Introduction: When Every Transaction Is a Potential Risk

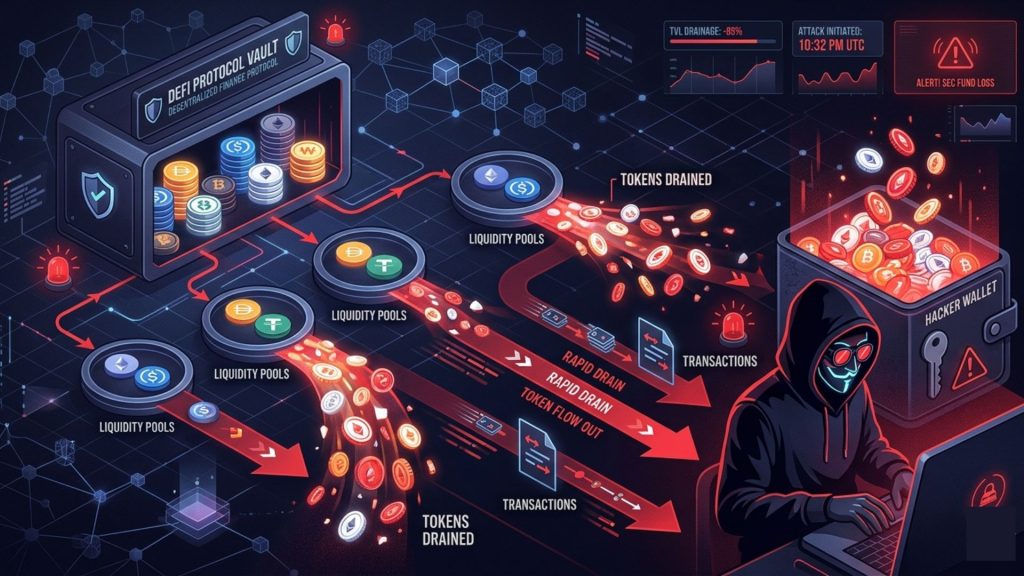
Picture this. It is 2:00 AM in Mumbai. A DeFi protocol sitting on Ethereum holds over $80 million in liquidity. Nobody is watching. A hacker begins silently draining tokens through a re-entrancy exploit. Within twelve minutes, the funds are gone. This actually happened. More than once. The blockchain is open.
Every transaction is visible to the public. Yet most protocols react only after the damage is done. The reason? They are not watching the chain in real time. That is exactly where token movement tracking comes in. And that is what this guide is about. Real-time blockchain threat monitoring is no longer a luxury. For any serious Web3 project, it is a survival requirement.
What Is Token Movement Tracking?
Token movement tracking is the process of monitoring on-chain transactions as they happen. It watches how tokens flow between wallets, smart contracts, and exchanges. Think of it like a CCTV system for your blockchain ecosystem. Except this one never blinks.
When a suspicious transfer occurs, the system flags it. When a known exploit pattern appears, an alert fires. When a whale moves tokens unexpectedly, your team gets notified. At its core, this is about awareness. You cannot defend what you cannot see.
Why Real-Time Blockchain Threat Monitoring Matters

Web3 has a security problem. A massive one. In 2024 alone, over $2.3 billion was lost to hacks, exploits, and rugpulls across DeFi protocols. Most of these attacks shared a common thread: they were not caught in time.
Post-mortem analysis is useful. Real-time detection is lifesaving. Here is why real-time monitoring is critical for any blockchain project:
Speed of attack execution: Most DeFi exploits complete within minutes. A flash loan attack, for instance, borrows, exploits, and repays within a single transaction block. If you are not monitoring at the block level, you will always be too late.
Scale of token movements: Hackers rarely move everything at once. They break large sums into smaller transactions. Pattern recognition over a stream of transactions is not something a human can do manually at scale.
Cross-chain complexity: Attackers increasingly bridge assets across chains to obscure trails. Real-time monitoring across multiple chains simultaneously is essential.
Regulatory pressure: Compliance requirements around AML and fraud detection are tightening in Web3. Real-time transaction monitoring is increasingly a legal requirement, not just a best practice.
How On-Chain Token Movement Tracking Works: A Technical Breakdown
Let us get into the actual mechanics. Understanding the architecture will help you build or choose the right monitoring stack.

Step 1: Connecting to Blockchain Nodes
Every blockchain publishes a stream of new blocks. Monitoring begins by connecting to full nodes or archive nodes using RPC (Remote Procedure Call) or WebSocket connections.
WebSocket connections are preferred for real-time use. They maintain a persistent connection and push new block data as it arrives. RPC polling works too but introduces latency.
For Ethereum-based chains, a node connection might look like this in practice. You subscribe to the newBlock or newPendingTransaction event. This gives you raw transaction data the moment it hits the mempool or gets confirmed.
Popular node providers used in production include Alchemy, Infura, QuickNode, and self-hosted Geth or Erigon nodes. Each has its own tradeoffs around speed, rate limits, and data richness.
Step 2: Parsing Transaction Data
Raw transaction data is not useful on its own. It needs to be decoded.
For ERC-20 token transfers, the key data points include the Transfer event, which contains the sender address, receiver address, and token amount. This event is emitted from the token contract every time tokens move.
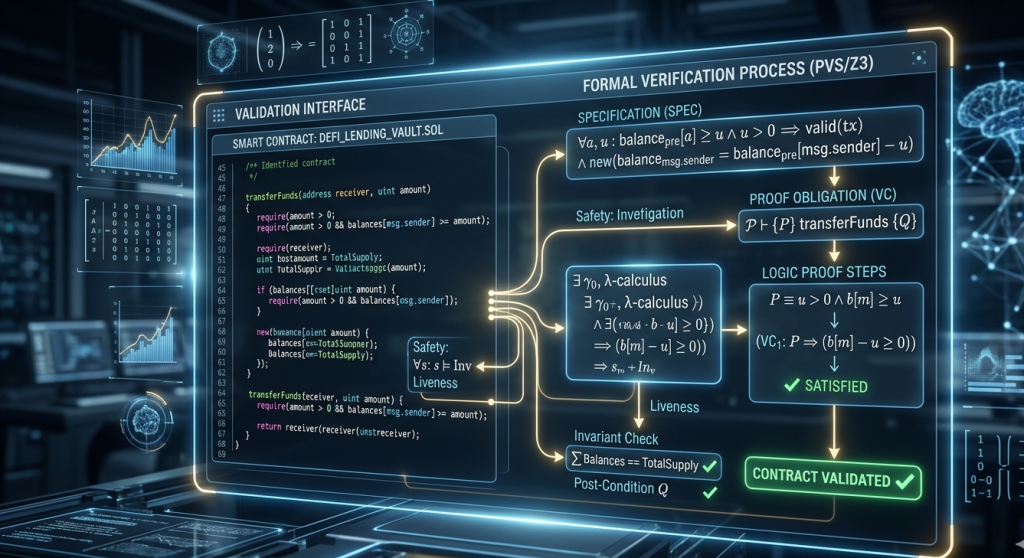
Smart contract interactions are more complex. You need the contract ABI (Application Binary Interface) to decode function calls and their parameters. This is how you tell the difference between a legitimate swap() call and a malicious drain() function that has been disguised.
ABI decoding is non-trivial at scale. Monitoring systems either maintain a local ABI database or query blockchain explorers like Etherscan dynamically.
Step 3: Applying Detection Logic
This is the intelligence layer. Raw parsed data feeds into a rule engine or machine learning model.
Rule-based detection works on predefined conditions. Examples include:
- Token transfer exceeds 500 ETH to an unknown wallet
- Same address performs more than 50 token swaps within 10 seconds
- Liquidity in a pool drops by more than 30% in a single block
- A newly deployed contract calls a flash loan within the same transaction
Heuristic-based detection looks for patterns that indicate known attack vectors. Flash loan patterns, for instance, have a signature: borrow large amount, execute complex multi-step interaction, repay within the same transaction. This is detectable.
Machine learning models can identify anomalies without explicit rules. They learn what normal looks like and flag deviations. This is particularly useful for detecting novel attack patterns that rule engines would miss.
Step 4: Cross-Referencing Threat Intelligence
Not all token movements are suspicious. You need context.
Modern monitoring systems cross-reference flagged addresses against threat intelligence databases. These databases contain wallet addresses linked to known hacks, sanctioned entities, mixer services like Tornado Cash, and rugpull histories.
At SecureDApp, our DeFPunk threat intelligence layer integrates this kind of cross-referencing directly into the monitoring pipeline. When a wallet that previously participated in a known exploit suddenly interacts with your protocol, the alert fires with context, not just raw data.
This is the difference between noise and signal.
Step 5: Alert Delivery and Response
A monitoring system is only as good as its alerting pipeline.
Alerts need to reach the right people through the right channels with the right context. Good alerting means:
- Webhook integrations into Slack, Discord, PagerDuty, or Telegram
- Severity classification so a whale wallet alert does not create the same urgency as an active exploit
- Alert enrichment with transaction hash, block number, contract address, and risk score
- Deduplication to prevent alert fatigue from repeated triggers
For protocol teams, the ideal scenario is an automated response layer on top of alerting. For example, a circuit breaker mechanism that pauses deposits automatically when an active drain is detected.
Key Metrics to Monitor in Real Time

Knowing what to watch is as important as knowing how to watch it.
Here are the most critical on-chain signals that every Web3 security team should be monitoring continuously:
Large token transfers: Any single transfer above a protocol-defined threshold warrants attention. The threshold differs by protocol size. For a small DeFi app, even a $50,000 single transfer is significant.
Liquidity pool composition changes: A sudden change in pool token ratios signals potential manipulation. Price oracle attacks often start with pool imbalances.
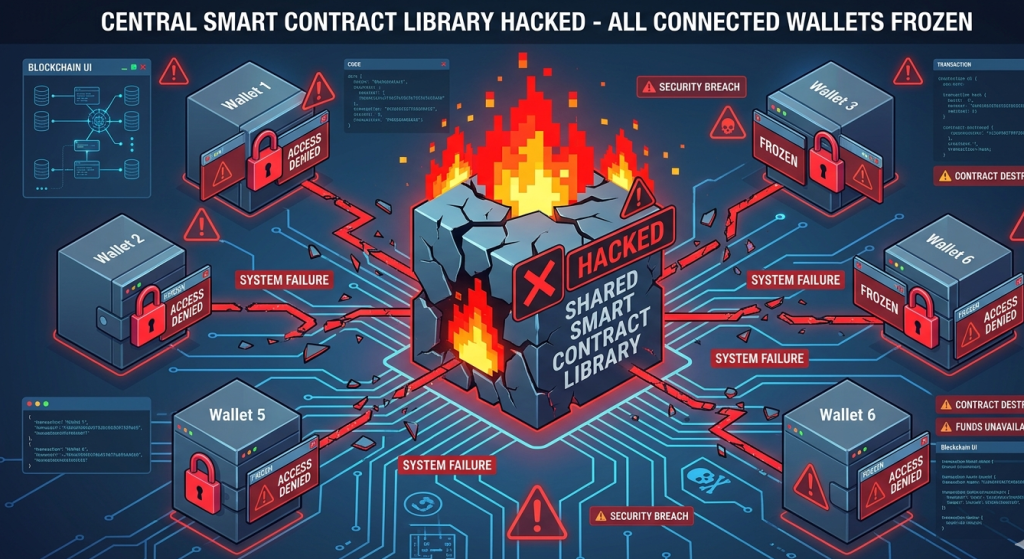
New contract deployments interacting with your protocol: Attackers frequently deploy fresh contracts to interact with targets. Monitoring for new contract interactions is an early warning signal.
Flash loan usage: Flash loans are legitimate tools. But they are also the mechanism of choice for capital-free exploits. Every flash loan interaction with your contracts deserves scrutiny.
Wallet clustering behaviour: A single attacker often controls multiple wallets. Watching for coordinated activity across wallets that move funds in similar patterns helps identify distributed attacks.
Blacklisted address interactions: Any interaction between a blacklisted address and your contracts should trigger an immediate high-priority alert.
Unusual gas usage: Some exploits involve anomalous gas patterns. A transaction using dramatically more gas than normal for a standard function call can indicate something unexpected is happening in the execution flow.
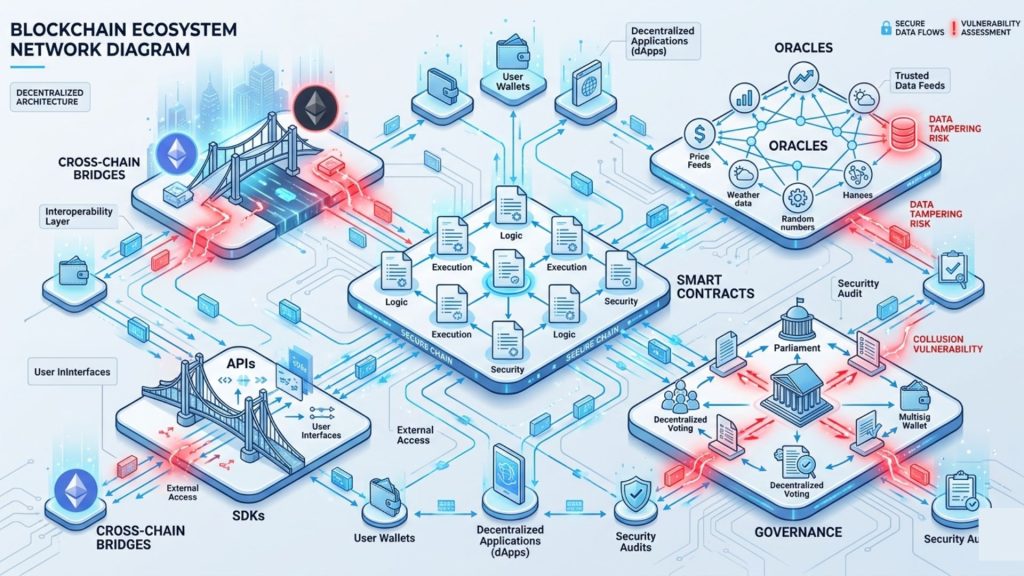
Token Movement Tracking Across Different Chains
Multi-chain monitoring is one of the harder engineering problems in Web3 security. Each blockchain has its own node infrastructure, transaction format, event structure, and finality model. Ethereum, BNB Chain, Polygon, Arbitrum, Optimism, Avalanche, and Solana all require chain-specific parsers and adapters.

The challenge becomes even more complex with cross-chain bridges. An attacker can steal tokens on Chain A and bridge them to Chain B before detection systems on Chain A have even flagged the theft. Effective multi-chain monitoring requires a unified data pipeline that can ingest from multiple chains simultaneously. Events from all chains feed into a common detection engine. Alert correlation across chains is essential. If the same wallet is active suspiciously on both Ethereum and Arbitrum within the same time window, that correlation should surface.
SecureDApp’s monitoring infrastructure is designed with this multi-chain reality in mind. Protocol teams working across networks get a single pane of glass view of their entire token movement landscape.
Common Attack Patterns Caught by Real-Time Monitoring
Let us look at the specific attack types that real-time blockchain threat monitoring is best positioned to catch.
Flash Loan Exploits
Flash loans borrow and repay in one transaction. The pattern is detectable because the borrow amount, the multi-contract interaction chain, and the repayment all happen within a single block. A well-tuned rule engine catches this in real time.
Price Oracle Manipulation
Attackers manipulate the price of a token in a DEX pool, then exploit protocols that use that pool as a price feed. This requires watching both pool token ratios and the downstream protocol’s behavior simultaneously.
Rug Pulls and Liquidity Removal
When a project developer or insider removes liquidity suddenly, token holders are left stranded. Monitoring for large liquidity removal events, especially when they are concentrated in a single wallet, catches this pattern early.
Governance Attacks
Malicious actors sometimes accumulate governance tokens quickly to push through harmful proposals. Monitoring large, rapid accumulations of governance tokens is an important signal for protocol security teams.
Bridge Exploits
Vulnerabilities in cross-chain bridge contracts have resulted in some of the largest hacks in Web3 history. Monitoring the balance changes of bridge contracts in real time is critical for any protocol that relies on bridging functionality.
How SecureDApp Approaches Token Movement Tracking

SecureDApp was built for exactly this problem. Our Web3 security stack includes tools that integrate real-time on-chain monitoring into the protocol lifecycle, not just as an afterthought.
Smart Contract Audit is our foundation. Before a contract goes live, our auditors identify vulnerabilities that would be exploitable. This reduces the attack surface that monitoring needs to cover.
DeFPunk is our threat intelligence and monitoring platform. It watches token movements, flags suspicious wallets, and correlates on-chain events with known threat data. DeFPunk is used by protocol teams who want continuous security visibility after deployment.
Incident Response Support is available when a real-time alert indicates a live threat. Having a team ready to respond is the difference between catching a hack midway and minimising damage versus reading about it in a post-mortem.
Our approach is built on a simple principle: security does not end at deployment. The chain never sleeps, and neither does our monitoring.
Building vs. Buying: What Protocol Teams Need to Know
Should your team build an in-house monitoring stack or use an existing solution?
Building gives you full control. You can tune detection rules precisely for your protocol’s behaviour. You can integrate deeply with your own alerting and incident response workflows. However, building a production-grade monitoring system takes significant engineering time. The node infrastructure, parsing pipeline, detection engine, and alert delivery all need to be built and maintained.
For most protocol teams, buying or using an existing security platform makes more practical sense. You get battle-tested detection logic, access to threat intelligence built up from monitoring many protocols, and faster time-to-value.
The right answer depends on your team’s engineering capacity, your risk profile, and your budget. For high-value protocols managing tens of millions in TVL, investing in a dedicated security monitoring solution is non-negotiable.
Best Practices for Real-Time On-Chain Monitoring

If you are setting up or improving your token movement tracking capability, keep these practices in mind.
Define your assets clearly. Know exactly what contracts and wallets your monitoring needs to cover. Include your token contracts, liquidity pools, governance contracts, treasury wallets, and any bridge contracts.
Set context-appropriate thresholds. A threshold that makes sense for a large protocol will generate false positives for a smaller one. Tune your rules based on your actual transaction volumes and normal operating patterns.
Layer your detection. Use rule-based detection for known patterns and machine learning for anomaly detection. Neither alone is sufficient.
Test your alerting pipeline. Monitoring is useless if the alert does not reach anyone. Test your Slack, PagerDuty, or Discord integrations regularly. Simulate alert conditions in a testnet environment.
Have a response plan. Detection without a response plan is just watching things go wrong. Define your incident response procedure before you need it. Who gets called? What actions can be taken automatically? Who has the authority to pause the protocol?
Do not monitor in isolation. Combine on-chain monitoring with off-chain signals. Social media, security researcher disclosures, and community reports can provide early warnings that complement on-chain data.
The Future of Real-Time Blockchain Threat Monitoring
This field is evolving fast. AI-powered anomaly detection is becoming more sophisticated. Models trained on historical attack data can identify novel exploit patterns with higher confidence than static rule engines. Decentralised security networks are emerging. Projects are exploring shared threat intelligence where protocols pool their monitoring data to collectively improve detection for everyone. MEV-aware monitoring is growing in importance.
Maximal Extractable Value bots operate in the mempool. Understanding their behaviour is increasingly relevant for protocols that want to understand front-running and sandwich attacks. Regulatory integration will deepen. As governments around the world develop Web3-specific compliance frameworks, real-time transaction monitoring will likely become a formal requirement for licensed DeFi operations. The direction is clear: real-time monitoring will become more intelligent, more automated, and more deeply integrated into the operational layer of every serious Web3 protocol.
Conclusion

Token movement tracking is not a niche concern for large protocols. It is a foundational security practice for any project that holds or manages value on-chain. Real-time blockchain threat monitoring closes the gap between when an attack starts and when your team knows about it. In a space where exploits complete in minutes, that gap is everything.
Whether you are building a new DeFi protocol, running an NFT marketplace, or managing a DAO treasury, the question is not whether you need monitoring. The question is how quickly you can get it in place. At SecureDApp, we help Web3 teams across the globe answer that question. From smart contract audits to live threat monitoring via DeFPunk, we are building the security infrastructure that Web3 actually needs. The chain is always running. Make sure someone is watching it.
Frequently Asked Questions
Token movement tracking monitors how tokens are transferred between wallets and smart contracts on a blockchain in real time. It helps detect suspicious activity, large outflows, or attack patterns as they happen rather than after the fact.
Blockchain analytics is typically retrospective; it examines historical data to identify patterns. Real-time threat monitoring is proactive; it processes transaction data as it arrives and triggers alerts within seconds of detecting anomalous behaviour.
It cannot prevent a flash loan attack that completes within a single block, since the borrow and repayment happen atomically. However, it can detect the pattern in real time and alert teams immediately, enabling faster containment and reducing further losses.
DeFPunk covers Ethereum, BNB Chain, Polygon, Arbitrum, Optimism, and other EVM-compatible chains. Multi-chain monitoring with unified alerting is a core part of the platform’s design.
Rules should be reviewed and updated at least quarterly, or immediately after any major security incident in the broader Web3 ecosystem. New attack patterns emerge regularly, and monitoring logic must evolve to stay effective.



