Introduction: The Marketplace Is Only as Safe as Its Chain

NFT marketplaces handle billions of dollars in digital asset transactions every year. They are not just trading platforms. They are ecosystems where ownership, identity, and value converge on-chain.
But here is the uncomfortable truth. Most NFT marketplaces are breached not through brute force. They fall because of weak smart contract logic, unmonitored on-chain activity, and delayed threat response.
In 2021, the Poly Network hack drained over $600 million in minutes. In 2022, OpenSea lost $1.7 million in a phishing-linked exploit. These were not random events. They were predictable failures in on-chain security coverage.
Real-time blockchain threat monitoring is no longer a luxury. For NFT marketplaces, it is survival infrastructure.
This blog explores what on-chain threats look like, how they evolve, and what it takes to build a truly protected NFT marketplace.
Understanding the NFT Marketplace Attack Surface

Before building protection, you must understand what you are protecting.
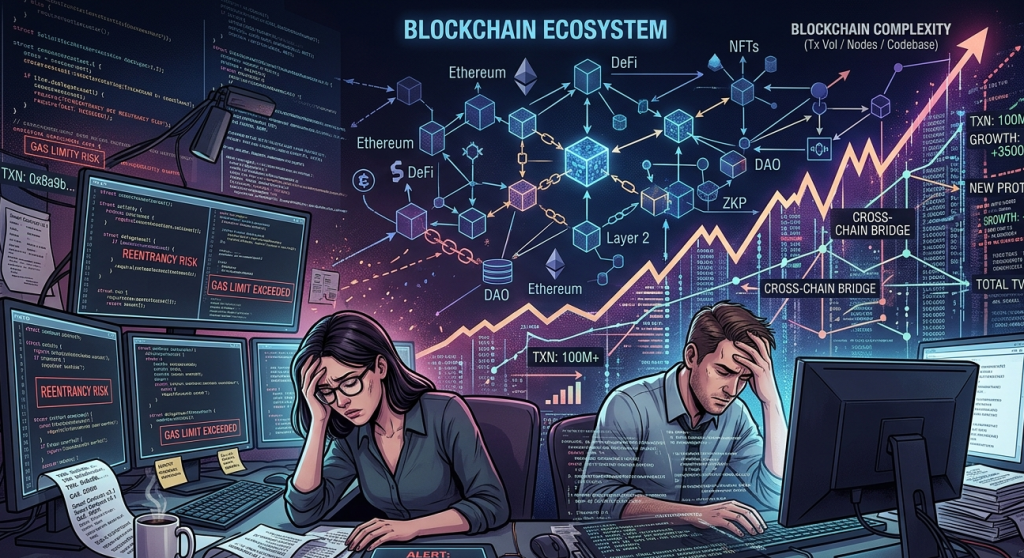
An NFT marketplace is not a single contract. It is a web of interdependent components. Each layer carries its own risk profile.
Smart Contracts govern minting, transfers, royalties, and listings. A single unchecked function can drain the entire platform.
Frontend Interfaces can be hijacked to redirect users to malicious contracts. Many attacks begin here, not on-chain.
Off-Chain Metadata stored on centralised servers can be altered to manipulate NFT appearances and perceived value.
Bridge Protocols connecting multiple blockchains introduce additional attack vectors that most security teams overlook.
Wallet Integrations carry signature manipulation risks. Attackers can trick users into approving unlimited token spend.
When you map this attack surface, one thing becomes clear. Threats do not wait for your next audit. They happen in real time, on-chain, round the clock.
What Is Real-Time Blockchain Threat Monitoring?
Real-time blockchain threat monitoring is the continuous surveillance of on-chain activity to detect, flag, and respond to malicious behaviour as it happens.
It is not a quarterly smart contract audit. It is not a bug bounty programme. It is a live, always-on security layer.
Here is what it covers:
Transaction Anomaly Detection identifies unusual patterns in asset transfers, sudden large withdrawals, or repeated failed calls that indicate probing activity.
Smart Contract Event Monitoring watches emitted events from contracts in real time. Unexpected ownership changes or mass token burns trigger immediate alerts.
Gas Price Spike Analysis can signal frontrunning bots or sandwich attacks targeting marketplace liquidity.
Blacklisted Address Screening checks every wallet interacting with your platform against known malicious addresses and sanctioned entities.
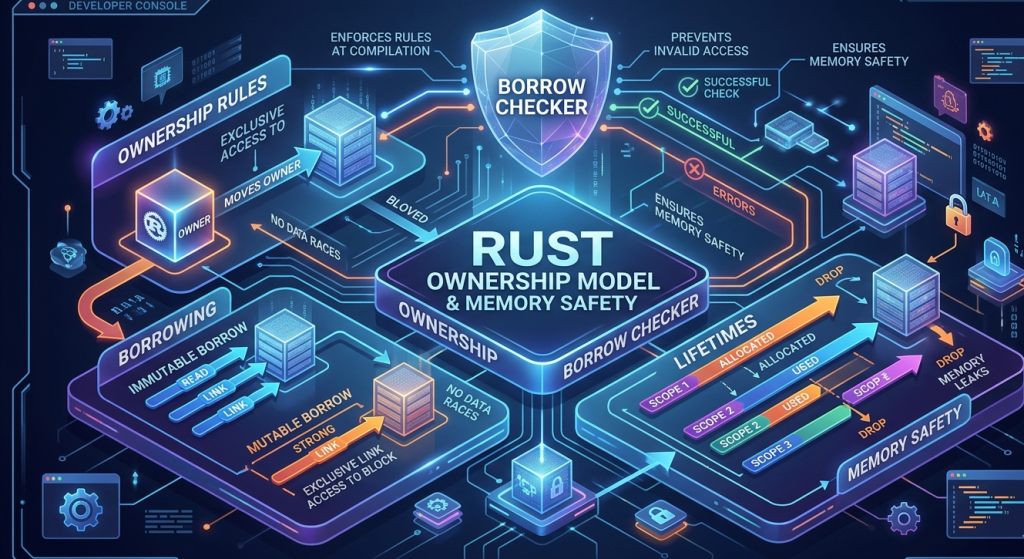
Re-entrancy Attack Detection monitors recursive call patterns that historically drain contract funds within a single transaction.
For NFT marketplaces specifically, this monitoring must happen at the block level. Every new block is a potential threat window.
Why Static Audits Are No Longer Enough
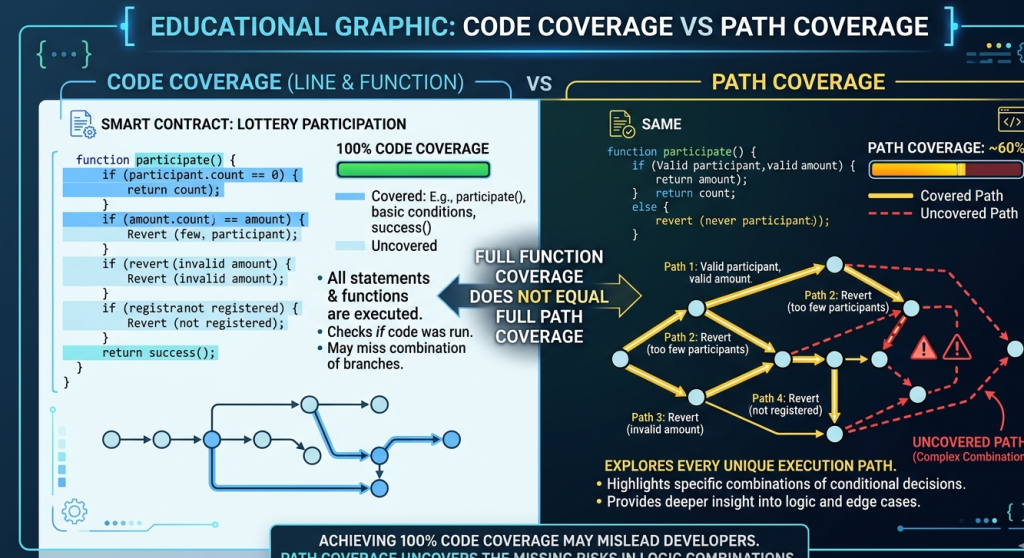
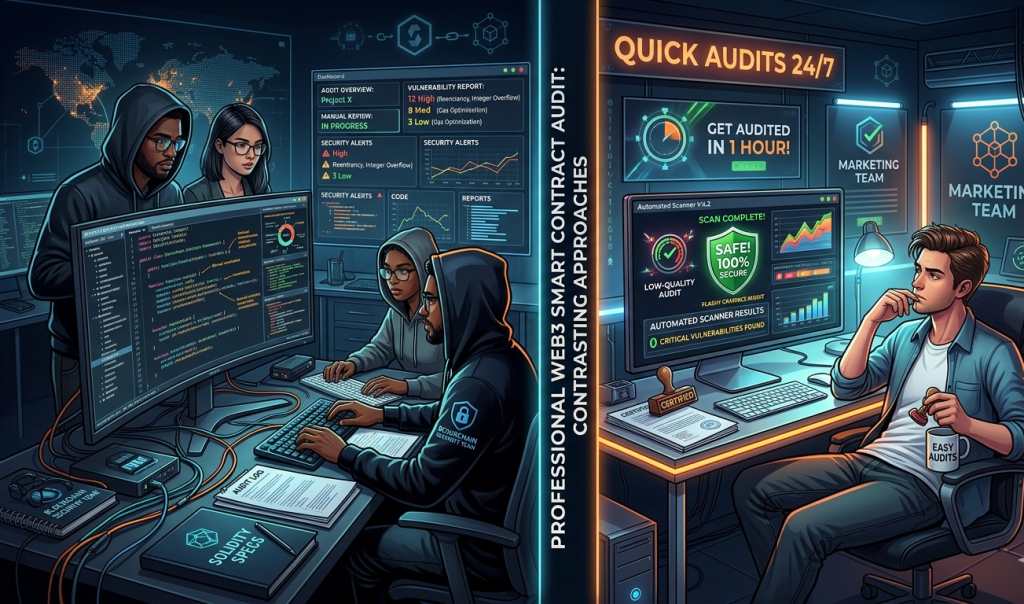
Smart contract audits are essential. No one disputes that. But an audit is a photograph. It captures a moment in time.
Your marketplace, however, is a living system. It gets upgraded. New integrations are added. User behaviour evolves. Threat actors adapt their methods.
A contract that was clean at audit time can become vulnerable after a protocol upgrade. A third-party dependency can introduce a zero-day. A new token standard can interact with your contract in ways nobody tested.
Audits catch what is already written. Real-time blockchain threat monitoring catches what is happening right now.
The two work together, but they are not interchangeable. Replacing one with the other creates blind spots that attackers love to exploit.
At SecureDApp, we approach this holistically. Our smart contract auditing service identifies vulnerabilities in your codebase. Our on-chain monitoring service then watches your deployed contracts continuously, closing the gap between audit and runtime.
Common On-Chain Threats in NFT Marketplaces
Let us get specific about the threats that real-time monitoring must address.
1. Reentrancy Exploits
Reentrancy attacks are among the oldest and most dangerous vulnerabilities. An attacker calls a contract function repeatedly before the first execution completes. The contract sends funds each time, draining its balance.
The 2016 DAO hack used this exact method. It is still happening today in newer forms. Real-time monitoring can detect the recursive call patterns before the drain is complete.
2. Flash Loan Attacks
Flash loans allow borrowing large amounts within a single transaction, no collateral needed. Attackers use these to manipulate NFT floor prices, exploit pricing oracles, or drain liquidity pools.
Monitoring for sudden, unusually large loan-and-return patterns in the same block helps detect this threat early.
3. Phishing-Linked Smart Contracts
Attackers deploy lookalike contracts that appear legitimate. Users interact with them, unknowingly signing approvals that drain their wallets.
Real-time address screening and contract similarity checks can flag these before widespread exposure.
4. Royalty Manipulation
Some marketplaces allow creators to set royalty percentages on-chain. Attackers exploit writable royalty functions to redirect payments to attacker-controlled wallets.
Monitoring royalty parameter changes in real time catches this manipulation quickly.
5. Metadata Manipulation
While metadata often lives off-chain, IPFS CID substitutions or centralised server compromises can change what an NFT looks like or represents.
Linking on-chain CID hashes with active integrity monitoring detects changes immediately.
6. Wash Trading and Price Manipulation
Coordinated accounts buy and sell NFTs between themselves to artificially inflate prices. This misleads genuine buyers and distorts market data.
Pattern recognition in wallet clustering and transaction frequency can expose wash trading networks.
Building Real-Time Protection: The Technical Architecture
A robust real-time blockchain threat monitoring system for an NFT marketplace has several core components working together.
Event Indexer and Block Listener
This layer connects directly to blockchain nodes and processes every new block. It indexes contract events, tracks state changes, and feeds data into the analysis engine.
For EVM-compatible chains like Ethereum and Polygon, this means subscribing to eth_subscribe via WebSocket connections and parsing logs against known ABI signatures.
Rule-Based Alert Engine
Predefined rules trigger alerts based on known attack patterns. For example, a rule might fire when any single address withdraws more than 10 ETH within two consecutive blocks.
Rules can be customised per marketplace and updated as new threat patterns emerge without redeploying the entire monitoring stack.
Machine Learning Anomaly Detector
Rules catch known patterns. Machine learning catches the unknown. By training on historical on-chain data, ML models can flag statistical anomalies that no predefined rule covers.
This is especially useful for detecting novel attack vectors in their early stages.
Incident Response Orchestrator
Detection without response is incomplete. The orchestrator connects alerts to response actions. These include pausing contracts, blocking addresses, notifying security teams, or triggering circuit breakers built into the smart contract.
Dashboard and Reporting Interface
Security teams need visibility. A real-time dashboard showing transaction flows, alert history, wallet risk scores, and contract state gives the team situational awareness at all times.
SecureDApp’s blockchain security monitoring tools are built around exactly this architecture. Our platform integrates with Ethereum, Polygon, BNB Chain, and other EVM networks to give marketplace operators continuous protection across their entire on-chain footprint.
SecureDApp’s Role in NFT Marketplace Security
SecureDApp is a Web3 security company offering a full stack of on-chain protection services. For NFT marketplaces, several of our offerings are directly relevant.
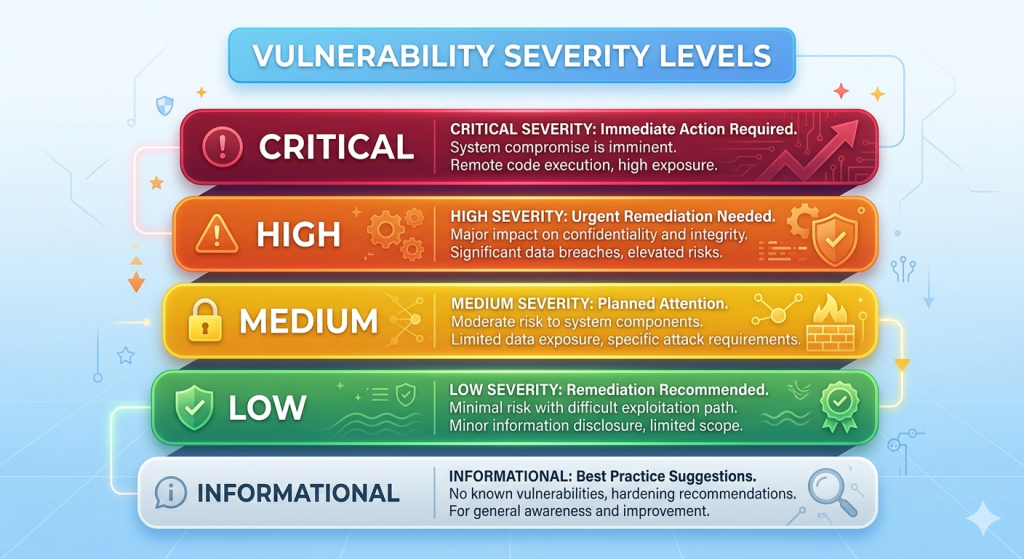
Smart Contract Auditing covers the codebase before deployment. Our auditors identify logic flaws, access control issues, and economic vulnerabilities that could be exploited post-launch.
Smart Contract Monitoring provides the real-time blockchain threat monitoring layer that keeps deployed contracts under continuous surveillance. Marketplace operators receive instant alerts when suspicious activity is detected.
Blockchain Forensics helps trace fund movements after an incident. If a breach occurs, our forensics tools reconstruct the attack path and identify affected wallets and contracts.
Token Due Diligence evaluates ERC-721 and ERC-1155 contracts for rug pull indicators, hidden minting functions, and other red flags before they are listed on a marketplace.
Our approach is not one-size-fits-all. NFT marketplaces have unique architecture and user behaviour patterns. We tailor monitoring rules and alert thresholds to each platform’s specific risk profile.
Case Study Context: How Monitoring Could Have Helped
Consider the Ronin Network bridge hack of March 2022. Attackers stole approximately $625 million. The breach was not detected for six days after it occurred.
That six-day gap was catastrophic. The attackers had ample time to move funds across multiple wallets and mixers.
Had real-time blockchain threat monitoring been active, the abnormal validator key usage and the unusually large withdrawal from the bridge contract would have triggered alerts within minutes of the first transaction.
Six days versus six minutes. That is the difference monitoring makes.
For NFT marketplaces, the math is similar. The faster a threat is detected, the less damage it causes.
Implementing On-Chain Monitoring: A Practical Checklist
If you operate or are building an NFT marketplace, here is a practical starting point for real-time security coverage.
Pre-Deployment
- Complete a thorough smart contract audit with a reputable Web3 security firm
- Implement circuit breakers and emergency pause functions in contracts
- Set rate limits on withdrawal functions
- Use time-locked admin functions to prevent instant parameter changes
Post-Deployment
- Connect to a real-time blockchain monitoring service
- Set up alerts for large fund movements, ownership transfers, and unusual gas patterns
- Monitor all integrated protocols and third-party contracts too
- Screen all interacting addresses against known malicious wallet databases
Ongoing Practices
- Conduct monthly threat model reviews
- Update monitoring rules when new vulnerabilities are publicly disclosed
- Run tabletop incident response exercises with your security team
- Reaudit before every major contract upgrade
The Human Side of Blockchain Security
Technology alone does not secure a marketplace. People do.
Security culture matters enormously in Web3 teams. Developers must understand common vulnerabilities. Product managers must prioritise security sprints. Founders must allocate budget for ongoing monitoring, not just a one-time audit.
Many NFT platforms are built by small, fast-moving teams. Speed is their advantage. But speed without security discipline leads to the exact vulnerabilities that attackers exploit.
Building a culture where security reviews are standard in every sprint cycle, where monitoring dashboards are checked daily, and where incident response plans exist before an incident happens is what separates resilient marketplaces from compromised ones.
Regulatory and Reputational Dimensions
NFT marketplace security is not just a technical concern. It has regulatory and reputational consequences too.
Regulators in multiple jurisdictions are increasingly focused on digital asset platforms. AML compliance, KYC requirements, and sanctions screening are becoming baseline expectations, not optional extras.
Real-time blockchain threat monitoring that includes sanctions address screening helps marketplaces stay compliant with OFAC and other global watchlists. This is not just risk mitigation. It is a regulatory necessity.
From a reputational standpoint, a single high-profile exploit can destroy years of community trust overnight. In Web3, news travels fast and users have no patience for preventable security failures.
Marketplaces that demonstrate proactive, transparent security practices attract more serious collectors and institutional participants. Security is a competitive advantage.
Future of NFT Marketplace Security
The threat landscape will continue to evolve. Here is what to expect in the coming years.
AI-Powered Attacks will become more common. Automated bots that can probe contracts for vulnerabilities in real time will require equally sophisticated AI-driven defence systems.
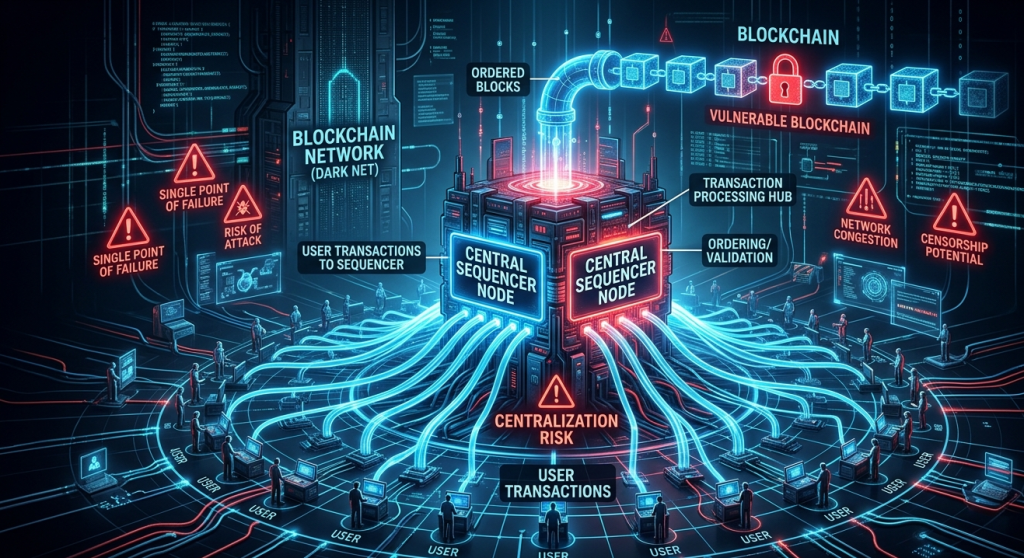
Cross-Chain Exploits will grow as NFT marketplaces expand to multiple chains. Bridges remain the weakest link. Monitoring must span all integrated networks, not just the primary chain.
Social Engineering at Scale will combine on-chain and off-chain tactics. Phishing campaigns will be more targeted and convincing, requiring both technical monitoring and user education.
Decentralised Governance Attacks will target marketplaces that use DAO structures. Attackers will accumulate voting power to pass malicious proposals. On-chain governance monitoring is an emerging necessity.
Zero-Knowledge Proof Exploits as ZK-based NFT platforms grow, new cryptographic vulnerabilities will emerge that current monitoring tools must evolve to cover.
Real-time blockchain threat monitoring will need to keep pace with all of these shifts. Platforms that invest in adaptable, intelligent monitoring infrastructure today will be better positioned to face tomorrow’s threats.s
Conclusion: Security Is Not a Feature, It Is a Foundation

NFT marketplaces are complex, high-value targets. They operate in a permissionless environment where code is law and mistakes are irreversible.
Real-time blockchain threat monitoring is the difference between reacting to a breach after the damage is done and stopping it before it escalates. Every NFT marketplace, regardless of size, needs this layer.
At SecureDApp, we work with Web3 teams to build security from the ground up. Our combination of smart contract auditing, continuous on-chain monitoring, and blockchain forensics gives marketplaces a complete security posture.
If you are building or operating an NFT marketplace and want to understand your current threat exposure, reach out to us at securedapp.io. We will help you map your attack surface and build the protection your platform deserves.
The blockchain is transparent. Your security strategy should be too.
Frequently Asked Questions (FAQs)
It is the continuous surveillance of on-chain activity to detect suspicious transactions, smart contract anomalies, and malicious wallet behaviour as they happen, rather than discovering them after damage is done.
An audit reviews code before deployment and finds pre-existing vulnerabilities. Real-time monitoring watches live contract behaviour post-deployment and catches threats as they occur during actual operation.
Yes. Scalable monitoring solutions exist for platforms at every stage. The cost of monitoring is always lower than the cost of a successful exploit. SecureDApp offers flexible plans suited to different platform sizes.
Most modern solutions cover Ethereum, Polygon, BNB Chain, Avalanche, Solana, and other major networks. SecureDApp supports multiple EVM-compatible chains and continues to expand network coverage.
Detection can happen within seconds of a suspicious transaction being included in a block. Automated response mechanisms like contract pausing can activate within the same block or the next one, dramatically limiting damage.



