Smart contracts were built on a simple promise: trustless execution. Once deployed, they run exactly as written, without the need for intermediaries, lawyers, or manual oversight. That promise has powered an entirely new financial ecosystem worth hundreds of billions of dollars. And it has also introduced one of the most unforgiving security environments in the history of software.
Unlike traditional applications, smart contracts cannot be patched with a quick update after launch. The immutability that makes them trustworthy also makes them fragile. A single vulnerability left unaddressed can drain a protocol’s entire treasury in minutes. The code is the contract, and if the code is flawed, there is no legal override, no emergency rollback, and often no recovery.
Smart contract security is not a niche concern anymore. It is a foundational requirement for any team building in Web3. The question is no longer whether vulnerabilities exist, but how well-prepared a team is to detect and neutralize them before they become headlines.
Why Smart Contract Vulnerabilities Are Different
Security professionals transitioning from traditional software development to blockchain often underestimate one critical difference: the attack surface in smart contracts is both narrow and brutally consequential.
In conventional systems, a breach might expose data or compromise a server. Incident response teams can contain the damage, restore systems, and notify affected parties. The situation is bad, but it is recoverable. In smart contracts, a successful exploit typically results in irreversible fund loss. There is no chargeback mechanism, no fraud department to call, and in most cases, no legal jurisdiction that can compel asset recovery.
Moreover, smart contract code is publicly visible. Every function, every state variable, every logic branch is visible to anyone who wants to examine it. For defenders, this promotes transparency and verifiability. For attackers, it is a detailed blueprint of exactly where to probe.
This combination of public code, financial assets, and immutability defines why smart contract security demands a different level of rigor than conventional application development.
Reentrancy: The Vulnerability That Refuses to Retire
Reentrancy is not a new concept. The 2016 DAO hack, which resulted in the loss of 3.6 million Ether, was a reentrancy attack. Yet variations of this vulnerability continue to appear in production contracts almost a decade later. Understanding why helps clarify how deeply it can hide within seemingly logical code.
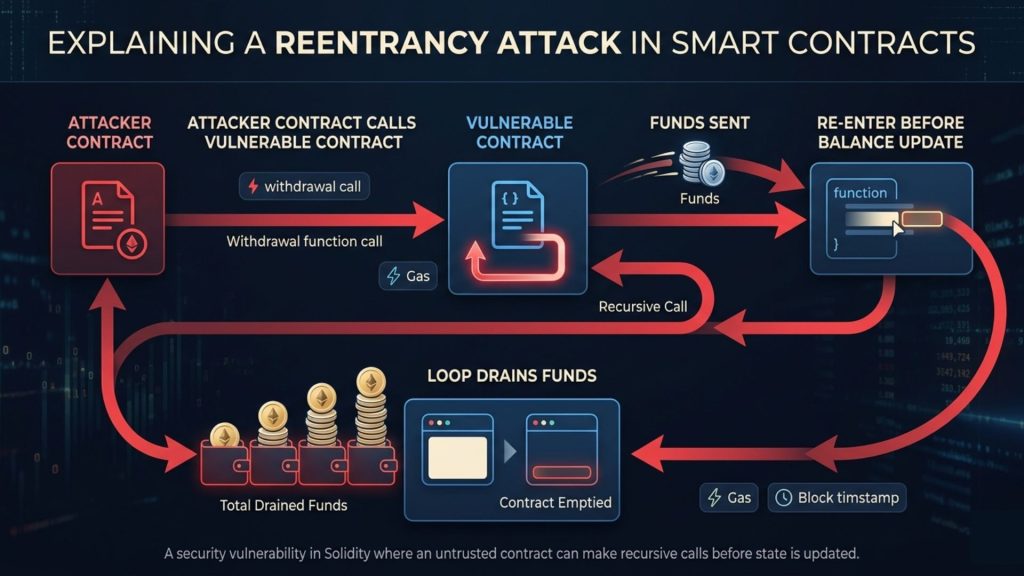
A reentrancy attack occurs when a contract calls an external address, and that address, before the original call completes, calls back into the vulnerable contract. If the vulnerable contract’s state has not been updated before the external call, the attacker can repeatedly trigger withdrawals, draining balances that the contract still believes are available.
Consider a simplified withdrawal function. A contract checks a user’s balance, sends the requested amount, and then updates the balance to zero. In a single-threaded execution model, this seems fine. But Ethereum’s execution model allows the receiving address, if it is itself a contract, to execute code upon receiving funds. If that code calls the withdrawal function again before the balance update completes, the cycle repeats.
How Teams Defend Against Reentrancy
The standard defense is the checks-effects-interactions pattern. State changes must occur before any external calls are made. Balances should be updated to zero before funds are transferred, not after. Additionally, reentrancy guards, implemented as boolean flags or modifiers that prevent recursive function calls, add a reliable second layer of protection.
Automated static analysis tools can flag reentrancy-prone patterns during development. Running a contract through analysis before deployment is not optional anymore; it is a basic standard of care for any production-grade protocol.
Integer Overflow and Underflow: Small Numbers, Large Consequences
Solidity, like most compiled languages, uses fixed-size integers. When arithmetic operations exceed the maximum value a variable can hold, the number wraps around to zero. When a subtraction drives a value below zero, it wraps to the maximum. These are integer overflow and underflow conditions, and in financial contracts, they can be devastating.
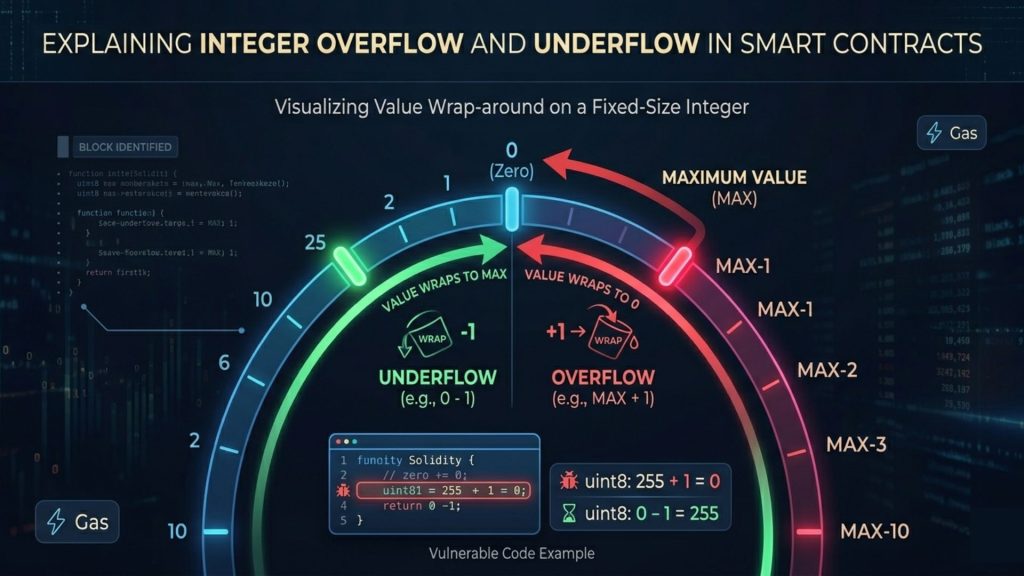
Consider a contract where a user’s token balance is stored as a uint256. If the balance is zero and the contract subtracts an amount without checking, the result wraps to an astronomically large number. An attacker who knows this can manipulate their balance to near-infinite levels with a single crafted transaction.
Prior to Solidity 0.8.0, developers had to manually use safe math libraries, such as OpenZeppelin’s SafeMath, to catch these conditions. Since 0.8.0, the compiler checks for overflow and underflow by default and reverts on violation. However, contracts written on earlier versions, many of which remain active and control significant value, retain this exposure.
The practical advice here is straightforward: contracts compiled before Solidity 0.8.0 should be carefully audited for arithmetic vulnerabilities, and any migration or upgrade path should explicitly address whether SafeMath was used consistently throughout.
Access Control Failures: When Anyone Can Call Anything
Access control vulnerabilities are responsible for a surprisingly large share of smart contract exploits. The logic is simple: if a function that should be restricted to the contract owner or an authorized role can be called by any address, attackers will find it and use it.
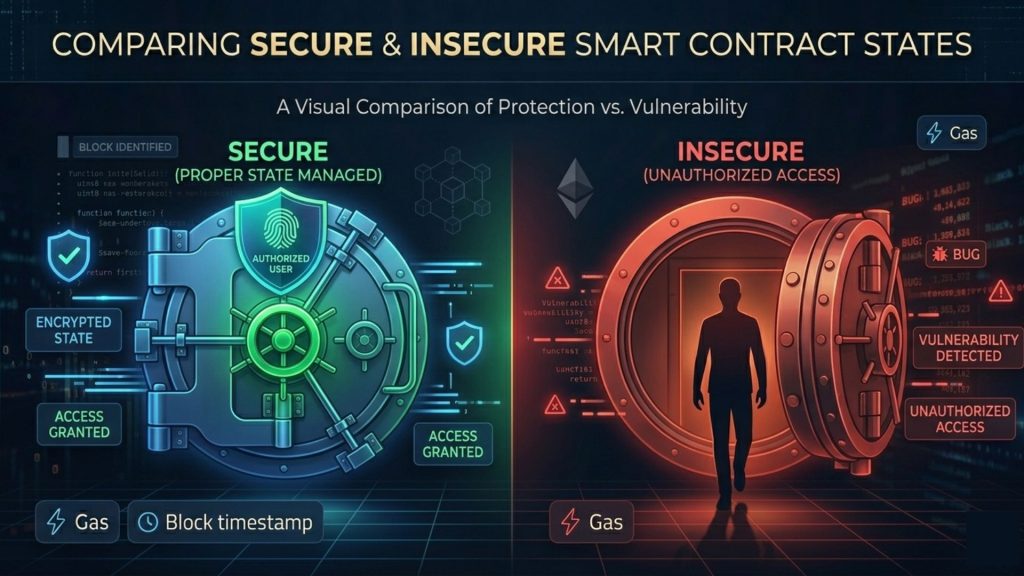
These failures often appear in initialization functions, administrative upgrade mechanisms, and treasury management functions. A common pattern involves a contract that exposes a function meant only to be called once during deployment, but without an appropriate guard to enforce that restriction after deployment.
In one category of attacks, exploiters discovered that protocol upgrade functions lacked access controls entirely, allowing them to redirect contract logic or drain funds by simply calling the function from an arbitrary address. The vulnerability was visible in the contract’s public bytecode, and the financial damage was irreversible.
Building Proper Access Control
Role-based access control, implemented through established patterns like those in OpenZeppelin’s AccessControl library, provides a structured approach. Functions that affect protocol state, treasury operations, or administrative settings should have modifiers that explicitly verify the caller’s identity and role before executing.
Multisig requirements for critical operations add another dimension of protection, ensuring that no single key compromise can trigger a destructive outcome. Time locks on sensitive operations also reduce the damage window if unauthorized access is somehow obtained.
Oracle Manipulation: Exploiting the Bridge Between Chains and Reality
Smart contracts are deterministic systems. They can only act on information that exists on-chain. When a contract needs external information, such as the current price of an asset, it relies on oracles to supply that data. This dependency creates one of the more sophisticated attack surfaces in DeFi: oracle manipulation.
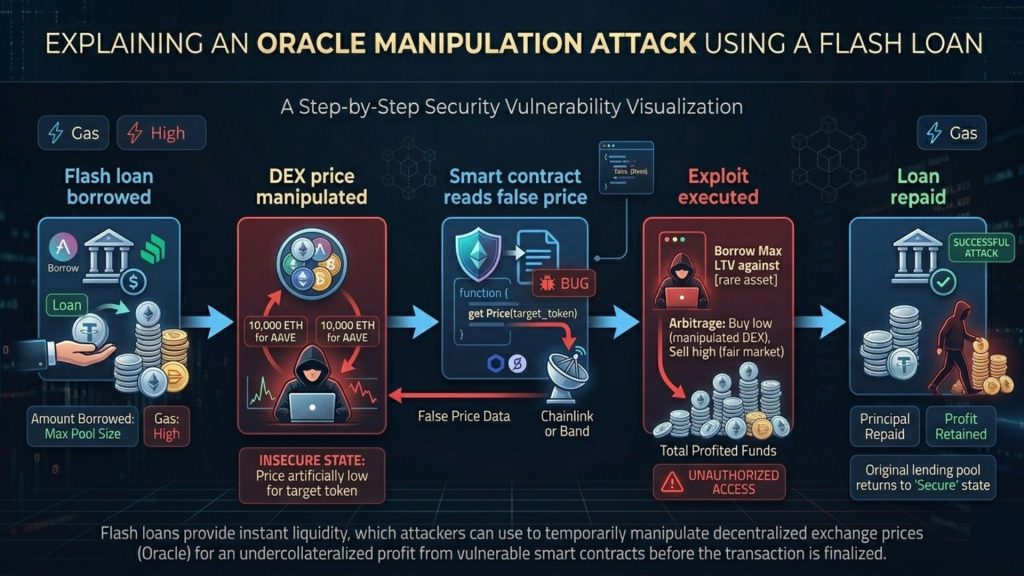
Price oracle attacks exploit the gap between what a contract believes an asset is worth and what the market actually values it at. Flash loans have made these attacks especially effective. An attacker can borrow a massive sum within a single transaction, use it to distort a price on a low-liquidity exchange that serves as an oracle, exploit the contract’s belief in that distorted price, and repay the flash loan, all within a single block.
The Mango Markets exploit of 2022, which resulted in over 100 million dollars in losses, demonstrated how oracle manipulation attacks could be engineered with precision against even well-audited protocols. The attack did not involve breaking the contract’s code. It involved feeding the contract manipulated data, which the contract dutifully acted upon.
Reducing Oracle Dependency Risk
Time-weighted average prices, known as TWAPs, reduce susceptibility to single-block manipulation by averaging prices across multiple blocks. Using decentralized oracle networks with multiple independent data sources reduces single points of failure. Protocols should also implement sanity checks that reject price data deviating beyond an acceptable range from recent history.
No oracle solution eliminates risk entirely, but a layered approach to price data verification substantially raises the cost and complexity of manipulation.
Logic Errors and Business Logic Exploits
Not all smart contract vulnerabilities are technical in the conventional sense. Some of the most damaging exploits target the business logic itself, situations where the contract executes exactly as written, but the logic was written incorrectly.
These vulnerabilities are the hardest to detect because they do not violate any programming convention. A reentrancy bug violates an expected execution pattern. A logic error might be subtle, such as a fee calculation that rounds in the wrong direction, an incentive structure that rewards unintended behavior, or a governance mechanism that allows a large tokenholder to pass proposals before defenders can respond.
The complexity of multi-protocol interactions in DeFi has expanded the surface for logic errors significantly. A contract that is individually sound can behave unexpectedly when composed with another protocol. This is sometimes called a composability attack, and it represents one of the newer frontiers of smart contract security.
Thorough testing, including fuzz testing with tools like Foundry or Echidna, helps surface edge cases that standard unit tests miss. Formal verification, while resource-intensive, provides mathematical proof of certain properties and is increasingly used for high-value contracts.
The Audit Illusion: Why Pre-Deployment Checks Are Not Enough
Here is an insight that many teams do not fully internalize until it is too late: a clean audit report does not mean a contract is secure. It means the contract was secure at the time it was reviewed, under the assumptions and scope defined by that audit.
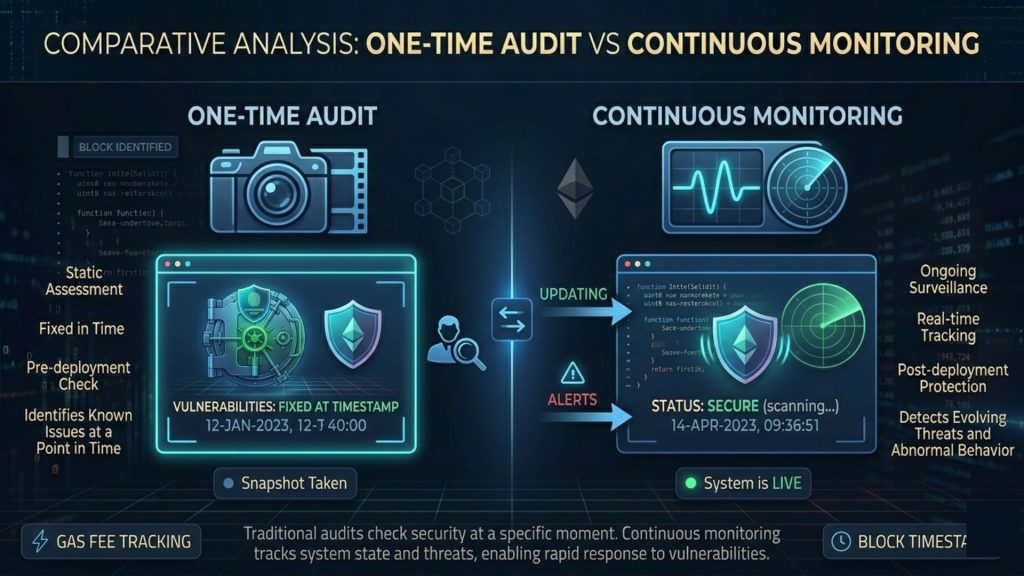
Protocols evolve. Upgradeable contracts introduce new logic. Integrations are added. Governance decisions modify parameters. Each change resets the risk landscape. A vulnerability that did not exist in the original audit can be introduced in a subsequent upgrade. And because the audit was completed before that upgrade, the new code was never reviewed.
This is where continuous monitoring becomes as important as pre-deployment auditing. Post-deployment security means watching for unusual on-chain activity, such as unexpected fund flows, abnormal function call patterns, or transactions that interact with the contract in ways that deviate from its intended usage.
Teams building serious protocols increasingly recognize that auditing and monitoring are complementary, not interchangeable. Tools that provide real-time on-chain visibility, like SecureWatch from SecureDApp, offer continuous monitoring alongside features like AutoPause, which can suspend suspicious transactions automatically during an active threat. The idea that an AI-driven system watching for anomalies can intercept an exploit in progress is no longer theoretical. It is now a practical component of a mature security stack.
Front-Running and MEV: The Hidden Attack Layer
Miners and validators, by nature of their role, see pending transactions before they are confirmed. This creates an opportunity for what is broadly known as maximal extractable value, or MEV. Front-running is one specific form: an actor sees a profitable transaction in the mempool and submits an identical or related transaction with a higher gas fee, ensuring it is processed first.
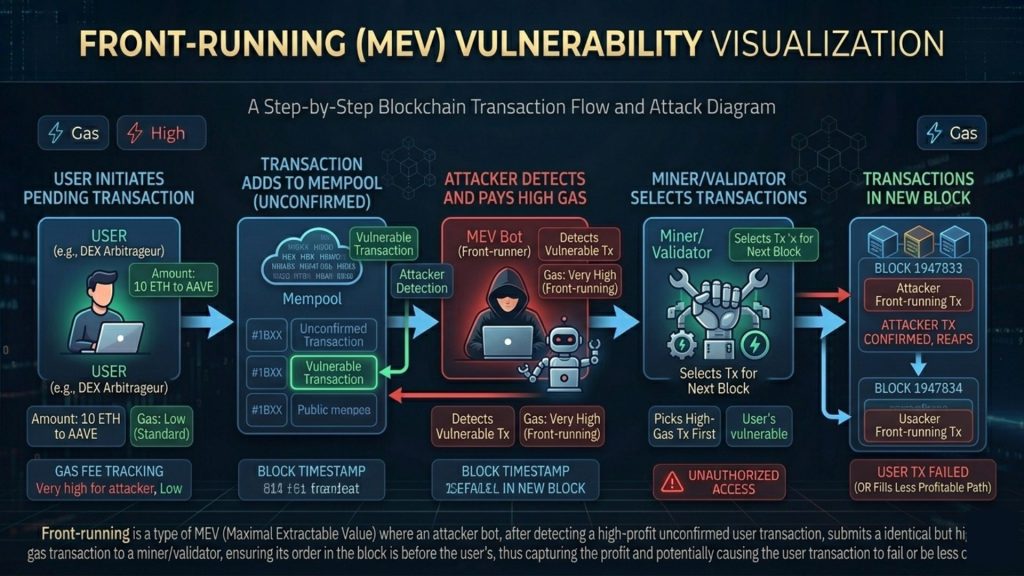
For decentralized exchanges, front-running can extract value from ordinary users on every trade. For protocols that rely on the ordering of certain transactions, it can produce unexpected and exploitable states. While not always classified as a vulnerability, front-running represents a real financial drain and can be weaponized in certain contract designs.
Commit-reveal schemes, where users first commit to an action cryptographically without revealing the details, and then reveal in a subsequent transaction, reduce front-running exposure. Some protocols also use private transaction services that bypass the public mempool for sensitive operations.
What a Layered Security Approach Looks Like in Practice
There is no single solution that eliminates smart contract risk. The protocols that have sustained themselves through multiple market cycles have generally adopted a layered approach, where each layer addresses different aspects of the threat surface.
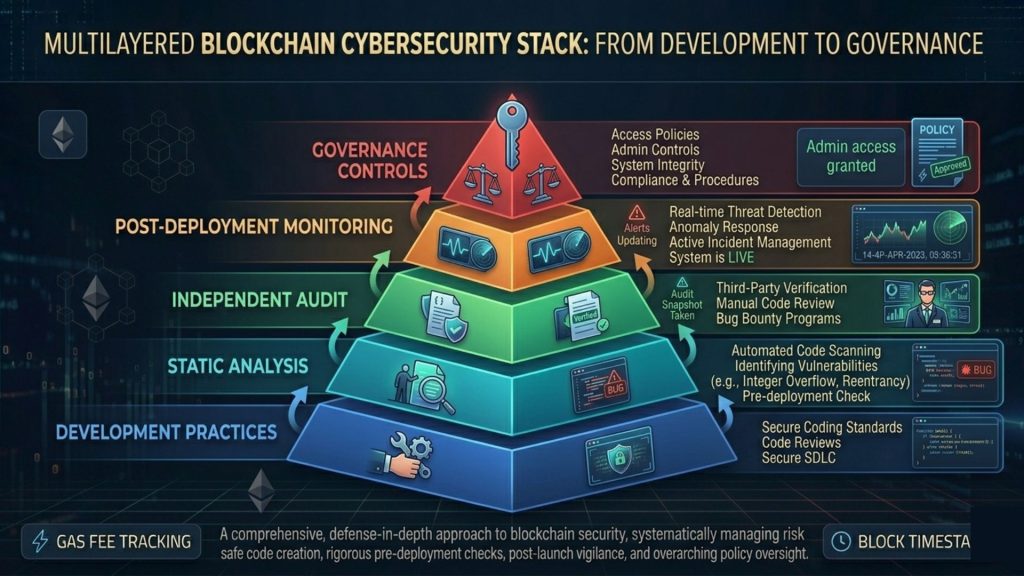
Pre-deployment, this means writing contracts in accordance with established secure development guidelines, using well-audited libraries, conducting thorough internal reviews, running automated static analysis, and commissioning independent audits from reputable firms.
Tools like Solidity Shield, SecureDApp’s smart contract auditing solution, sit at this pre-deployment layer, scanning for common vulnerability patterns, logic issues, and configuration errors before code ever reaches mainnet. Having automated detection as part of the development workflow, rather than as a final gate, shifts the conversation from “did we catch this?” to “do we know this has been checked continuously?”
Post-deployment, the focus shifts to monitoring, anomaly detection, and incident response planning. This includes setting up alerts for unusual contract interactions, monitoring on-chain data for early signs of exploit activity, and having a defined response process if something suspicious appears.
Governance security is also worth addressing explicitly. Voting mechanisms, proposal parameters, and governance token distributions should be designed to prevent hostile takeovers. Time locks between proposal approval and execution give communities time to react. Quorum requirements prevent thin-participation attacks.
Practical Steps for Security-Conscious Teams
Building securely does not require a complete overhaul of development practices. It requires integrating specific habits at every stage of a contract’s lifecycle.
- Adopt secure development patterns from the beginning. Use OpenZeppelin libraries for access control, safe math, and standard interfaces rather than reinventing them.
- Run static analysis on every significant code change. Do not wait for the final audit to find what tooling could have flagged weeks earlier.
- Commission at least one independent audit before mainnet deployment. For high-value protocols, multiple auditors reduce the likelihood of a shared blind spot.
- Define an upgrade governance process before you need one. If your contract is upgradeable, know who can authorize changes, what review process applies, and what the time lock is.
- Implement on-chain monitoring from day one. The assumption that nothing will go wrong after launch has been proven wrong too many times.
- Maintain an incident response plan. Know what you will do if a suspicious transaction appears, who is authorized to trigger emergency measures, and how you will communicate with your community.
- Continuously review integrations. Each new protocol you integrate with extends your attack surface. Security reviews should account for the behavior of every external dependency.
The Regulatory Dimension: Security as Compliance
The regulatory environment around blockchain and DeFi is maturing quickly. In several jurisdictions, the expectation that protocols maintain demonstrable security standards is moving from informal expectation to enforceable requirement.
For teams operating in regulated environments, smart contract security is increasingly part of a compliance conversation, not just a technical one. Documentation of audits, testing methodologies, and monitoring practices may be required for licensing, institutional partnerships, or insurance coverage.
This shift is, in many ways, a healthy development. Framing security as compliance creates organizational pressure to take it seriously at every level, not just the development team. It also raises the baseline across the industry, making the ecosystem incrementally safer for every participant.
Final Thoughts
Smart contract security is not a box to check before launch. It is a continuous responsibility that extends for as long as a protocol is active and holds value. The vulnerabilities discussed here, from reentrancy to oracle manipulation, are not theoretical; they are documented attack vectors that have cost real users real money.
The teams that build lasting protocols are the ones that treat security as architecture, not afterthought. They embed it in their development workflow, commission independent reviews, monitor their contracts after deployment, and plan for the possibility that something unexpected will happen.
The tools and practices to do this well exist today. Static analysis, independent auditing, on-chain monitoring, and governance controls are all accessible to teams of any size. The question is not whether the infrastructure exists. The question is whether a team is willing to use it consistently.
In an industry where a single vulnerability can erase years of development and community trust in a matter of minutes, consistent security practice is not a competitive advantage. It is the baseline requirement for responsible building.
Frequently Asked Questions
1. What is smart contract security?
Smart contract security refers to the set of practices, tools, and processes used to identify and mitigate vulnerabilities in smart contracts before and after deployment. It covers code auditing, testing, monitoring, and incident response.
2. What are the most common smart contract vulnerabilities?
Reentrancy, integer overflow and underflow, access control failures, oracle manipulation, and business logic errors are among the most frequently exploited vulnerability categories in smart contracts.
3. Is a smart contract audit enough to ensure security?
No. An audit provides a snapshot of security at a specific point in time. Upgrades, integrations, and governance changes can introduce new risks after the audit is complete. Continuous monitoring is necessary to address post-deployment threats.
4. What is the checks-effects-interactions pattern?
It is a coding convention that requires state changes to occur before any external calls are made. This prevents reentrancy attacks by ensuring a contract’s state is accurate before it interacts with outside addresses.
5. What is oracle manipulation in DeFi?
Oracle manipulation involves feeding a smart contract false or distorted external data, often asset prices. Attackers can use flash loans to temporarily distort prices on low-liquidity markets that serve as oracles, causing contracts to make decisions based on incorrect data.
6. What is a reentrancy attack?
A reentrancy attack occurs when a vulnerable contract calls an external address, and that address calls back into the vulnerable contract before the original execution completes, allowing repeated draining of funds the contract still believes are available.
7. How does access control failure manifest in smart contracts?
Access control failures occur when functions intended for authorized users only can be called by any address. Common examples include unprotected initialization functions or administrative actions lacking proper role checks.
8. What is MEV and why does it matter for security?
Maximal extractable value refers to value that can be extracted by miners or validators by reordering, including, or excluding transactions. Front-running is a specific form of MEV that can drain value from users and be exploited in certain contract designs.
9. How can teams test for logic errors in smart contracts?
Fuzz testing tools like Foundry and Echidna help identify edge cases by generating a large variety of inputs automatically. Formal verification provides mathematical proofs of certain contract properties, and peer code review helps catch errors that automated tools may miss.
10. What is the role of continuous monitoring in smart contract security?
Continuous monitoring watches for unusual on-chain behavior after deployment, such as abnormal fund flows or unexpected function calls. It provides early warning of potential exploits and enables faster incident response, complementing pre-deployment auditing.
11. Should upgradeable contracts be treated differently from fixed contracts?
Yes. Upgradeable contracts require additional scrutiny because every upgrade introduces new code that may not have been audited in the context of the current system state. Governance controls, time locks, and review requirements for upgrades are essential.
12. What is the difference between a static analysis tool and a formal audit?
Static analysis tools scan code automatically for known vulnerability patterns. A formal audit involves experienced security researchers manually reviewing code, understanding business logic, and testing assumptions that automated tools may not identify.
13. How do time-weighted average prices reduce oracle manipulation risk?
TWAPs average price data across multiple blocks, making single-block price manipulation significantly more expensive and difficult. An attacker would need to sustain price distortion over multiple blocks to influence a TWAP-based oracle meaningfully.
14. What happens if a vulnerability is found after deployment?
Response options depend on whether the contract is upgradeable. For upgradeable contracts, a patched version can be deployed after governance approval. For fixed contracts, mitigation often involves pausing the protocol if such a function exists, communicating with the community, and coordinating with security researchers.
15. How is smart contract security becoming part of regulatory compliance?
Several jurisdictions are developing frameworks that expect DeFi protocols to demonstrate security practices, including audit documentation, testing evidence, and monitoring capabilities. Institutional investors and insurance providers also increasingly require demonstrated security standards before engaging with a protocol.



