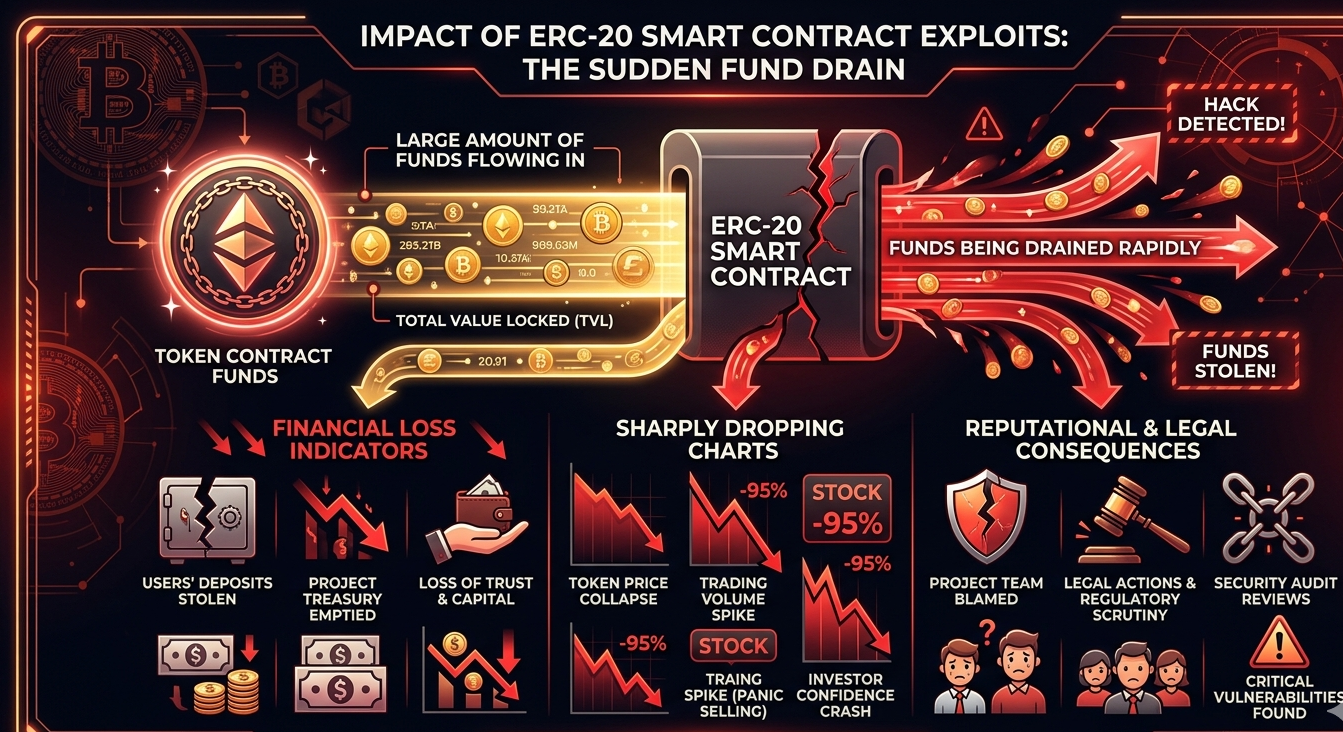
Every token launch starts with confidence. It ends, far too often, with an exploit. In 2023 alone, smart contract vulnerabilities across ERC-20 tokens contributed to over a billion dollars in losses across DeFi ecosystems. If your token contract has a flaw, it does not matter how strong your tokenomics are or how large your community is. One critical vulnerability can render everything worthless in minutes.
Smart contract security is not optional for ERC-20 tokens. It is the foundation on which every other promise you make to investors, holders, and stakeholders rests. Yet most teams treat auditing as a checkbox rather than a process. They run a quick tool scan, submit to one audit firm, and call it done. That approach is dangerously insufficient.
This guide breaks down exactly how to audit ERC-20 smart contracts for security risks. You will learn what vulnerabilities to look for, what the audit process should involve, and how to approach security in a way that actually protects your token from real-world threats.
Why ERC-20 Contracts Are High-Value Targets
ERC-20 tokens power the majority of DeFi protocols, ICOs, DAOs, and on-chain economies. This makes them among the most targeted contract types in the blockchain ecosystem. Attackers understand that a single flaw in a widely deployed token contract can be exploited repeatedly before anyone notices.
Furthermore, ERC-20 contracts often interact with liquidity pools, staking contracts, and governance modules. This creates an expanded attack surface. A vulnerability that seems minor in isolation can become catastrophic when combined with another protocol’s logic.
Moreover, the ERC-20 standard itself is deceptively simple. It defines a clear interface, but the implementation details are where security breaks down. Developers often reuse code snippets, introduce subtle logic errors, or overlook how their contract behaves under adversarial conditions.
Understanding the ERC-20 Standard Before You Audit
Before diving into the audit process, it is important to understand what makes ERC-20 contracts distinct. The standard defines six mandatory functions: totalSupply, balanceOf, transfer, transferFrom, approve, and allowance. Each of these functions carries its own set of known attack vectors.
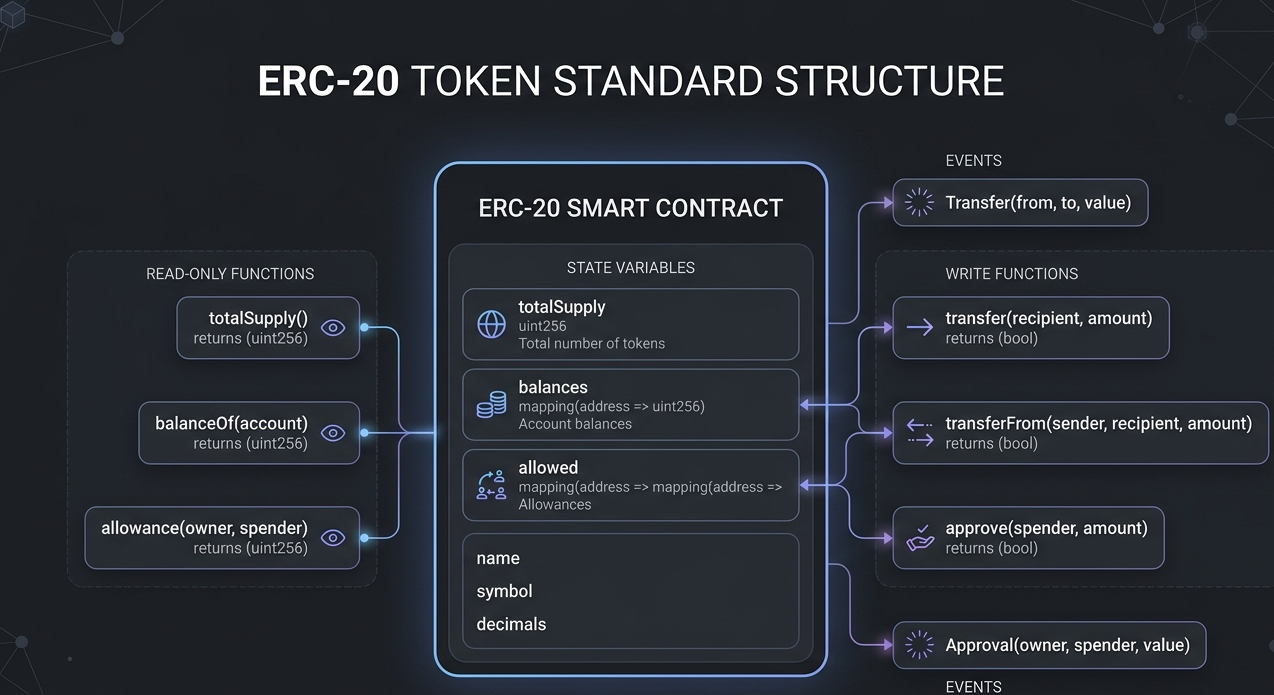
The approve and transferFrom combination, for example, is notorious for enabling front-running attacks. When a user calls approve to change an allowance from one value to another, an attacker watching the mempool can exploit the window between the two states. This is called the ERC-20 race condition, and it has been known for years. Yet many contracts are still deployed without protection against it.
Therefore, understanding what each function is supposed to do is step one. Auditing it is step two. And understanding how it can be abused is the step most teams skip entirely.
Core Smart Contract Security Vulnerabilities in ERC-20 Tokens
Reentrancy Attacks
Reentrancy is one of the most well-documented vulnerabilities in Solidity development, yet it still appears in production contracts. In ERC-20 tokens, reentrancy most commonly surfaces in contracts that extend base functionality, such as those with minting hooks, callback mechanisms, or token receiver patterns.
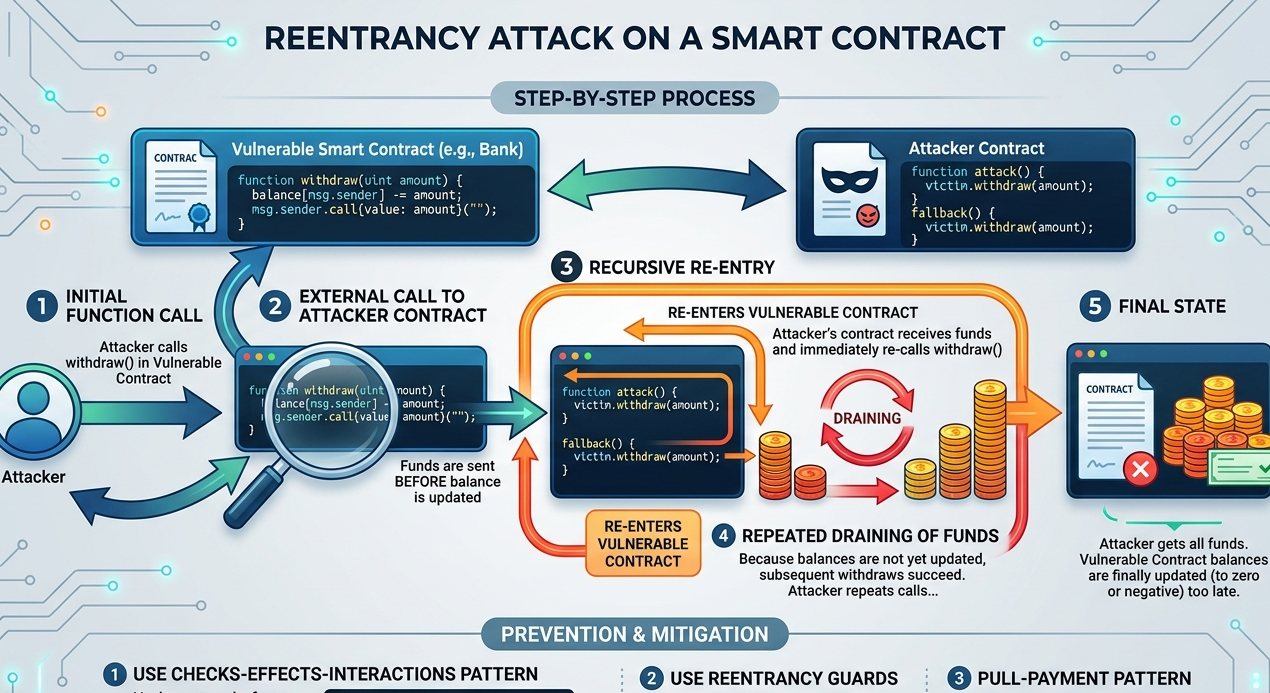
The attack works by recursively calling back into the target contract before the first execution completes. As a result, an attacker can drain balances or mint tokens far beyond intended limits. The fix is straightforward with proper checks-effects-interactions patterns, but only if the developer knows to apply them.
Integer Overflow and Underflow
In older Solidity versions below 0.8.0, arithmetic operations did not revert on overflow or underflow. This meant that adding to a maximum uint256 value would silently wrap back to zero. In token contracts, this could be exploited to manipulate balances, allowances, or supply values.
While Solidity 0.8.0 introduced built-in overflow checks, many production contracts are still running on older compilers. Additionally, contracts using unchecked blocks for gas optimization can reintroduce this vulnerability if not handled carefully.
Access Control Flaws
Many ERC-20 tokens include administrative functions such as minting, burning, pausing, or upgrading the contract. When these functions lack proper access control, they become a direct pathway for attackers or malicious insiders to manipulate token supply or disable contract functionality.

Common mistakes include using tx.origin instead of msg.sender for authorization, failing to properly implement role-based access control, and leaving owner functions unprotected in test or staging environments that were accidentally deployed to mainnet.
Front-Running and MEV Vulnerabilities
Maximal Extractable Value, or MEV, has become a sophisticated threat in modern DeFi. For ERC-20 contracts, front-running during approval updates or large transfers can result in significant financial losses for users. Notably, sandwich attacks on token swap transactions are a direct consequence of poor front-running protection.
Incorrect Event Emissions
Events are how off-chain systems track on-chain activity. When events are emitted incorrectly, or not emitted at all, it creates a disconnect between actual contract state and what external systems believe is happening. This can be exploited to confuse indexers, oracles, and monitoring tools.
The ERC-20 Smart Contract Security Audit Process

Step 1: Automated Vulnerability Scanning
The audit process should begin with automated tools that flag common vulnerability patterns. These tools can scan for reentrancy risks, unchecked return values, arithmetic issues, and known Solidity anti-patterns. However, automated scanning alone is never sufficient. It provides a starting point, not a conclusion.
Tools like static analyzers can detect syntactic and structural issues, but they cannot reason about business logic. An audit that relies entirely on tooling will miss the vulnerabilities that matter most.
Step 2: Manual Code Review
Manual review is where real smart contract security expertise shows its value. An experienced auditor reads the code the way an attacker would, looking for edge cases, logic flaws, and unexpected interactions between functions.
During manual review, the auditor should trace every execution path, check every state-changing function, verify that access controls are correctly implemented, and confirm that tokenomics behave as intended under adversarial conditions.
Step 3: Formal Verification
Formal verification uses mathematical proofs to confirm that a contract behaves correctly under all possible inputs. It is the most rigorous form of security analysis available for smart contracts. For high-value ERC-20 tokens, formal verification of critical functions like transfer and approve can provide a level of assurance that manual review alone cannot.
Step 4: Economic and Game Theory Analysis
Security is not only about code. It is also about incentives. An auditor should consider how rational actors would behave given the contract’s mechanics. Can someone profit from manipulating the token supply? Does the staking design create perverse incentives? Are there flash loan attack surfaces in associated contracts?
Step 5: Test Coverage Verification
A contract without comprehensive tests is a contract that has not been properly challenged. Auditors should verify that the development team has tested all edge cases, boundary conditions, and failure modes. Low test coverage is itself a red flag and an indicator of deeper security risks.
Common Audit Mistakes That Miss Real Risks
One of the most common mistakes is treating an audit as a one-time event. Smart contracts do not exist in isolation. Protocols evolve, integrations change, and new attack vectors emerge. A contract that was secure at deployment may become vulnerable six months later due to changes in connected protocols or broader ecosystem dynamics.
Another frequent mistake is auditing only the main token contract while ignoring peripheral contracts. Vesting schedules, governance contracts, staking pools, and bridge integrations all interact with the token and can introduce vulnerabilities that affect its security.
Furthermore, many teams focus exclusively on what the contract does rather than what it could be made to do. The attack surface includes every external call, every integration point, and every assumption the contract makes about external systems.
How Solidity Shield Strengthens ERC-20 Audit Quality
Solidity Shield by SecureDApp is a smart contract auditing platform designed specifically to address the gaps that traditional audits leave behind. It combines automated vulnerability detection with deep manual analysis to deliver comprehensive smart contract security assessments for ERC-20 tokens and beyond.
Where generic audit tools scan for known patterns, Solidity Shield is built around the full threat landscape of Solidity development. It identifies reentrancy vectors, access control weaknesses, arithmetic edge cases, and business logic flaws in a structured and repeatable way.
For ERC-20 tokens specifically, Solidity Shield examines the complete token lifecycle, from minting and distribution to staking integrations and bridge interactions. This end-to-end perspective ensures that no part of the token’s attack surface goes unexamined.
Moreover, Solidity Shield delivers findings in a format that developers can actually act on. Vulnerability reports are prioritized by severity, mapped to specific code locations, and paired with remediation guidance. This reduces the time between finding a vulnerability and fixing it, which is critically important for teams working under launch deadlines.
Post-Audit Security Practices for ERC-20 Tokens
An audit is a point-in-time assessment. Smart contract security requires ongoing attention. After the audit is complete, teams should establish a clear process for reviewing any contract changes against the audit findings. Even small modifications can reintroduce vulnerabilities that were previously resolved.
Additionally, teams should consider setting up a bug bounty program to incentivize ethical disclosure of vulnerabilities. This creates a continuous feedback loop from the broader security community and acts as a complement to formal auditing.
Finally, monitoring contract activity on-chain provides early warning of unusual behavior. Even a fully audited contract can behave unexpectedly in response to novel attack patterns or unexpected usage.
Real-World Scenario: What a Missed Vulnerability Looks Like
Consider a DeFi project that launched an ERC-20 token with a staking mechanism. The token contract passed an automated scan without critical findings. However, a manual auditor later identified that the staking contract used the approve-then-transferFrom pattern without any front-running protection.
During a large liquidity event, an attacker exploited the approval race condition to intercept tokens mid-transfer. The project lost several hundred thousand dollars in a matter of minutes. The vulnerability had existed since deployment. No automated tool had caught it because the logic was correct in isolation. It only became dangerous in context.
This scenario illustrates precisely why smart contract security for ERC-20 tokens requires both technical depth and contextual understanding. Solidity Shield is designed to provide both.
Conclusion
Auditing ERC-20 smart contracts is not a single step. It is a structured process that combines automated scanning, manual code review, formal verification, and economic analysis. Each layer catches what the others might miss. Together, they form a defense that is genuinely robust.
Smart contract security determines whether your token can be trusted. And trust, in the blockchain ecosystem, is everything. If you are building or launching an ERC-20 token, do not wait until after deployment to think about security. Start with a thorough audit, use the right tools, and maintain that vigilance over time.
Solidity Shield provides the technical depth and structured methodology your ERC-20 token deserves. Because the cost of a missed vulnerability is always greater than the cost of a thorough audit.
Frequently Asked Questions
1. What is the most critical vulnerability to check in an ERC-20 smart contract?
Access control flaws and reentrancy are among the most critical issues to identify. Access control vulnerabilities can allow unauthorized minting or burning of tokens. Reentrancy can allow attackers to drain balances through recursive calls. Both require manual review to detect reliably.
2. Can automated tools fully audit an ERC-20 contract?
No. Automated tools are excellent at detecting known patterns and syntactic issues, but they cannot reason about business logic, economic incentives, or cross-contract interactions. A thorough audit always requires manual expert review in addition to automated scanning.
3. How long does an ERC-20 smart contract audit take?
For a standard ERC-20 token contract, a thorough audit typically takes between five and fourteen days depending on complexity, the number of integrated contracts, and the depth of testing required. More complex tokens with staking or governance modules require additional time.
4. What should I do after receiving an audit report?
Prioritize critical and high-severity findings immediately. Work with your development team to remediate all identified issues before deployment. After fixes are applied, request a re-audit to verify that remediations are correct and have not introduced new issues.
5. Is one audit enough for a production ERC-20 token?
A single audit provides a point-in-time assessment. If the contract is modified after the audit, or if it integrates with new protocols, additional review is necessary. For high-value tokens, continuous monitoring and periodic re-audits provide stronger long-term security assurance.



