DeFi moved over $100 billion in value last year. And fraudsters followed every rupee, every dollar of it. The blockchain is transparent. Everything is recorded. Yet somehow, exploits still happen within seconds. Flash loans drain liquidity pools. Rug pulls leave investors with worthless tokens. Phishing attacks steal wallet access quietly. The question is not whether DeFi has fraud problems. The question is why do projects keep getting caught off guard?
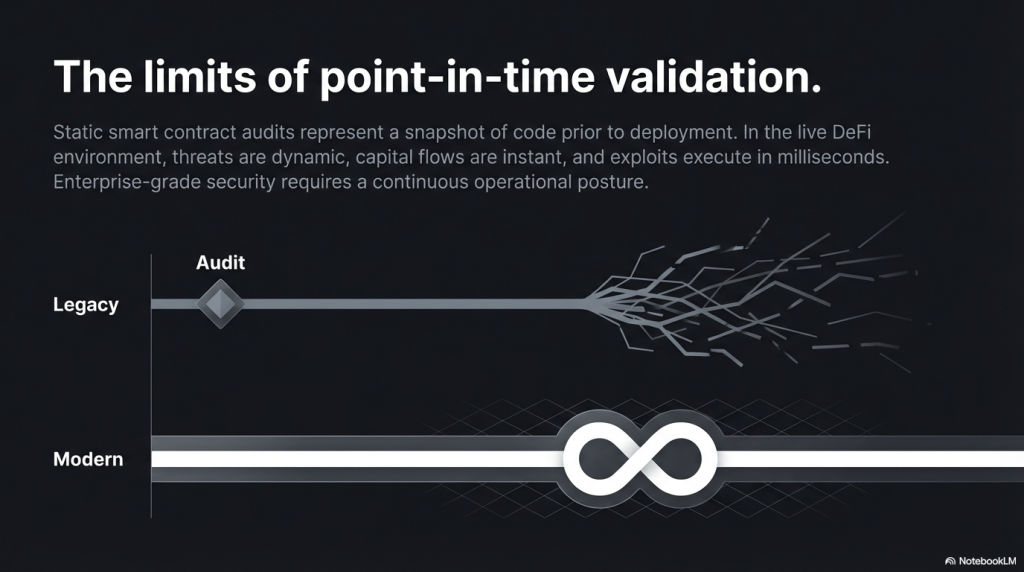
The answer lies in timing. Most DeFi projects react to fraud after it has already happened. The transaction is confirmed. The funds are gone. The postmortem report comes out three days later. Real-time blockchain threat monitoring changes this completely. It shifts the response from reactive to proactive. It watches every transaction as it enters the mempool. It flags anomalies before they become catastrophes. It gives DeFi protocols a fighting chance. This blog breaks down exactly how on-chain data can be used for fraud prevention in DeFi. No fluff. No jargon overload. Just what you actually need to understand.
Why DeFi Fraud Is Different From Traditional Finance Fraud
Traditional fraud detection relies on intermediaries. Banks flag suspicious transactions. Payment gateways hold funds for review. Chargebacks exist as a safety net. DeFi has none of these safety nets by design. Transactions are irreversible. Smart contracts execute automatically. There is no customer service number to call.
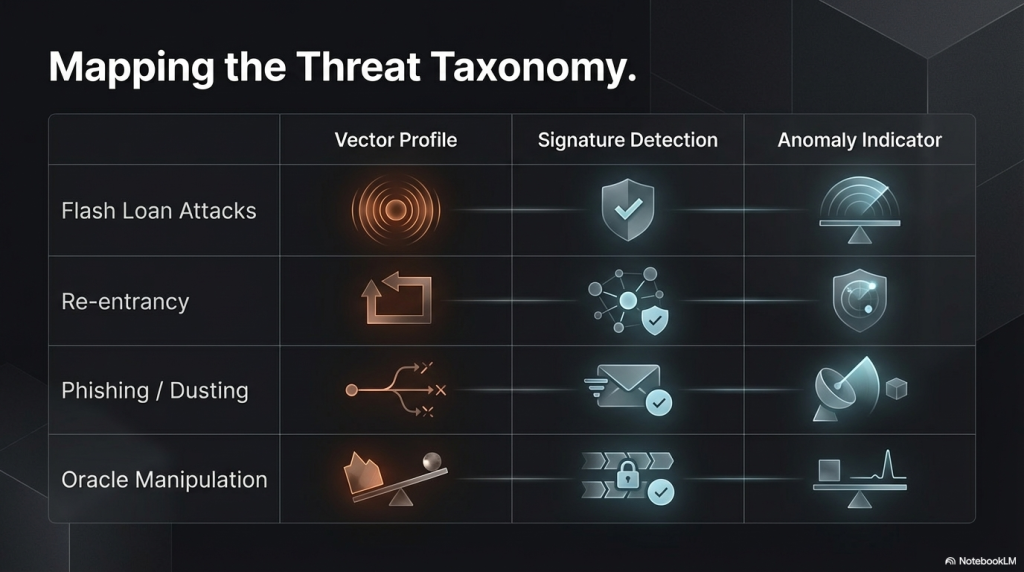
This is both DeFi’s strength and its greatest vulnerability. Some of the most common DeFi frauds include:
Flash Loan Attacks: Attackers borrow millions, manipulate prices, and repay within one block. The whole operation is done in under 13 seconds on Ethereum.
Rug Pulls: Developers abandon projects after raising funds. Liquidity is removed. Token price crashes to zero.
Price Oracle Manipulation: Attackers skew price feeds to borrow more than the collateral is worth.
Sandwich Attacks: Bots detect pending transactions and insert trades before and after to profit at the user’s expense.
Re-entrancy Exploits: Malicious contracts repeatedly call a function before previous execution finishes.
Each of these attacks leaves traces on-chain. The problem is that most projects do not watch for those traces in real time.
What Is Real-Time Blockchain Threat Monitoring?
Real-time blockchain threat monitoring is the continuous surveillance of on-chain activity. It watches transactions as they happen. It analyses patterns. It triggers alerts when something looks wrong. Think of it like a CCTV system for your smart contracts. Except instead of recording footage for later review, it raises an alarm the moment suspicious movement is detected.
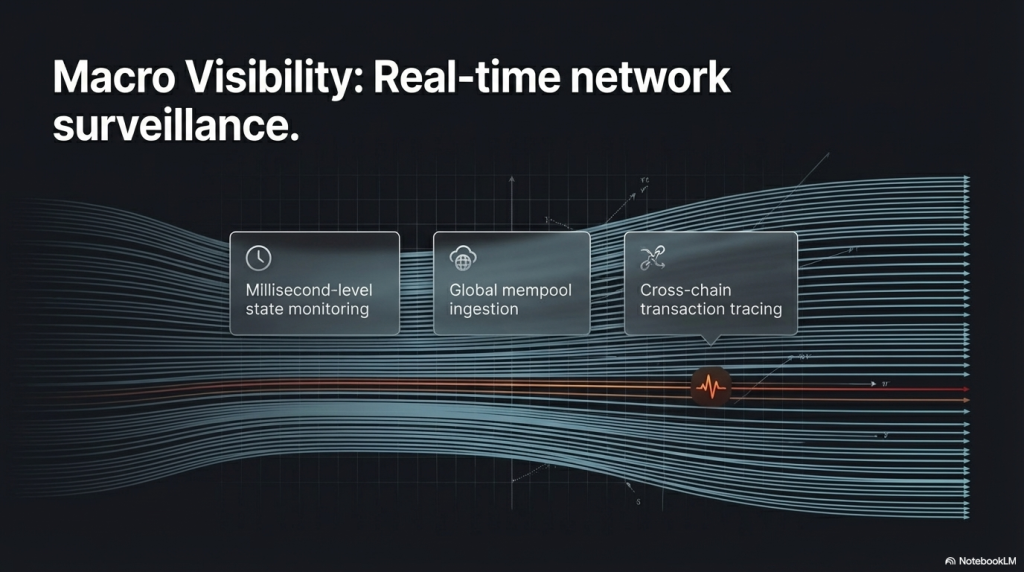
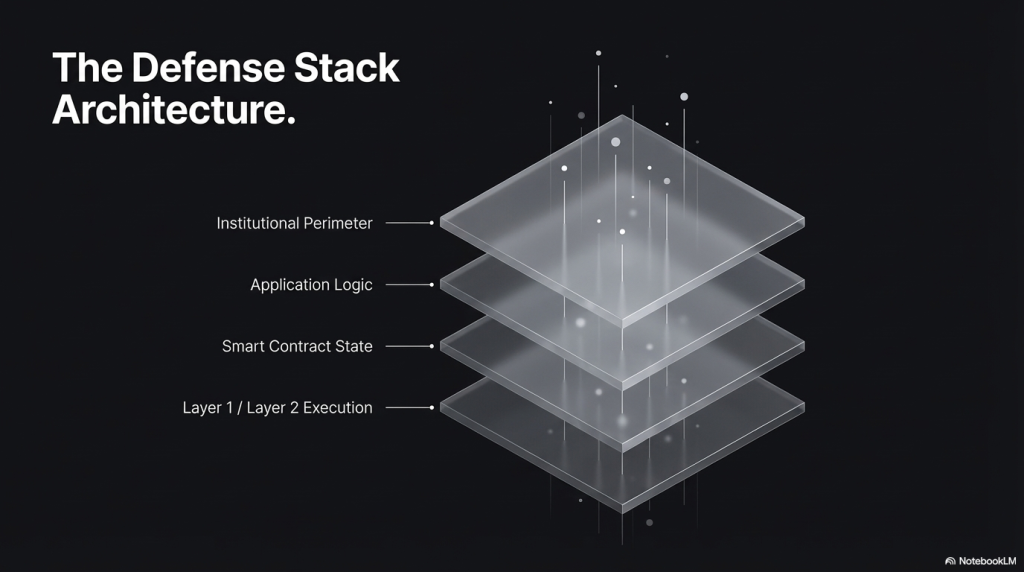
This type of monitoring works across multiple layers:
Mempool Monitoring: Watching unconfirmed transactions before they land on-chain. This is where you catch front-running bots and sandwich attacks.
Smart Contract Event Monitoring: Tracking emitted events from deployed contracts. Every significant action triggers an event. Monitoring these reveals anomalies.
Wallet Behaviour Analysis: Identifying wallets with suspicious histories. Blacklisted addresses. Known exploiter wallets. Newly funded burner addresses.
Liquidity Flow Tracking: Watching sudden large withdrawals from liquidity pools. This is the classic early indicator of a rug pull in motion.
Real-time blockchain threat monitoring does not just look at what happened. It looks at what is happening right now and compares it against what should be happening.
How On-Chain Data Powers Fraud Detection
Every blockchain transaction carries a wealth of data. Source and destination addresses. Gas prices. Token amounts. Contract interactions. Timestamps. Function call signatures. Fraud prevention systems mine this data to find anomalies. Here is how it works in practice.
1. Transaction Volume Anomaly Detection
A protocol normally processes 200 transactions per hour. Suddenly, 4,000 transactions hit in five minutes. That is a red flag. Volume spikes can indicate flash loan attacks, bot activity, or coordinated manipulation. Real-time systems detect these spikes and pause activity or alert teams automatically.
2. Address Risk Scoring
Not all wallets are equal. Some wallets have histories of rug pulls. Some have received funds from known mixer services like Tornado Cash. Some are freshly created minutes before an attack. Real-time on-chain analysis assigns risk scores to wallet addresses. When a high-risk wallet interacts with your protocol, the system immediately flags it.
3. Smart Contract Function Call Monitoring
Most legitimate users interact with protocols in predictable ways. They swap tokens. They add liquidity. They stake assets. Unusual function calls or unusual call sequences indicate exploitation attempts. For example, a re-entrancy attack leaves a very specific on-chain fingerprint. The same function is called multiple times within a single transaction. Monitoring tools can detect this pattern instantly.
4. Oracle Price Deviation Alerts
DeFi protocols rely on price oracles to determine asset values. When an oracle price deviates massively from the market price in a short time, it signals manipulation. Real-time monitoring tracks oracle prices against reference markets. An abnormal deviation triggers an immediate alert or an automated circuit breaker.
The Role of Smart Contract Audits in Fraud Prevention
Real-time monitoring is most effective when the smart contract code itself is clean. A compromised or vulnerable contract is like a house with broken locks. Even the best security camera cannot prevent theft if someone can walk right in. This is where smart contract auditing becomes a foundational piece of any DeFi fraud prevention strategy. Before a protocol goes live, every line of code must be reviewed for vulnerabilities.

SecureDApp’s smart contract audit services do exactly this. SecureDApp has audited hundreds of smart contracts across DeFi, NFT, and blockchain gaming protocols. The team identifies vulnerabilities like access control flaws, integer overflows, re-entrancy risks, and logic errors before they can be exploited. A thorough audit creates the secure foundation on which real-time monitoring then becomes truly effective. You are not just watching the protocol. You are watching a protocol you know has been properly secured.
Building a Real-Time Fraud Detection Stack for DeFi
If you are a DeFi project looking to implement real-time blockchain threat monitoring, here is a practical framework to build on.
Step 1: Audit Your Smart Contracts First
You cannot monitor effectively what has not been secured first. Get a professional smart contract audit done. Understand where the vulnerabilities lie and fix them before launch.
Step 2: Set Up On-Chain Event Monitoring
Use blockchain node providers or indexing services to subscribe to smart contract events. Build alerts for events like large transfers, ownership changes, and access control modifications.
Step 3: Integrate Mempool Watchers
Run or use services that watch the mempool. This gives you visibility into what transactions are about to be confirmed. You can detect attacks before they land.
Step 4: Use Address Intelligence Databases
Integrate address risk scoring APIs. Compare interacting wallets against known fraud databases. Flag or block high-risk addresses from interacting with your protocol.
Step 5: Define Circuit Breakers
Write automated responses into your protocol. If a single transaction withdraws more than X% of liquidity, pause withdrawals temporarily. If oracle price deviates by more than Y%, halt borrowing. These circuit breakers buy time for manual intervention.
Step 6: Establish an Incident Response Protocol
Knowing about a threat is only useful if you can respond quickly. Define who gets alerted, who has authority to pause the protocol, and what communication goes out to users when an incident is detected.
Real-World Cases Where Monitoring Could Have Made a Difference
Let us look at some real DeFi exploits and see where monitoring could have intervened.
The Euler Finance Hack (2023)
Euler Finance lost approximately $197 million in one of the largest DeFi hacks in history. The attacker used a flash loan to manipulate the protocol’s donation mechanism.
The attack involved unusually large flash loan amounts and a sequence of function calls that deviated from normal protocol interaction patterns. A real-time monitoring system watching for abnormal flash loan usage combined with unusual function call sequences could have triggered an alert in time.
The Multichain Incident (2023)
Multichain saw over $125 million drained in suspicious transactions. What was notable was the pattern of large outflows happening over an extended period.
Liquidity flow tracking with anomaly detection on withdrawal size and frequency could have flagged this activity much earlier. Real-time blockchain threat monitoring would have raised alarms on the first few abnormal transactions.
How SecureDApp Helps DeFi Projects Stay Ahead of Threats
SecureDApp is a Web3 security company that has built its reputation on protecting DeFi, NFT, and blockchain infrastructure projects from exactly these kinds of attacks. SecureDApp offers a full spectrum of security services that work together as a layered defence system.
Smart Contract Audits: SecureDApp’s team of experienced auditors reviews code manually and with automated tools. They have audited projects across EVM and non-EVM chains including Ethereum, Solana, Polygon, BNB Chain, and Avalanche.
Blockchain Threat Intelligence: SecureDApp provides actionable threat intelligence that helps projects understand their risk surface before and after launch.
Incident Response Support: When something goes wrong, SecureDApp’s team helps projects respond quickly, trace fund flows, and work with affected parties.
For DeFi teams that are serious about security, starting with SecureDApp’s audit and building a monitoring strategy on top of that clean foundation is the right approach. You can visit securedapp.io to explore these services and request a consultation.
Key Metrics to Monitor for DeFi Fraud Prevention
If you are building your own monitoring framework, here are the specific metrics that matter most.
Total Value Locked (TVL) Delta: Watch for sudden drops in TVL. A rapid outflow in a short window is a critical warning sign.
Gas Price Spikes: Abnormally high gas prices often indicate bots competing to front-run transactions.
New Contract Interactions: Track when a previously unknown contract starts interacting with your protocol at scale.
Approval Events: Unlimited token approvals from unusual addresses are a phishing and exploit vector.
Ownership Transfer Events: Any ownership or admin role transfer should trigger immediate investigation.
Cross-Chain Bridge Activity: Monitor large amounts flowing through bridges as they are often the first step in fund extraction.
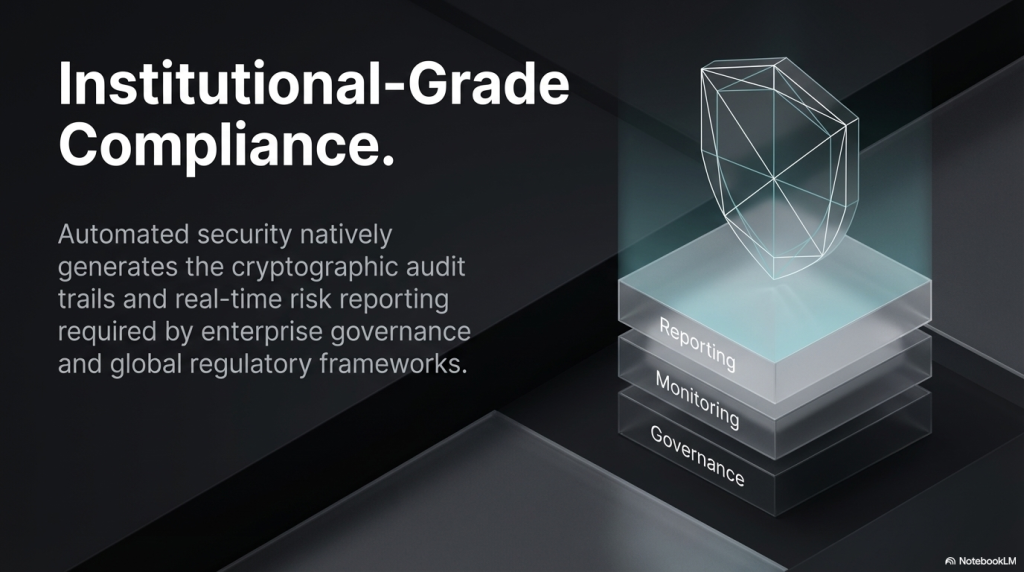
The Regulatory Push Is Also Driving Monitoring Adoption
India’s FIU-IND has started requiring VDA service providers to comply with AML obligations. FATF guidelines are increasingly applying travel rule requirements to DeFi. The EU’s MiCA regulation is bringing structured oversight to crypto assets. Real-time on-chain monitoring is no longer just a good security practice. It is becoming a regulatory requirement for any DeFi protocol that wants to operate in regulated markets.
Projects that already have robust monitoring infrastructure in place will find compliance significantly easier. They already have the data. They already have the logs. They already have the audit trail.
Common Mistakes DeFi Projects Make With Security Monitoring
Even projects that invest in monitoring often make these critical mistakes. Monitoring Without Auditing First: Setting up alerts for a vulnerable contract is like installing a burglar alarm in a house with no walls. Fix the code first.
Alert Fatigue: Too many alerts and teams stop paying attention. Tune your monitoring to flag what truly matters with high confidence.
No Incident Response Plan: Detection without response is useless. Know exactly what to do when an alert fires.
Single Chain Focus: DeFi exploits often span multiple chains. Your monitoring needs multi-chain visibility.
Not Updating Detection Rules: Attackers adapt. Update your threat signatures and detection logic regularly.
Conclusion: The Future of DeFi Security Is Proactive, Not Reactive
The DeFi ecosystem is maturing. Billions of dollars of value now sit in smart contracts. The stakes are too high for security to remain an afterthought. Real-time blockchain threat monitoring is not a luxury. It is the minimum standard for any serious DeFi protocol that wants to protect its users and its reputation.
The technology is available. The data is on-chain and publicly accessible. The tools exist to build powerful monitoring systems. What is needed is the commitment to build security into the protocol architecture from day one. Start with a thorough smart contract audit. Build your monitoring stack on that secure foundation. Define your circuit breakers and incident response procedures. Train your team to respond swiftly.
If you are building a DeFi protocol and want to get your security foundation right, SecuredApp is a trusted partner that has helped hundreds of Web3 projects do exactly this. Visit securedapp.io to learn more about their smart contract audit and blockchain security services.
Frequently Asked Questions (FAQs)
Real-time blockchain threat monitoring is the continuous surveillance of on-chain transactions and smart contract activity as they happen. It analyses patterns, flags anomalies, and triggers alerts when suspicious activity is detected. Unlike post-incident analysis, it works proactively before damage is done.
On-chain data includes transaction details, wallet histories, smart contract events, gas prices, and token flows. Fraud prevention systems analyse this data to detect volume anomalies, high-risk wallet interactions, unusual function call patterns, and oracle price manipulations in real time.
Flash loans happen within a single transaction block, making full prevention extremely challenging. However, monitoring can detect abnormal flash loan usage patterns, unusual function call sequences, and oracle price deviations associated with flash loan attacks. Circuit breakers can then automatically pause the protocol to limit damage.
A smart contract audit identifies and fixes vulnerabilities in the code before deployment. Monitoring watches for unusual behaviour at runtime. Both are essential together. Monitoring a vulnerable contract only tells you when it is being exploited. Auditing removes the vulnerability that allows exploitation in the first place.
SecureDApp provides end-to-end Web3 security services including smart contract audits, blockchain threat intelligence, and incident response support. Their team has audited projects across major chains including Ethereum, BNB Chain, Solana, Polygon, and Avalanche. Visit securedapp.io to request a consultation



