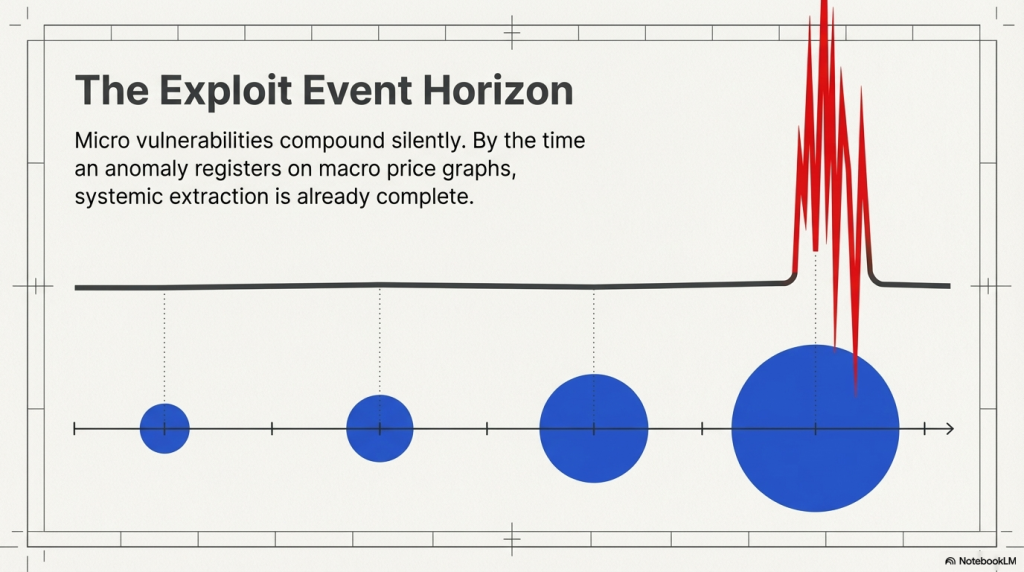
The blockchain ecosystem moves fast. Very fast. In the time it takes to read this sentence, hundreds of transactions have been submitted, validated, and settled on-chain. And somewhere in that chaos, there are bad actors looking for a window. MEV extraction and flash loan attacks are not hypothetical threats.
They are happening right now, across every major chain. These attacks are sophisticated, automated, and often invisible to the naked eye. Real-time blockchain threat monitoring is the only credible defence. This blog goes deep into the mechanics of MEV and flash loans, how detection systems work, and what security teams and developers must know to stay ahead.
Understanding MEV: The Hidden Tax on Every Transaction
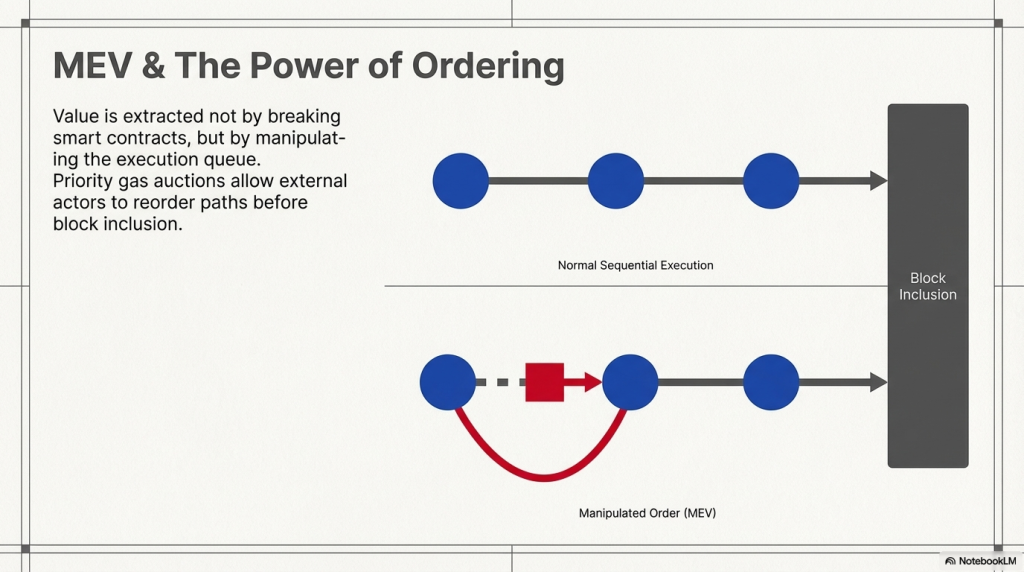
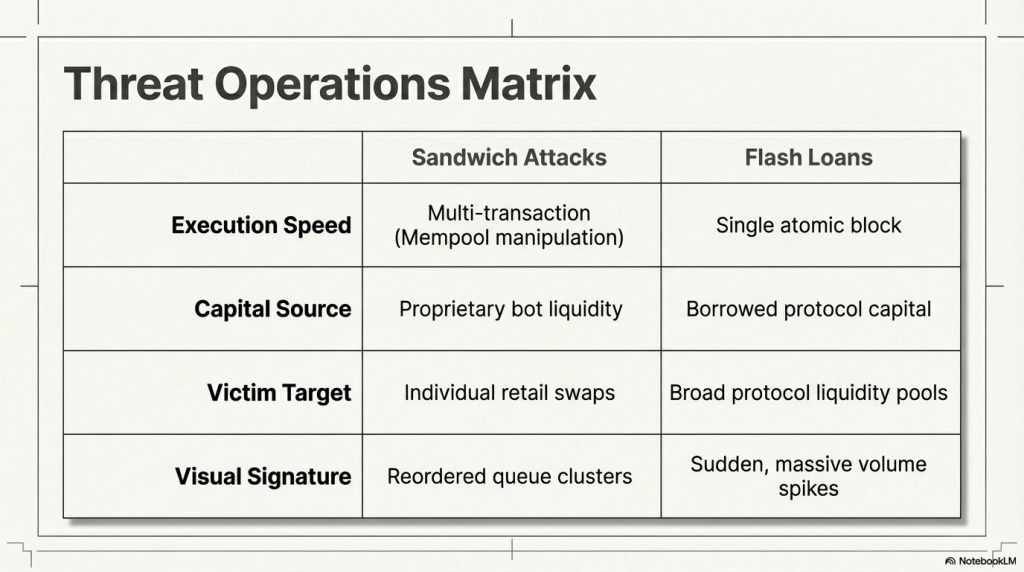
Maximal Extractable Value, or MEV, refers to the profit a miner or validator can extract by manipulating transaction ordering inside a block. It was originally called Miner Extractable Value when Proof-of-Work was dominant. The concept remains the same across consensus mechanisms.
How MEV Actually Works
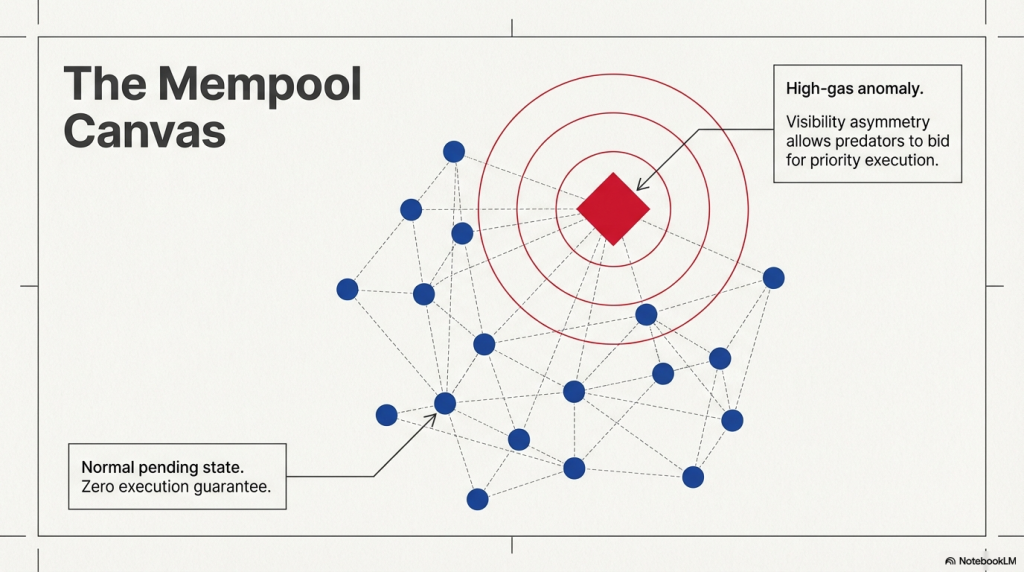
Every transaction you submit goes into the mempool first. It waits there, publicly visible, before being picked up by validators. MEV bots scan this mempool in real time. They identify profitable opportunities and either front-run, back-run, or sandwich your transaction.
The Three Core MEV Attack Patterns
- Front-running: The bot sees your pending trade and places its own trade before yours. It gets a better price. You get a worse one.
- Back-running: The bot places a trade immediately after a known profitable transaction. This is common in liquidation scenarios.
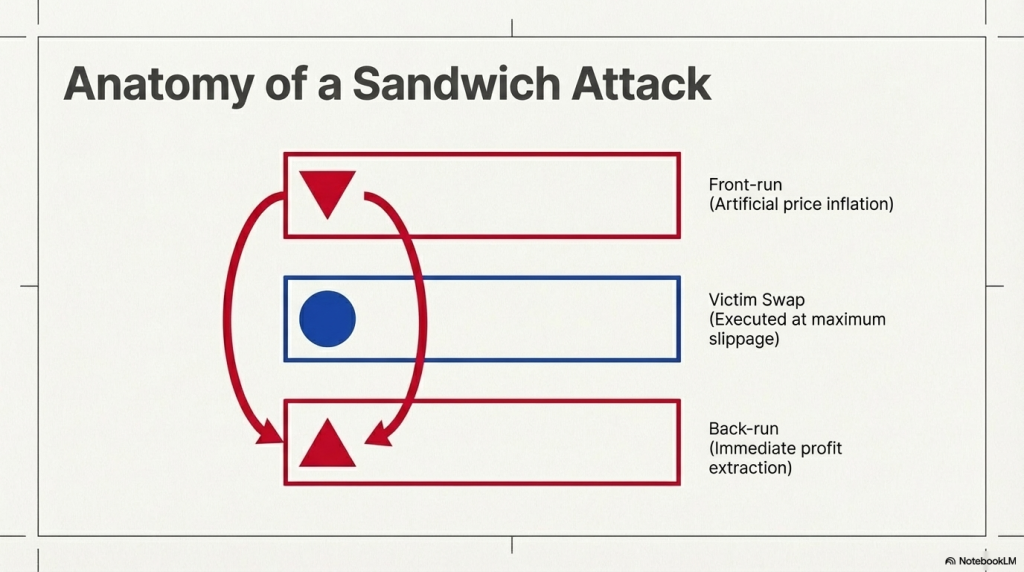
- Sandwich attacks: The bot wraps your transaction between two of its own. It buys before you, drives the price up, then sells after you buy at the inflated price.
According to Flashbots data, cumulative MEV extracted on Ethereum alone has exceeded $1.3 billion. The number is likely much higher when you factor in private order flow and cross-chain activity.
MEV is not just a financial problem. It degrades user trust, distorts market prices, and creates unfair advantages for those with faster infrastructure. Real-time blockchain threat monitoring systems are specifically designed to identify these patterns before or as they happen.
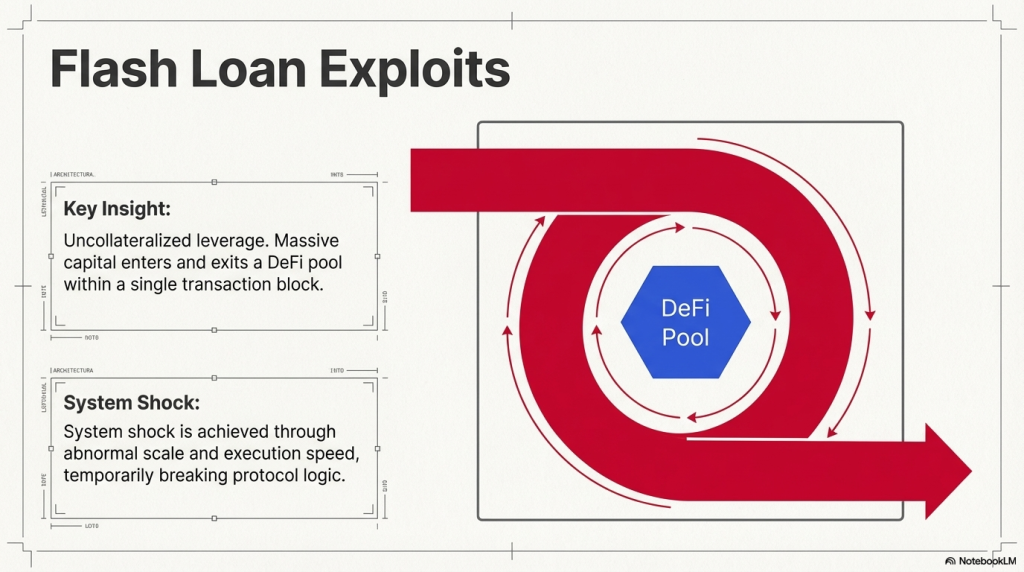
Flash Loan Attacks: Speed as a Weapon
Flash loans are a genuinely innovative DeFi primitive. You can borrow millions of dollars with zero collateral, as long as you return the funds within a single transaction. The entire borrow-use-repay cycle happens atomically.
Attackers weaponise this. They borrow massive amounts, manipulate on-chain price oracles or liquidity pools, extract profit, and repay the loan. All within one transaction. If the repayment fails, the entire transaction reverts. The attacker loses nothing except gas.
Anatomy of a Flash Loan Attack
A typical flash loan exploit follows this sequence:
- Borrow a large sum from a lending protocol like Aave or dYdX
- Use borrowed capital to manipulate prices on a DEX or oracle
- Exploit the manipulated state to drain a vulnerable protocol
- Repay the flash loan and pocket the difference
The bZx attack in 2020 used flash loans to manipulate Uniswap prices and drain funds from the bZx margin trading protocol. The attacker made nearly $1 million in a single transaction. Since then, flash loan exploits have drained hundreds of millions from DeFi protocols.
Why Traditional Security Tools Fail Here
Flash loan attacks are atomic. They complete within milliseconds. Static code audits can identify vulnerable patterns, but they cannot prevent an attack that is already executing. You need detection at the transaction level, in real time.
Real-Time Blockchain Threat Monitoring: The Technical Architecture
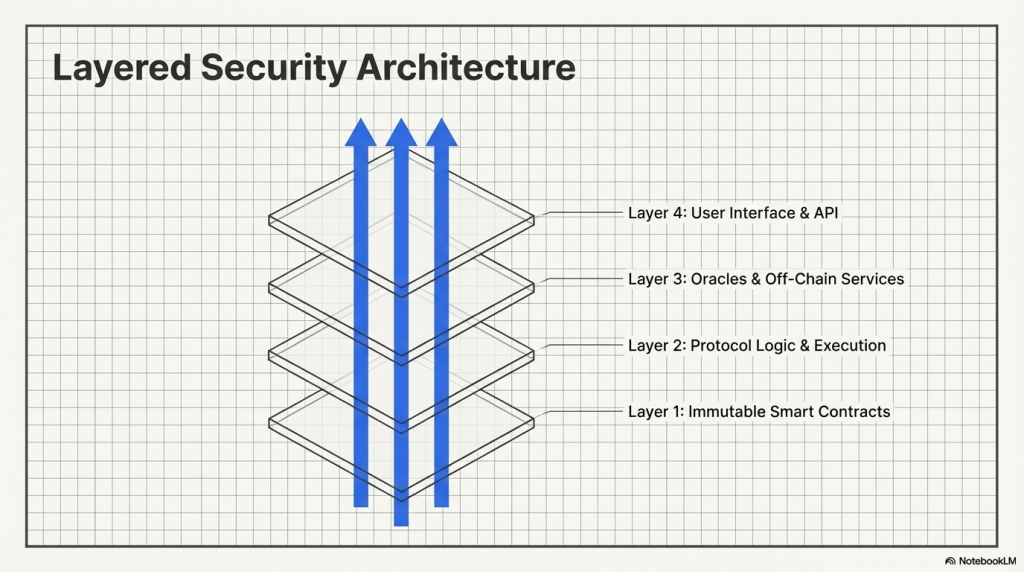
Real-time blockchain threat monitoring is not a single tool. It is a layered architecture that combines mempool surveillance, on-chain event analysis, heuristic pattern matching, and anomaly detection.
Layer 1: Mempool Surveillance
The mempool is the first line of intelligence. Monitoring systems connect directly to multiple nodes and ingest pending transactions as they arrive. The system flags transactions with unusually high gas prices, which is a classic sign of front-running intent. It also identifies transactions that interact with known vulnerable contracts or mimic patterns seen in past exploits.
Layer 2: On-Chain Event Streaming
Once transactions are mined, event logs provide a rich stream of data. Monitoring systems parse Transfer events, Swap events, Borrow and Repay events in real time. A flash loan attack will always emit a borrow event followed immediately by abnormal token flows within the same block.
Layer 3: Heuristic and Signature-Based Detection
Security researchers encode known attack patterns into detection signatures. A sandwich attack signature, for instance, looks for three consecutive transactions where the first and third share the same sender address and interact with the same liquidity pool. When this pattern appears, an alert is triggered instantly.
Layer 4: Anomaly Detection Using ML
Not every attack matches a known signature. Machine learning models trained on historical exploit data can detect statistical deviations in transaction behaviour. Sudden spikes in a contract’s interaction volume, unusual token price movements within a single block, or atypical call depth in contract execution are all signals that warrant investigation.
SecureDApp’s smart contract monitoring module integrates all four of these layers. It provides continuous surveillance across deployed contracts, generating real-time alerts when exploit patterns are detected. Protocol teams can configure custom alert thresholds and get notified within seconds.
Key Detection Signals for MEV and Flash Loan Attacks
Knowing what to look for is half the battle. These are the primary technical indicators that real-time blockchain threat monitoring systems use to identify active threats.
MEV Detection Signals
- Gas price spikes: MEV bots pay premium gas to guarantee transaction ordering.
- Identical contract calls in the same block: Front-run and back-run pairs often target the same function.
- Profit extraction patterns: Sequences where one address consistently profits from surrounding transactions.
- Use of Flashbots bundles or private relays: Not all MEV is visible in the public mempool.
Flash Loan Attack Detection Signals
- Large borrow followed by price impact: A sudden borrow of millions followed by significant oracle price changes is a red flag.
- Call depth anomalies: Flash loan exploits often involve deeply nested contract calls. Detection systems monitor maximum call depth per transaction.
- Token balance irregularities: A protocol’s token reserve dropping sharply within one block is a strong indicator.
- Reentrancy patterns: Some flash loan attacks exploit reentrancy vulnerabilities. Unusual recursive call patterns trigger alerts.
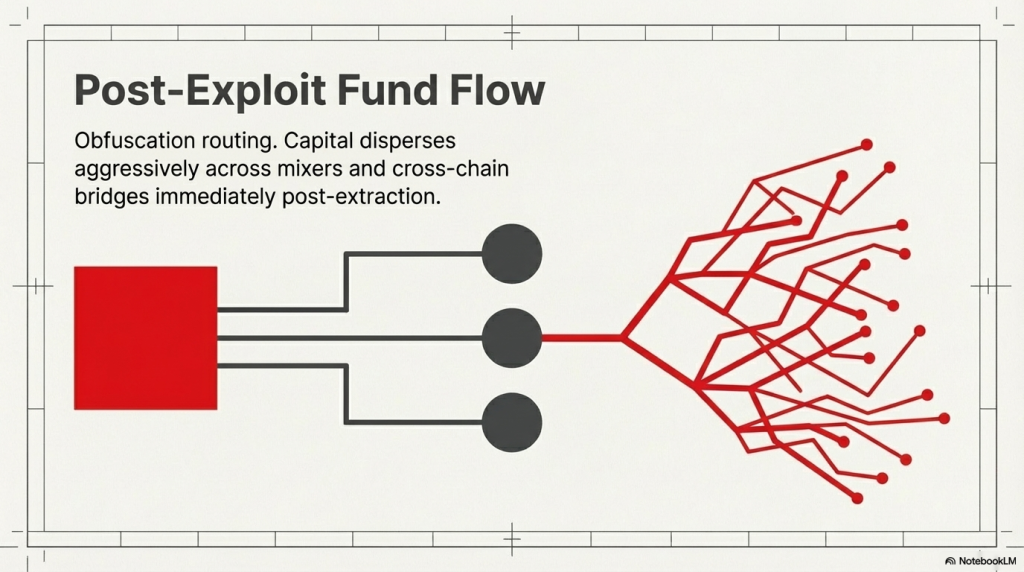
On-Chain Forensics: Tracing an Attack After It Happens
Prevention is the goal, but not every attack is caught before it executes. Post-incident forensics are critical for understanding what happened, how much was lost, and how to prevent recurrence.
Transaction Trace Analysis
Tools like Tenderly, Etherscan’s transaction trace view, and OpenZeppelin Defender allow analysts to replay a transaction step by step. You can see exactly which functions were called, in what order, and what state changes occurred. This is essential for identifying the exploit path.
Fund Flow Mapping
After an attack, the stolen funds move. Monitoring tools track token flows across wallets in real time. If stolen assets are being routed through mixers like Tornado Cash or cross-chain bridges, the system can flag the associated wallet addresses for community blacklisting.
Smart Contract Audit Review
Post-incident, teams should revisit the contract’s audit history. Was the vulnerable function flagged in any prior audit? If yes, why was it not remediated? SecureDApp’s smart contract audit service provides a detailed vulnerability report, including severity classification and remediation guidance. Coupling this with continuous monitoring creates a full security lifecycle for any DeFi protocol.
The Role of Smart Contract Audits in Pre-empting These Attacks
Real-time blockchain threat monitoring catches attacks as they happen. But catching is not the same as preventing. A smart contract audit done before deployment is where true prevention begins.
What Auditors Look For
- Price oracle dependencies: Is the contract relying on a single oracle that can be manipulated?
- Reentrancy vulnerabilities: Can an attacker re-enter a function before state updates are committed?
- Unchecked external calls: Does the contract trust return values from external contracts without validation?
- Flash loan attack surfaces: Can a large borrowed amount destabilise the contract’s internal accounting?
SecureDApp offers comprehensive smart contract audits that cover all of these vectors and more. The audit process includes automated scanning using industry-standard tools combined with manual review by experienced security researchers. The output is a structured report that development teams can act on before going live.
An audit without monitoring is incomplete. A protocol can be perfectly audited at deployment but become vulnerable as the DeFi ecosystem changes around it. New liquidity sources, new oracles, new composability patterns introduce fresh attack surfaces. This is why audit plus continuous monitoring is the gold standard.
Building a Real-Time Threat Detection Pipeline: A Developer’s Perspective
If you are building a DeFi protocol or working on a security tooling product, here is a practical architecture for a real-time threat detection pipeline.
Step 1: Connect to Multiple Node Providers
Relying on a single RPC endpoint creates a single point of failure. Connect to at least three providers across different geographies. Use WebSocket connections for low-latency mempool access. Providers like QuickNode, Alchemy, and Infura all offer mempool streaming endpoints.
Step 2: Ingest and Decode Transaction Data
Parse incoming transactions using the contract ABI. Decode function selectors and input data. Build a local data structure that maps transaction hash to decoded action. This is the raw material for your detection logic.
Step 3: Apply Detection Rules
Define rules as composable functions. A sandwich attack rule, for instance, would check if within the last N transactions there exists a pattern of Address A buys, then another swap, then Address A sells. Rules should be configurable, versioned, and testable against historical data.
Step 4: Alert and Respond
Alerts should be multi-channel: webhook, email, Telegram bot, and PagerDuty integration. For critical threats, the response can be automated. Circuit breakers built into the smart contract can pause operations if a certain anomaly threshold is crossed. SecureDApp’s monitoring platform supports on-chain response actions for protocols that have integrated the relevant guardian contracts.
Industry Examples: What Happens Without Proper Monitoring
The DeFi graveyard is full of protocols that learned the hard way. These examples are instructive.
Cream Finance ($130 Million, October 2021)
Attackers used flash loans to exploit a price oracle manipulation vulnerability in Cream Finance. The attack involved over 50 transactions and drained approximately $130 million. The complex transaction chain went undetected until it was too late. A monitoring system configured to flag unusual oracle deviations combined with flash loan borrowing would have triggered alerts mid-attack.
Mango Markets ($114 Million, October 2022)
The attacker manipulated the MNGO token price through spot market trades and then borrowed against the artificially inflated collateral. This was not a flash loan attack in the traditional sense, but it shared the same oracle manipulation vector. On-chain price deviation monitoring would have been the critical detection layer here.
Euler Finance ($197 Million, March 2023)
One of the largest flash loan attacks in DeFi history. The attacker exploited a logic flaw in Euler’s donation mechanism using flash loans. Post-incident analysis revealed the vulnerable code had been introduced several months earlier. A combination of code review and continuous monitoring of borrowing patterns could have detected this earlier.
How SecureDApp Approaches Real-Time Blockchain Threat Monitoring
SecureDApp’s suite of security tools is built specifically for the DeFi and Web3 ecosystem. The approach is end-to-end, covering pre-deployment security and live production monitoring.
Smart Contract Audits
Every protocol should begin with a thorough audit. SecureDApp’s audit process uses both automated vulnerability scanners and manual expert review. The output is an actionable report categorised by severity: critical, high, medium, and low. Teams get clear remediation steps, not just a list of issues.
Continuous On-Chain Monitoring
Post-deployment, SecureDApp monitors contract activity 24/7. The system tracks function calls, token flows, gas usage patterns, and interaction frequency. Deviations from baseline behaviour trigger alerts in real time. Protocol teams can configure which contracts to watch and which thresholds to set.
Threat Intelligence and Reporting
SecureDApp maintains a growing database of known attack vectors, malicious wallet addresses, and exploit signatures. This intelligence feeds directly into the monitoring engine, enabling faster identification of known threat actors. Monthly security reports give protocol teams a clear picture of the threat landscape.
Best Practices for Protocol Teams and Security Engineers
Whether you are a solo developer building on a testnet or a protocol managing hundreds of millions in TVL, these practices are non-negotiable.
- Audit before deployment, always: No exception. Even simple contracts can have dangerous edge cases.
- Use time-weighted average prices (TWAP) for oracles: TWAP-based oracles are significantly harder to manipulate within a single block.
- Implement circuit breakers: On-chain pause mechanisms that activate on anomaly detection can prevent full exploitation.
- Monitor the mempool continuously: Front-running attempts often appear in the mempool minutes before execution.
- Run post-mortems on every near-miss: Near-miss events are intelligence. Study them seriously.
- Test against known attack vectors: Use forked mainnet environments to simulate flash loan attacks and MEV scenarios before going live.
Conclusion: Monitoring Is Not Optional Anymore

The DeFi space has matured considerably. But so have the attackers. MEV extraction and flash loan exploits are now highly professionalised. Entire teams of researchers and developers work full-time on finding and exploiting vulnerabilities in smart contracts. Real-time blockchain threat monitoring is not a luxury feature. It is foundational infrastructure for any protocol that takes its users’ funds seriously. Combined with thorough smart contract audits, robust oracle design, and well-tested circuit breakers, it forms the backbone of a credible security posture.
SecureDApp is committed to making this level of security accessible to every team building in Web3. From comprehensive audits to always-on monitoring, the tools exist. The question is whether protocol teams will choose to use them. If you are building a DeFi protocol or managing existing smart contract deployments, reach out to the SecureDApp team at securedapp.io. Get your contracts audited. Get your production environment monitored. Because in this space, it is not a question of if an attack will come. It is a question of whether you will see it coming.
FAQ on Blockchain Threat Monitoring
Real-time blockchain threat monitoring involves continuous surveillance of on-chain and mempool activity. It detects suspicious transaction patterns, anomalous token flows, and known exploit signatures as they occur. The goal is to alert protocol teams or trigger automated responses before or during an attack, not after.
MEV cannot be entirely eliminated as long as public mempools exist. However, it can be significantly mitigated. Using private transaction relays, slippage controls, and commit-reveal schemes reduces MEV exposure. Monitoring systems help identify which bots are repeatedly targeting your protocol, enabling strategic responses.
Flash loan attacks are atomic. The entire sequence happens within a single transaction block. This makes them extremely fast and difficult to detect in advance. Regular exploits may unfold over multiple transactions and blocks. The atomic nature of flash loan attacks means real-time monitoring must operate at sub-second latency.
SecureDApp combines smart contract audit intelligence with live monitoring. The system uses known vulnerabilities identified during audits to create custom monitoring signatures for each protocol. This means the monitoring is not generic. It is tailored to the specific risk profile of your deployed contracts.
First, pause the protocol if a pause mechanism exists. Second, secure the remaining funds by disabling vulnerable functions. Third, trace the attack using transaction replay tools to understand the exploit path. Fourth, engage a security firm like SecureApp for a post-incident audit and patching. Fifth, communicate transparently with your community. Speed and transparency are both critical in the aftermath.



