Language choice is a security decision. In the smart contract world, this reality is more consequential than almost anywhere else in software development. The language you write in shapes what mistakes you can make, what tools can protect you, and what attack surfaces your protocol exposes to the world.
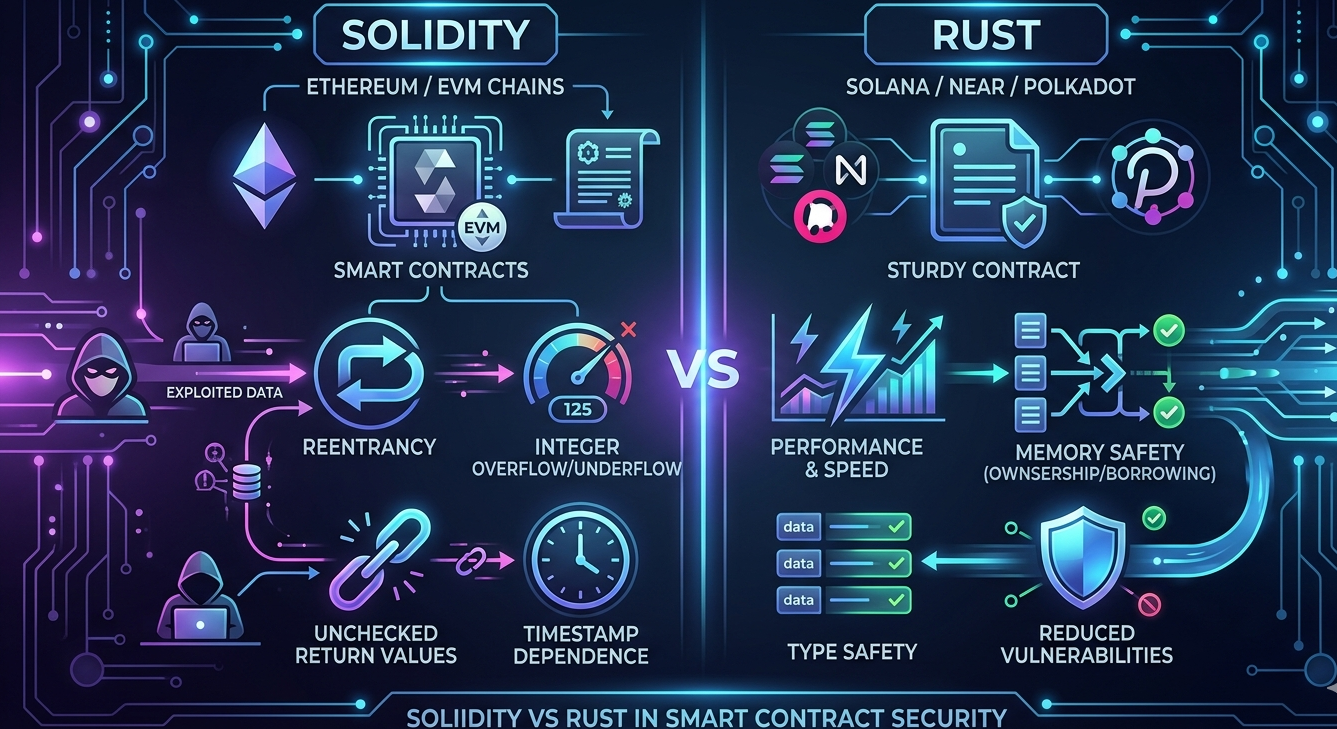
The debate between Solidity and Rust has intensified as Rust-based blockchains like Solana, NEAR, and Polkadot have grown significantly. For teams building cross-chain protocols or evaluating which ecosystem to build in, understanding how these languages compare on the security dimension is not just interesting. It is strategically important.
A Brief Orientation: Where Each Language Lives
Solidity is the dominant language of the Ethereum Virtual Machine ecosystem. It was designed specifically for smart contract development and runs on Ethereum, Polygon, BNB Chain, Avalanche, and dozens of other EVM-compatible networks. The EVM ecosystem represents the largest concentration of on-chain value in Web3.
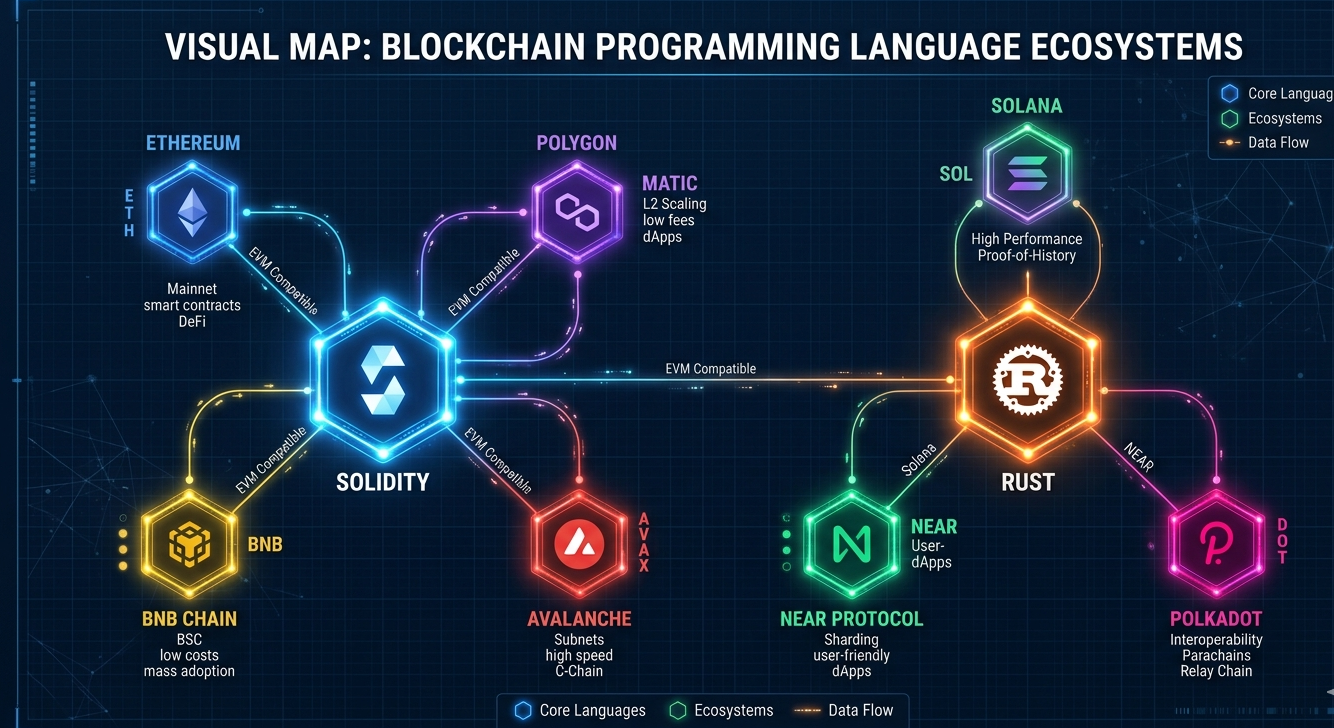
Rust was not designed for smart contracts. It is a general-purpose systems programming language prioritizing memory safety and performance. It has been adopted as the primary language for Solana’s Sealevel runtime, as well as for Near Protocol and Polkadot’s Substrate framework. Its adoption in blockchain is driven by its performance characteristics and the safety guarantees its type system provides.
Rust’s Memory Safety Model and What It Means for Security
Rust’s most celebrated security feature is its ownership model. At compile time, Rust enforces rules about how memory is allocated, accessed, and freed. These rules make entire categories of memory-related vulnerabilities impossible by design. Buffer overflows, use-after-free errors, and null pointer dereferences simply cannot occur in safe Rust code.
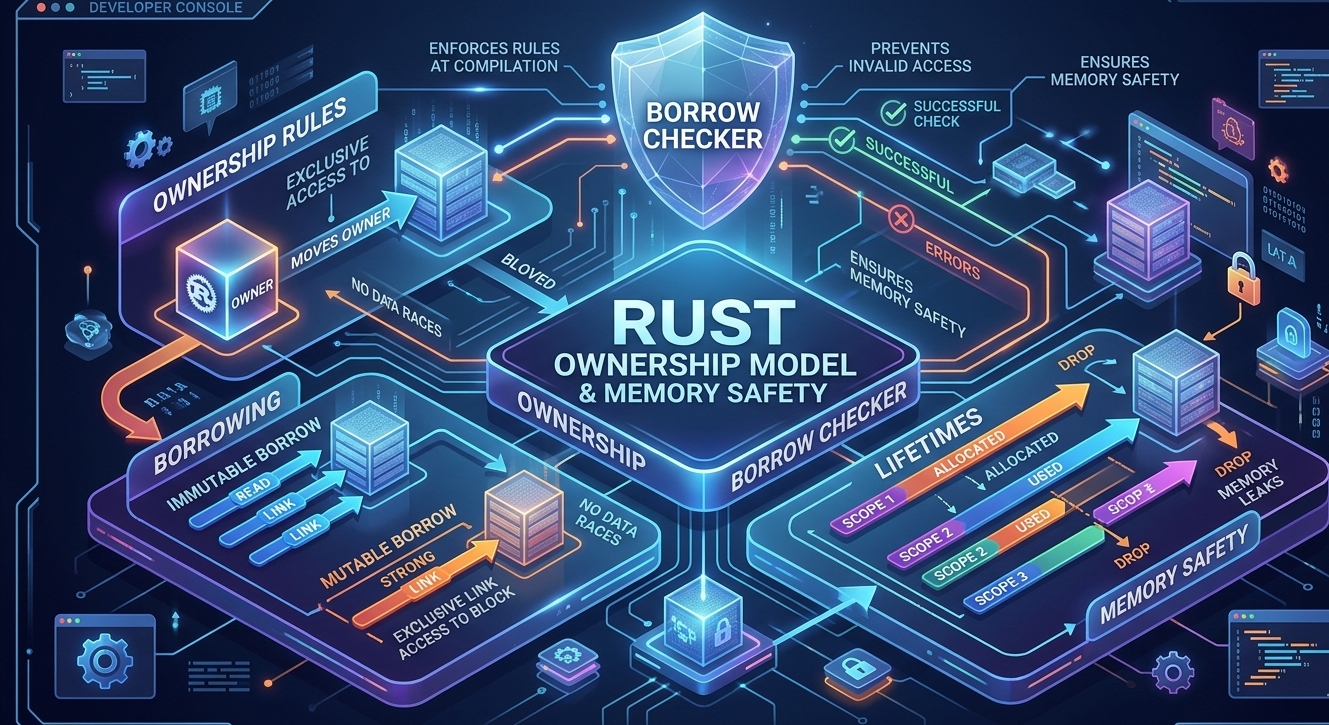
For traditional software, these guarantees represent a massive security improvement over languages like C or C++. In a blockchain context, however, the most impactful smart contract vulnerabilities are not memory errors. They are logic errors, economic design flaws, and reentrancy patterns. Rust’s memory safety guarantees do not directly address these categories.
Additionally, Rust programs can include unsafe blocks where the memory safety guarantees are suspended. Solana programs, in particular, often require unsafe code for cross-program invocations and account deserialization. The presence of unsafe code reintroduces the risk categories that Rust’s ownership model was supposed to eliminate.
Solidity’s Known Vulnerability Landscape
Solidity has a well-documented set of vulnerability patterns. Reentrancy, integer overflow and underflow, unchecked external calls, front-running exposure, delegate call misuse, and access control errors are the most common sources of exploits in the EVM ecosystem. These patterns are well-understood, extensively documented, and addressed by a mature tooling ecosystem.
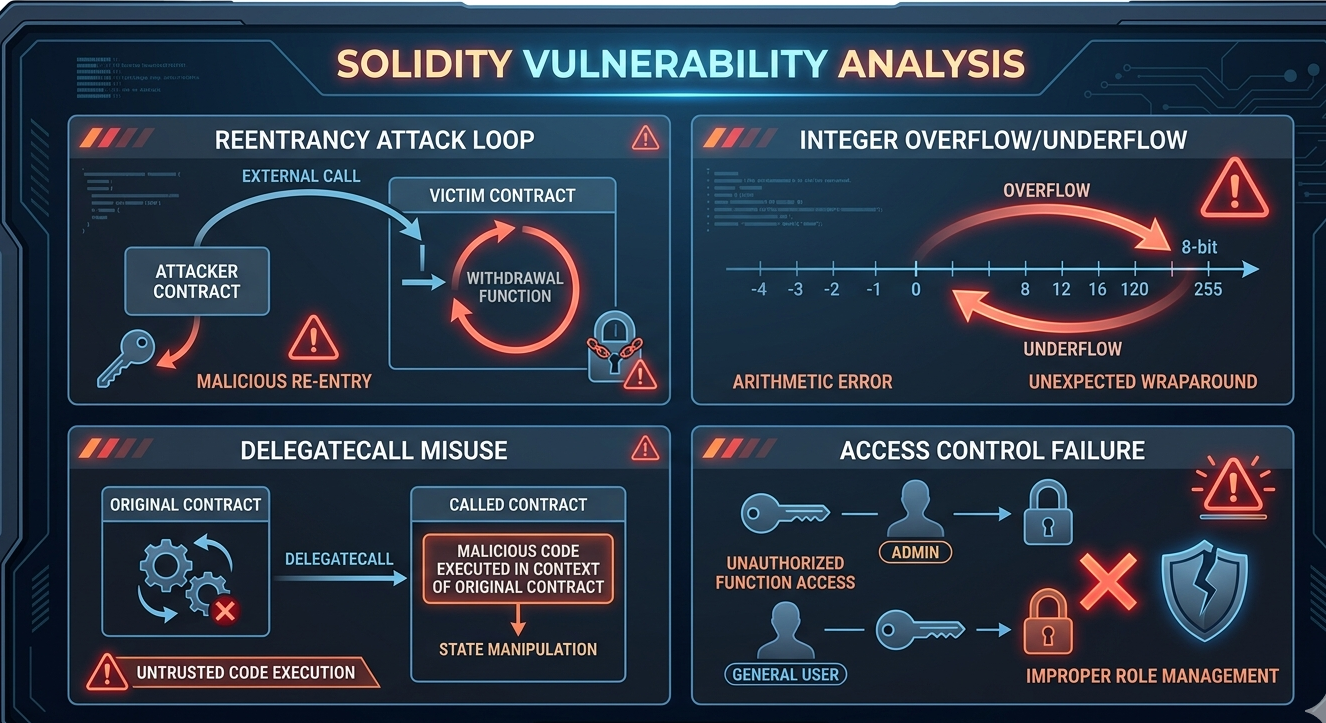
Importantly, many of these vulnerability classes have been substantially mitigated by compiler-level improvements and language evolution. Solidity 0.8 introduced automatic integer overflow protection. Modern access control patterns and security libraries have dramatically reduced the frequency of certain vulnerability classes. The language has matured significantly since the early DAO exploit era.
The flip side of Solidity’s well-documented vulnerability landscape is that attackers know exactly what to look for. The fact that reentrancy attacks still occur is partly because the tooling ecosystem has not been uniformly adopted. Protocols that do not use security analyzers, skip audits, or rely on outdated patterns remain vulnerable to attacks that the community has understood for years.
Rust Smart Contract Vulnerabilities: Less Known, Not Fewer
A common misconception is that Rust’s safety guarantees translate into safer smart contracts in general. This is not accurate. Rust-based smart contracts have their own distinct vulnerability patterns that are less widely understood and for which the tooling ecosystem is considerably less mature.
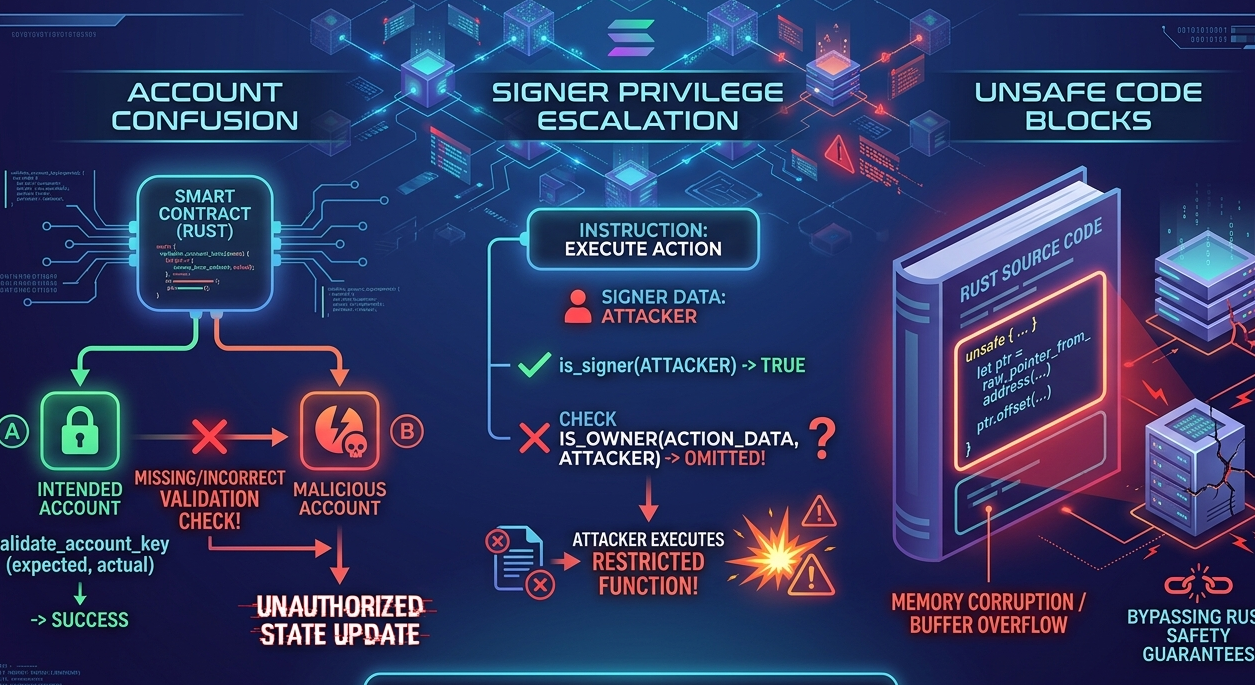
Solana programs, for instance, are vulnerable to account confusion attacks where a program fails to properly validate the type or ownership of accounts passed to it. Arithmetic overflow in Rust does not panic in release mode by default, creating a subtle vulnerability that has been exploited on Solana. Cross-program invocation vulnerabilities introduce trust assumption errors that the compiler cannot detect. Signer privilege escalation is a specific Solana vulnerability class with no direct equivalent in EVM development.
Because the Solana and Rust-based smart contract security ecosystem is younger, the tooling, audit firm expertise, and documented remediation patterns are less mature than their Solidity equivalents. A Rust-based smart contract is not inherently more secure. It faces different risks in a less well-equipped defensive environment.
The Tooling and Ecosystem Advantage
This is where Solidity’s maturity becomes a genuine security advantage. The EVM smart contract security ecosystem is the most developed in Web3. Solidity has benefited from years of adversarial pressure, community research, and tooling investment. The result is a comprehensive defensive infrastructure that Rust-based ecosystems have not yet replicated.

Solidity Shield is a direct product of this ecosystem maturity. Built specifically for Solidity and EVM smart contracts, it combines automated static analysis with expert review capabilities that leverage years of accumulated knowledge about how EVM contracts fail. The vulnerability database it draws on represents the distilled lessons of every significant EVM exploit, translated into detection rules that protect against recurrence.
For teams building on EVM chains, the availability of tools like Solidity Shield, combined with a deep pool of experienced auditors, a large community of security researchers, and extensive documentation of known attack patterns, means that effective security is achievable at a level that Rust-based ecosystems have not yet matched.
Economic and Incentive Considerations
Security is not just about language design. It is also about incentive structures. The EVM ecosystem, with its concentration of high-value protocols, attracts the most sophisticated security researchers and the largest bug bounty programs. This creates a security pressure gradient that continuously surfaces and addresses vulnerabilities.
Solana and other Rust-based ecosystems have their own security research communities, but the concentration of value and the density of expert attention are not yet comparable to Ethereum. For a protocol, this matters. More researchers means more scrutiny. More scrutiny means fewer undetected vulnerabilities surviving to the deployment stage.
Furthermore, the audit firm ecosystem for EVM contracts is significantly more developed. There are more qualified firms, more published research, and more competitive pricing for Solidity audits than for Rust-based contract audits. For teams making practical decisions about security investment, this availability difference is material.
Where Rust Genuinely Excels
Acknowledging Rust’s genuine advantages is important for an honest comparison. Rust’s type system provides compile-time guarantees that catch a class of errors before they ever become runtime vulnerabilities. For protocol logic where invariants can be expressed in the type system, this provides meaningful assurance.
Additionally, Rust’s performance characteristics allow for more computationally intensive on-chain logic without hitting execution limits. For protocols that require complex computation, Rust may enable designs that are not practical in Solidity within EVM gas constraints.
Rust is also evolving rapidly in the blockchain context. Formal verification tooling, specialized security analyzers, and best practice documentation are advancing. The gap between the EVM and Rust ecosystems in terms of security tooling maturity may narrow significantly over the next few years.
A Realistic Security Assessment
Both languages produce exploitable smart contracts when used carelessly. Both require dedicated security tooling, expert auditing, and continuous attention to emerging vulnerability patterns. Neither provides security by default.
For teams choosing between ecosystems today, the practical security advantage lies with Solidity and EVM due to the maturity of the defensive ecosystem. The vulnerabilities are better understood, the tooling is more advanced, and the community knowledge is deeper. Solidity Shield exemplifies this advantage, providing a level of automated security analysis for Solidity contracts that has no direct equivalent for Rust-based smart contracts.
For teams already building on Rust-based chains, the most important security investment is recognizing that Rust’s memory safety guarantees are not sufficient and that dedicated smart contract security practices, including expert audit review and property-based testing, are just as necessary as they are in the EVM ecosystem.
The Future of Smart Contract Security Across Languages
As the blockchain space matures, the security tooling gap between EVM and non-EVM ecosystems will likely narrow. Cross-chain protocols are already pushing the industry toward security practices that apply consistently regardless of underlying language. The fundamental principles of smart contract security, defense in depth, continuous testing, expert review, and post-deployment monitoring, are not language-specific.
However, for the present, teams building in Solidity benefit from the most developed security infrastructure in Web3. The combination of language evolution, tooling maturity, and ecosystem knowledge represented by solutions like Solidity Shield provides meaningful security advantages that should factor into technology and ecosystem decisions.
Conclusion
The Solidity versus Rust debate in smart contract security does not have a simple winner. Both languages produce vulnerable contracts when security is deprioritized. Both can produce robust contracts when security practices are applied seriously.
The practical security advantage today lies with Solidity for teams building in the EVM ecosystem. The defensive infrastructure, tooling maturity, and community knowledge available through solutions like Solidity Shield represent years of accumulated learning that makes effective security more achievable. As Rust-based ecosystems continue to evolve, the gap may narrow. For teams making decisions in the current environment, however, the security ecosystem advantage of EVM development is real and meaningful.
FAQ: Solidity vs Rust Smart Contract Security
1. Does Rust’s memory safety make Solana contracts more secure than Ethereum contracts?
Not necessarily. Rust’s memory safety prevents a class of low-level vulnerabilities, but the most significant smart contract exploits across both ecosystems involve logic errors and economic flaws, not memory errors. Each platform has distinct vulnerability patterns.
2. What are the most common vulnerabilities in Rust-based smart contracts?
Account confusion attacks, arithmetic overflow in release mode, cross-program invocation trust errors, and signer privilege escalation are among the most significant Rust smart contract vulnerability classes, particularly on Solana.
3. Is there equivalent tooling for Rust smart contracts as there is for Solidity?
Not yet at the same maturity level. The EVM ecosystem has significantly more advanced tooling, more experienced audit firms, and more documented vulnerability patterns than the Rust smart contract ecosystem.
4. How does Solidity Shield help teams secure EVM contracts?
Solidity Shield combines automated static analysis with expert review to detect the full spectrum of known EVM vulnerability classes. It is built on years of accumulated knowledge about how Solidity contracts fail, providing protection that benefits directly from the EVM ecosystem’s security maturity.
5. Should language choice be a primary security consideration when building a protocol?
Language choice matters, but the security discipline applied within that language matters more. A well-audited Solidity contract using proven patterns is significantly safer than an unaudited Rust contract, despite any theoretical language-level advantages.



