In 2023 alone, blockchain exploits drained over $1.8 billion from DeFi protocols. Most of these attacks were not sudden. They had on-chain signals: hours before funds moved. The difference between the projects that survived and those that lost everything? Real-time blockchain threat monitoring. This overview covers how modern threat alert systems work. It explains the threat landscape, the detection architecture, and what enterprises need in 2026.
The Blockchain Threat Landscape in 2026
Blockchain networks are now critical financial infrastructure. Billions of dollars settle on-chain daily. Attackers know this. They have adapted accordingly. Today’s threats are not random. They are structured, patient, and often multi-step.
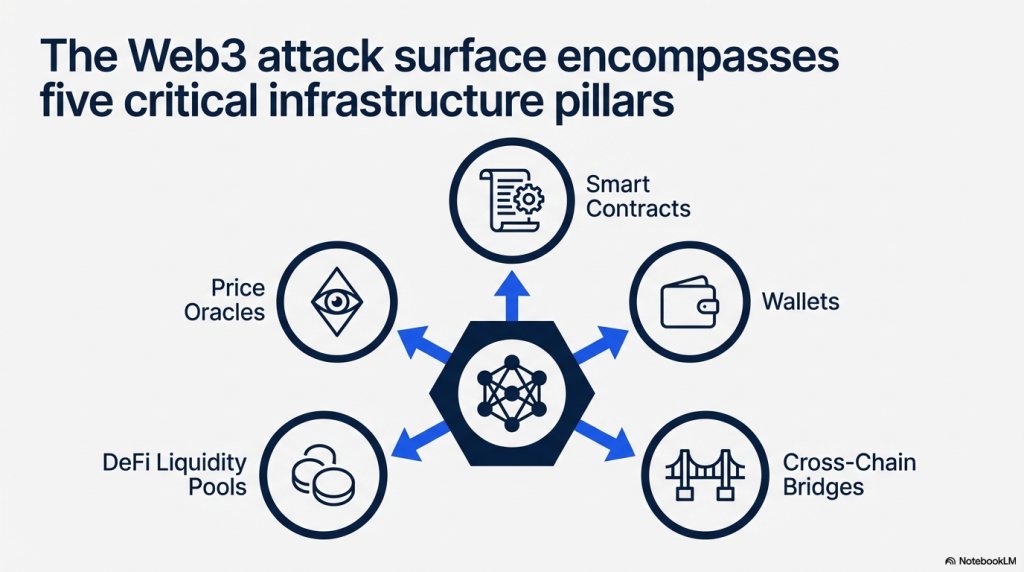
What the Modern Attack Surface Looks Like
Smart contracts hold liquidity. Wallets hold assets. Bridges connect chains. Each layer introduces a different class of vulnerability.

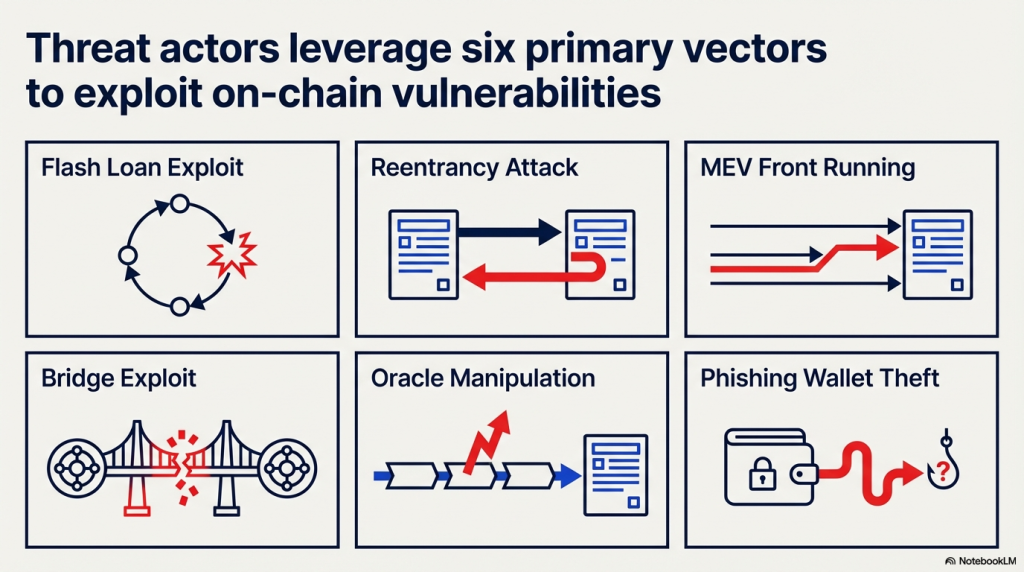
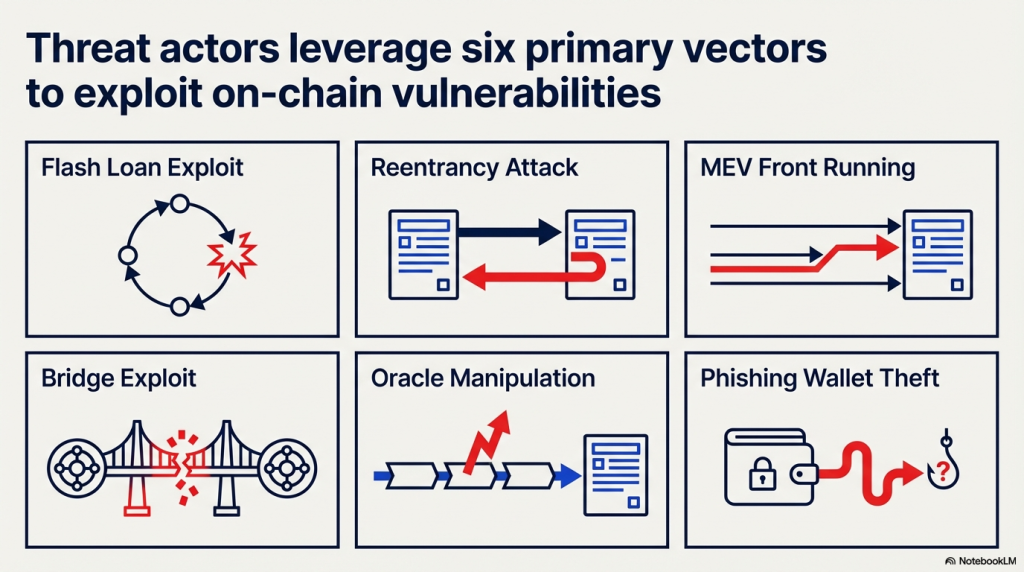
- Flash loan exploits manipulate price oracles within a single transaction block.
- Reentrancy attacks drain contracts by exploiting recursive call logic.
- MEV bots front-run transactions in the mempool before they confirm.
- Bridge exploits compromise cross-chain validation mechanisms.
- Phishing campaigns move funds through layered wallet clusters.
The common thread? Every attack leaves an on-chain signal before or during execution. Real-time detection is about catching that signal before the damage is done.
What Is Real-Time Blockchain Threat Monitoring?
Real-time blockchain threat monitoring is continuous surveillance of on-chain activity. It tracks wallet behaviour, contract interactions, token flows, and transaction patterns. When something deviates from normal, it triggers an alert: or an automated response. This is different from a one-time audit. An audit checks code before deployment. Monitoring watches what happens after.
The Core Components of a Threat Alert System
A functional monitoring system operates across four technical layers:
| Layer | Function | Output |
| Data Ingestion | Reads mempool and confirmed transaction data | Raw transaction stream |
| Behaviour Analysis | Compares patterns against known attack signatures | Anomaly score |
| Alert Engine | Triggers notifications based on rule thresholds | Real-time alert |
| Response Layer | Executes automated containment actions | Contract pause / wallet flag |
Each layer must operate with minimal latency. A delay of even a few seconds can mean the difference between stopping an exploit and losing funds.
How Threat Detection Works on the Blockchain
On-chain monitoring is not the same as traditional network security monitoring. There are no IP addresses or packet headers. Everything is transaction data. Effective detection requires understanding the semantics of that data: not just its structure.
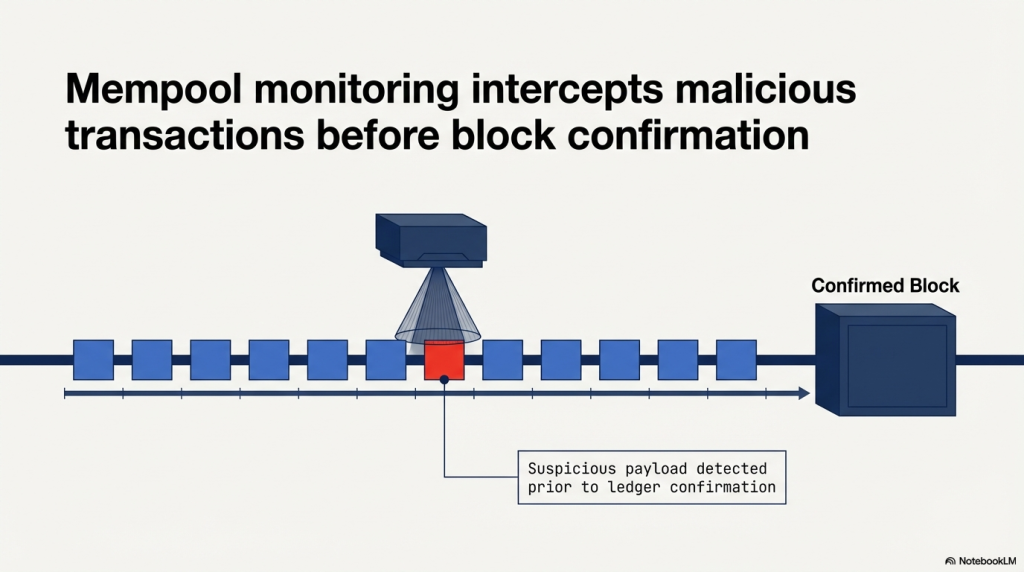
Mempool Monitoring: Catching Attacks Before They Confirm
The mempool is a staging area. Transactions wait here before miners include them in a block. Many exploits: especially flash loan attacks: are visible in the mempool before confirmation. Monitoring the mempool allows early intervention. Alerts can trigger within milliseconds.
Event Log Analysis: Reading What Contracts Emit
Smart contracts emit events during execution. These events are the audit trail of on-chain activity. Unusual event sequences: large transfers, sudden ownership changes, role escalations: are red flags. A well-tuned monitoring system parses event logs in real time and correlates them against threat models.
Wallet Clustering and Behavioural Profiling
Attackers rarely use a single wallet. They route funds through clusters. Effective monitoring systems build wallet behaviour profiles over time. When a wallet suddenly deviates from its historical pattern, it scores higher on the anomaly index. This is particularly useful for detecting money laundering and phishing-based fund movement.
Types of Alerts in a Blockchain Threat Monitoring System
Not all alerts are equal. A mature system distinguishes between severity levels.
| Alert Type | Trigger Condition | Severity |
| Anomalous Fund Flow | Large unexpected transfer from monitored wallet | High |
| Contract Reentrancy Signal | Recursive call pattern detected in transaction trace | Critical |
| Flash Loan Flag | Large borrow + swap + repay within one block | Critical |
| Wallet Cluster Alert | Funds routed through flagged address network | Medium–High |
| Oracle Manipulation Signal | Price feed deviation beyond expected variance | High |
| Ownership Transfer Alert | Admin key or contract ownership changed unexpectedly | Critical |
| MEV Front-Run Detection | Transaction sandwich pattern in mempool | Medium |
Each alert category maps to a specific response protocol. Critical alerts should trigger automated containment. High alerts require immediate human review.
Real-Time Monitoring vs Traditional Security Approaches
Before real-time monitoring became viable, teams relied on static tools. The gap is significant.
| Dimension | Traditional Approach | Real-Time Monitoring |
| Detection Timing | After exploit is confirmed | During or before exploit |
| Response Speed | Hours to days | Seconds to minutes |
| Coverage | Periodic snapshots | Continuous surveillance |
| Threat Intelligence | Manual review | AI-driven pattern analysis |
| Containment | Manual intervention required | Automated policy enforcement |
| Scalability | Limited by analyst bandwidth | Scales with transaction volume |
The gap is not marginal. In blockchain environments, a 10-minute detection delay is catastrophic.
How SecureWatch Operationalises Real-Time Monitoring
SecureDApp’s SecureWatch is built specifically for blockchain runtime threat detection. It is not a log aggregator or a dashboard with delayed data. It is an active defence layer.
What SecureWatch Does
- Monitors on-chain activity across major blockchain networks continuously.
- Applies behavioural anomaly detection models trained on historical attack data.
- Clusters wallet addresses to identify fund-laundering patterns.
- Triggers automated contract pause mechanisms when critical thresholds are breached.
- Integrates with DevSecOps pipelines for continuous security coverage.
The platform allows security teams to define custom policies. When on-chain conditions match a policy, the response is automatic. This reduces the window between detection and containment from minutes to seconds.
The Policy-Based Containment Model
SecureWatch does not just monitor. It acts. Security teams configure response policies based on alert types. Examples include:
- Pause contract withdrawals when flash loan signatures are detected.
- Flag wallet for review when fund flow crosses defined thresholds.
- Alert compliance team when ownership transfer is detected on monitored contract.
This model shifts security from reactive to anticipatory.
The Role of AI in Blockchain Threat Detection
Manual rule-based systems cannot keep pace with evolving attack vectors. Attackers iterate quickly. New exploit patterns emerge weekly in the DeFi space. AI-driven detection models offer an adaptive layer on top of static rule sets.
Machine Learning in Anomaly Detection
ML models learn from historical transaction data. They build a baseline of normal behaviour. When a transaction or wallet deviates from that baseline, the model flags it. The advantage is that ML catches novel attacks: ones that do not match known signatures. This is critical because zero-day exploits, by definition, have no prior signature.
AI Audit + Runtime Monitoring: The Prevention Stack
AI is not only useful at runtime. SecureDApp’s Solidity Shield uses AI for pre-deployment auditing. It scans smart contracts across 150+ vulnerability classes before they go live. When combined with SecureWatch’s runtime monitoring, it creates a full prevention stack:
- Pre-deployment: AI identifies vulnerabilities before the contract is deployed.
- Post-deployment: SecureWatch monitors the contract’s behaviour continuously.
This is the security lifecycle: not a single checkpoint, but continuous vigilance.
Enterprise Implications: Why This Matters for Regulated Organisations
Real-time blockchain threat monitoring is no longer optional for enterprises. Regulators are asking questions. Boards are demanding accountability. A security incident on-chain is now a compliance event: not just a technical failure.
Regulatory Alignment
In India, financial institutions operating in blockchain must align with IFSCA guidelines. Globally, FATF recommendations require transaction monitoring for Virtual Asset Service Providers. A real-time monitoring system provides the audit trail and alert records regulators require.
The Cost of Not Monitoring
Consider the operational cost of a single exploit:
- Direct asset loss: often millions of dollars.
- Protocol reputation damage: user trust erodes immediately.
- Legal and regulatory scrutiny: investigations can take months.
- Team distraction: incident response consumes engineering resources.
A monitoring platform is not an expense. It is risk mitigation infrastructure.
SecureDApp’s Institutional Credibility
SecureDApp is registered with UIDAI as an Offline Verification Seeking Entity (OVSE). This means it operates within India’s formal digital identity and compliance framework. For enterprises in regulated sectors, this is a meaningful signal of institutional alignment. It is especially relevant for organisations exploring blockchain-based KYC through SecureX-DID.
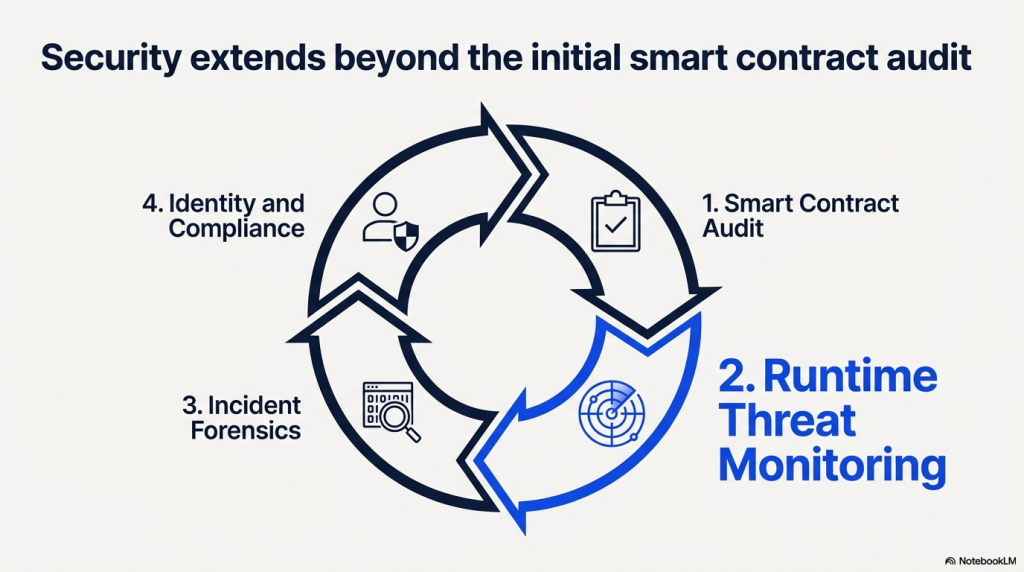
The Full Web3 Security Lifecycle
Threat monitoring is one layer in a broader security infrastructure. SecureDApp covers the entire lifecycle:
| Stage | Product | Function |
| Pre-Deployment | Solidity Shield | AI-powered smart contract vulnerability audit |
| Post-Deployment | SecureWatch | Real-time on-chain anomaly detection and containment |
| Incident Response | SecureTrace | Blockchain forensic investigation and asset tracing |
| Identity & Compliance | SecureX-DID | Decentralised identity with Aadhaar-aligned verification |
No other platform in the Indian Web3 security space integrates all four layers. This is the structural differentiation: not a marketing claim, but an architecture fact.
Building a Threat Monitoring Strategy: Key Considerations
Deploying a threat monitoring system requires more than plugging in a tool. Here are the critical questions every security team must answer:
1. What Are Your Monitored Assets?
Define the scope: Which contracts, wallets, and bridges need coverage? Prioritise by risk and asset value.
2. What Response Policies Make Sense?
Automated responses are powerful: but they must be calibrated carefully. An aggressive pause policy can disrupt legitimate operations. Collaborate with protocol architects to define safe thresholds.
3. How Will Alerts Be Triaged?
A monitoring system that generates noise is worse than no system. Build a tiered alert triage process. Critical alerts need 24/7 coverage.
4. Is the System Audited and Tested?
The monitoring system itself must be secure. Run red team exercises against your detection logic. Test response policies before deploying them in production. Forward-Looking Trends in Blockchain Threat Monitoring The threat monitoring space is evolving rapidly. Here is what to watch in 2026 and beyond.
Cross-Chain Monitoring Becomes Standard
As protocols expand across multiple chains, monitoring must follow. A threat that begins on Ethereum may move funds to Solana within minutes. Cross-chain visibility is no longer optional.
Intent-Based Transaction Analysis
Next-generation systems will not just analyse what a transaction does. They will model what it is trying to do: based on contextual signals. This narrows the detection gap significantly for novel attack patterns.
Regulatory-Mandated Monitoring Infrastructure
Regulators in the EU, US, and India are moving towards mandatory monitoring requirements. Enterprises that build monitoring infrastructure now will have a compliance advantage. Platforms like SecureWatch are designed with this regulatory trajectory in mind.
Conclusion
Real-time blockchain threat monitoring is the foundation of serious Web3 security. Audits are necessary: but they are not sufficient. Code that passes an audit can still be exploited at runtime. The protocols and enterprises that survive the next wave of blockchain attacks will be those that monitor continuously, respond automatically, and treat security as infrastructure: not an afterthought. SecureDApp is built for exactly that environment.
FAQs on Real Time Blockchain Threat Monitoring
It is continuous surveillance of on-chain transactions, wallet activity, and contract behaviour. The system flags anomalies and can trigger automated responses: in real time, not hours later.
An audit checks code before deployment. Monitoring watches what happens after the contract goes live. Both are necessary: they cover different phases of the security lifecycle.
Yes: if configured with automated response policies. Systems like SecureWatch can pause contracts or flag wallets automatically when a threat signature is detected.
Yes. Threat monitoring is not just for large exchanges. Any protocol holding user funds needs this layer. The cost of monitoring is always lower than the cost of an exploit.
SecureWatch combines behavioural anomaly detection, wallet clustering, policy-based containment, and DevSecOps integration. It is one layer of SecureDApp’s full four-layer security stack: which also covers auditing, forensics, and identity.



