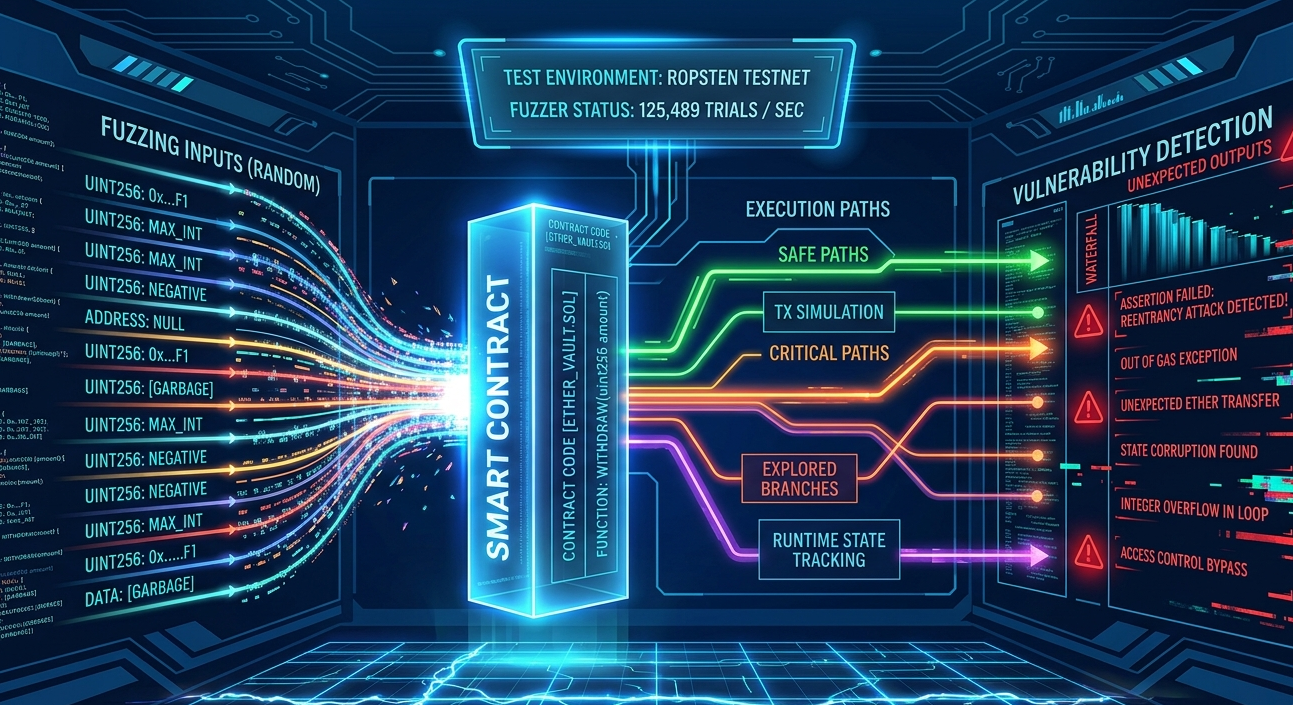
The fundamental advantage of dynamic analysis is that it tests actual behavior. When you fuzz a smart contract function, you observe what happens in practice when that function receives edge case inputs. This can reveal vulnerabilities that no amount of code reading would surface, because the vulnerability only manifests in specific, non-obvious execution contexts.
Dynamic analysis can also simulate realistic attack scenarios. A tester can construct a test environment that mirrors the deployed protocol’s interaction patterns and systematically test economic attack surfaces, governance attack vectors, and cross-protocol interaction risks. This simulation capability is a qualitative leap beyond what static analysis can provide.
Fuzzing as a Dynamic Analysis Technique
Fuzzing deserves specific attention because it has become increasingly important in smart contract security testing. Tools like Echidna and Foundry’s fuzzing capabilities allow security researchers to define properties that a contract should always satisfy and then bombard the contract with random inputs to find counterexamples.
This approach is particularly valuable for financial contracts where invariants like total supply consistency, balance conservation, or price bound guarantees should hold under all conditions. If a fuzzer can find an input sequence that violates these invariants, it has found a real vulnerability regardless of whether the underlying code looks clean to a static analyzer.
The limitation of fuzzing is coverage. A fuzzer can only test what it can reach, and the state space of a complex DeFi protocol is astronomical. Intelligent corpus generation and targeted property definition are needed to maximize the value of a fuzzing campaign. Without domain expertise guiding the test design, fuzzing can produce high runtime cost with limited coverage of the most important attack surfaces.
Symbolic Execution: The Bridge
Symbolic execution occupies an interesting position between static and dynamic analysis. It executes the contract, but instead of concrete values, it uses symbolic representations that stand in for all possible values. This allows it to reason about the full range of possible behaviors without requiring concrete test inputs.
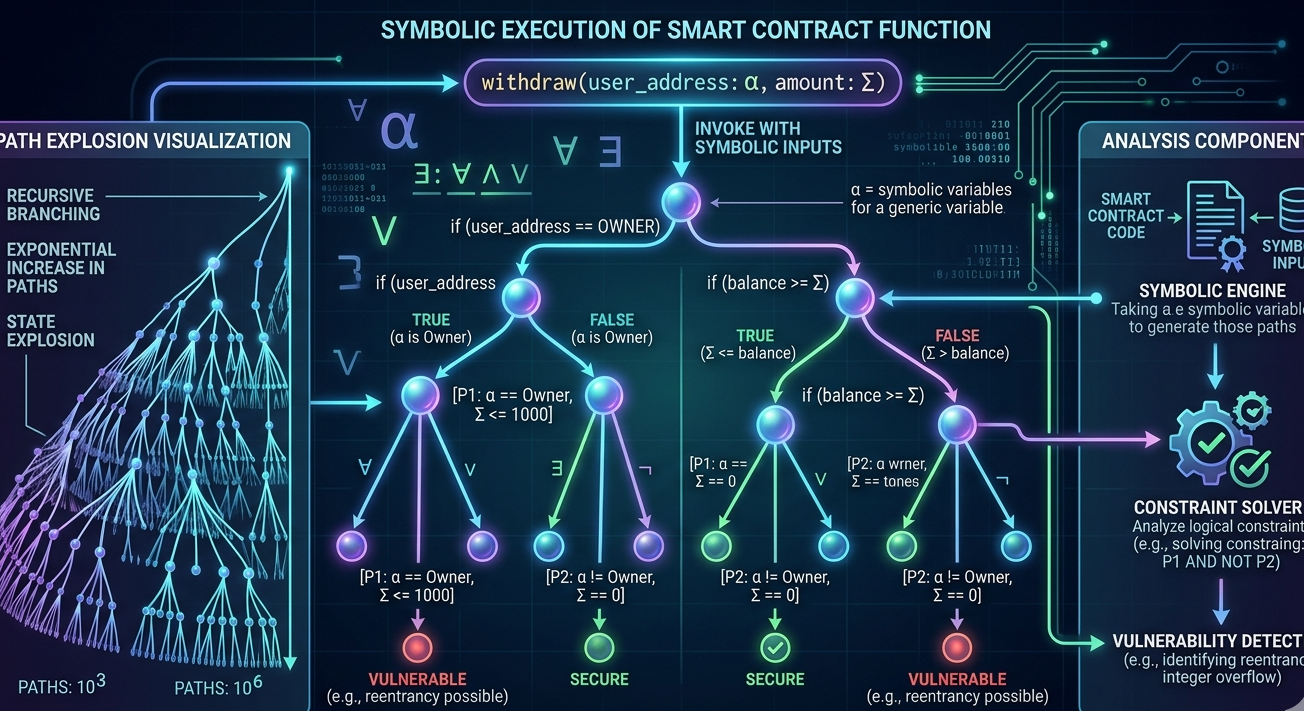
Symbolic execution can formally prove that certain properties hold under all inputs, or it can find specific input values that violate properties. When it works well, it provides the coverage depth of exhaustive testing with the speed advantages closer to static analysis. However, symbolic execution is computationally expensive and struggles with path explosion in complex contracts, where the number of possible execution paths grows exponentially with contract complexity.
Despite these limitations, symbolic execution is a valuable technique in a comprehensive security toolkit. For core protocol logic with well-defined properties and manageable path complexity, it provides a level of assurance that neither pure static analysis nor random fuzzing can match.
How Solidity Shield Applies Both Techniques
Solidity Shield integrates both static and dynamic analysis approaches in its vulnerability detection workflow. The static analysis layer provides fast, consistent coverage of known vulnerability patterns, ensuring that common issues are identified immediately and do not distract from deeper analysis. This layer processes the entire codebase systematically and produces a prioritized list of findings with context for each.
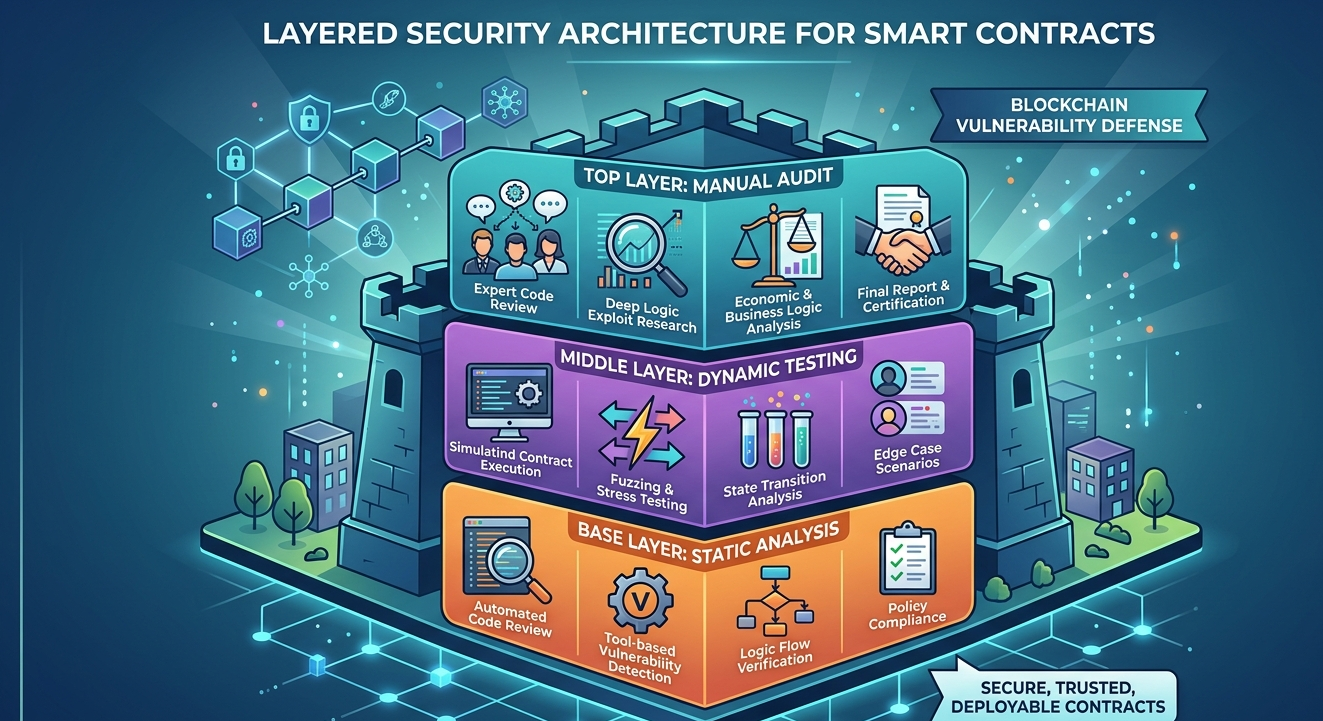
The dynamic analysis layer then extends coverage to runtime behaviors that static analysis cannot reach. This includes simulation of interaction patterns, testing of economic invariants, and evaluation of cross-contract behavior under adversarial conditions. The combination ensures that both the structural vulnerabilities visible in code analysis and the behavioral vulnerabilities only visible in execution are covered before any contract reaches mainnet.
This layered approach reflects how professional security teams approach complex systems. You start with fast, broad-coverage static analysis to establish a baseline, then deepen coverage through dynamic testing focused on the highest-risk areas identified in the static pass. Solidity Shield implements this workflow automatically, making the combined approach accessible to development teams without requiring separate tool stacks.
Choosing the Right Analysis Strategy for Your Protocol
Protocol complexity should guide the balance between static and dynamic analysis investment. For simpler contracts with limited state and interaction surfaces, thorough static analysis may provide sufficient coverage. For complex DeFi protocols with multiple token interactions, governance mechanisms, and economic incentive structures, dynamic analysis is not optional.
The stage of development also matters. Static analysis is most valuable during active development, providing fast feedback that helps developers avoid introducing vulnerabilities in the first place. Dynamic analysis is most valuable closer to deployment, when the contract architecture is stable and the goal is to identify any remaining vulnerabilities before launch.
A common approach for production-grade protocols is to run continuous static analysis throughout development, conduct a targeted fuzzing campaign on critical functions once the architecture stabilizes, and commission a manual expert audit that leverages both static and dynamic findings as context for a deeper architectural review.
The Role of Code Coverage in Dynamic Analysis
One practical challenge with dynamic analysis is understanding how much of the contract’s behavior has actually been tested. Code coverage metrics help, but they are not sufficient on their own. A contract can have 100 percent function coverage in a test suite while still having critical execution paths that were never exercised under adversarial conditions.
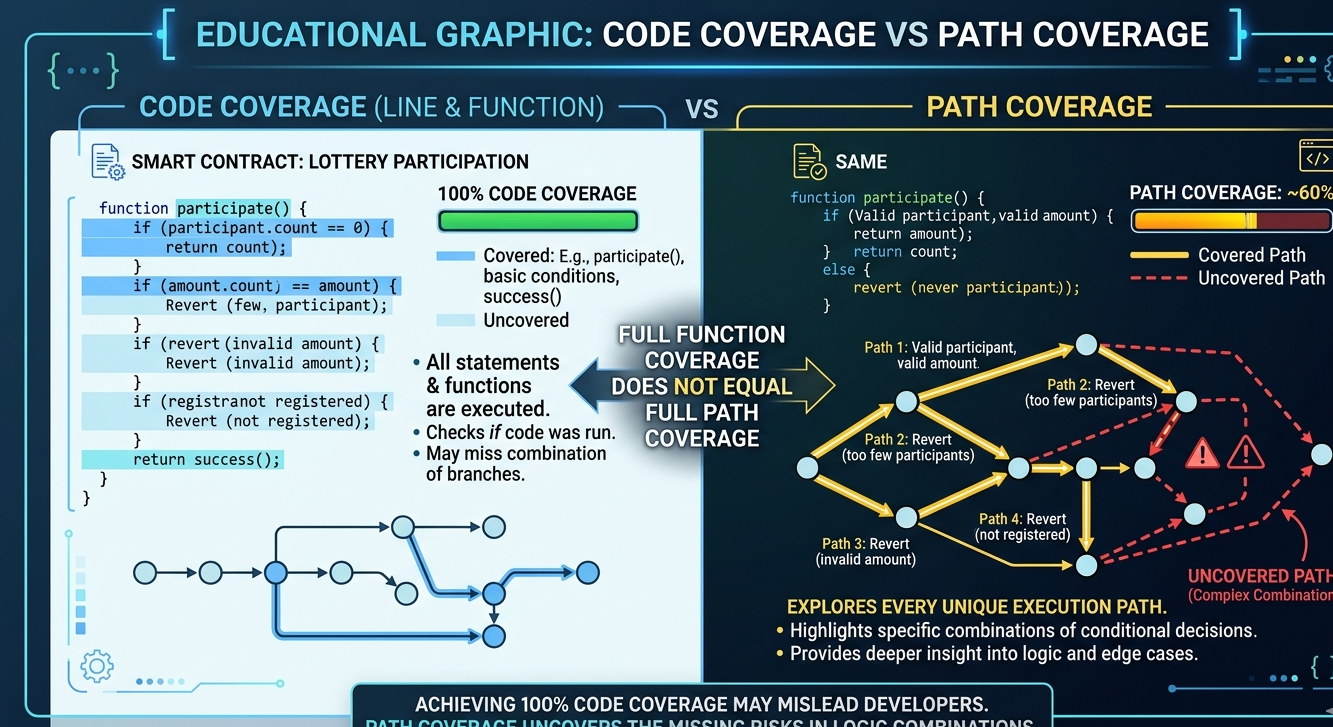
Path coverage, rather than function coverage, is the more meaningful metric for security purposes. The goal is to ensure that the most dangerous execution paths, particularly those involving external calls, state changes, and value transfers, are exercised with inputs specifically designed to probe their boundaries.
Solidity Shield’s analysis approach incorporates coverage considerations into its dynamic testing methodology, prioritizing the coverage of high-risk execution paths rather than optimizing purely for coverage metrics that may not reflect real-world attack exposure.
Conclusion
Static and dynamic analysis are not competing methodologies. They are complementary tools that illuminate different aspects of smart contract security. Static analysis provides fast, consistent coverage of structural vulnerabilities. Dynamic analysis reveals behavioral risks that only emerge during execution. Together, they form the analytical foundation of any serious smart contract security program.
Solidity Shield implements this combined approach in a workflow designed for real development teams, making comprehensive security analysis accessible without requiring separate tool stacks or specialized expertise in each individual technique. For protocols where the cost of a vulnerability is measured in user funds and protocol credibility, this layered approach is not an option. It is the baseline.
FAQ: Static vs Dynamic Analysis
1. Which is better for catching reentrancy vulnerabilities?
Static analysis reliably catches most reentrancy patterns through control flow analysis. Dynamic analysis can confirm exploitability by actually executing potential reentrancy scenarios. Using both provides the highest confidence in reentrancy protection.
2. Can dynamic analysis replace a formal audit?
No. Dynamic analysis extends coverage into runtime behavior but does not replace the architectural judgment and contextual reasoning that experienced human reviewers provide. It is one layer in a comprehensive security strategy, not a standalone solution.
3. What is the biggest advantage of fuzzing for smart contracts?
Fuzzing tests actual contract behavior under a wide range of inputs, including edge cases that no human tester would think to try manually. For financial invariants and numeric boundary conditions, fuzzing can find vulnerabilities that static analysis and manual review consistently miss.
4. How does Solidity Shield combine static and dynamic analysis?
Solidity Shield applies static analysis as a first pass for fast, consistent coverage of known vulnerability patterns, then extends into dynamic analysis for runtime behavior testing. The combination ensures coverage across both structural vulnerabilities and behavioral risks.
5. Is symbolic execution practical for large contracts?
Symbolic execution is computationally intensive and struggles with path explosion in complex contracts. It is most practical for analyzing specific, critical contract functions with well-defined properties rather than as a tool for full-codebase analysis.



