In 2023, on-chain exploits drained over $1.7 billion from DeFi protocols, exchanges, and cross-chain bridges. By 2025, that figure had not declined – it had reorganized. Rather than relying on quick, opportunistic attacks, threat actors now operate with forensic patience. They map contract logic, identify mempool timing windows, and stage multi-step extraction campaigns that unfold across hours or days before anyone notices.
The threat surface has also expanded significantly. Enterprise adoption of blockchain infrastructure, across financial services, supply chain, healthcare data provenance, and digital identity – means security failures now carry consequences far beyond protocol losses. Today, regulatory penalties, reputational damage, and cross-border legal exposure follow every major on-chain incident.
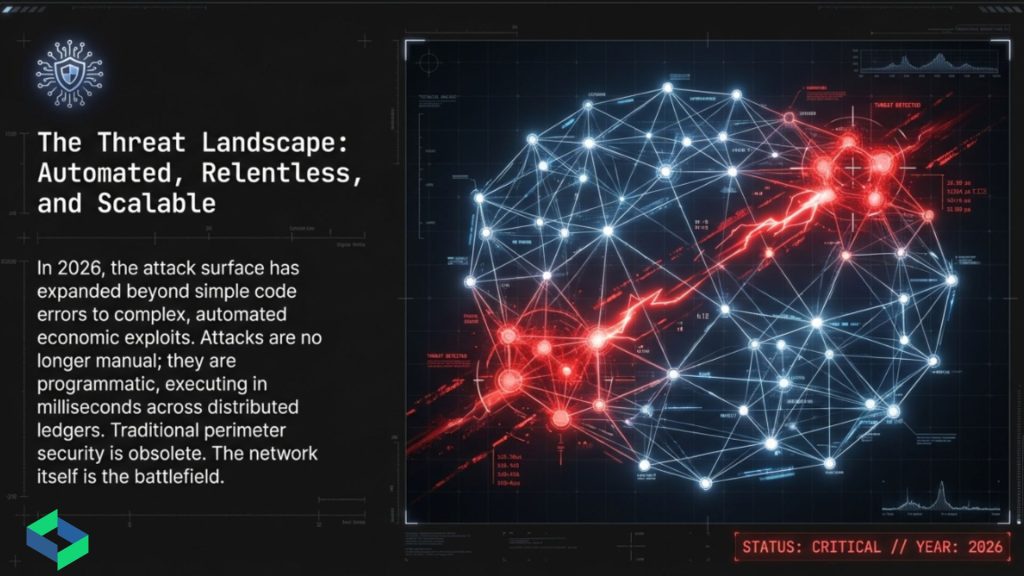
As a result, the old model of “deploy and audit once” is no longer viable. What enterprises need instead is a layered security architecture: preventive controls at the contract level, continuous surveillance after deployment, forensic-grade investigation tools for incident response, and sound identity infrastructure that eliminates PII exposure.
This guide maps that full architecture – from vulnerability classes and detection logic to compliance frameworks and forensic methods. It is written for security practitioners, architects, and compliance officers responsible for protecting blockchain infrastructure at enterprise scale.
Part I: Understanding Blockchain Security Architecture
What Blockchain Security Actually Means in 2026
Blockchain security is not a single discipline. It is, in fact, a multi-layer problem spanning four distinct operational zones, each with its own threat model, detection surface, and remediation approach.
Zone 1 – Pre-Deployment (Smart Contract Security): The attack surface begins the moment a contract is written. Logic flaws, improper access control, unchecked external calls, reentrancy patterns, and ERC-standard incompatibilities create exploit pathways that survive deployment if not caught during audit.
Zone 2 – Post-Deployment (On-Chain Threat Monitoring): A contract that passes audit is not static. Attacker behavior evolves over time, and new dependency vulnerabilities emerge. Contract interactions in live environments generate behavioral signals that no static audit can anticipate. Consequently, continuous monitoring of transaction flows, wallet behavior, and on-chain state changes becomes the only reliable post-deployment defense.
Zone 3 – Post-Incident (Forensic Investigation): When an exploit occurs – and for organizations at scale, incidents are a matter of when, not if – the ability to reconstruct transaction timelines, trace extracted funds, map entity relationships, and produce legally sound documentation determines both asset recovery probability and regulatory outcome.
Zone 4 – Identity and Compliance (Decentralized Identity Infrastructure): Every entity interacting with a blockchain environment carries an identity footprint. Traditional centralized identity systems create data honeypots and compliance drag. In contrast, decentralized identity infrastructure built on zero-knowledge proofs and W3C DID standards eliminates PII exposure while maintaining full verifiability.
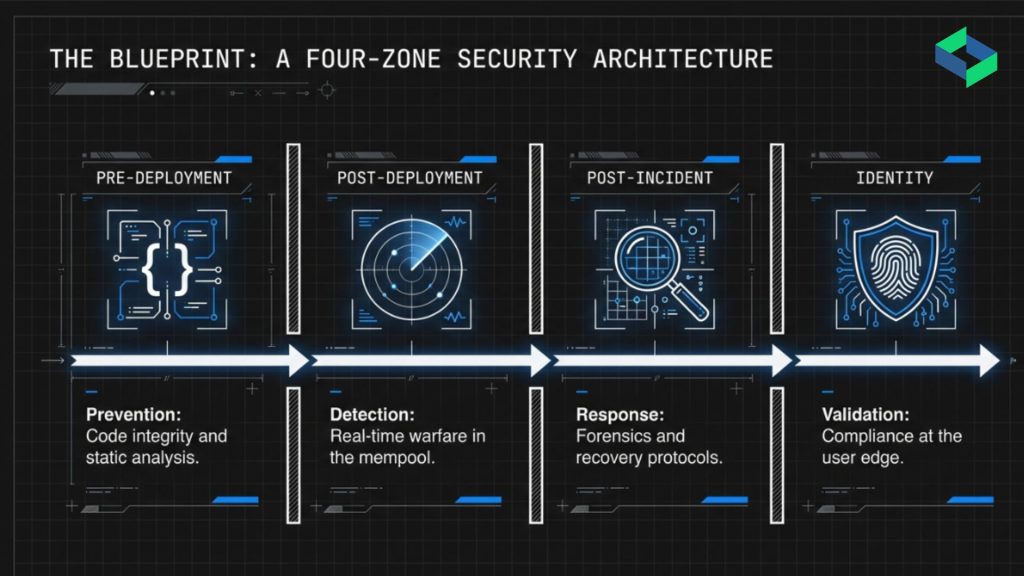
Each zone represents a distinct security problem. Organizations that address only one or two zones may feel protected – yet remain exposed across the others.
The Distributed Ledger as a Security Architecture
Understanding blockchain security requires clarity on what the underlying architecture actually provides – and what it does not.
A blockchain is a distributed database where records are maintained across multiple nodes at once. Each block of transactions is cryptographically linked to the one before it, creating an append-only ledger that is extremely hard to alter retroactively. Consensus mechanisms, proof of work, proof of stake, delegated variants – enforce agreement on ledger state without requiring a trusted central party.
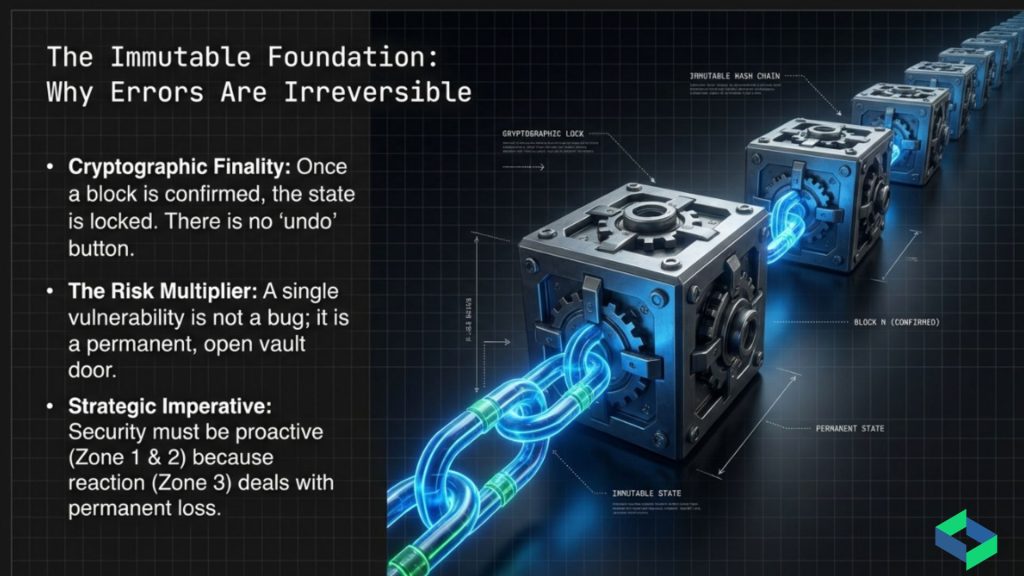
What the Chain Guarantees and What It Does Not
This architecture provides strong guarantees on data permanence, transaction ordering, and censorship resistance. However, it does not provide application-layer security. Smart contracts execute based on their code – meaning flawed code executes its flaws just as reliably, at scale, with no rollback option.
The cryptographic strength of the chain is separate from the security of what runs on it. An audited, well-built smart contract running on a compromised permissioned node network is only as secure as that network’s weakest validator. At the same time, a sound validator set cannot compensate for a contract with an unchecked reentrancy path.
This gap – between chain-level security and application-layer security – is the root cause of most misaligned security expectations in blockchain deployments.
Part II: Smart Contract Vulnerabilities – The Pre-Deployment Attack Surface
Taxonomy of Smart Contract Vulnerability Classes
Smart contract vulnerabilities fall into clear categories based on where they originate in the code. Understanding these categories shapes audit methodology, detection tooling, and remediation priority.
Reentrancy Attacks
The reentrancy vulnerability remains the most damaging class by historical losses. It occurs when a contract makes an external call before updating its internal state. This timing gap allows the callee to recursively invoke the caller and drain funds before the balance check runs. The DAO hack in 2016 extracted roughly $60 million via this mechanism. Despite nearly two decades of documentation, reentrancy patterns still appear in production contracts – largely due to developer oversight and non-obvious call paths in complex multi-contract systems.
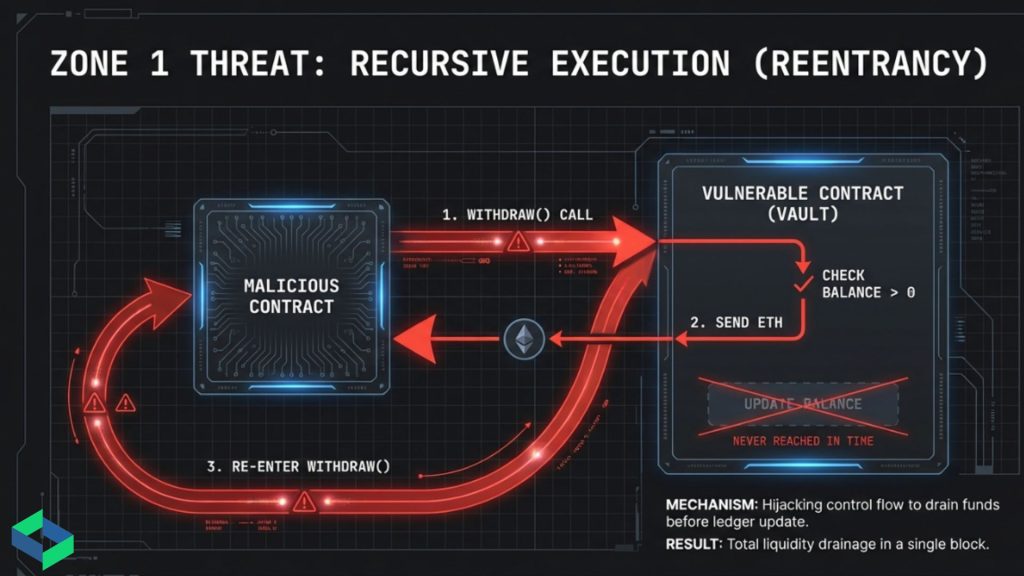
Detection requires tracing all external call sequences against state update ordering. Moreover, automated analysis must map execution paths across the full contract dependency graph, not just isolated function analysis.
Unchecked Return Values
Many Solidity functions return Boolean success indicators. When left unchecked, silent failures proceed as successes. Token transfers that appear to succeed but do not actually move funds create economic gaps that attackers exploit – typically by building transaction sequences that depend on the silent failure.
Integer Overflow and Underflow
Prior to Solidity 0.8.0, arithmetic operations did not revert on overflow or underflow automatically. Values wrapping around could, for example, turn a large withdrawal into a near-zero balance – or inflate a token allowance from zero to the maximum uint256 value. Legacy contracts compiled below version 0.8.0 still carry this risk without explicit SafeMath implementations.
Access Control Misconfiguration
Missing or incorrectly set access modifiers expose admin functions – ownership transfer, fund withdrawal, parameter changes – to unauthorized callers. In practice, attacker reconnaissance often starts by mapping a contract’s access control graph to find privileged functions without adequate restriction.
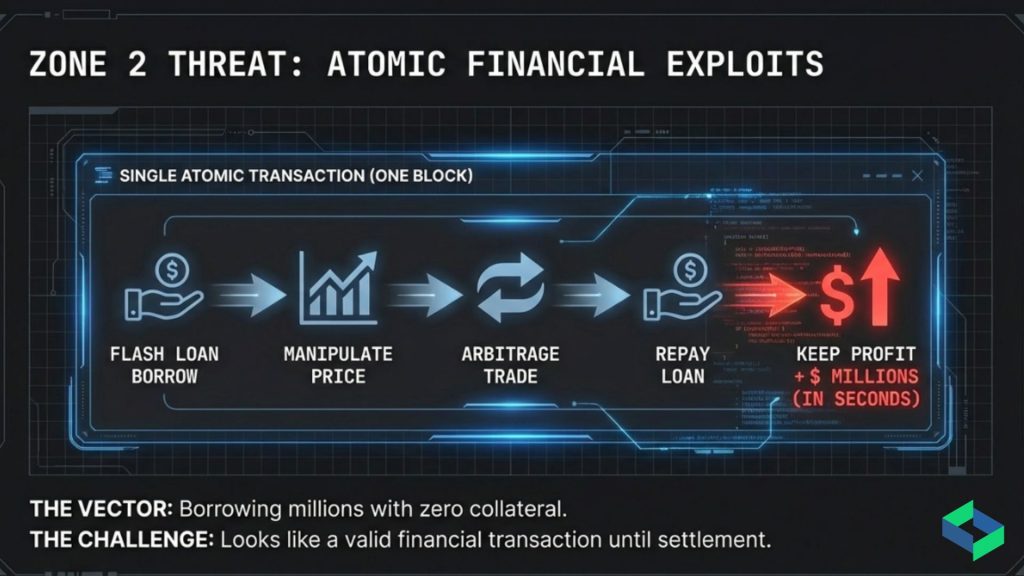
Flash Loan Attack Vectors
Flash loans allow uncollateralized borrowing within a single transaction, provided the borrowed amount is returned before that transaction closes. When combined with price oracle manipulation, governance token accumulation, or liquidity pool imbalance, flash loans enable attacks that require no upfront capital. The economic logic works like this: an attacker borrows a large sum, uses it to distort on-chain price discovery, executes a dependent exploit, profits, and repays the loan – all within one atomic transaction.
The 2021–2023 period saw flash loan attacks drain hundreds of millions across multiple protocols. As a result, detection now requires monitoring for transaction-level anomalies: single-block liquidity imbalances, oracle price deviations outside statistical baselines, and large single-transaction borrowing events tied to protocol interactions.
Logic Flaws and Business Rule Violations
Beyond standard vulnerability patterns, contracts often contain protocol-specific logic errors: wrong reward formulas, missing validation on governance vote weights, or improper handling of edge cases in liquidation logic. These flaws are not detectable by pattern-matching tools alone – they require semantic understanding of protocol intent versus actual implementation.
ERC Standard Incompatibility
Tokens claiming ERC-20 or ERC-721 compliance but failing to handle edge-case behavior correctly – fee-on-transfer tokens treated as standard transfers, non-standard return values, missing interface implementations – create integration vulnerabilities when protocols assume full specification compliance.
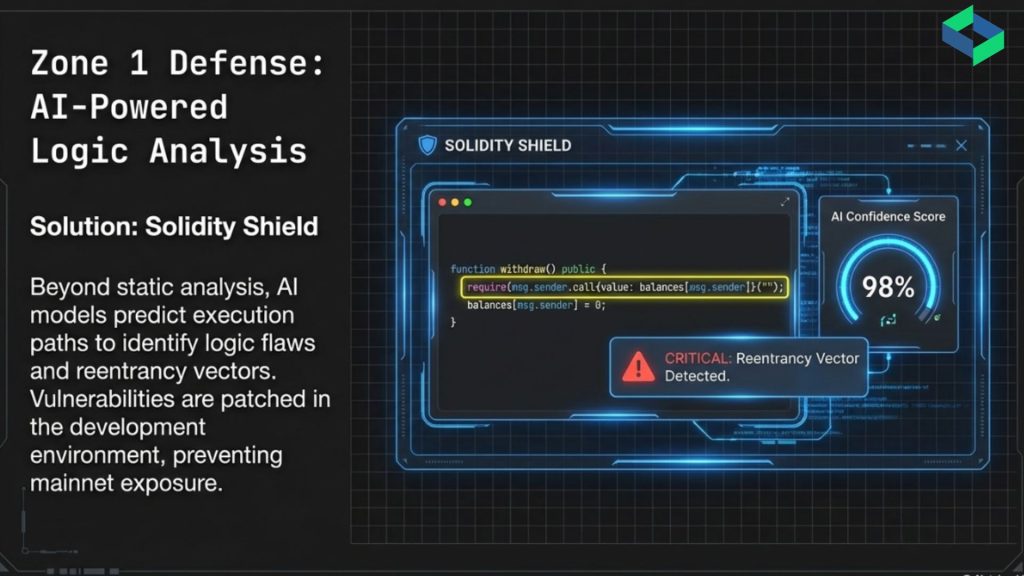
AI-Powered Smart Contract Audit: The Solidity Shield Model
Manual smart contract auditing is a structural bottleneck. Expert auditors are scarce, lead times are long, and the cost of traditional auditing pushes teams to compress audit scope. The outcome is that many contracts reach production with incomplete coverage.
How Automated AI Audit Addresses the Gap
AI-powered audit systems tackle this limitation by combining automated vulnerability scanning with machine learning pattern recognition trained on the full history of known exploits. Solidity Shield uses this model for Solidity-based Ethereum contracts – detecting 150+ vulnerability classes, including reentrancy, unchecked transfers, gas inefficiencies, logic flaws, ERC incompatibility, and security misconfiguration – with analysis completing in under one minute even for complex contracts.
The key advantage here is not speed alone – it is coverage consistency. Automated AI analysis applies the same level of scrutiny to every function, every execution path, and every external call. This eliminates the coverage gaps that human fatigue and time pressure introduce during manual review. Additionally, audit history dashboards give teams visibility into how contract security evolves across development iterations.
That said, AI-powered audit does not remove the need for manual review of protocol-specific business logic. Therefore, the most effective audit method combines automated coverage of known vulnerability patterns with expert review focused on whether the code does what the protocol design actually intends. Solidity Shield serves as the preventive security layer that augments – and substantially speeds up – this combined approach.
Part III: Post-Deployment Threat Monitoring – The Live Attack Surface
Why Static Audit Is Not Enough for Deployed Contracts
A deployed smart contract is a live target operating in a hostile environment. The threat model post-deployment differs fundamentally from pre-deployment analysis.
Attackers continuously probe deployed contracts for behavioral edge cases that audit did not anticipate. New dependency vulnerabilities emerge – an audited contract interacting with an unaudited third-party protocol inherits that protocol’s risk surface. Furthermore, governance mechanisms can be manipulated gradually through token accumulation strategies that no one-time audit could detect. MEV (maximal extractable value) actors also monitor mempool state to front-run, sandwich, or back-run transactions – extracting value without triggering any anomaly visible to the protocol itself.
The real question is not whether an audit was thorough – it is whether the runtime environment still matches the assumptions under which that audit was conducted. Over time, it rarely does.
Real-Time On-Chain Threat Monitoring: Architecture and Detection Logic
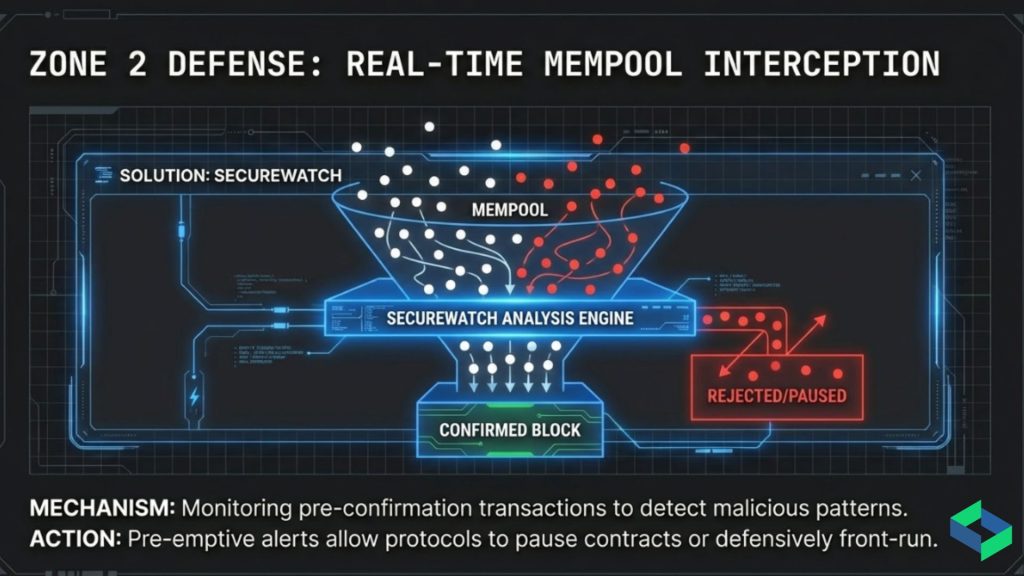
Real-time on-chain threat monitoring works across three detection layers: mempool surveillance, confirmed transaction analysis, and behavioral modeling.
Layer 1: Mempool Surveillance
The mempool – the pool of pending, unconfirmed transactions – is the earliest detection signal available. Attackers often broadcast transaction sequences to the mempool before execution, creating a detection window measured in seconds. Even so, that window is sufficient for automated alerting systems. Mempool monitoring detects front-running preparation, unusually large pending withdrawals from known protocol contracts, and gas price anomalies consistent with priority fee bidding ahead of an exploit.
Layer 2: Confirmed Transaction Analysis
On-chain monitoring of confirmed transactions processes event logs, state change deltas, and transaction trace data to identify behavioral anomalies against established baselines. Key signals include:
- Abnormal transaction volume spikes against a contract within a rolling time window
- Unusual wallet behavior: new wallets hitting high-value contracts immediately after creation
- Parameter tampering: function call arguments outside normal operational ranges
- Privilege escalation attempts: calls to admin functions from non-whitelisted addresses
- Flash loan patterns: large single-transaction borrow-interact-repay sequences across monitored protocols
- Cross-protocol fund movements consistent with laundering or obfuscation
Layer 3: Behavioral Modeling and Anomaly Detection
Baseline behavioral models, trained on historical transaction data, establish what “normal” looks like for a given protocol. Deviations from that baseline – in volume, timing, caller patterns, gas usage, or interaction sequences – trigger graduated alert thresholds. Machine learning anomaly detection further identifies novel attack patterns that do not match known exploit signatures, reducing reliance on signature-only detection logic that struggles against new attack methods.
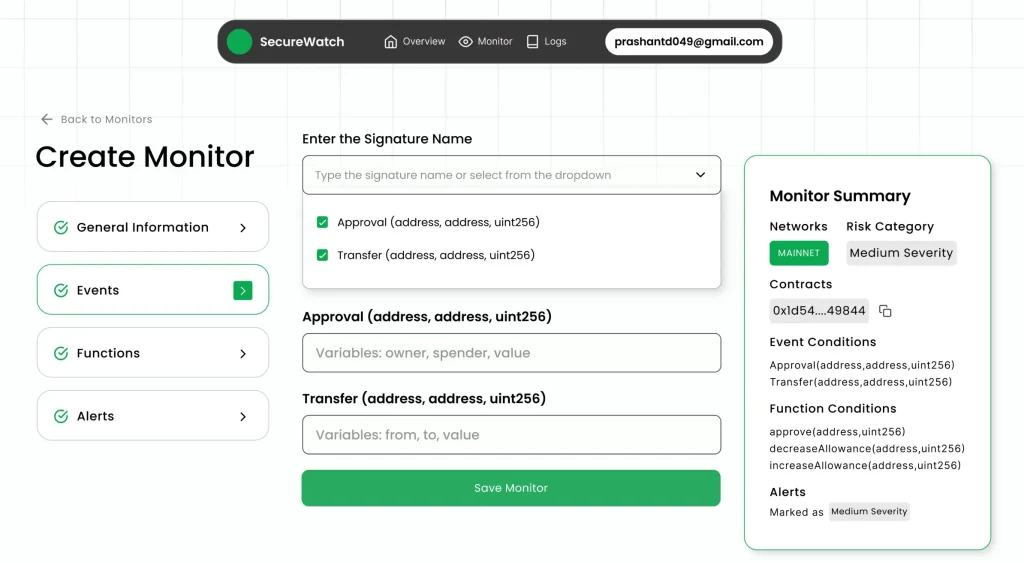
Customizable Security Policies
Enterprise protocols have varied security requirements. A DeFi lending protocol has different monitoring priorities than a cross-chain bridge or a staking pool. Effective monitoring platforms, therefore, let organizations define and tailor security policies – alert thresholds, monitored function sets, whitelisted address ranges, and escalation workflows – rather than applying generic logic that either generates noise or misses protocol-specific risks.
Platforms like SecureWatch operationalize this approach through continuous on-chain anomaly detection with customizable security policies, real-time alerting, and ongoing analysis refinement – providing post-deployment surveillance that complements the pre-deployment audit layer.
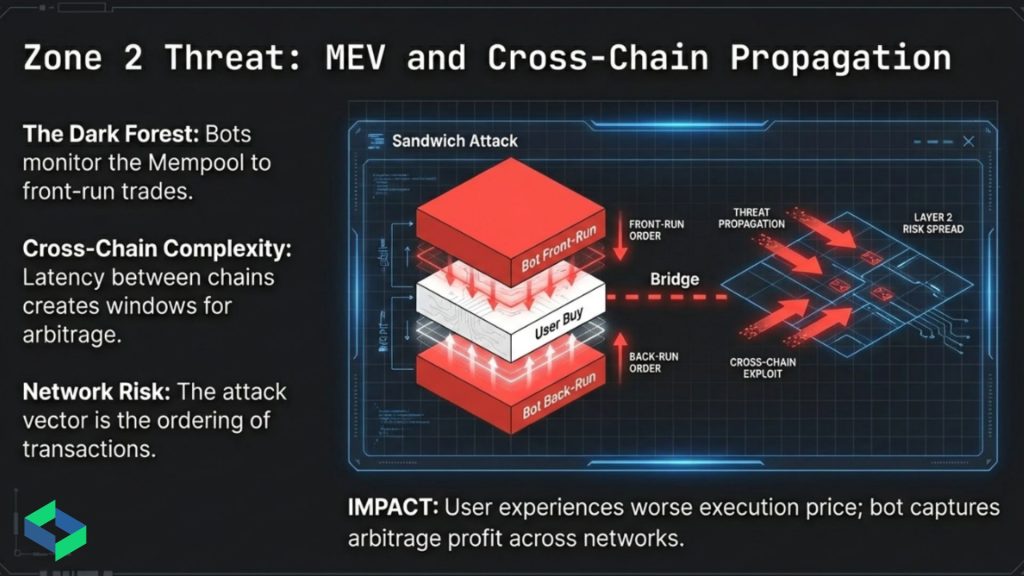
MEV and Cross-Chain Risk Propagation
Two threat categories deserve specific attention in 2026’s monitoring environment: MEV extraction and cross-chain risk propagation.
MEV extraction – the practice of miners, validators, or bots reordering, inserting, or blocking transactions to capture value – has evolved well beyond simple arbitrage. Today it includes sophisticated sandwich attack strategies targeting large AMM trades, lending protocol liquidations, and NFT mints. As a result, MEV-aware monitoring must track not just individual transactions but ordering patterns within blocks – identifying sequences where a profitable transaction is suspiciously positioned around a high-value target.
Cross-chain bridges, meanwhile, represent a highly concentrated risk surface. Because they aggregate assets from multiple chains into a single custody mechanism, they become attractive targets for large-scale attacks. Cross-chain risk propagation monitoring tracks asset flows across chains, flagging patterns where large quantities move rapidly between chains – especially toward chains with weaker monitoring coverage – as potential signals of an in-progress or imminent attack.
Part IV: Blockchain Forensic Investigation – The Post-Incident Layer
Forensic Methodology for On-Chain Incidents
When an exploit occurs, the forensic investigation has three goals: reconstruct the full attack sequence, trace the movement of extracted funds, and produce documentation fit for legal proceedings and regulatory reporting.
Blockchain’s permanence is a genuine forensic asset. Every transaction is recorded with a timestamp, caller address, contract address, function selector, value, and event emissions. The challenge, therefore, is not data availability – it is data volume and interpretive complexity. A skilled attacker operating across multiple wallets, protocols, and chains generates thousands of on-chain events. Making sense of that event stream requires automated transaction graph analysis, entity attribution, and pattern recognition at scale.
Transaction Thread Tracing
Auto-trace functionality maps transaction graphs from the origin address of a known exploit forward through all wallet interactions – identifying fund flows, intermediate hops, and eventual destination addresses. This process must account for common obfuscation tactics: chain-hopping via bridges, fragmenting large balances across dozens of wallets, using privacy protocols to break transaction linkage, and converting to privacy coins at CEX ramps.
Wallet Clustering and Entity Attribution
Individual attacker operations rarely use a single wallet. Instead, clustering algorithms identify wallets that share behavioral characteristics – common transaction patterns, timing correlations, shared gas funding sources, or similar interaction sequences – and group them into entity clusters. Attribution then maps those clusters to known entities where possible: exchange KYC data released under legal process, previously flagged attacker addresses, or blockchain intelligence databases.
Fraud Pattern Recognition
Machine learning models trained on historical exploit data identify structural patterns – address reuse strategies, fund fragmentation ratios, timing between exploit execution and fund movement – that link a new incident to known threat actor methods or reveal novel strategies for classification. This distinction between opportunistic attacks and coordinated campaigns has significant implications for legal response and regulatory reporting.
Legal Documentation and Regulatory Reporting
Investigation output that cannot be used in legal proceedings or submitted to regulators has limited practical value. Forensic platforms must therefore generate documentation that meets chain-of-custody standards, includes full transaction provenance, and is formatted for cross-jurisdictional regulatory submission. AML/KYC integration connects on-chain address data with regulated exchange identity data where legal authority for disclosure exists.
SecureTrace operationalizes this forensic model – using AI and ML techniques to perform transaction thread tracing, wallet clustering, fraud pattern detection, and investigation-grade report generation – turning raw blockchain data into legal-grade intelligence for incident response and compliance teams.
Case Study Pattern: Cross-Chain Bridge Exploit Reconstruction
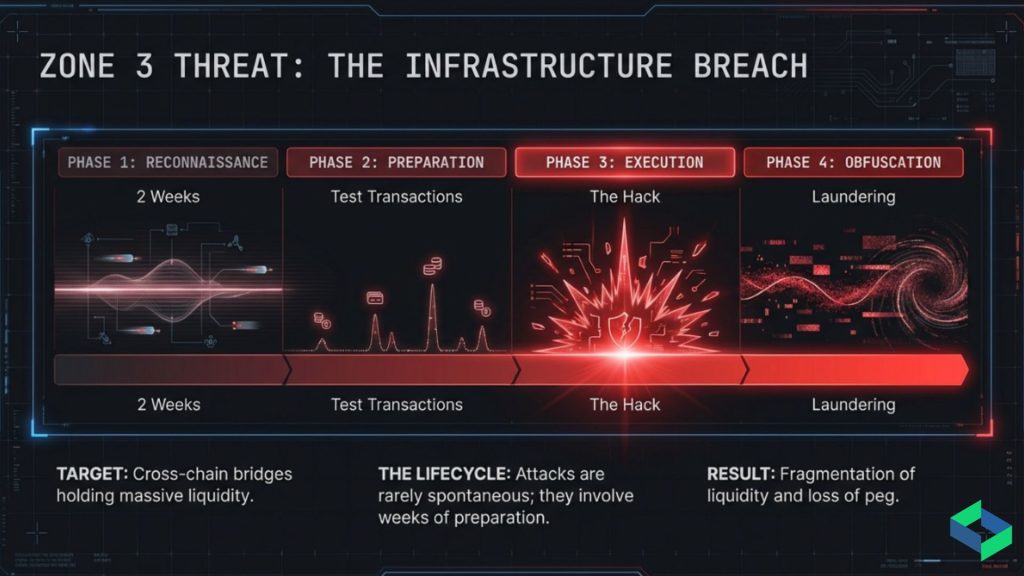
To illustrate forensic method in concrete terms, consider the structural pattern common to major bridge exploits in recent years.
Phase 1 – Reconnaissance (Days to Weeks Pre-Attack): Attacker wallets begin probing the bridge contract with small test transactions. These wallets are typically new or have thin transaction histories. Through these tests, the attacker establishes exact confirmation timing, fee structures, and contract state behavior under edge conditions.
Phase 2 – Preparation (Hours Pre-Attack): Capital consolidates across multiple wallets, often through flash loan positions or exchange withdrawals timed to stay below standard monitoring thresholds. Meanwhile, gas price bidding begins to secure transaction ordering priority at the moment of attack.
Phase 3 – Exploit Execution (Minutes): The core exploit sequence runs in a small number of carefully ordered transactions. Exploit mechanics vary – validator signature forgery, incorrect balance verification, reentrancy in withdrawal logic – but the execution window is always narrow by design.
Phase 4 – Obfuscation (Hours to Days Post-Attack): Extracted funds are immediately fragmented across dozens of wallets, bridged to alternative chains, and routed through mixers or privacy protocols. The attacker uses the gap between exploit discovery and exchange-level alerting to begin converting assets to fiat-accessible positions.
Forensic Detection Points: Effective post-incident investigation identifies the reconnaissance phase through historical mempool analysis, maps Phase 3 sequences from contract event logs, and traces Phase 4 fund movements through the full cross-chain graph using bridge transaction records. The completeness of this reconstruction ultimately determines the legal strength of any proceedings that follow.
Part V: Enterprise Identity Security – The Compliance and Authentication Layer
The Structural Problem with Centralized Identity in Blockchain Environments
Enterprise blockchain environments require identity – for users, institutions, contracts, and regulatory compliance. The dominant approach has traditionally been centralized: a database, an IAM system, a KYC data store controlled by a single entity.
This architecture creates compounding liabilities. Centralized PII stores are high-value breach targets. Compliance with GDPR, MiCA, and equivalent frameworks requires complex data governance infrastructure. Repetitive KYC processes across multiple blockchain participants create friction, cost, and duplicate data exposure. Cross-border operations also face conflicting data localization rules that centralized architecture cannot cleanly resolve.
The Case for Self-Sovereign Identity
The structural alternative is self-sovereign identity – a decentralized model where the subject controls their own identity data. Users disclose only what a specific interaction requires, without ever exposing the underlying PII to any relying party. This approach eliminates the data concentration problem at its source, rather than trying to protect concentrated data after the fact.
Zero Knowledge Proof Architecture in Enterprise Identity
The technical foundation of enterprise self-sovereign identity is zero-knowledge proof cryptography. A ZKP allows one party to prove to another that a statement is true – without revealing the information behind that statement.
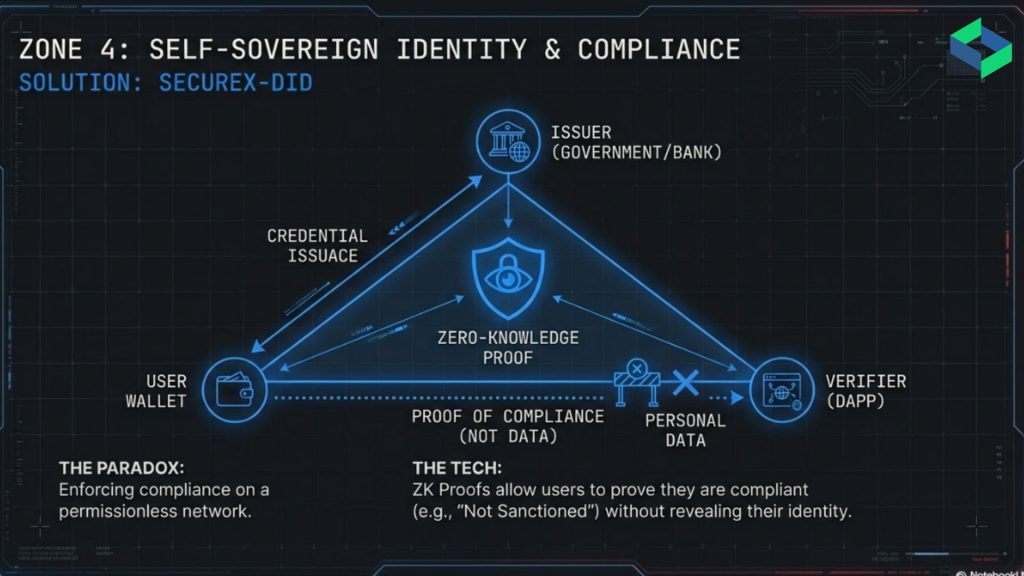
In practice, this means: a user can prove they are over 18 without revealing their date of birth. An institution can prove it holds a valid compliance certification without showing the full certification documentation. A wallet can prove it is not on a sanctions list without revealing the wallet address to the verification service.
How DIDs and Verifiable Credentials Work Together
W3C Decentralized Identifiers (DIDs) provide the addressing layer – a globally unique identifier anchored to a blockchain registry and controlled by the identity subject, with no dependency on a central authority. Verifiable Credentials (VCs), issued by trusted credential authorities and held in the subject’s identity wallet, represent the actual claims: education credentials, compliance certifications, KYC status, and professional licenses.
Merkle tree-based verification then enables selective disclosure. A VC containing multiple claims can have individual claims proven without exposing the full credential. For example, a supply chain operator can prove their environmental compliance claim without revealing the auditor’s embedded full report.
Enterprise Implementation Benefits
The compliance benefits of ZKP-based identity are concrete and immediate. GDPR’s data minimization principle – collect only what is necessary – is architecturally satisfied when the system makes it technically impossible to collect unnecessary data. Additionally, GDPR’s right to erasure is operationalized when PII is never transmitted to or stored by relying parties in the first place.
KYC reuse across ecosystem participants – exchanges, DeFi protocols, compliance services – reduces per-transaction identity verification costs while keeping regulatory compliance intact. Passwordless authentication, backed by cryptographic proof of wallet or credential possession, also eliminates the password-based attack surface entirely.
SecureX-DID implements this architecture using ZKP, W3C DID, Verifiable Credentials, and Merkle tree-based verification – enabling enterprise identity infrastructure that provides proof without exposure and satisfies regulatory requirements without creating the data concentrations that attackers target.
Part VI: The Enterprise Security Lifecycle – Bringing It Together
Full-Stack Web3 Security Architecture
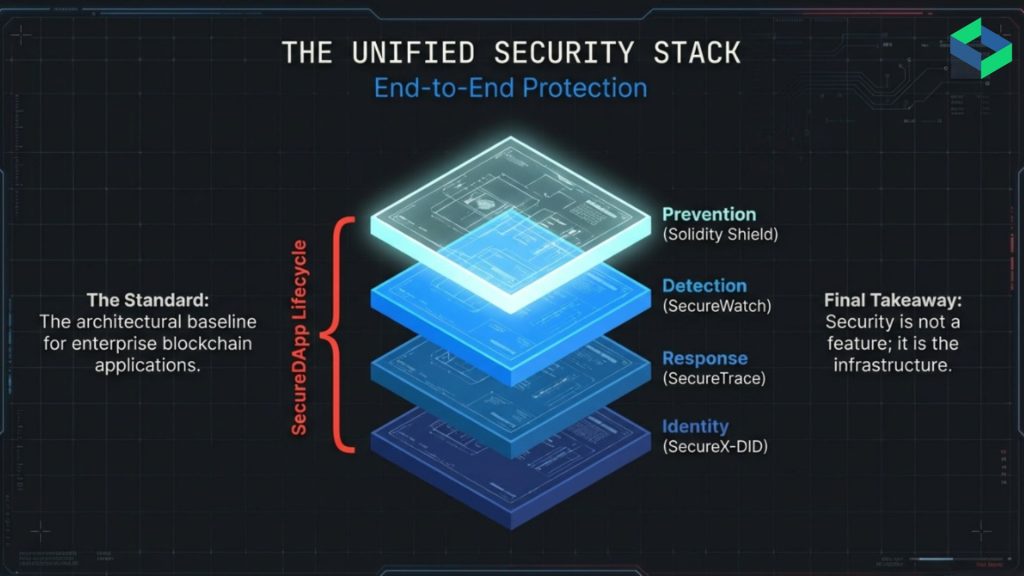
The four security zones described in this guide are not independent systems. Together, they form an integrated security lifecycle where the output of each layer actively strengthens the others.
Pre-deployment audit findings from Solidity Shield feed into SecureWatch’s monitoring policy configuration – known vulnerability patterns generate specific detection rules for post-deployment surveillance. SecureWatch alerting then triggers SecureTrace forensic investigation workflows when anomalies cross defined thresholds. In turn, SecureTrace investigation output informs the threat intelligence used to refine SecureWatch detection models. Finally, SecureX-DID identity verification integrates with both access control enforcement and compliance reporting workflows.
This integration closes the gaps between security layers that attackers systematically exploit. In fragmented security architectures, the space between audit completion and monitoring activation – or between incident detection and forensic initiation – is precisely where attacker dwell time accumulates. Integrated architectures eliminate those spaces.
| Security Stage | Product | Function |
|---|---|---|
| Pre-Deployment | Solidity Shield | AI-powered vulnerability detection, 150+ vulnerability classes, audit report generation |
| Post-Deployment | SecureWatch | Real-time on-chain monitoring, behavioral anomaly detection, and mitigation with customizable security policies |
| Incident Response | SecureTrace | Transaction thread tracing, wallet clustering, forensic report generation, legal documentation |
| Identity & Compliance | SecureX-DID | ZKP-based authentication, W3C DID framework, verifiable credentials, GDPR-aligned architecture |
Regulatory Alignment and Compliance Architecture
The regulatory environment for blockchain security has hardened considerably. The EU’s Markets in Crypto-Assets (MiCA) regulation, now fully in force, imposes licensing requirements, operational resilience standards, and incident reporting obligations on crypto-asset service providers in European markets. Similarly, the Financial Action Task Force’s Travel Rule – requiring CASPs to transmit originator and beneficiary data with virtual asset transfers – makes transaction monitoring infrastructure a compliance baseline, not an optional security enhancement.
US Regulatory Obligations
In the United States, FinCEN’s Virtual Asset Service Provider framework and SEC enforcement actions have confirmed that blockchain enterprises carry the same AML/BSA compliance obligations as traditional financial institutions. Furthermore, compliance failures can extend to personal liability for compliance officers in some jurisdictions – raising the stakes well beyond organizational penalties alone.
For enterprise organizations, this regulatory landscape makes security architecture inseparable from compliance architecture. Transaction monitoring is Travel Rule infrastructure. Forensic investigation capability is incident reporting infrastructure. Decentralized identity is GDPR compliance infrastructure. In short, the security stack described in this guide is simultaneously the compliance stack.
The Cost-Benefit Reality
The cost of building and maintaining this infrastructure is substantially lower than the combined cost of regulatory penalties, post-exploit remediation, and reputational damage from a major security failure. Risk modeling consistently shows that enterprise-grade blockchain security investment generates positive ROI within 24 months for organizations operating at meaningful scale.
Incident Response Workflow Design
Effective blockchain security architecture includes explicit incident response workflow design – not as a contingency document, but as an operational process with defined triggers, roles, and escalation paths.
Detection to Escalation: SecureWatch anomaly detection triggers graduated alerts based on severity classification.
- Level 1 anomalies (behavioral deviations below exploit probability threshold) generate monitoring queue entries.
- Level 2 anomalies (pattern combinations consistent with known attack precursors) trigger immediate analyst review.
- Level 3 anomalies (confirmed exploitation signatures or large unauthorized fund movements) activate incident response protocols automatically.
Investigation Initiation: SecureTrace forensic investigation initiates automatically on Level 3 triggers, beginning transaction graph reconstruction from the identified origin event. In parallel, workflows notify legal counsel, compliance teams, and exchange partners for Travel Rule–relevant asset tracing.
Communication and Reporting: Regulatory incident reporting timelines are jurisdiction-specific – MiCA mandates reporting within defined windows. Therefore, forensic investigation output must be formatted for multi-jurisdictional submission from the start of the investigation, not adapted for regulatory purposes after internal analysis is complete.
Asset Recovery Coordination: Exchange partner coordination for address blocking and asset freezing depends on the speed and completeness of the forensic trace. Every hour of delay reduces recovery probability as funds move further through obfuscation networks. Automated investigation initiation is consequently the single highest-impact intervention for improving asset recovery outcomes.
Part VII: The Forward-Looking Security Architecture
Where Blockchain Security Is Heading
Several converging developments will reshape blockchain security requirements over the next 24–36 months. Understanding them now is essential for organizations building infrastructure that will still be defensible when these shifts arrive.
Cross-Chain Attack Surface Expansion
The growth of layer 2 rollups, app-specific chains, and cross-chain interoperability protocols has significantly expanded the attack surface available to threat actors. Attacks that begin on one chain and extract value on another – exploiting the security gap between chains – are now the dominant pattern in large-scale exploits. As a result, security architecture must evolve to treat the multi-chain environment as a single threat surface, with monitoring, forensic, and identity infrastructure that operates natively across chains.
AI-Augmented Attack Methodology
The same AI capabilities that improve defensive tooling are equally available to attackers. Automated vulnerability scanning of deployed contracts, AI-generated attack transaction sequences, and machine learning-optimized obfuscation routing all represent the next evolution in attacker capability. Consequently, defensive AI systems must maintain capability parity – detecting AI-generated attack patterns requires detection models trained on adversarial examples, not just historical human-authored exploits.
Regulatory Convergence Toward Security Mandates
Regulatory frameworks across major jurisdictions are converging toward mandatory security infrastructure requirements for blockchain enterprises. Based on the trajectory of MiCA, FATF Travel Rule implementation, and US VASP frameworks, enterprise-grade monitoring, forensic, and identity infrastructure is likely to become a regulatory prerequisite for operating in most developed markets within 36 months – rather than a competitive differentiator.
Zero-Knowledge Proof Infrastructure Maturity
ZKP cryptography is moving steadily from academic research into production infrastructure. Proof generation performance has improved dramatically through hardware acceleration and algorithmic advances. Enterprise identity systems, compliance reporting, and privacy-preserving analytics built on ZKP foundations are entering production at scale. This maturation will unlock new classes of compliance-preserving blockchain interactions that are currently impractical due to computation cost.
On-Chain AI Agent Security
Autonomous AI agents operating on-chain – executing trades, managing protocol parameters, interacting with governance systems – represent a fast-emerging security challenge. Their behavior is difficult to audit with standard smart contract analysis tools. Monitoring frameworks must therefore evolve to classify and assess autonomous agent behavior against defined safety policies, with automated intervention mechanisms for anomalous agent actions.
Conclusion: Security as Infrastructure, Not Insurance
The blockchain security landscape of 2026 does not reward reactive posture. Attackers operate with greater sophistication, more capital, and more patience than the ad-hoc approaches that characterized early blockchain deployments. Organizations that operate securely in this environment are those that treat security as continuous operational infrastructure – not as an audit-and-forget compliance checkbox.
The four-layer architecture described in this guide – preventive contract security, post-deployment monitoring, forensic investigation, and decentralized identity – represents the current standard for enterprise blockchain security. Each layer addresses a distinct threat surface, and together they close the coverage gaps that sophisticated attackers exploit.
SecureDApp’s integrated stack – Solidity Shield, SecureWatch, SecureTrace, and SecureX-DID – implements this architecture as a unified platform. Rather than forcing enterprises to integrate multiple point solutions with mismatched data models, it provides coverage across the full Web3 security lifecycle in one coherent system.
The trajectory of regulation, attacker sophistication, and ecosystem complexity all point in the same direction: organizations that build comprehensive security infrastructure now will operate from a defensible position as those pressures increase. Those that delay will face the compounding combination of greater attack exposure and heavier regulatory consequence.
This guide is a reference framework, not a complete implementation specification. Specific architectural decisions – monitoring policy design, forensic workflow integration, identity system deployment – require assessment against each organization’s protocol architecture, regulatory jurisdiction, and operational context. The depth of that assessment is where real security is built.
FAQ: Blockchain Security in 2026
Currently, access control misconfiguration and logic flaws cause most production losses. While reentrancy was once dominant, automated audits now detect it more consistently. Therefore, permission design and business logic validation are the primary risk areas.
Traditional monitoring relies on logs and network data, which can be altered or withheld. In contrast, on-chain monitoring operates on immutable transaction records. Consequently, the challenge shifts from data integrity to rapid signal detection.
The FATF Travel Rule requires VASPs to collect and transmit sender and beneficiary data. As enforcement increases, compliance infrastructure becomes mandatory. Therefore, enterprises need integrated monitoring and secure data-sharing systems.
Self-sovereign identity removes centralized storage of sensitive PII. Instead, users prove compliance attributes through cryptographic credentials. As a result, organizations reduce breach exposure and meet data minimization standards.
Recovery success depends primarily on how quickly investigation begins. Early forensic action limits fund obfuscation across chains and exchanges. Therefore, automated monitoring-to-investigation workflows significantly improve outcomes.


