Blockchain is no longer a niche experiment. It is the backbone of trillion-dollar ecosystems, decentralized finance platforms, and institutional-grade digital infrastructure. Yet, for all its innovation, the blockchain space continues to bleed value through exploits, flash loan attacks, rug pulls, and smart contract vulnerabilities.

The problem is not that threats do not exist. The problem is that most teams discover them too late.
On-chain threat monitoring has become a non-negotiable discipline for anyone serious about protecting blockchain-based systems. In 2026, the tools available to security teams have grown sharper, faster, and significantly more intelligent. This guide covers the top 10 on-chain threat detection tools that security professionals, DeFi founders, and blockchain developers should understand and consider for their stack.
Why On-Chain Threat Monitoring Matters More Than Ever in 2026
Before diving into the tools, it is worth understanding why this space has exploded in importance. Over the past three years, on-chain attacks have grown in both frequency and sophistication. Threat actors no longer rely on simple exploits. They use layered attack patterns that unfold across multiple blocks, sometimes within a single transaction.
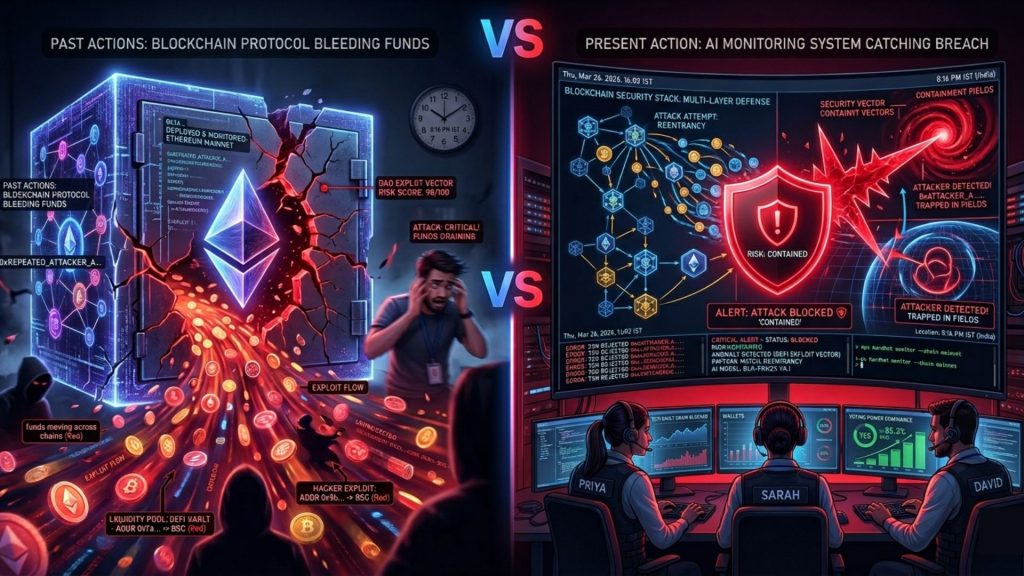
Most teams invest heavily in pre-deployment audits. However, a critical insight often gets overlooked: the majority of high-value exploits happen after deployment, not before it. An audit is a snapshot. An on-chain threat monitoring system is a continuous guard.
Furthermore, the regulatory landscape is tightening. Jurisdictions across the globe, including India, the European Union, and the United States, are increasingly requiring DeFi platforms and crypto-native businesses to demonstrate active security monitoring. Passive security postures are no longer acceptable.
With that context established, here are the top 10 on-chain threat detection tools making the biggest impact in 2026.
1. SecureWatch by SecureDApp
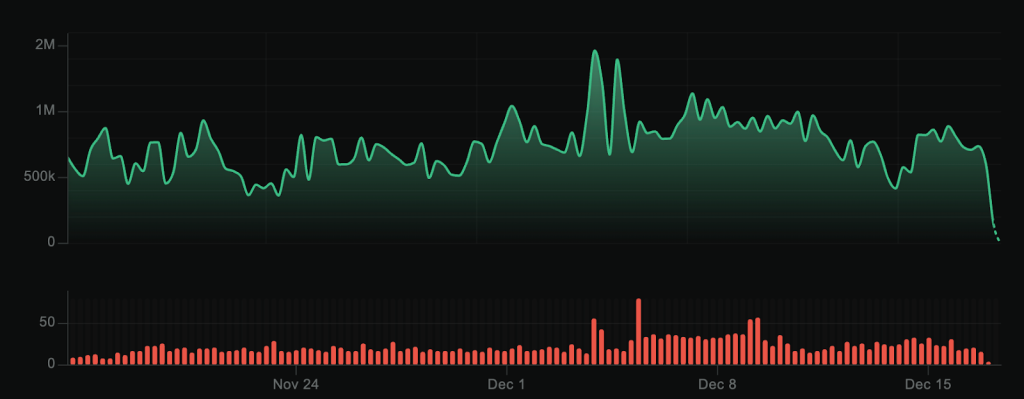
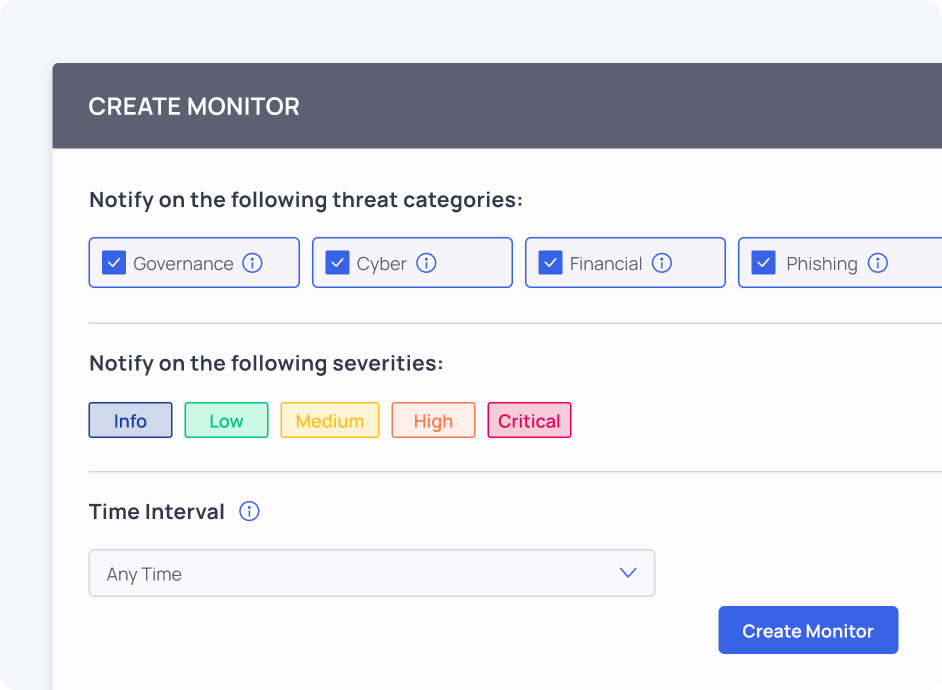
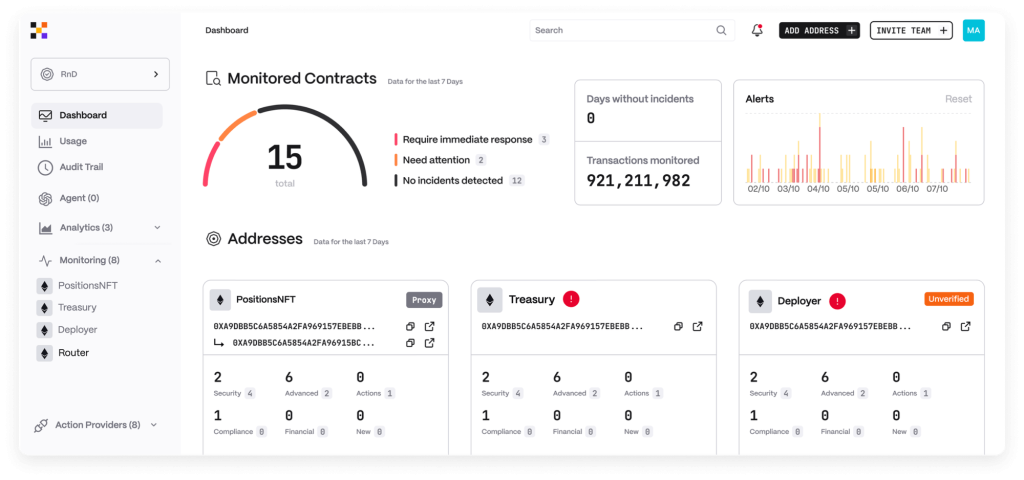
SecureWatch stands as one of the most advanced on-chain threat monitoring platforms available in 2026. Built specifically for blockchain environments, it combines AI-driven threat detection with continuous post-deployment surveillance across multiple chains.
What makes SecureWatch genuinely different is its AutoPause feature. When suspicious activity is detected, the system can automatically pause vulnerable transactions or halt specific contract interactions before damage spreads. This is not a passive alert system. It is an active mitigation layer built directly into the monitoring pipeline.
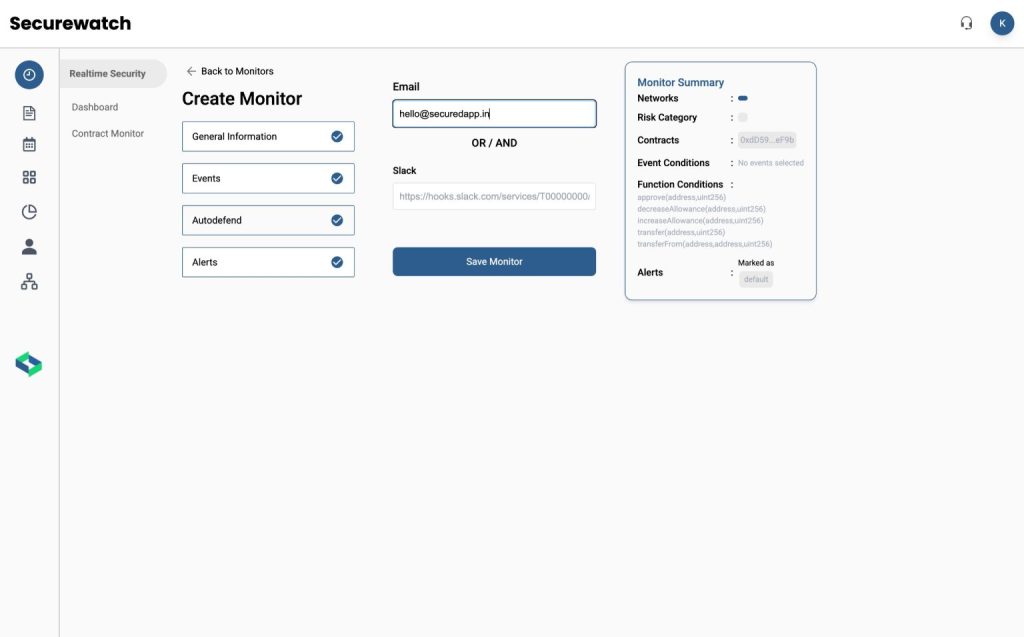
SecureWatch is a patented product under the Government of India, which adds a significant layer of credibility and trust for institutional deployments. For teams operating in Web3, DeFi, or enterprise blockchain environments, SecureWatch delivers the kind of real-time on-chain threat monitoring that modern security operations demand. It supports multi-chain coverage, providing a unified view across multiple blockchain networks without requiring teams to juggle separate dashboards.
Moreover, its integration with SecureTrace adds forensic investigation capabilities, making it a comprehensive platform for both detection and response.
2. Forta Network
Forta Network is a decentralized threat detection protocol that enables developers and security researchers to deploy custom detection bots across multiple blockchain networks. In 2026, Forta continues to be a widely adopted foundation layer for on-chain threat monitoring.
Its strength lies in its open, community-driven model. Security researchers can publish detection bots for specific threat patterns, and teams can subscribe to relevant alert feeds. Forta covers smart contract exploits, bridge attacks, whale wallet movements, and governance manipulation attempts.
However, Forta requires technical effort to configure and maintain. Teams without dedicated security engineers may find the setup process demanding. Still, for mature security teams, Forta remains a foundational piece of the on-chain detection stack.
3. MISP
MISP is an open-source threat intelligence platform used for sharing and organizing security data across teams and organizations. It is commonly applied in traditional cybersecurity environments and can also support broader security workflows.
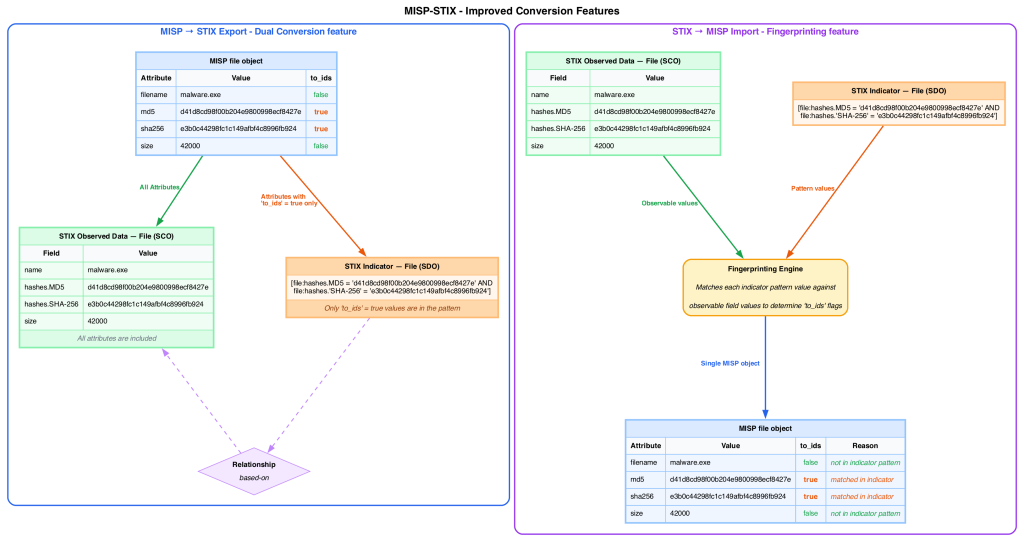
The platform enables the collection and correlation of indicators, helping teams identify patterns and maintain awareness of potential threats. While it is not specifically designed for on-chain monitoring, it can be used alongside other tools to provide additional context during analysis.
MISP also supports information sharing in near real time, which can assist teams in coordinating responses and improving overall visibility into emerging risks.
4. Chainalysis
Chainalysis Reactor is an investigative and intelligence platform widely used by exchanges, compliance teams, and law enforcement agencies. Its relevance to on-chain threat monitoring comes from its ability to map adversarial wallets, track fund flows, and identify exposure to known malicious addresses.
In 2026, Chainalysis has expanded its real-time monitoring capabilities. Teams can now receive automated alerts when wallets associated with their platform interact with flagged entities. This is especially valuable for DeFi protocols and centralized exchanges navigating compliance requirements.
Reactor excels at post-incident investigation, though its pricing and institutional focus make it better suited for larger organizations than early-stage blockchain projects.
5. Hacken
Hacken is a Web3 security provider focused on helping blockchain projects identify and reduce risk. Its offerings include smart contract audits, penetration testing, and ongoing security monitoring for decentralized applications and protocols.
Rather than concentrating only on incident response, Hacken takes a broader approach that includes preventative measures such as audits and vulnerability discovery. This allows teams to address potential weaknesses before they can be exploited.
The firm has worked with a range of blockchain projects and platforms, reflecting its involvement across different parts of the Web3 ecosystem.
6. Hypernative
Hypernative provides AI-powered risk detection for blockchain protocols, wallets, and DeFi applications. Its platform monitors for a wide range of threat categories, including smart contract vulnerabilities being exploited, unusual fund flows, governance attacks, and cross-chain bridge anomalies.

In 2026, Hypernative is recognized for its low false-positive rate. Many on-chain threat monitoring systems flood security teams with noise, leading to alert fatigue. Hypernative’s model is trained to distinguish genuine threats from routine on-chain activity with high precision.
The platform integrates directly with popular DeFi protocols and provides actionable alerts with enough context for teams to respond quickly. Its multi-chain support covers Ethereum, Solana, Avalanche, BNB Chain, and several others.
7. OpenZeppelin Defender Sentinel
OpenZeppelin Defender has been a trusted name in smart contract security for years. Its Sentinel feature allows teams to monitor transactions in real time and trigger automated responses based on predefined conditions. In 2026, Defender Sentinel has become an important component of operational on-chain threat monitoring for development teams.
Sentinels can watch for specific function calls, unusual gas usage spikes, or events emitted by a contract. When triggered, the system can send notifications, call admin functions, or pause contracts automatically through the relayer module.
OpenZeppelin Defender is particularly well-suited for teams that already use the OpenZeppelin smart contract library, as integration is seamless. For teams seeking a developer-first approach to on-chain threat monitoring, Defender remains a strong and battle-tested choice.
8. Anomali ThreatStream
Anomali ThreatStream is a threat intelligence platform used to collect, analyze, and manage security data from multiple sources. It is widely used in traditional cybersecurity environments to support monitoring and risk assessment workflows.
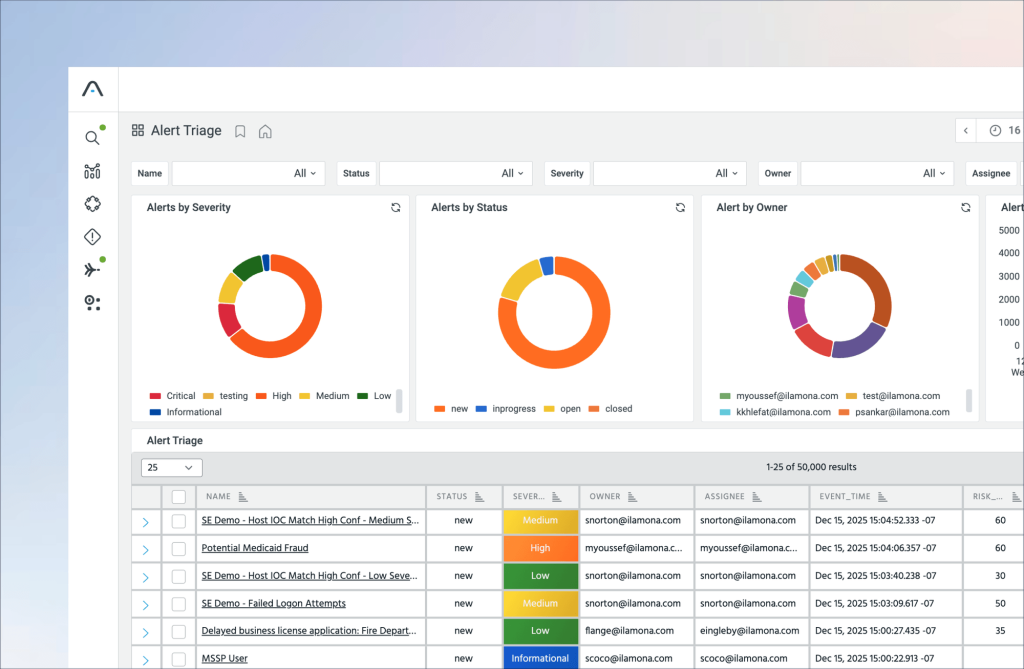
The platform focuses on aggregating threat indicators, such as IP addresses, domains, and malware signatures, and correlating them to identify patterns that may indicate malicious activity. This approach helps teams gain a clearer understanding of potential threats and their context.
It also supports investigation and response processes by organizing intelligence into a structured format, enabling teams to track activity and improve visibility into evolving security risks.
9. Nansen
Nansen approaches on-chain threat monitoring from an analytics and intelligence perspective. While it is best known for wallet labeling and market intelligence, Nansen’s alert system and portfolio monitoring tools serve a meaningful security function in 2026.
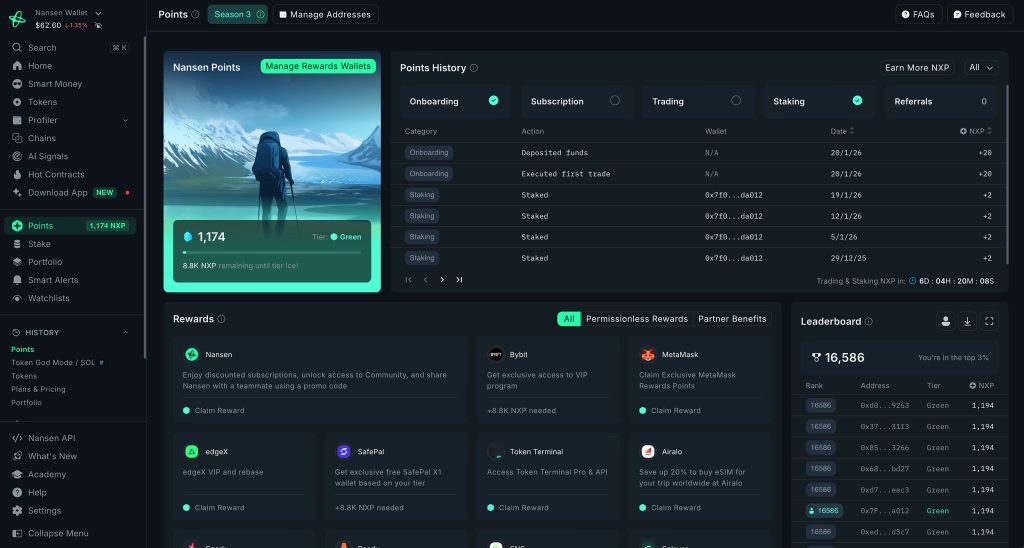
Security teams and protocol operators can track labeled wallets associated with known exploiters, hacking groups, and dark web entities. When these wallets begin interacting with a protocol or accumulating a specific token, it often signals elevated risk weeks before an attack materializes.
Nansen is particularly valuable for teams that want to monitor the threat environment at the strategic level, understanding attacker behavior patterns and the economic signals that precede major exploits.
10. Certik Skynet
Certik Skynet is a continuous security monitoring platform integrated with Certik’s broader audit and intelligence ecosystem. It provides on-chain threat monitoring across multiple dimensions, including smart contract risk scoring, community trust signals, governance health, and active vulnerability alerts.
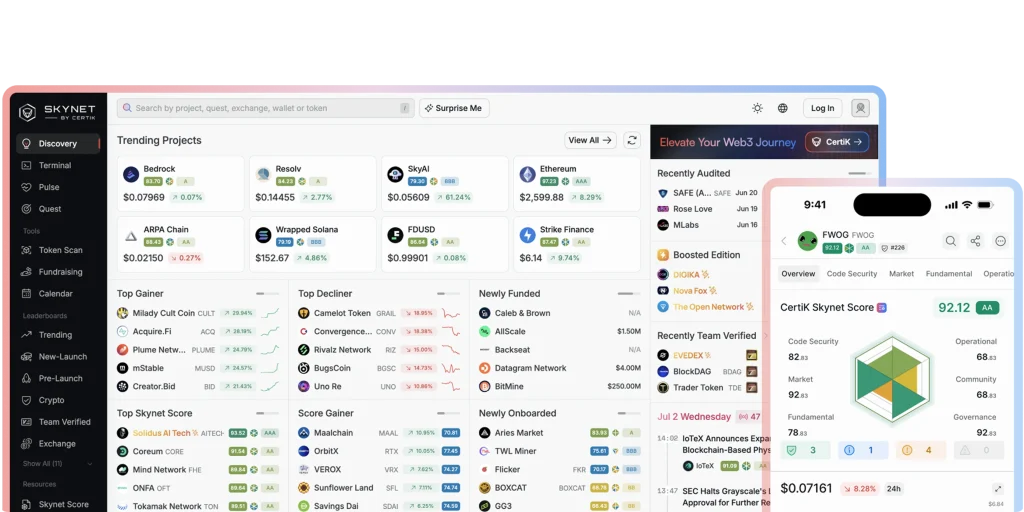
In 2026, Skynet has expanded its real-time incident detection capabilities. When an exploit is detected on any monitored protocol, Skynet distributes rapid alerts to subscribed teams, enabling faster awareness and response across the ecosystem.
Skynet is well-suited for DeFi protocols seeking a monitoring solution that combines technical detection with reputation and trust layer visibility. Its public-facing dashboards also serve a transparency function, showing the broader community the health status of monitored protocols.
How to Choose the Right On-Chain Threat Monitoring Tool
With ten strong options on the table, the real question is which tool fits your specific environment. A few factors worth considering:
Chain Coverage. Ensure the platform monitors all the networks your protocol or product operates on. Multi-chain deployments need multi-chain monitoring.
Detection Speed. Time is the most valuable asset in an exploit scenario. Tools that detect threats at the mempool level or simulation stage offer a meaningful advantage over those that alert only after a transaction confirms.
Response Automation. Detection alone is not enough. The best on-chain threat monitoring systems, like SecureWatch with AutoPause, can take automated action to limit damage before a human can even respond.
Integration Depth. Consider how easily a tool integrates with your existing operations, notification systems, and incident response playbooks.
Accuracy and Noise Control. High false-positive rates erode trust in monitoring systems. Teams start ignoring alerts, which defeats the entire purpose. Prioritize tools with demonstrated signal accuracy.
The Role of AI in On-Chain Threat Monitoring
Artificial intelligence has fundamentally changed what is possible in this space. Traditional rule-based detection systems struggle against novel attack vectors because they can only identify threats that have been seen before. AI-powered systems, by contrast, can identify anomalous patterns in transaction behavior even when the specific attack vector is new.
In 2026, the most capable on-chain threat monitoring platforms use machine learning models trained on historical exploit data, normal transaction distributions, and adversarial simulation outputs. The result is detection that is faster, broader, and more nuanced than static rules alone can provide.
SecureWatch, Hypernative, and Hexagate are all investing heavily in AI-driven detection layers, and that investment is paying dividends in real-world performance.
Common Gaps in Blockchain Security That On-Chain Monitoring Fills
Even the best-audited smart contracts can be exploited. Audits identify vulnerabilities in code at a point in time. They cannot anticipate how a contract will behave when real users interact with it in combination with other protocols, market conditions, and unpredictable on-chain state.
On-chain threat monitoring fills that gap by watching live behavior continuously. It bridges the distance between pre-deployment assurance and post-deployment reality. For teams serious about security, monitoring is not optional. It is the layer that makes every other security investment more effective.
Furthermore, on-chain monitoring provides valuable data for incident response. When something goes wrong, the ability to reconstruct exactly what happened, wallet by wallet and transaction by transaction, is critical for understanding the attack, communicating with stakeholders, and strengthening defenses.
Conclusion
On-chain threat monitoring is one of the most important disciplines in blockchain security today. As ecosystems grow more complex, as DeFi protocols become more interconnected, and as the value at stake continues to climb, the cost of inadequate monitoring becomes impossible to ignore.
The ten tools covered in this guide represent the strongest options available in 2026 across different use cases, team sizes, and technical requirements. From the continuous AI-driven detection and AutoPause mitigation of SecureWatch, to the decentralized bot network of Forta, to the economic attack intelligence of Hexagate, each platform addresses a specific dimension of the threat landscape.
Ultimately, no single tool covers every scenario. The most resilient security postures combine strong pre-deployment auditing through solutions like Solidity Shield with continuous post-deployment on-chain threat monitoring via platforms like SecureWatch. Detection must be fast, response must be faster, and the intelligence informing both must be current.
The question for every blockchain team in 2026 is not whether they need on-chain threat monitoring. The question is whether they can afford to be without it.
Frequently Asked Questions (FAQs)
1. What is on-chain threat monitoring?
On-chain threat monitoring is the continuous surveillance of blockchain transactions, smart contract behavior, and wallet activity to detect and respond to security threats in real time. It operates on live blockchain data rather than relying solely on pre-deployment audits.
2. Why is on-chain monitoring important for DeFi protocols?
DeFi protocols handle large volumes of value through automated smart contracts. Without real-time monitoring, exploit attempts, flash loan attacks, and oracle manipulations can drain funds before any human intervention is possible.
3. What is the difference between a smart contract audit and on-chain monitoring?
A smart contract audit is a one-time or periodic review of code for vulnerabilities. On-chain monitoring is continuous and watches live transaction behavior, filling the gap that audits cannot cover after deployment.
4. Can on-chain threat monitoring prevent attacks automatically?
Yes, certain platforms like SecureWatch include automated mitigation features. The AutoPause feature, for example, can automatically pause suspicious transactions or contract activity when a threat is detected, limiting damage without requiring human intervention.
5. What blockchains do these tools support?
Most enterprise-grade on-chain threat monitoring tools support major networks including Ethereum, BNB Chain, Polygon, Avalanche, Solana, and various layer-2 networks. Coverage varies by platform, so teams should verify support for their specific chains.
6. How does AI improve on-chain threat detection?
AI models can identify anomalous patterns in transaction behavior that would not match any predefined rule. This is especially valuable for detecting novel attack vectors that have not been seen in previous exploits.
7. Is on-chain monitoring only relevant for large protocols?
No. Smaller protocols are often more attractive targets precisely because they tend to have weaker security postures. On-chain threat monitoring is relevant for any project that handles real value on-chain.
8. How fast can on-chain threat monitoring systems detect attacks?
The best systems operate at the mempool level, detecting threats before transactions are confirmed on-chain. This provides the fastest possible window for intervention, sometimes within seconds of an attack initiating.
9. What is AutoPause and why does it matter?
AutoPause is a mitigation feature in SecureWatch that can automatically pause suspicious transactions or smart contract activity when a threat is detected. It reduces the window of exposure without waiting for manual response.
10. How does on-chain monitoring help with regulatory compliance?
Many regulatory frameworks now require active security monitoring for blockchain platforms. On-chain monitoring provides audit trails, real-time alerting, and incident documentation that support compliance reporting and demonstrate due diligence to regulators.
11. What is the role of wallet labeling in threat detection?
Wallet labeling, as used by tools like Nansen and Chainalysis, associates known malicious or high-risk wallet addresses with historical exploit activity. When these wallets interact with a monitored protocol, teams receive early warning signals.
12. Can on-chain monitoring detect insider threats?
It can detect anomalous behavior consistent with insider threats, such as unusual access patterns, large unauthorized fund movements, or governance manipulation. However, attribution of intent requires additional investigation.
13. What is mempool monitoring and how does it help?
The mempool contains transactions that have been submitted to the network but not yet confirmed. Monitoring at this layer allows detection of potentially harmful transactions before they finalize, enabling preemptive action.
14. How do I integrate on-chain threat monitoring with my existing operations?
Most platforms offer webhook notifications, API integrations, and direct connections to communication tools like Slack, PagerDuty, and email. Some, like OpenZeppelin Defender, also offer automated response capabilities tied to contract admin functions.
15. What should I look for when selecting an on-chain monitoring tool?
Key factors include chain coverage, detection speed, response automation capabilities, false-positive rate, integration options, and the depth of threat intelligence underlying the detection models. The ability to take automated mitigation action, not just send alerts, is increasingly important.



