Introduction: The DeFi Security Problem No One Wants to Talk About

Decentralised finance has unlocked genuine financial freedom for millions. But it has also become one of the most exploited environments in the history of digital assets.
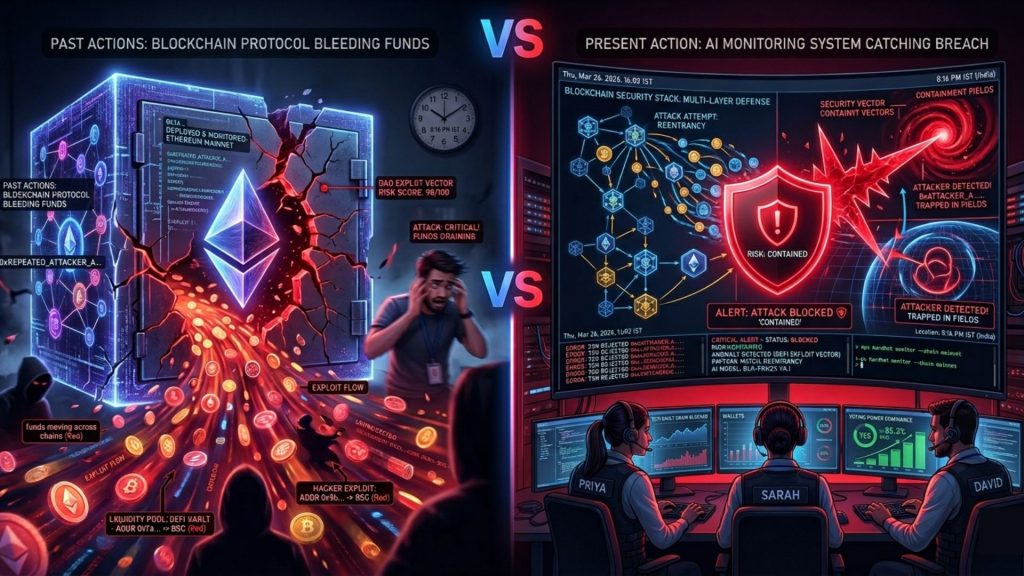
In 2023 alone, DeFi protocols lost over $1.8 billion to hacks, rug pulls, and fraud schemes. The numbers in 2024 were no different. What is alarming is not just the scale, but the speed. Attacks unfold in seconds. Funds are drained in a single block. By the time a team raises an alarm, the exploit is long over.
Traditional security tools are not built for this. They analyse, report, and notify after the fact. In DeFi, after the fact means too late.
This is where real-time blockchain threat monitoring changes the entire equation. It is not a fancy term. It is an operational necessity. And understanding how it works is critical for anyone building, investing in, or managing a DeFi protocol.
This blog breaks down how on-chain data can be used as a live fraud prevention engine and how platforms like SecureDApp are making this accessible for Web3 businesses at every stage.
What Makes DeFi Fraud Different from Traditional Financial Fraud
In traditional banking, fraud detection works because of centralised oversight. Banks have transaction logs, identity records, and regulatory authority. They can freeze accounts in minutes.
DeFi has none of these built-in controls. Transactions are pseudonymous. Smart contracts execute automatically. There is no admin key that pauses everything the moment something suspicious happens, at least not by default.
This structural difference creates a completely new threat landscape.
The three defining features of DeFi fraud are:
Speed: Most exploits happen in one or two transactions. Flash loan attacks, for example, borrow, manipulate, and repay within a single block. This takes under 12 seconds on Ethereum.
Irreversibility: Blockchain transactions cannot be undone. Once funds leave a wallet, recovery requires either the attacker’s cooperation or a governance-level vote that may never pass.
Obfuscation: Attackers route funds through mixers, bridged chains, and throwaway wallets. The forensic trail exists on-chain, but reading it requires specialised tools and expertise.
Understanding these features is what makes real-time on-chain monitoring so critical. You cannot fight this threat with weekly security audits alone.
What Is Real-Time Blockchain Threat Monitoring?
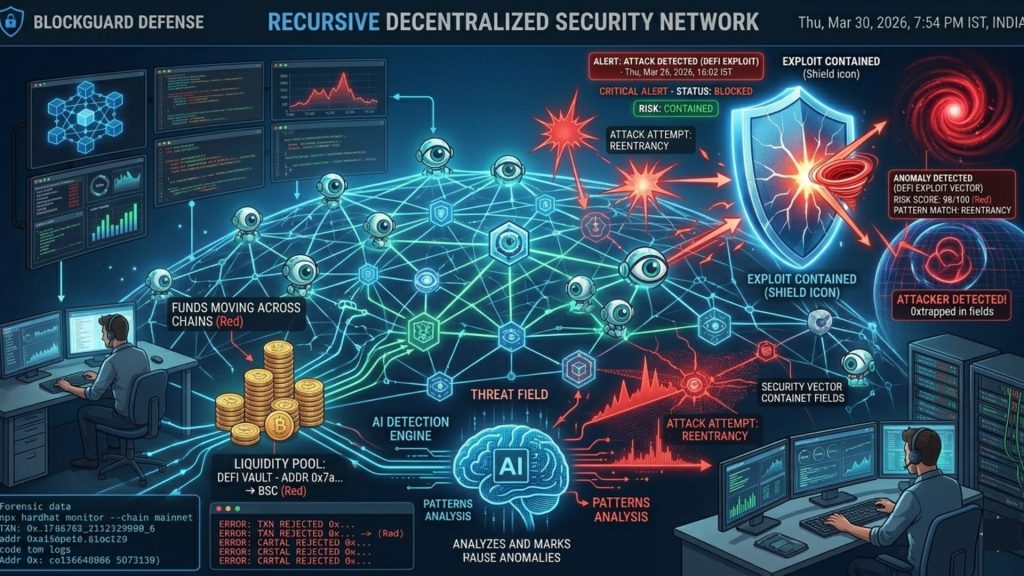
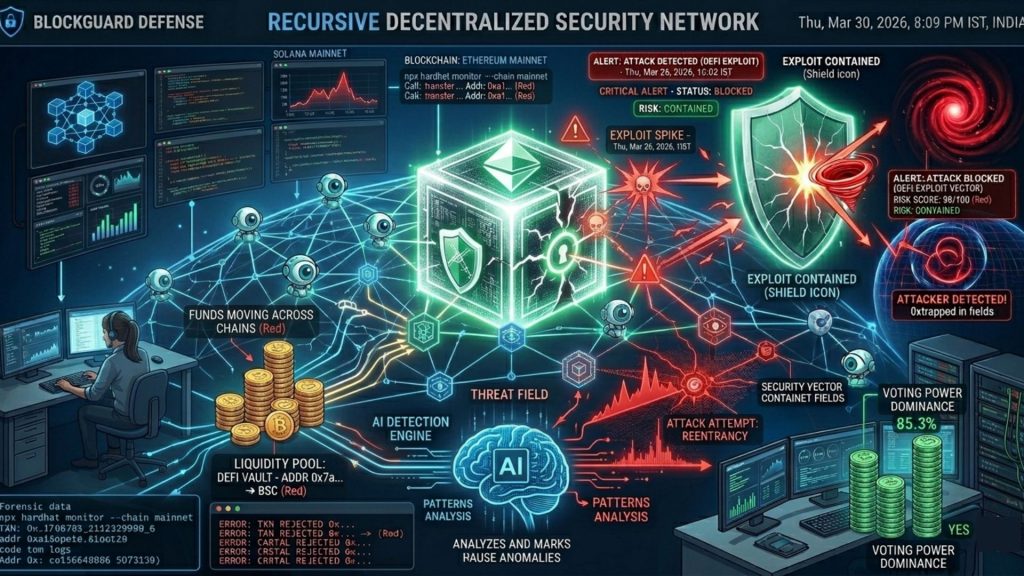
Real-time blockchain threat monitoring refers to the continuous surveillance of on-chain activity to identify, classify, and alert on suspicious patterns as they happen.
Think of it like a security operations centre (SOC), but for the blockchain. Instead of watching network logs, it watches transaction flows, wallet interactions, contract calls, and token movements as they occur across one or more chains.
The key word is real-time. Not hourly. Not daily. Block by block.
Every transaction that hits the mempool or gets confirmed is fed into an analysis pipeline. That pipeline checks it against known threat signatures, behavioural patterns, and risk heuristics. If something triggers a flag, an alert is issued in seconds, not minutes.
At SecureDApp, this is one of the core capabilities embedded within our Web3 security infrastructure. We monitor smart contract interactions, liquidity events, wallet risk profiles, and governance calls in real time to give protocol teams the visibility they urgently need.
Key On-Chain Data Signals Used in Fraud Detection
Not all on-chain data is equally useful. Fraud detection systems prioritise specific signals that historically precede or accompany malicious activity.
1. Abnormal Transaction Volume Spikes
A sudden surge in transactions targeting a specific contract is a classic early warning sign. It often signals either a coordinated attack attempt or a bot-driven exploitation campaign.
Monitoring volume deviations against baseline behaviour helps distinguish organic growth from threat activity.
2. Flash Loan Initiations from New Wallets
Flash loans are legitimate DeFi tools. But they are also the weapon of choice in price oracle manipulation attacks.
When a wallet with zero prior history initiates a large flash loan and immediately interacts with a price-sensitive protocol, that combination is a high-priority red flag.
3. Token Approval Draining Patterns
Phishing attacks in DeFi often rely on tricking users into approving unlimited token transfers to malicious contracts.
Monitoring approval events for unusual beneficiary addresses, especially newly deployed contracts, is a core fraud prevention signal.
4. Large Wallet Concentration Before a Liquidity Pull
In rug pull scenarios, a small number of wallets quietly accumulate governance tokens or LP positions before a sudden exit. On-chain data reveals this concentration pattern before the pull happens.
5. Contract Upgrade and Proxy Calls
Upgradeable contracts are legitimate in design. But unexpected proxy upgrades right before large transactions are a pattern seen repeatedly in governance exploits and insider attacks.
6. Cross-Chain Bridge Activity Involving Flagged Wallets
Attackers often bridge stolen funds immediately to reduce traceability. Real-time monitoring of bridge interactions against known exploit wallets can catch fund movements before they reach mixers.
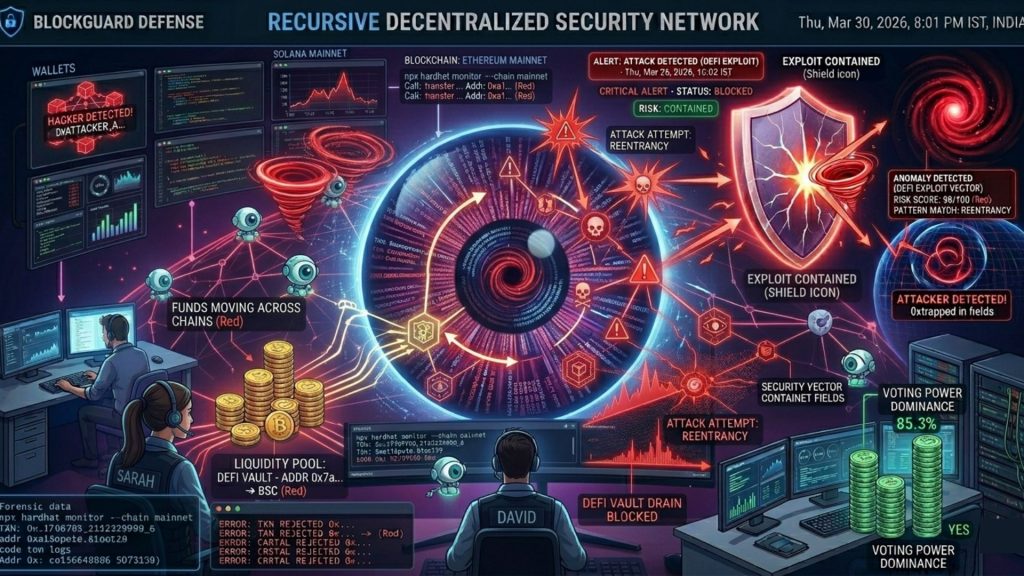
How Real-Time Monitoring Prevents Fraud, Not Just Detects It
Detection is valuable. Prevention is better. This is a meaningful distinction and one that separates mature threat intelligence systems from basic alert tools.
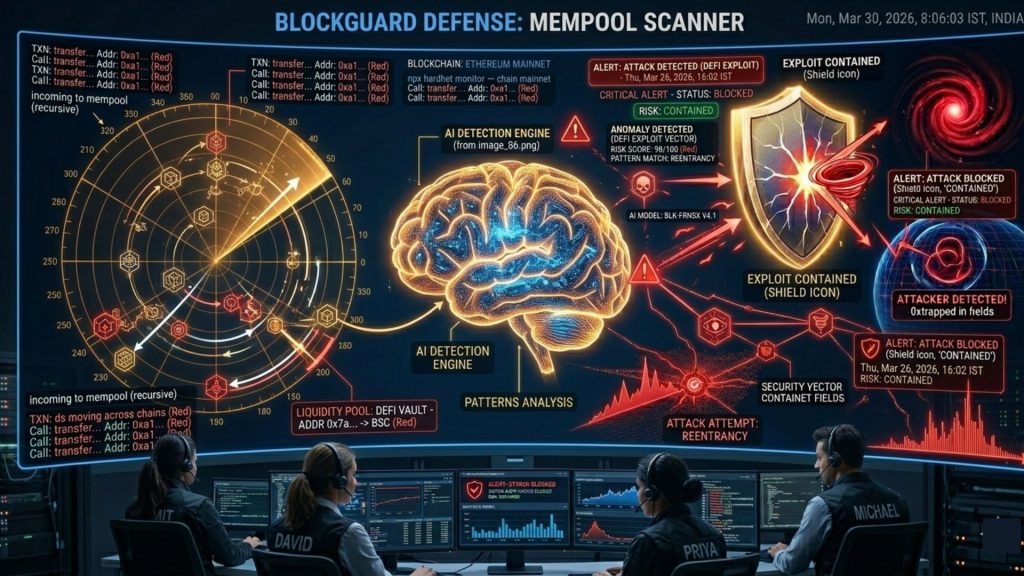
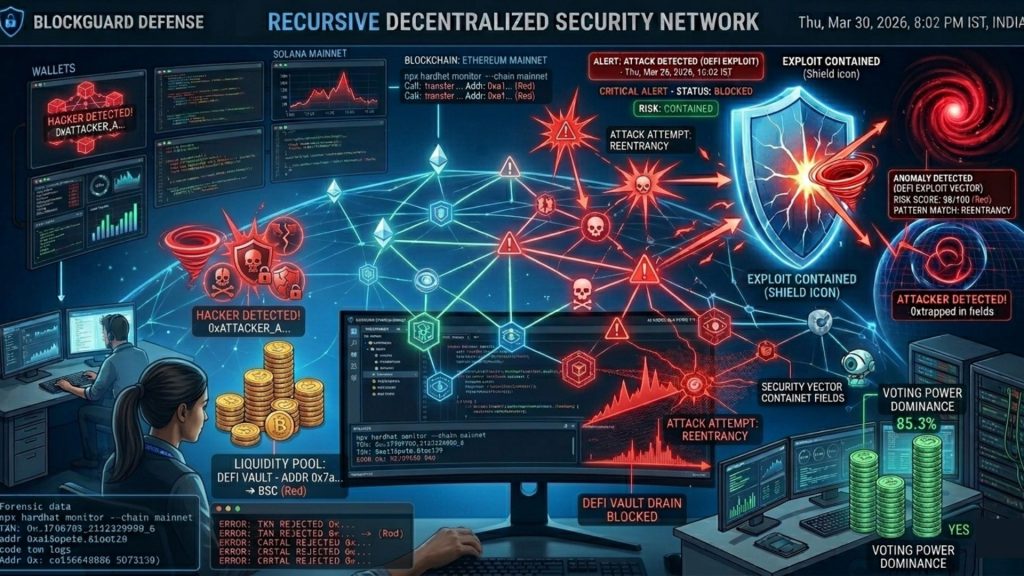
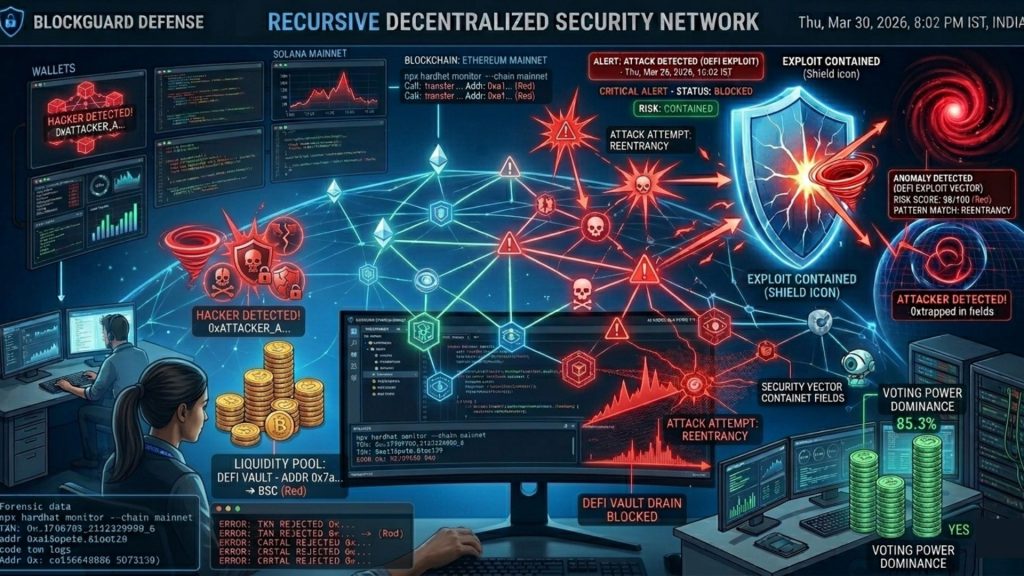
Pre-Transaction Risk Scoring
Modern on-chain monitoring systems can score transactions in the mempool before they are confirmed. If a transaction matches known attack patterns, a protocol can trigger automatic circuit breakers to pause specific functions.
This is not theoretical. Several DeFi protocols now have automated pause mechanisms tied directly to anomaly detection systems.
Wallet Risk Intelligence
Not all wallets are equal. A wallet that has interacted with Tornado Cash, has a history of initiating failed arbitrage attacks, or was funded by a known exchange hack withdrawal is a fundamentally different risk than a fresh retail wallet.
Real-time wallet scoring adds a risk layer to every interaction. Protocols can use this to rate-limit, require additional verification, or simply reject high-risk wallet interactions at the contract level.
Alert Escalation for Security Teams
Speed of response determines outcomes in DeFi security. A team that receives an alert within 30 seconds of anomalous activity on their contract has a meaningful window to respond.
SecureDApp’s threat monitoring infrastructure is designed specifically to give protocol security teams that window. Alerts are tiered by severity, include contextual on-chain evidence, and are delivered through channels that guarantee immediate attention.
Incident Response Readiness
Real-time monitoring is also foundational to incident response. When an attack is underway, having a live feed of what is happening on-chain helps security teams contain damage, communicate with exchanges, and coordinate chain-level responses far more effectively.
The Threat Intelligence Angle: Connecting On-Chain Signals to Attack Campaigns
Threat intelligence in traditional cybersecurity means understanding not just individual incidents, but the actors, tools, and techniques behind them. The same principle applies to DeFi.
A single flash loan attack is an event. A pattern of flash loan attacks targeting the same oracle mechanism across multiple protocols is a campaign. Recognising the campaign is where real threat intelligence begins.
On-chain data makes this possible in ways that are unique to blockchain environments. Because all transactions are public and immutable, analysts can trace the origin wallets, follow the fund flows, identify shared infrastructure, and link attacks that might appear unrelated on the surface.
This intelligence feeds back into real-time monitoring. When a new wallet is seen initiating a similar attack pattern to one observed three months ago, the system flags it immediately rather than waiting for the attack to succeed.
SecureDApp builds this kind of layered threat intelligence for Web3 organisations. Our analysis goes beyond individual contract monitoring to cover attacker infrastructure, cross-chain movement patterns, and known exploit toolkit signatures.
Business Case: Why DeFi Protocols Must Invest in Real-Time Monitoring
For protocol teams and Web3 businesses, this is not just a technical decision. It is a business one.
Regulatory pressure is increasing. MiCA in Europe and evolving frameworks in India, Singapore, and the UAE are beginning to require demonstrable risk controls for DeFi platforms operating in those jurisdictions. Real-time monitoring infrastructure is increasingly a compliance expectation.
Institutional capital demands it. Institutional investors evaluating DeFi protocols for deployment now conduct security due diligence that includes asking whether real-time monitoring is in place. Not having it is a commercial disadvantage.
Insurance requirements are shifting. DeFi protocol insurance products, which are still maturing, are increasingly linking premium rates to the quality of a protocol’s security infrastructure. A monitored protocol is a lower-risk protocol.
User trust is your most valuable asset. A single exploit that goes undetected for even 30 minutes can drain millions and destroy user confidence that took years to build. Real-time monitoring is what protects that trust at the operational level.
The cost of implementing professional monitoring is a fraction of the cost of a single significant exploit. This is a straightforward ROI argument.
SecureDApp’s Approach to On-Chain Threat Monitoring
Secured\DApp has built its Web3 security practice with a clear understanding that smart contract audits, while essential, are not sufficient on their own.
A code audit gives you a security assessment at a point in time. Real-time monitoring gives you continuous coverage as your protocol evolves, as attackers adapt, and as the threat landscape changes.
Our services are designed to work in layers. Smart contract security audits establish the baseline. Ongoing monitoring covers the live environment. Threat intelligence informs both.
For DeFi protocols specifically, we provide monitoring coverage that includes transaction anomaly detection, wallet risk scoring, liquidity event surveillance, governance activity monitoring, and cross-chain movement tracking.
We work with protocol teams at the architecture stage to ensure that monitoring hooks, pause mechanisms, and alert integrations are built into the protocol design itself. Security by design is always more effective than security as an afterthought.
If you are building, launching, or operating a DeFi protocol and you do not have real-time on-chain monitoring in place, now is the right time to change that. The threat environment will not wait.
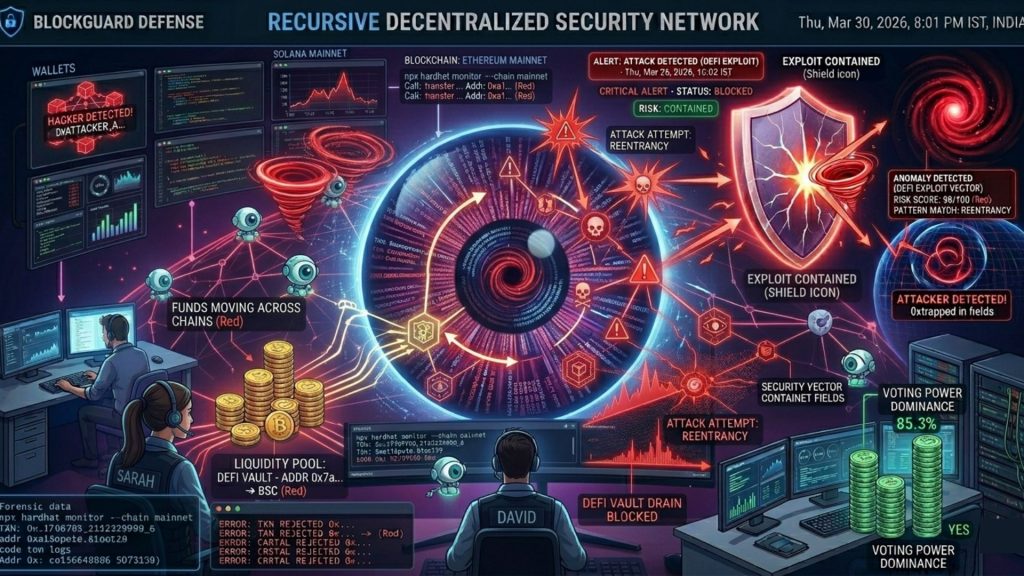
Common DeFi Fraud Vectors and What Monitoring Catches
Understanding the specific attacks that real-time monitoring addresses helps clarify its practical value.
Oracle Manipulation: Attackers use flash loans to manipulate the price reported by an on-chain oracle, then exploit the distorted price in lending or trading contracts. Monitoring catches the flash loan initiation combined with oracle interaction in the same block.
Rug Pulls: Malicious developers or insiders drain protocol liquidity after accumulating user deposits. Monitoring catches wallet concentration, unusual LP burns, and sudden ownership transfer calls before the exit.
Governance Attacks: Attackers acquire enough governance tokens to pass malicious proposals. Monitoring tracks rapid token accumulation and unusual voting patterns.
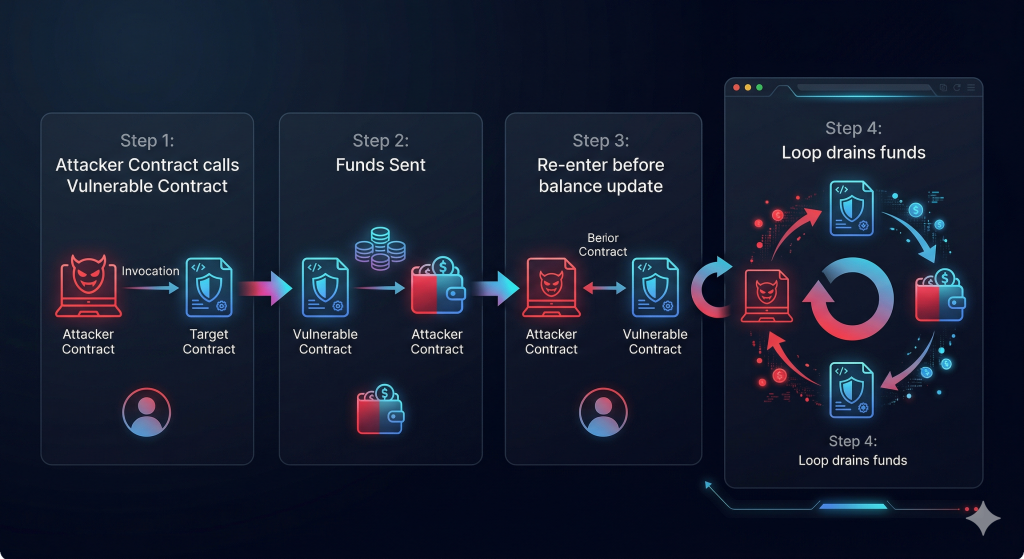
Re-entrancy Exploits: Despite being a well-known vulnerability, re-entrancy attacks still occur, particularly in protocols forked from older codebases. Monitoring catches unusual recursive call patterns.
Phishing and Approval Exploits: Users are tricked into approving malicious contracts. Monitoring flags new contract deployments that immediately receive a high volume of approval transactions.
Front-Running and MEV Exploitation: Bots monitor the mempool and insert transactions ahead of legitimate user activity to extract value. Monitoring identifies systematic front-running patterns that signal MEV exploitation at scale.
Building a Real-Time Monitoring Strategy for Your Protocol
If you are starting from scratch, here is a practical framework for thinking about on-chain monitoring for your DeFi protocol.
Step 1: Define Your Critical Functions
Identify which contract functions, if exploited, would cause the most damage. These are your highest-priority monitoring targets. Typically these include deposit and withdrawal functions, price oracle calls, governance execution functions, and token approval handlers.
Step 2: Establish Baseline Behaviour
You cannot detect anomalies without knowing what normal looks like. Spend time characterising normal transaction volume, typical wallet interaction patterns, and expected function call frequencies during your protocol’s active periods.
Step 3: Set Alert Thresholds
Define what constitutes a meaningful deviation. A 200% spike in transaction volume at 3 AM is different from the same spike during a major protocol announcement. Context matters. Good monitoring systems allow threshold customisation.
Step 4: Integrate Automated Response Mechanisms
Where possible, build circuit breakers and pause functions into your contract architecture. These can be triggered automatically when monitoring alerts hit certain severity thresholds, buying your team critical response time.
Step 5: Establish an Incident Response Plan
Real-time monitoring is only as valuable as your ability to act on what it tells you. Define who gets alerted, what their first actions should be, and how communication flows both internally and externally during a security event.
Step 6: Partner with a Specialist
Building all of this internally from scratch requires significant expertise and ongoing maintenance. Partnering with a Web3 security specialist like SecureDApp means you get access to a system that is already calibrated to the current threat landscape, maintained by people who focus on nothing else.
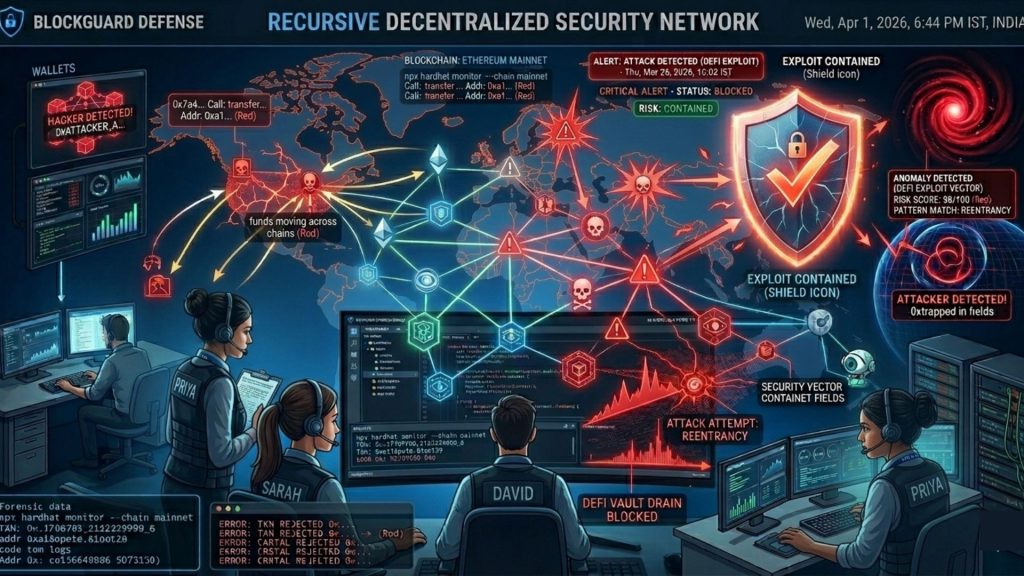
The Regulatory Dimension: On-Chain Monitoring as Compliance Infrastructure
Something that deserves more attention in the Web3 security conversation is the overlap between threat monitoring and regulatory compliance.
Anti-money laundering (AML) obligations are increasingly being extended to DeFi platforms. The Financial Action Task Force (FATF) guidance on virtual assets and the implementation of that guidance across jurisdictions from India to the European Union creates compliance obligations that require exactly the kind of transaction monitoring infrastructure we have been discussing.
Screening wallets against sanction lists, identifying high-risk transaction patterns consistent with money laundering, and maintaining records of suspicious activity are all compliance functions that map directly onto the technical infrastructure used for fraud prevention.
This creates a significant efficiency opportunity for DeFi protocols. A single real-time monitoring system can simultaneously address both security threat detection and regulatory compliance. The same on-chain data feed, the same alert pipeline, the same risk scoring infrastructure serves both functions.
SecureDApp’s approach accounts for this dual-use nature. When we build monitoring infrastructure for a protocol, we design it to address both the security threat landscape and the emerging regulatory compliance requirements that protocols in regulated markets must meet.
Conclusion: Real-Time Monitoring Is Not Optional Anymore
The DeFi space has matured past the point where “move fast and audit later” is an acceptable strategy. The attacks are sophisticated. The financial stakes are enormous. The regulatory attention is intensifying.
Real-time blockchain threat monitoring is no longer a premium add-on for well-funded protocols. It is the baseline standard of operational security for any DeFi protocol that takes its responsibilities to users, investors, and the broader ecosystem seriously.
The good news is that the tools exist, the expertise exists, and the frameworks for deploying effective monitoring are well-developed. The only question is whether your protocol will act on this before or after an incident occurs.
SecureDApp works with DeFi protocols across the lifecycle, from pre-launch audits to post-launch continuous monitoring and threat intelligence. If you want to understand what a monitoring strategy for your specific protocol looks like, reach out to our team. We are ready to help you build the security infrastructure your protocol deserves.
Frequently Asked Questions
Real-time blockchain threat monitoring is the continuous surveillance of on-chain activity, tracking transactions, wallet interactions, and contract calls as they happen. It uses automated analysis to detect suspicious patterns and issue alerts before or during an attack, rather than after funds have been lost.
Both are possible, depending on how your protocol is built. Detection is always possible. Prevention becomes possible when monitoring is combined with automated circuit breakers and pause mechanisms built into the smart contract. When a suspicious pattern triggers an alert, an automated response can pause critical functions within seconds.
A smart contract audit is a point-in-time code review that identifies vulnerabilities before deployment. On-chain threat monitoring is a continuous, live surveillance system that operates after deployment. Both are necessary. An audit secures your code before launch. Monitoring protects your protocol after launch, as the threat environment evolves.
Any protocol that handles user funds needs monitoring. This includes decentralised exchanges, lending and borrowing platforms, yield aggregators, liquid staking protocols, cross-chain bridges, and governance-heavy DAOs. The higher the total value locked (TVL), the more critical monitoring becomes.
SecureDApp provides layered Web3 security that combines smart contract audits with ongoing monitoring and threat intelligence. Our monitoring covers transaction anomaly detection, wallet risk scoring, governance surveillance, and cross-chain movement tracking. We also integrate monitoring with compliance requirements, ensuring that protocols operating in regulated markets meet both security and regulatory standards.



