Introduction
In 2024, over $2.3 billion was lost to smart contract exploits across DeFi and Web3 protocols. Most of these attacks did not happen in hours. They happened in seconds. Sometimes in a single transaction.
This is the brutal reality of on-chain security. Once a malicious transaction is confirmed, it is irreversible. You cannot call your bank. There is no dispute process. The funds are simply gone.
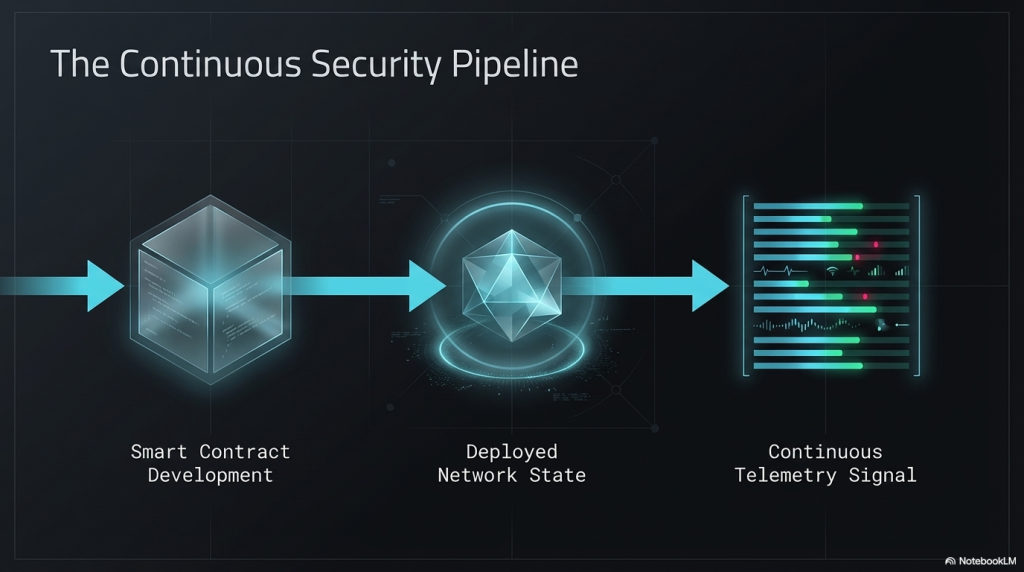
This is precisely why real-time blockchain threat monitoring has become the most critical layer in a Web3 security stack. Static audits and manual code reviews are valuable, but they are insufficient alone. You need eyes on-chain, watching every transaction, every state change, every anomalous call pattern.
This blog explores the technical mechanics of smart contract exploit detection in real time. We cover how on-chain detection systems work, what attack patterns they monitor, how mempool surveillance functions, and what tooling and practices teams must adopt to stay ahead of adversaries.
Why Static Audits Are Not Enough
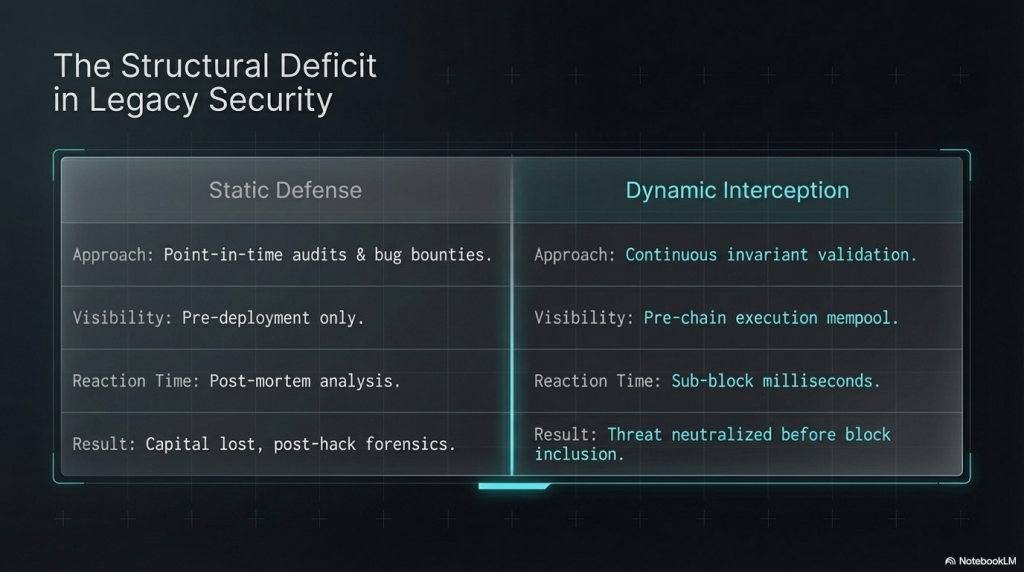
Most Web3 teams run a smart contract audit before deploying. That is a good baseline. But audits have hard limitations.
An audit captures code at a point in time. It checks logic, access controls, and common vulnerability patterns. What it cannot do is watch how the contract behaves once it is live, integrated with other protocols, and exposed to adversarial actors who probe for weaknesses 24/7.
Many exploits have happened on audited contracts. The Reentrancy attack on Euler Finance in 2023 hit a protocol that had been audited multiple times. The Nomad bridge hack in 2022 drained $190 million from a codebase that security firms had reviewed.
Audits answer one question: “Does this code look safe today?” Real-time monitoring answers a different question: “Is this contract being exploited right now?”
Both questions matter. Only one can save funds in the moment.
Understanding the Exploit Lifecycle On-Chain
To build effective detection, you must first understand how exploits unfold. Most attacks follow a recognisable lifecycle.
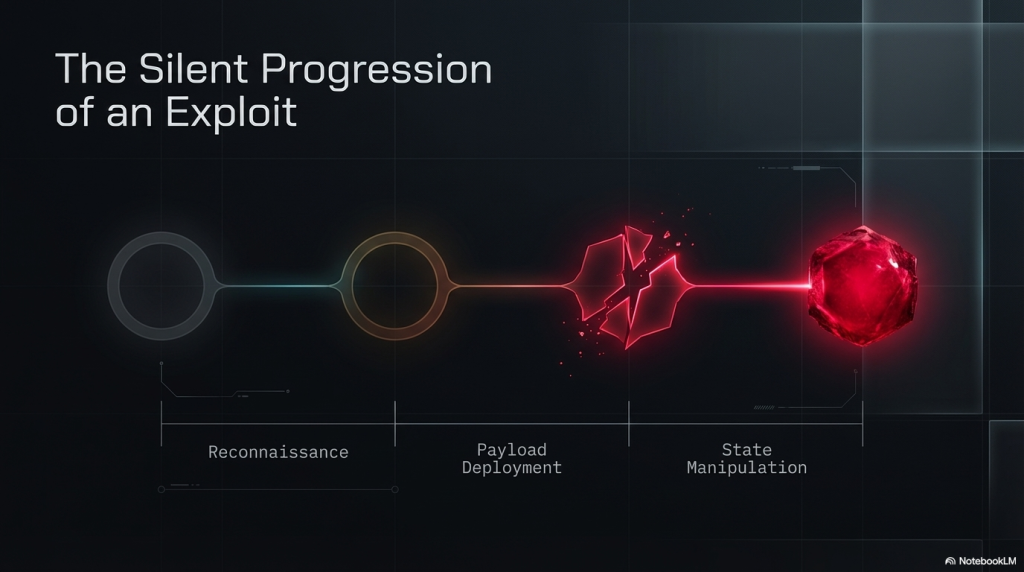
Phase 1: Reconnaissance and Probing
Attackers typically send small-value test transactions before the main attack. These probe the protocol’s state, check reentrancy guards, test oracle price deviation limits, or verify flash loan availability.
These probes look innocuous in isolation. In sequence, they form a clear signal.
Phase 2: Setup Transactions
Many exploits require setup. An attacker might take a large flash loan, build a malicious contract, or accumulate tokens to manipulate price oracles. These setup steps happen before the exploit transaction and are visible on-chain.
Phase 3: The Exploit Transaction
This is usually a single complex transaction. It may bundle multiple contract calls, use flash loans, execute reentrancy, or manipulate oracles in the same atomic operation.
Phase 4: Profit Extraction
After the exploit, funds are moved quickly. Typically within the same block or within a few blocks, tokens are swapped, bridged to another chain, or deposited into a mixing protocol.
Understanding this lifecycle means detection systems can fire alerts at Phase 1 or Phase 2, well before funds are drained.
Core Techniques in Real-Time Blockchain Threat Monitoring
Let us now get into the actual technical methods that power modern on-chain exploit detection.
1. Transaction Simulation Before Confirmation
One of the most powerful techniques is simulating pending transactions before they are confirmed. This operates at the mempool level.
The Ethereum mempool holds transactions that have been broadcast but not yet included in a block. A well-architected monitoring system can pull these pending transactions, simulate their execution against the current chain state, and determine whether they would trigger an anomalous outcome.
For example, a transaction that would cause an ERC-20 balance to drop to zero across multiple user accounts is a strong exploit signal. Simulation allows you to see the outcome before it happens.
Tools like Tenderly’s simulation API, Alchemy’s Simulate API, and Foundry’s cast simulate command enable this. More advanced systems build custom EVM forks in memory to run high-speed simulations at scale.
This is real-time blockchain threat monitoring at its most proactive.
2. Event and Log Monitoring
Every meaningful on-chain action emits an event log. A Transfer event fires when tokens move. A Borrow event fires when a lending protocol is used. A Swap event fires on a DEX.
Exploit detection systems subscribe to these event streams in real time. They look for patterns such as abnormally large single transfers, repeated recursive calls within a transaction, unexpected ownership changes, or token drains across multiple users in sequence.
Setting thresholds on event parameters, like flagging any single withdrawal exceeding 15% of a protocol’s total value locked (TVL), is a common starting point.
The sophistication comes in correlating multiple events across a transaction trace to identify attack patterns versus normal large transactions.
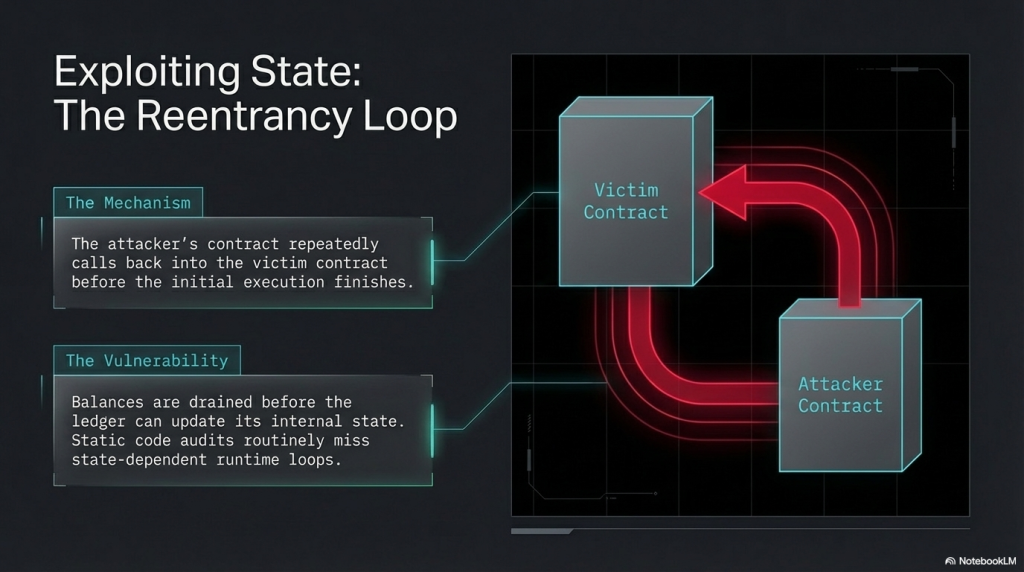
3. Trace Analysis and Call Graph Inspection
A simple transaction contains a “call trace”, which is the complete tree of function calls made during execution. For a standard token transfer, this trace is shallow. For a flash loan attack, the trace can be hundreds of calls deep.
Monitoring systems that analyse call traces can detect:
- Reentrant call patterns (Contract A calls Contract B which calls back into Contract A)
- Delegatecall abuse (using another contract’s logic in the current context)
- Unexpected proxy upgrades (admin functions called under non-standard conditions)
- Oracle manipulation sequences (price read followed by large trade followed by price read)
Call graph analysis is CPU intensive but extremely accurate. Most production exploit detection systems combine lightweight event monitoring for speed with deep trace analysis for precision.
4. Invariant Monitoring
Every well-designed protocol has mathematical invariants: conditions that must always hold true. For a DEX using the constant product formula, the product of reserve balances must remain constant after every swap (excluding fees).
Invariant monitoring continuously checks whether protocol-level conditions remain intact after each transaction. A violation is an immediate exploit signal.
This technique is especially powerful for AMM protocols, lending markets, and stablecoin mechanisms. For example, if the collateralisation ratio on a lending protocol drops below the minimum required in a single transaction, that is either an exploit or a severe configuration error — both require immediate investigation.
At SecureDApp, our audit processes help teams identify and formalise their protocol invariants before deployment. These formalised invariants then become the basis for post-deployment monitoring rules.
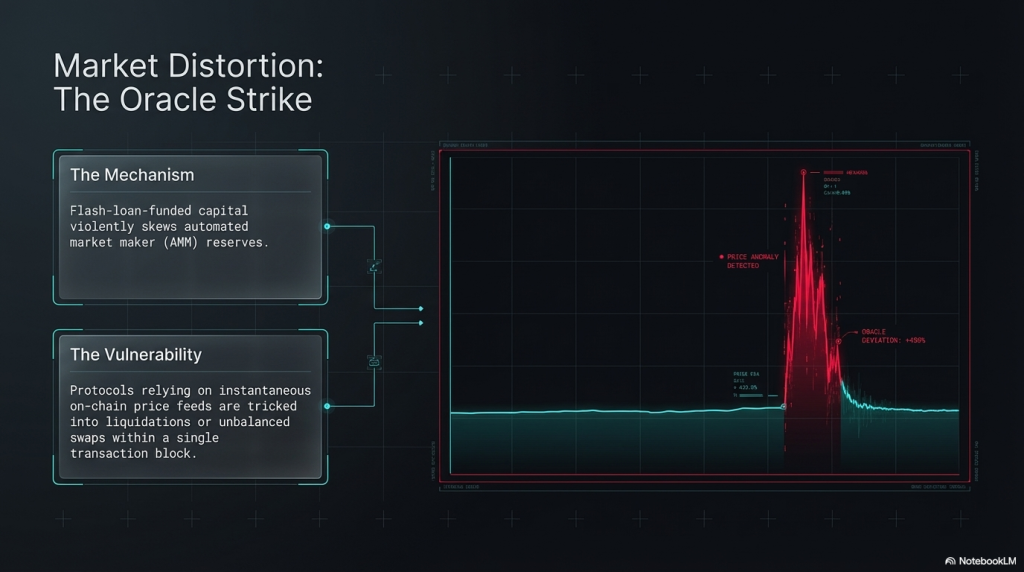
5. Price Oracle Deviation Detection
Oracle manipulation is responsible for a significant portion of DeFi exploits. An attacker manipulates the price reported by an on-chain oracle, uses the manipulated price to borrow against inflated collateral, and exits before the oracle corrects.
Real-time oracle monitoring involves watching price feeds from Chainlink, Uniswap TWAPs, Pyth, and other sources simultaneously. When a spot price deviates significantly from a time-weighted average over a short window, this is a strong manipulation signal.
Effective detection systems track price deviations in percentage terms, flag deviations exceeding a configurable threshold (often 5-10% in under 30 seconds), and cross-reference this with large borrow or withdrawal transactions in the same block.
6. MEV and Sandwich Attack Detection
Maximal Extractable Value (MEV) bots operate in the mempool, reordering transactions to extract profit. Sandwich attacks — where a bot places transactions before and after a victim’s trade represent a form of economic attack against users.
While not always a “hack” in the traditional sense, MEV-based attacks can drain significant value from protocols and users. Detection involves monitoring the transaction ordering within blocks, identifying front-running patterns, and flagging searcher bots that consistently appear before large trades.
Mempool Surveillance: Catching Exploits Before Confirmation
The mempool is where transactions wait. It is also where many attacks are visible before they execute.
How Mempool Monitoring Works
A node subscribed to the peer-to-peer gossip network receives pending transactions as they propagate. A dedicated mempool monitoring service processes these at high throughput, typically thousands of transactions per second on mainnet.
For each pending transaction, the system can:
- Decode the calldata to identify which function is being called
- Check whether the calling address has a prior history of exploit activity
- Simulate the transaction outcome, as described earlier
- Compare the transaction parameters against known attack signatures
If any of these checks raise a flag, an alert fires in real time. Depending on integration, this alert can trigger an automated circuit breaker.
Circuit Breakers and Automated Pause Mechanisms
The most actionable form of real-time monitoring includes automated response. If a monitoring system detects a likely exploit in the mempool, it can trigger a pause transaction in the same block or earlier (using higher gas), halting the affected contract before the attack confirms.
This is called a “defender” pattern or “guardian” architecture. It requires the protocol to have a pause mechanism built in, with a trusted guardian contract or EOA authorised to trigger it.
SecureDApp’s smart contract security assessments specifically check for the presence and correctness of pause mechanisms, ensuring they are not themselves attack surfaces.
Limitations of Mempool Monitoring
Not all attacks are visible in the public mempool. Private relay networks like Flashbots allow transactions to be submitted directly to validators, bypassing the public mempool entirely. These “dark” transactions cannot be intercepted in advance.
This is why full-stack monitoring also includes post-inclusion analysis, reviewing every confirmed transaction for exploit indicators, even if no warning came from the mempool.
On-Chain Forensics: Detecting Exploits in Confirmed Blocks
Even when mempool surveillance is in place, attacks can slip through via private relays or be too fast to intercept. Post-confirmation monitoring is therefore equally critical.
Block-by-Block Transaction Analysis
A production monitoring system processes every confirmed block in near real time, typically within 1-3 seconds of confirmation on Ethereum mainnet.
For each transaction in the block, the system runs detection logic:
- Is the sender a known attacker address or flagged contract?
- Does the transaction touch a flagged protocol or token contract?
- Are the resulting state changes consistent with expected protocol behaviour?
- Does the transaction emit anomalous event combinations?
Heuristic-Based Exploit Signatures
Over years of analysing DeFi exploits, security researchers have built libraries of heuristic signatures. These are patterns in transaction structure, calldata, or event sequences that reliably indicate specific attack types.
Examples include:
- The “reentrancy signature”: a function call sequence where the same function appears at multiple depth levels in the call trace
- The “flash loan drain signature”: a flash loan repayment in the same transaction as a large token outflow from a protocol
- The “delegatecall upgrade signature”: a proxy contract changing its implementation address followed by a large asset transfer
SecureDApp’s security team continuously updates internal exploit signature libraries based on post-mortems of real-world attacks. These signatures power both our audit checklist and our monitoring recommendations.
Machine Learning for Anomaly Detection
Beyond rule-based heuristics, advanced monitoring systems apply ML models trained on labelled exploit and non-exploit transaction data.
Graph neural networks are particularly well-suited here. On-chain activity forms a graph: addresses are nodes, and transactions are edges. Exploit patterns often form distinctive subgraph structures. For example, a flash loan from Protocol A to attacker Contract B to victim Protocol C and back forms a triangular structure rarely seen in normal activity.
ML models can surface these structural anomalies even when specific exploit signatures do not match, catching novel attack variants.
Tools and Infrastructure for Real-Time Monitoring

Let us review the key tooling teams use to implement these detection methods.
Ethereum Node Infrastructure
Reliable real-time monitoring starts with low-latency node access. Running a full node (Erigon, Geth, or Nethermind) or using a dedicated node service like Alchemy, Infura, or QuickNode with WebSocket subscriptions is essential.
WebSocket subscriptions to newPendingTransactions and newHeads events feed the raw data pipeline.
OpenZeppelin Defender
Defender provides an end-to-end security operations platform. It includes Sentinels for event monitoring, Autotasks for automated responses, and integration with popular alert channels like PagerDuty and Telegram.
For teams that want monitoring without building infrastructure from scratch, Defender is a strong starting point.
Forta Network
Forta is a decentralised monitoring network. Independent “detection bots” run across the network, each watching for specific attack patterns. Teams can deploy custom bots or subscribe to community bots covering known exploit types.
Forta’s decentralised architecture means monitoring is not a single point of failure, which is important for critical DeFi infrastructure.
Tenderly Alerts and Simulations
Tenderly provides visual transaction debugging, simulation APIs, and a real-time alerting system. Teams can set conditions on transaction parameters and receive webhook notifications when conditions are met.
The simulation API is particularly valuable for pre-confirmation analysis within custom monitoring pipelines.
Custom Node-Level Monitoring
For high-value protocols, teams often build custom monitoring infrastructure directly at the node level. This involves running a modified node client that hooks into the transaction processing pipeline and runs detection logic synchronously.
This approach offers the lowest latency detection can happen within milliseconds of a transaction entering the mempool but requires significant engineering investment.
Integrating SecureDApp’s Security Services with Real-Time Monitoring

Real-time monitoring is most effective when it is built on a foundation of thorough security analysis. This is where SecureDApp’s services become directly relevant.
Smart Contract Auditing as the Baseline
Before deploying monitoring, teams need a clear understanding of their contract’s intended behaviour. This is precisely what a comprehensive security audit delivers.
SecureDApp’s audit process involves deep manual review of Solidity or Vyper code, automated static analysis, economic attack modelling, and formal specification of protocol invariants. The audit output includes a detailed list of all functions, expected behaviour, and risk classifications.
This audit output directly informs monitoring configuration. You cannot write a useful invariant monitoring rule without first knowing what the invariant is. You cannot configure meaningful event thresholds without understanding the protocol’s normal transaction profile.
Visit securedapp.io to learn about our smart contract audit offerings.
SecureWatch: Continuous Post-Deployment Monitoring
After an audit and deployment, protocols need ongoing vigilance. This is why SecureDApp offers SecureWatch, a continuous monitoring service tailored for DeFi and Web3 protocols.
SecureWatch combines:
- Real-time transaction monitoring for audited contracts
- Automated anomaly detection based on protocol-specific baselines
- Instant alerts via Telegram, Slack, PagerDuty, or email
- On-call incident response support
- Regular security reports and threat intelligence updates
SecureWatch is specifically designed for protocols that want comprehensive real-time blockchain threat monitoring without building an entire security operations centre in-house.
Penetration Testing to Sharpen Detection Rules
SecureDApp’s Web3 penetration testing service simulates real attacker behaviour against your deployed contracts in a test environment. The output identifies which attacks your monitoring systems would and would not catch.
This gap analysis is invaluable for tuning detection sensitivity and eliminating false positives.
Building Your Own Monitoring Stack: A Technical Blueprint
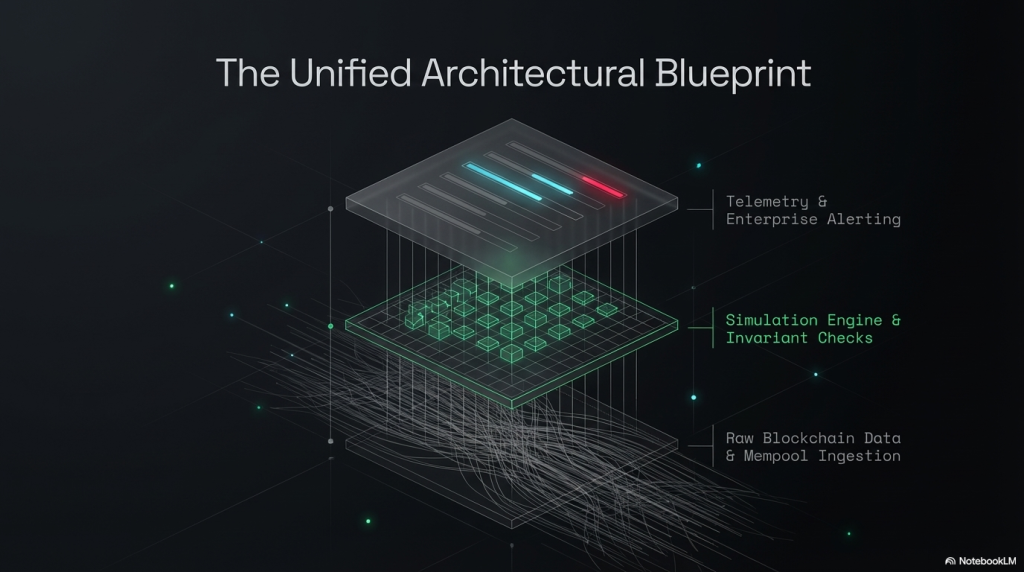
For teams building in-house monitoring capabilities, here is a practical architecture blueprint.
Data Ingestion Layer
Subscribe to your node via WebSocket. Use eth_subscribe with newPendingTransactions for mempool data and newHeads for confirmed block headers. Use eth_getBlockByHash with full transaction data for block-level processing.
Consider running multiple nodes in different geographies to minimise latency and maximise mempool coverage.
Processing Layer
Build a message queue (Kafka or RabbitMQ works well) between raw data ingestion and detection logic. This decouples ingestion speed from processing complexity and allows horizontal scaling.
Each transaction enters the queue and flows through a series of detection modules: decoder, simulator, heuristic matcher, invariant checker, and ML anomaly scorer.
Alert Layer
Detection outputs feed into an alert aggregation system. PagerDuty, OpsGenie, or a custom webhook handler works here. Include all relevant transaction data in the alert payload: block number, transaction hash, flagged contract, detection rule triggered, and simulated outcome.
Every alert should be actionable. Include a direct link to a transaction explorer like Etherscan or Tenderly for one-click investigation.
Response Layer
For protocols with pause mechanisms, build an automated responder that can trigger a pause when detection confidence exceeds a defined threshold. Use multi-sig controls on the pause key to prevent false-positive shutdowns from causing unnecessary disruption.
Document runbooks for human responders. When an alert fires at 3am, the on-call engineer needs to know exactly what to do without having to think from scratch.
Common Pitfalls in On-Chain Monitoring
Even well-resourced teams make mistakes when building monitoring systems. Here are the most common ones to avoid.
High false positive rates are the first problem. If every routine large transaction triggers an alert, teams develop alert fatigue and start ignoring notifications. Detection rules must be calibrated against the protocol’s actual transaction history to establish accurate baselines.
Monitoring only the primary contract is another frequent error. Modern DeFi protocols interact with many external contracts. Oracle contracts, liquidity pool contracts, and bridge contracts are all part of the attack surface. Monitoring must cover the full dependency graph.
Neglecting private relay transactions is a blind spot many teams do not account for. Supplement mempool monitoring with post-confirmation analysis to close this gap.
Finally, not having an incident response plan renders monitoring pointless. An alert that does not lead to a defined action sequence does not save funds. Pair every detection capability with a clear response protocol.
The Road Ahead: AI-Powered On-Chain Security
The frontier of smart contract exploit detection is moving toward AI-native architectures. Large language models are being applied to transaction calldata decoding, making it easier to identify novel attack patterns without hand-coded signatures.
Graph neural networks are getting better at modelling the complex interdependencies of DeFi protocols. Reinforcement learning is being explored for adversarial simulation, training agents to find novel exploit paths in protocol models.
At SecureDApp, we are actively researching how AI can enhance both our audit methodologies and our real-time monitoring capabilities. The goal is to shrink the window between an exploit attempt and detection to as close to zero as possible.
Real-time blockchain threat monitoring is not a feature. It is a fundamental requirement for any protocol that holds user funds. The stakes are too high for anything less.
Conclusion
Smart contract exploit detection has evolved well beyond static code review. Today, a layered defence combines pre-deployment auditing, mempool surveillance, post-confirmation block analysis, invariant monitoring, oracle deviation detection, and automated response mechanisms. The key takeaway is that real-time blockchain threat monitoring must be continuous, protocol-specific, and deeply integrated with incident response capabilities. Every minute between exploit and detection is money drained from users.
SecureDApp’s combination of deep audit expertise and the SecureWatch monitoring platform gives Web3 protocols a single trusted partner for the full security lifecycle, from code review through to live threat detection. If your protocol is live without continuous monitoring, now is the time to fix that.
Explore SecureDApp’s smart contract security services at securedapp.io.
Frequently Asked Questions
Real-time blockchain threat monitoring refers to continuously watching on-chain transactions, state changes, and event logs to detect exploit activity as it happens. It matters because smart contract exploits are irreversible. Once a malicious transaction confirms, funds cannot be recovered. Monitoring can catch attacks during the mempool phase or within seconds of confirmation, enabling emergency response before total loss.
Not all. Attacks submitted through private relay networks like Flashbots bypass the public mempool and cannot be intercepted in advance. However, a layered monitoring stack that combines mempool surveillance with post-confirmation analysis can detect these attacks within one to two blocks of execution, minimising loss if automated circuit breakers are in place.
Invariant monitors track mathematical conditions that must always hold true in a protocol. For example, the total collateral must always exceed total debt in a lending protocol. After every transaction, the monitor checks whether these conditions still hold. A violation is either an exploit or a severe configuration error both trigger an immediate alert.
SecureWatch is SecureDApp’s continuous post-deployment monitoring service. It combines protocol-specific event monitoring, anomaly detection based on established transaction baselines, and instant multi-channel alerting. It is configured using outputs from SecureDApp’s audit process, ensuring monitoring rules align precisely with the protocol’s intended behaviour.
The first step is to trigger the protocol’s pause mechanism if one exists, stopping further exploitation. Simultaneously, the incident response team should review the flagged transaction on a block explorer, confirm the exploit, and notify stakeholders. The protocol should remain paused while a post-mortem analysis determines the root cause. Public disclosure should follow established responsible disclosure practices to maintain community trust.



