Launching a blockchain protocol without a thorough smart contract security audit is not a calculated risk. It is an invitation to disaster. The historical record is unambiguous: undiscovered vulnerabilities in smart contracts have cost the industry billions of dollars and destroyed projects that took years to build.
But submitting your code for an audit without proper preparation is its own kind of mistake. Underprepared submissions lead to wasted audit time, superficial coverage, and a false sense of security. Founders who understand what they are doing get measurably more value from the same audit engagement.
This checklist is designed for Web3 founders, CTOs, and technical leads who want to approach their smart contract security audit with the structure and discipline the process deserves. Use it before you submit, during the engagement, and after you receive the report.
Before the Audit: Codebase Preparation
Freeze the Codebase
Before an audit begins, your codebase must be frozen. Code that changes during an active audit creates confusion, invalidates previous findings, and forces auditors to restart portions of their review. Agree on a specific commit hash or tagged release as the audit target and hold it firm.
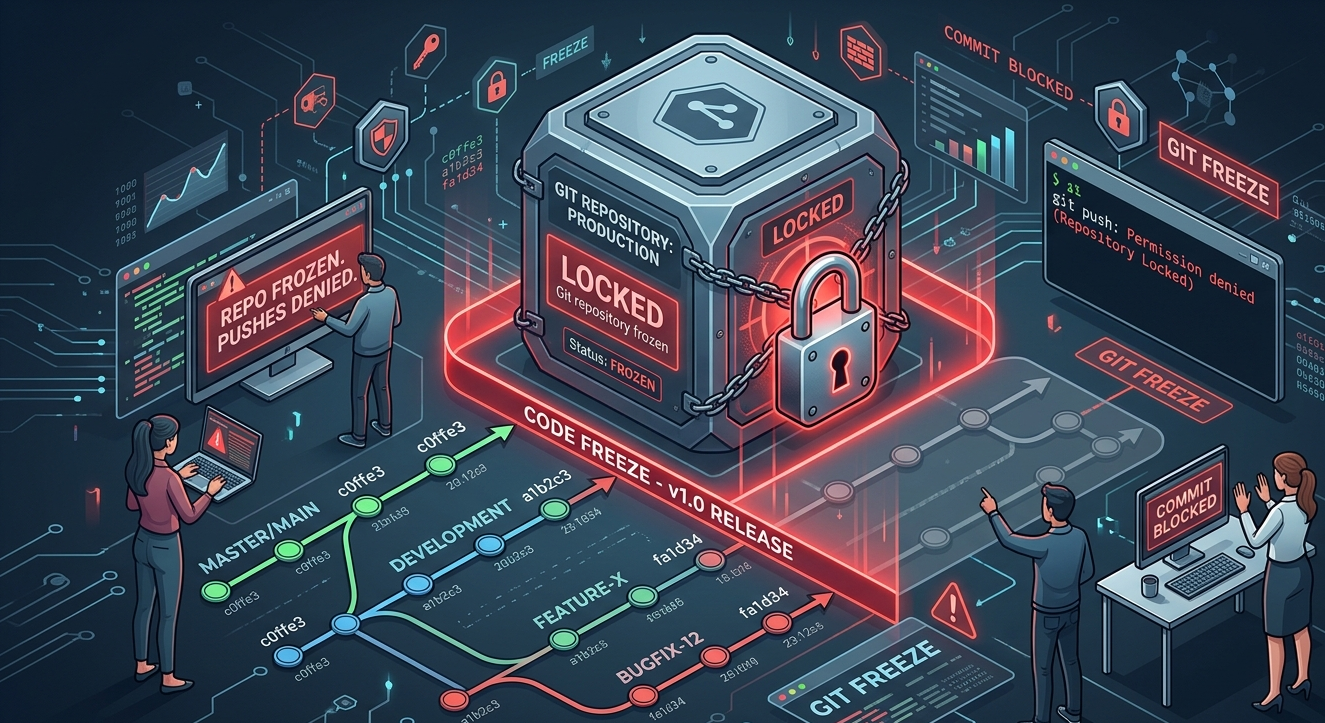
This requires coordinating with your development team. If there are critical bug fixes or features still in progress, complete them before the audit begins. It is better to delay your start date by a week than to conduct an audit on code that is still changing.
Resolve Compiler Warnings
Compiler warnings are not just cosmetic issues. Some represent real risks, and all of them consume audit attention that should be directed at logical vulnerabilities. Before submitting, address every compiler warning in your codebase. If a warning is genuinely acceptable, document why.
Submit code that compiles cleanly. This is a basic signal of codebase maturity that sets the right tone for the entire engagement.
Write Comprehensive NatSpec Documentation
NatSpec comments are the primary mechanism for communicating intended behavior in Solidity. Every public and external function should have NatSpec documentation describing what it does, what its parameters mean, what it returns, and any important preconditions or postconditions.
This matters because auditors distinguish between unintentional bugs and intentional design choices. Without documentation, they cannot reliably make that distinction. Poor documentation leads to false positives, missed real vulnerabilities, and a longer, more expensive engagement.
Create an Architecture Overview Document
Provide auditors with a written overview of your protocol architecture. This should describe the purpose of each contract, how contracts interact with each other, the key user flows, and any design decisions that might seem unusual without context.
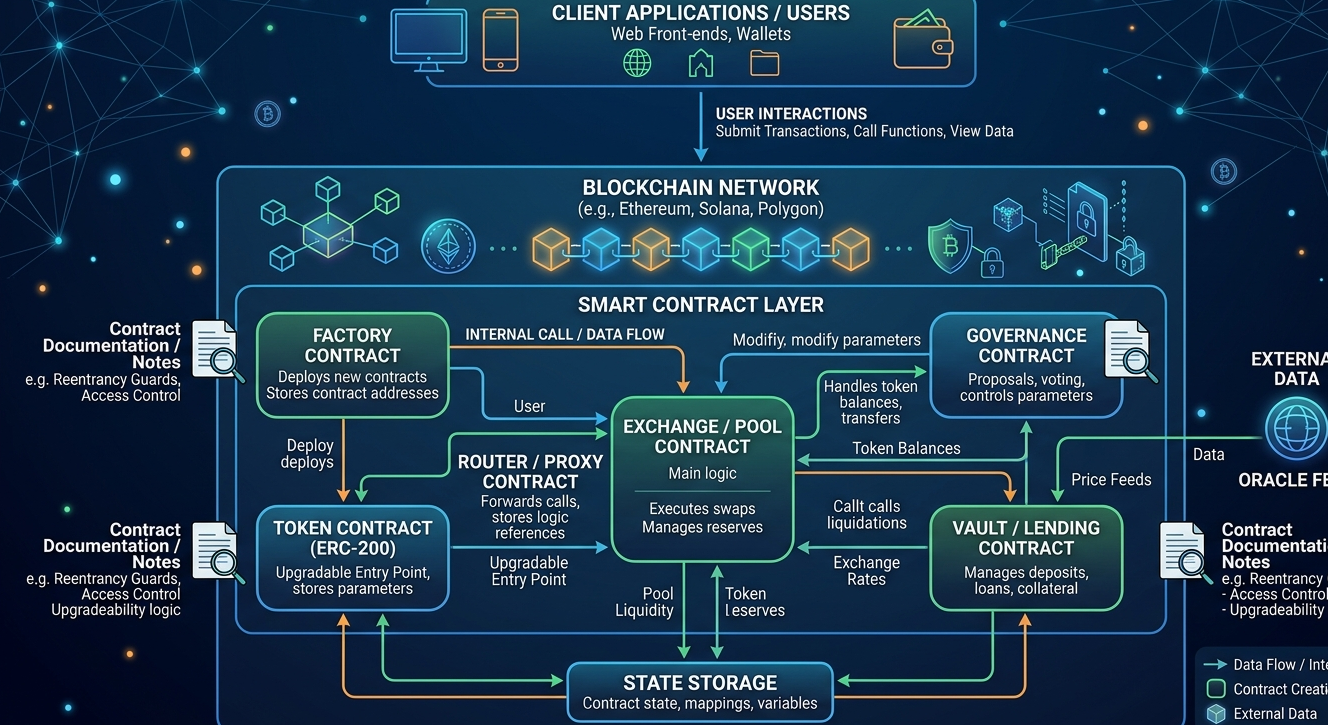
Include diagrams where they help. Even rough flowcharts showing how funds move through your system give auditors a mental model they can validate against the actual code, which is one of the most effective ways to find discrepancies between intent and implementation.
List All External Dependencies
If your contracts interact with external protocols, oracles, or token standards, document every dependency explicitly. Include the contract addresses, the functions you call, and the assumptions your code makes about the behavior of those dependencies.
External dependencies are a common source of vulnerabilities that scoped audits miss. Make sure your scope definition with the audit firm explicitly addresses how external dependencies will be handled.
Before the Audit: Security Baseline
Run Solidity Shield and Address Initial Findings
Before your code reaches a formal manual audit, run it through Solidity Shield. This gives you a comprehensive automated analysis of your Solidity code against known vulnerability patterns, identifying common issues that would otherwise consume expensive audit time.
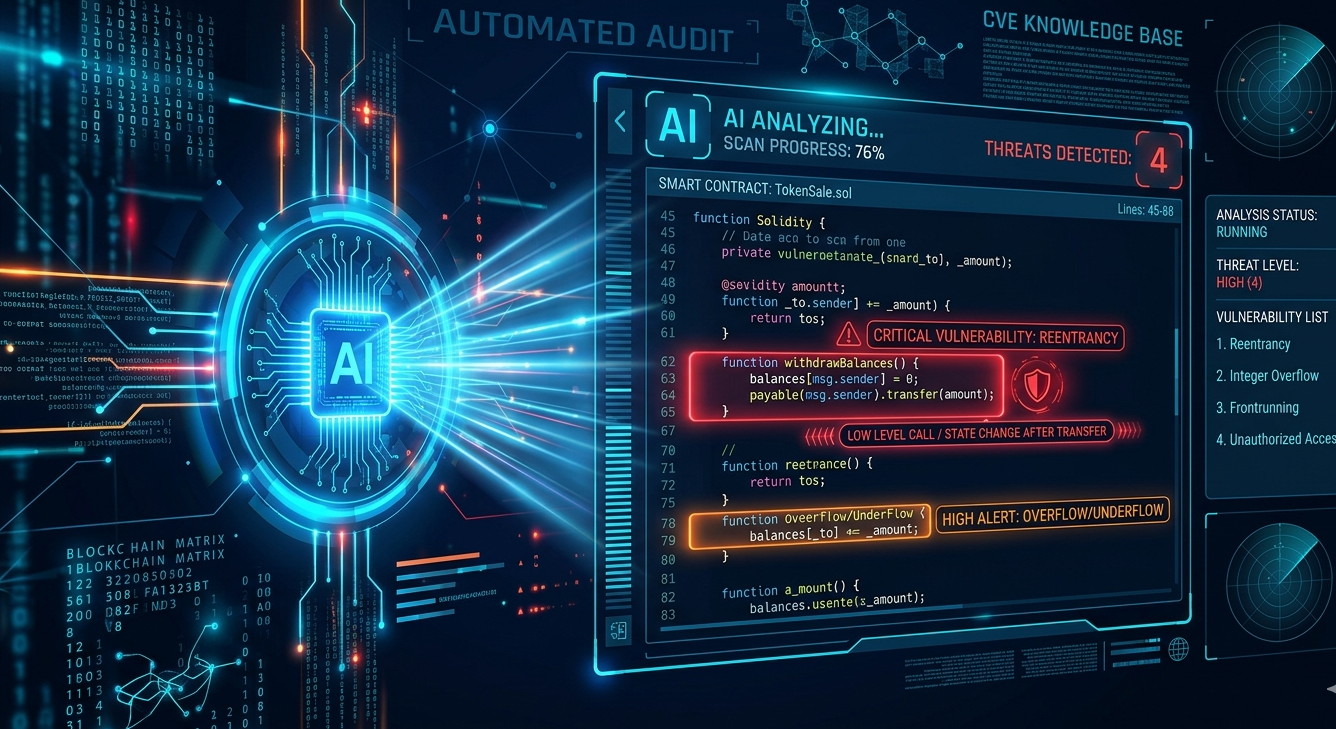
Address the findings from this analysis before the formal audit begins. When your codebase arrives at the manual review phase without common patterns, auditors can focus entirely on the complex logical and architectural issues that require human expertise. This measurably improves the depth and value of the engagement.
Run Your Test Suite to Completion
Your test suite should pass completely before audit submission. Partially failing tests or skipped tests are red flags that suggest the codebase is not at the maturity level appropriate for a security review.
More importantly, a comprehensive test suite helps auditors understand your intended behavior. When they can run your tests and observe what passes and what is expected to fail, they gain context that improves their ability to identify deviations from design intent.
Check for Known Vulnerability Patterns Yourself
Before submitting, have your own team review the codebase for the most common vulnerability classes. This includes reentrancy, unchecked external calls, integer overflow and underflow in older compiler versions, access control gaps, and improper use of tx.origin.
Finding these yourself before the audit is always better than having the auditor find them. It demonstrates codebase maturity, reduces finding count on basic issues, and focuses the audit on the vulnerabilities your team genuinely could not find.
During the Audit: Engagement Management
Assign a Single Technical Point of Contact
Designate one technically capable team member as the primary point of contact with the audit firm. This person should be able to answer questions about design intent quickly and escalate to other team members as needed.

Fragmented communication with multiple people answering questions in different ways creates confusion and slows the audit. A single knowledgeable point of contact keeps the engagement running efficiently.
Respond to Auditor Questions Quickly
Auditors regularly need clarification about intended behavior. Slow responses create delays, and delays in the middle of a manual review disrupt the auditor’s flow and concentration. Commit to responding to questions within one business day during an active engagement.
Do Not Modify the Audited Code During Review
Even if you discover an issue on your own while the audit is running, do not modify the audited codebase until the engagement is complete. Document the issue and share it with the auditor. Changes during an active review can invalidate portions of work already completed and create confusion about which version of the code applies to which findings.
After the Audit: Remediation and Review
Triage Findings by Severity Immediately
When the report arrives, your first step is to triage findings by severity. Critical and high findings require immediate attention. Review them carefully with your technical team, ensure everyone understands the vulnerability, and begin remediation planning before moving to lower severity items.
Verify Every Fix Before Marking as Resolved
Do not mark a finding as resolved based on developer confidence alone. Have the developer who implemented the fix explain specifically how it addresses the reported vulnerability. Have a second team member independently review the fix before it goes back to the auditor for verification.
Request Full Remediation Review
Every finding that was addressed must be reviewed by the auditor for confirmation. This is non-negotiable. Deployed code with unconfirmed fixes is only marginally safer than code with unaddressed findings, because you lack certainty about whether the vulnerability was actually eliminated.
Publish the Audit Report
Publishing your audit report is a meaningful trust signal for your community. It shows transparency, demonstrates that you took security seriously, and provides users with information they can factor into their own risk assessment. Most serious protocols in 2026 publish their audit reports, and the absence of a published report raises questions from sophisticated users.
The Ongoing Security Mindset
This checklist addresses the discrete event of a single audit engagement. However, smart contract security is not an event. It is a continuous practice. Every time you upgrade a contract, add a feature, or change a dependency, new risk is introduced.
Build a development culture that treats security as integral to the engineering process, not external to it. Use Solidity Shield throughout your development cycle to maintain continuous visibility into your codebase’s vulnerability profile. Treat each audit as a milestone in an ongoing process, not as the destination.
Protocols that maintain this mindset are the ones that survive. The history of blockchain exploits is largely a history of teams that treated the audit as a checkbox rather than a commitment.
Frequently Asked Questions
How early in the development process should I start thinking about audits?
From day one. Security-conscious architecture decisions made early are far cheaper than refactoring for security later. Running tools like Solidity Shield throughout development, not just before launch, is the practical expression of this principle.
What if the auditor finds a critical vulnerability in my core architecture?
Address it, even if it requires significant rework. Protocols that launch with known critical vulnerabilities because fixing them was too expensive or time-consuming rarely survive their first significant exploit. The cost of a rework is always less than the cost of a catastrophic loss.
Do I need a new audit for every update I deploy?
Not necessarily a full audit for every minor update. However, any meaningful change to contract logic, any new features, and any changes to access control or value flow should be audited. What constitutes ‘meaningful’ requires judgment, but when in doubt, audit.
Can running Solidity Shield replace the need for a formal audit?
No. Solidity Shield is a powerful automated analysis tool that significantly strengthens your security baseline. However, for protocols handling substantial user funds, it complements rather than replaces expert manual review. It prepares your code for the most effective manual audit possible.
How do I handle audit findings that I believe are false positives?
Document your reasoning clearly and present it to the auditor. Include the specific design intent behind the relevant code and your explanation of why the reported concern does not constitute a real vulnerability in context. Good auditors engage with this dialogue seriously and will either agree, or explain more clearly why the vulnerability is real.



