In 2023 alone, over USD 1.8 billion was lost to DeFi exploits and on-chain attacks. Most of those losses had one thing in common: the threat was visible on-chain before any damage was done. Nobody was watching. Real-time blockchain threat monitoring exists precisely to fix this gap. It is not a dashboard. It is an active defence layer that watches every transaction, flags anomalies, and enables containment before exploits fully execute. This blog breaks down how on-chain monitoring works, why traditional security tools fall short, and what a well-architected monitoring stack looks like in 2026.

Why Blockchain Threats Need a Different Approach
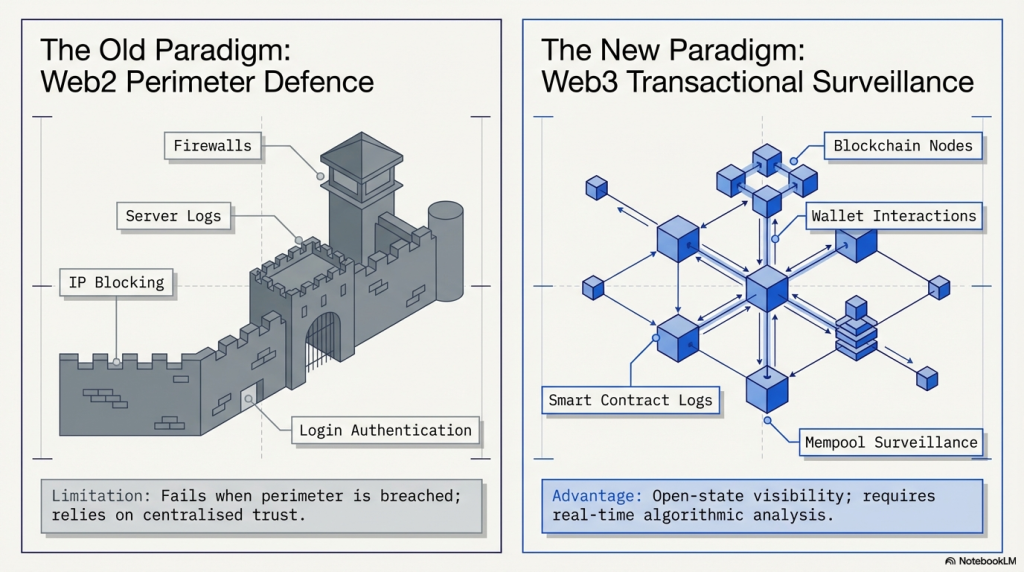
Traditional cybersecurity is built around perimeter defence. Firewalls, endpoint tools, and access controls protect a known boundary. Blockchain has no perimeter. Every transaction is public. Every contract is open. Every interaction happens on a shared, permissionless ledger. This openness is by design, but it creates a threat surface that perimeter tools cannot cover.
Attackers on-chain move fast. A flash loan exploit can execute across multiple protocols in a single block. A reentrancy attack can drain a contract in seconds. A malicious wallet can manipulate liquidity and exit before any alert fires. The attack window is often under 30 seconds. Post-mortem analysis does not help here. You need monitoring that detects threats as they are unfolding, not after.
The Structural Gap in Traditional Security
Most Web3 teams rely on two tools: smart contract audits and manual monitoring. Audits are essential. But they are point-in-time assessments. They evaluate code at the moment of review, not during live operation. New exploits emerge constantly. A contract that passed audit in January may have a vulnerability surface exposed by a protocol upgrade in March. An audit cannot protect you in real time. Manual monitoring is not feasible at scale. Tens of thousands of transactions hit major chains every minute. No security team can parse that volume manually.
The gap between audit and runtime is where most exploits land.
| Security Layer | What It Covers | What It Misses |
| Smart Contract Audit | Pre-deployment vulnerability scan | Runtime conditions, new vectors |
| Manual Monitoring | Known alert patterns | Speed, scale, novel anomalies |
| Real-Time On-Chain Monitoring | Live transaction behaviour | Nothing, by design |
What Real-Time Blockchain Threat Monitoring Actually Does
Real-time blockchain threat monitoring is an active intelligence layer. It sits between the chain and your response team.
Here is what it does at a technical level.
1. Mempool Surveillance
Transactions broadcast to the network sit in the mempool before they are included in a block. Monitoring the mempool gives you visibility before confirmation. You can detect suspicious patterns at the point of intent, not execution. This is where MEV (Maximal Extractable Value) attacks, sandwich attacks, and front-running behaviours first appear.
2. Event Log and State Change Analysis
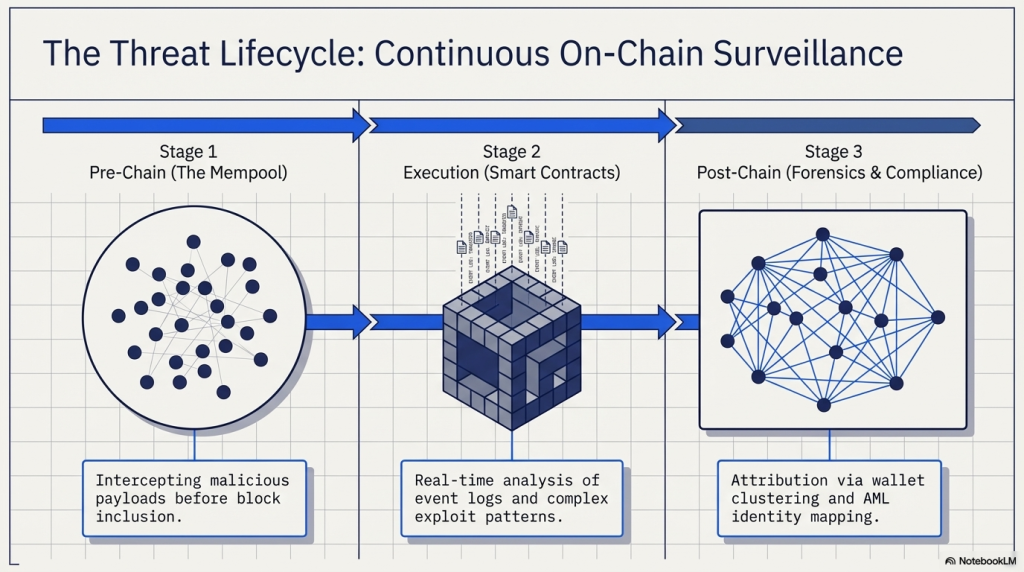
Smart contracts emit events when state changes occur. Transfers, approvals, function calls, ownership changes. A monitoring system parses these event logs in real time. It looks for sequences that match known attack patterns. Example: A large approval followed by an immediate multi-hop transfer across three wallets in one block. That sequence is an indicator of a compromised key or a malicious approval exploit.
3. Behavioural Anomaly Detection
Not all threats match known signatures. A well-built monitoring system uses behavioural baselines. It learns what normal looks like for a specific contract or protocol. Unusual deviations trigger alerts. This is how novel, zero-day attacks are caught before they appear in any threat database.
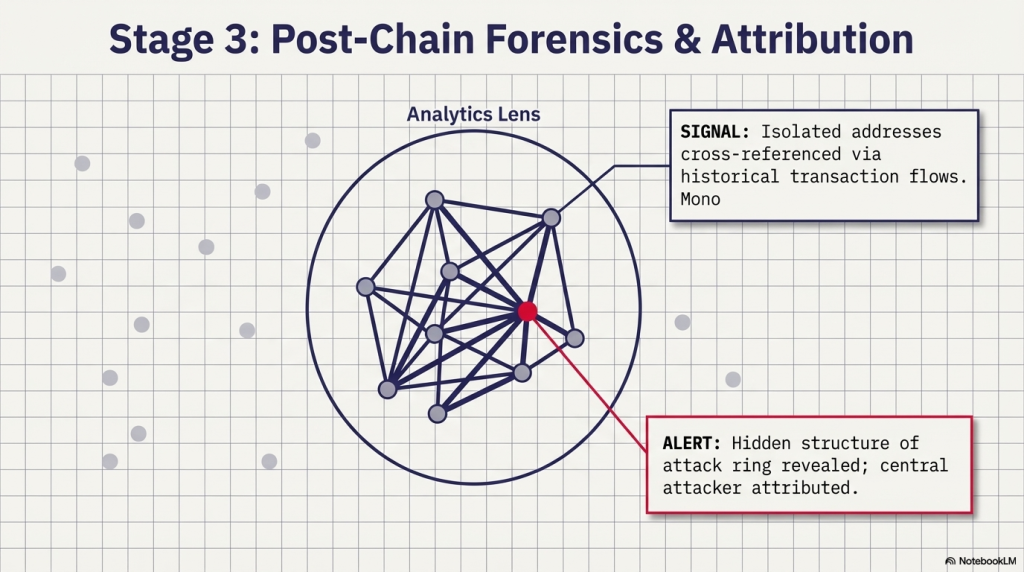
4. Wallet Clustering and Attribution
Sophisticated attackers use multiple wallets to obscure origin and movement. On-chain monitoring tools map wallet relationship graphs. They identify clusters of addresses likely controlled by the same entity. This is critical for both threat detection and post-incident forensic investigation.
5. Automated Containment
Detection without response is incomplete. Advanced monitoring platforms integrate with protocol-level controls. When a threat is confirmed, the system can trigger automated actions.
- Pause vulnerable contract functions
- Block suspicious wallet interactions
- Alert security teams via webhook, Slack, or PagerDuty
- Log evidence for forensic use
Attack Types That On-Chain Monitoring Can Detect
Let us be specific about what kinds of threats a real-time monitoring stack is built to catch.
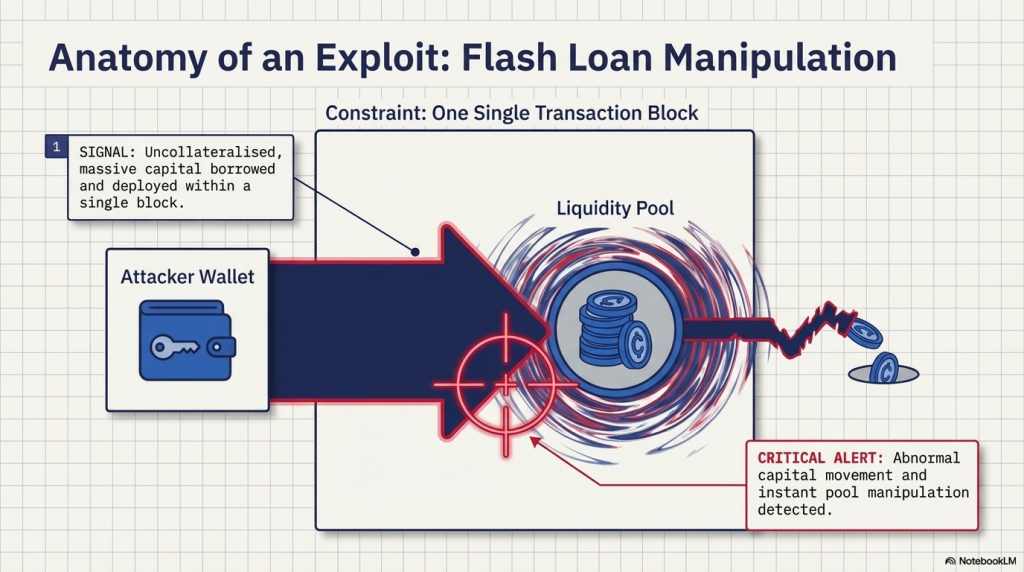
Flash Loan Attacks
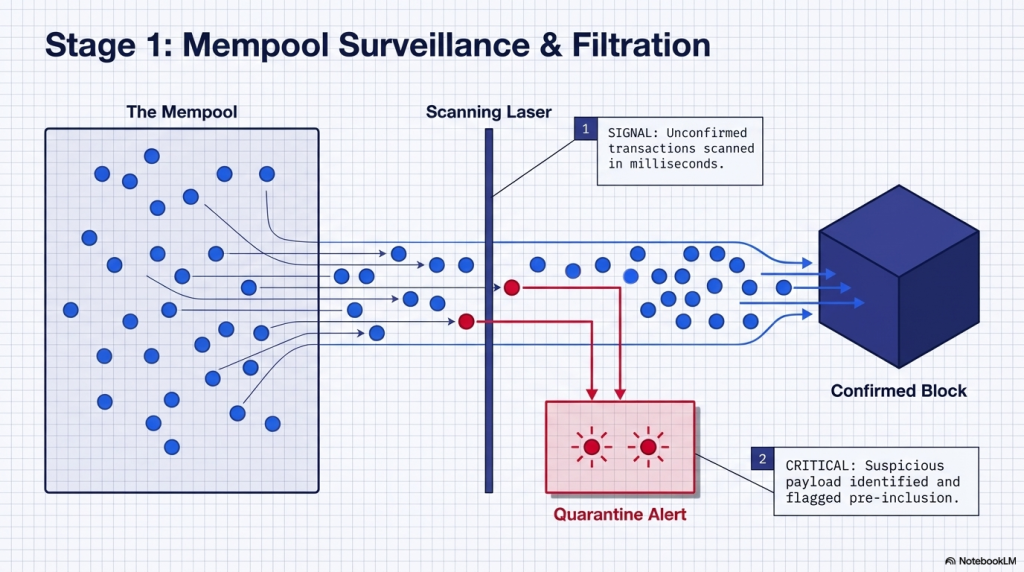
Flash loans allow borrowing large sums without collateral, provided the loan is repaid in the same transaction. Attackers use flash loans to manipulate oracle prices, drain liquidity pools, or trigger protocol logic flaws.The signal is visible at the mempool level. A single transaction borrowing hundreds of millions, touching multiple contracts, repaying instantly. This pattern is detectable before block confirmation.
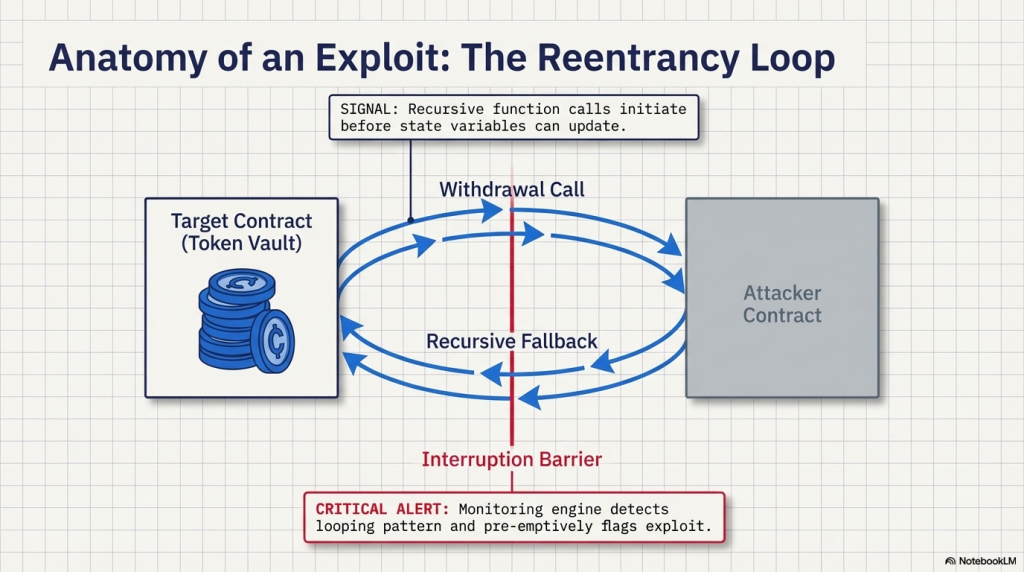
Reentrancy Exploits
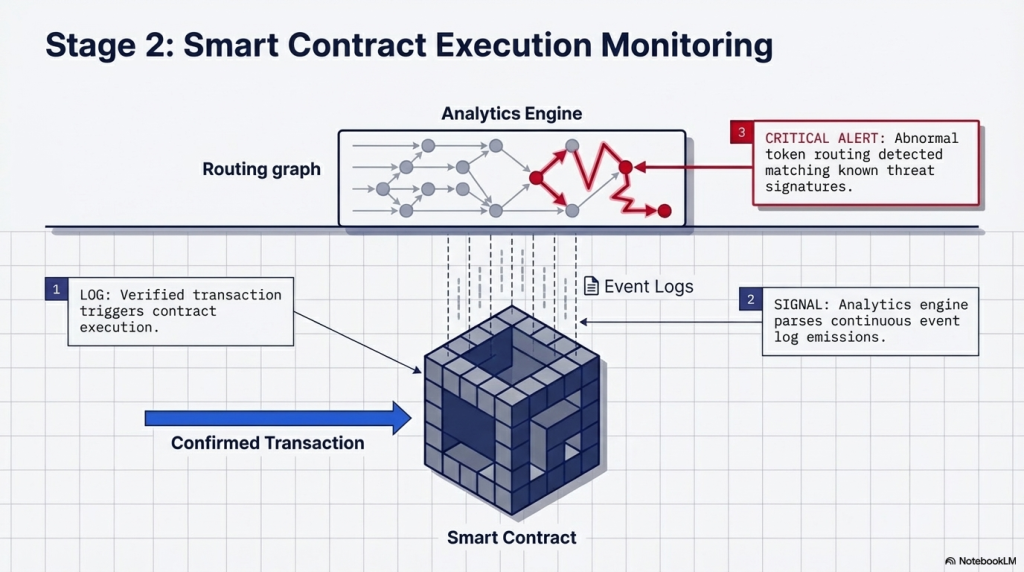
A reentrancy attack tricks a contract into calling an external function before updating its internal state. The attacker withdraws funds, the withdrawal triggers another withdrawal, and the loop repeats until the contract is drained. Monitoring for recursive external calls on withdrawal functions is a known detection strategy. Live event parsing can catch this in real time.
Price Oracle Manipulation
DeFi protocols use price oracles to determine asset values. If an attacker manipulates the oracle, they can borrow more than their collateral covers. Real-time monitoring watches for rapid, large price deviations on monitored oracle feeds. An abnormal price spike or crash in a short window triggers an immediate alert.
Governance Attacks
Some protocols have been attacked through their own governance mechanisms. A large token purchase, an immediate governance proposal, a flash vote, and a malicious execution. This sequence unfolds over hours, sometimes minutes. Monitoring governance contract events and token flow patterns can surface this threat early enough to intervene.
Rug Pull Indicators
Not every threat is external. Monitoring token contract ownership, liquidity lock status, and large insider wallet movements can surface rug pull risk early. Signals include: sudden LP token withdrawal, contract ownership transfer to an unknown address, or large insider sells.
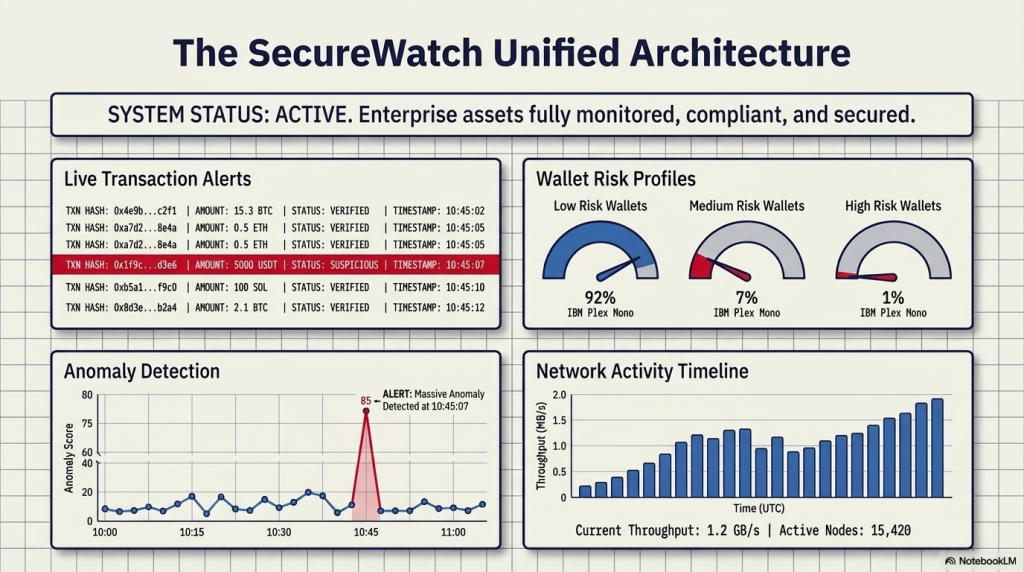
How SecureWatch Operationalises This Model
SecureDApp’s SecureWatch is built to operationalise real-time blockchain threat monitoring at an enterprise level. It is not a passive alert dashboard. It is an active containment layer.
| Capability | What SecureWatch Does |
| Behavioural anomaly detection | Establishes baselines, flags deviations in real time |
| Wallet clustering intelligence | Maps multi-wallet attack setups automatically |
| Contract pause mechanisms | Integrates with protocol controls for immediate containment |
| Policy-based automation | Custom rules that trigger specific response actions |
| DevSecOps integration | Continuous monitoring pipeline within development workflows |
| Cross-chain visibility | Monitors activity across multiple chains simultaneously |
The key differentiator is that SecureWatch does not just monitor. It contains. When a threshold is crossed, the system acts. This reduces the response window from minutes to seconds. For crypto exchanges, DeFi protocols, and institutional blockchain deployments, that difference is the difference between a contained incident and a catastrophic loss.
On-Chain Monitoring vs Traditional Monitoring: A Direct Comparison
| Parameter | Traditional Security Monitoring | Real-Time On-Chain Monitoring |
| Data source | Server logs, network traffic | Mempool, event logs, state changes |
| Detection speed | Minutes to hours | Seconds to sub-second |
| Coverage | Off-chain infrastructure | Smart contracts, wallets, protocols |
| Threat types | Network intrusions, malware | Flash loans, reentrancy, oracle attacks |
| Response action | Alert and investigate | Alert, contain, and investigate |
| Cross-chain support | Not applicable | Native multi-chain coverage |
The two are not alternatives. They are complementary. But for Web3-native threats, traditional tools have no visibility into the attack surface that matters.
The Architecture of an Enterprise Monitoring Stack
A production-grade monitoring deployment is not a single tool. It is a layered architecture.
Layer 1: Data Ingestion
Raw chain data from full nodes, archive nodes, and RPC providers. Mempool feeds from relevant networks. High-throughput ingestion pipelines are needed. At peak, Ethereum processes over 1 million transactions per day.
Layer 2: Detection Engine
Rules-based detection for known patterns. ML-based anomaly detection for unknown threats. Custom policy rules defined by the security team for protocol-specific risks.
Layer 3: Alert and Response Layer
Tiered alerting. Low severity for informational. High severity for immediate action. Integration with incident response workflows, on-call systems, and protocol governance.
Layer 4: Forensic and Evidence Layer
Every alert, every triggered event, every wallet interaction is logged. This creates an audit trail for post-incident investigation, regulatory reporting, and legal action. SecureDApp’s SecureTrace works in conjunction with SecureWatch here, enabling full forensic reconstruction of attack sequences.
Regulatory Implications for Enterprise Deployments
Real-time blockchain threat monitoring is increasingly a compliance requirement, not just a security best practice. Regulated entities operating in Web3 are expected to demonstrate active risk controls. Passive audits do not satisfy this expectation. Regulatory bodies including FATF, MAS, and India’s evolving VDA framework all point toward continuous monitoring obligations for Virtual Asset Service Providers (VASPs).
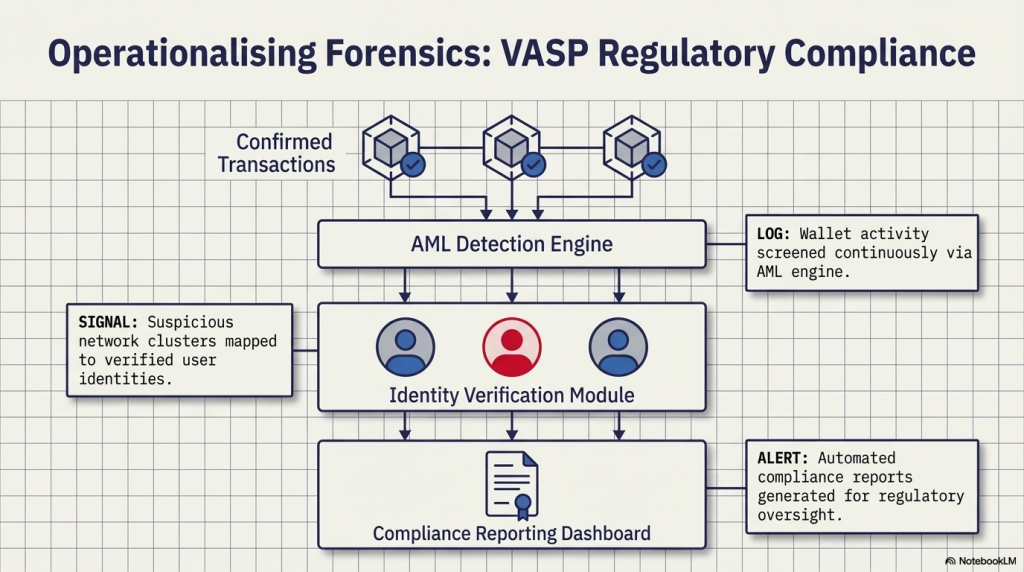
For enterprises integrating blockchain infrastructure, a documented monitoring stack reduces regulatory exposure and satisfies audit requirements. SecureDApp’s position as a UIDAI-registered Offline Verification Seeking Entity (OVSE) reinforces this compliance architecture. It bridges Web3 monitoring with regulated identity infrastructure, enabling onboarding that satisfies both blockchain security and KYC obligations.
Implementation Considerations for Web3 Teams
Setting up on-chain monitoring requires more than deploying a tool. Here are the key considerations.
Define Your Threat Model First
Every protocol has a unique risk profile. A lending protocol faces different threats than an NFT marketplace. Start with a threat model that maps your contract functions, economic attack surfaces, and known vulnerability classes.
Set Baselines Before Going Live
Anomaly detection requires a baseline. Spend time profiling normal behaviour before activating high-sensitivity alerts. Rushed deployments lead to alert fatigue from false positives.
Integrate with Your Incident Response Plan
Monitoring without a response plan creates awareness without action. Define who gets alerted, what they do, how the contract is paused if needed, and who communicates externally.
Audit First, Monitor Continuously
Monitoring is not a substitute for a smart contract audit. Both are necessary. Solidity Shield from SecureDApp covers the pre-deployment layer. SecureWatch covers runtime. Together they close the security gap across the full deployment lifecycle.
The Cost of Not Monitoring
The question is not whether real-time blockchain threat monitoring is worth the investment.The question is whether the cost of a single exploit is worth avoiding. The Euler Finance hack in 2023 resulted in a USD 197 million loss. Post-incident analysis showed that anomalous donation function behaviour was observable on-chain before the attack completed.
The Mango Markets exploit in 2022 involved oracle price manipulation. The manipulation was visible in real time. No automated monitoring was in place to act on it. These are not edge cases. They are the norm for protocols that treat security as a pre-deployment checklist rather than an operational discipline.
Conclusion
The field is moving fast. Several developments will define monitoring architecture through 2027 and beyond. Cross-chain monitoring maturity: As bridging activity grows, threats increasingly span multiple chains. Monitoring must follow assets across ecosystems. AI-driven threat prediction: Beyond anomaly detection, models trained on historical exploit data will begin anticipating attack setups before they execute.
Zero-knowledge proof integration: Monitoring systems will increasingly operate on encrypted state data, enabling surveillance without exposing sensitive protocol information. Regulatory mandates: Formal requirements for documented real-time monitoring controls will emerge from global VASP regulations. Early deployment creates first-mover compliance advantage. Integration with identity infrastructure: Linking on-chain monitoring to enterprise identity systems like SecureX-DID will allow threat attribution at a human identity level, not just a wallet level.
Frequently Asked Questions on Real Time Blockchain Threat Monitoring
It is a security layer that analyses blockchain transactions, smart contract events, and wallet behaviour as they happen. It detects threats like flash loan attacks, reentrancy exploits, and oracle manipulation in real time, and can trigger automated containment responses.
A smart contract audit is a pre-deployment code review. It identifies vulnerabilities in the contract logic before it goes live. On-chain monitoring is a runtime layer. It watches the deployed contract in operation, flagging threats that emerge after deployment or that were not covered by the audit.
No security tool guarantees 100% prevention. However, real-time monitoring dramatically reduces the window in which an attack can operate undetected. Faster detection means faster containment, which limits the damage from any exploit.
Most enterprise-grade monitoring solutions support EVM-compatible chains including Ethereum, BNB Chain, Polygon, Avalanche, and Arbitrum. Multi-chain and cross-chain coverage is increasingly standard as asset bridging grows.
SecureWatch is designed for DevSecOps integration. It connects to existing alert pipelines, incident response tools, and protocol governance systems. It also works alongside SecureTrace for post-incident forensic investigation and with Solidity Shield for pre-deployment audit coverage.



