Introduction: Why Real-Time Blockchain Threat Monitoring Matters
Blockchain is transparent by design. Every transaction is on-chain. Everyone can see it. But here is the uncomfortable truth most projects and users are watching nothing. They only find out about a hack, a rug pull, or a suspicious drain after the money is gone. By then, it is too late. Real-time blockchain threat monitoring is not a luxury anymore. It is survival infrastructure for anyone serious about Web3 security. Whether you are a DeFi protocol, an NFT project, a DAO treasury manager, or an individual investor knowing what is happening on-chain before damage is done can save everything.
This tutorial walks you through exactly how to set it up. Step by step. No vague advice. No fluff. Let’s get into it
What Is Real-Time Blockchain Transaction Monitoring?
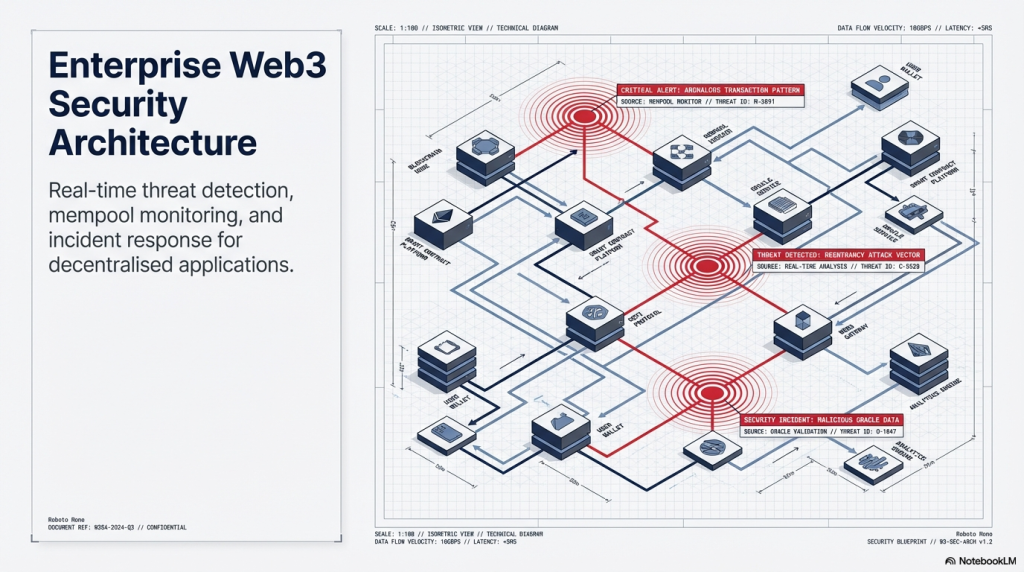
Real-time blockchain transaction monitoring means watching on-chain activity as it happens. Think of it like CCTV for your smart contracts and wallets. Instead of reviewing footage after a break-in, you see suspicious movement the moment it starts. At its core, it involves tracking specific wallet addresses, contract interactions, token transfers, and function calls on the blockchain and triggering alerts when anything anomalous shows up. For security teams and protocol owners, this translates into earlier threat detection, faster incident response, and significantly reduced financial damage.
Step 1: Understand What You Need to Monitor
Before you set up any tool, you must define what matters to you. Monitoring everything is noise. Monitoring the right things is signal. Here are the core categories you should decide on:

Smart Contract Activity Any call to your deployed contracts especially high-value functions like withdraw, mint, upgrade, or any admin-controlled operations.
Wallet Addresses Treasury wallets, deployer wallets, multi-sig addresses, and known team wallets.
Token Transfers Unusual outflows of your project token, large unexpected mints, or sudden burns.
Gas Anomalies Sudden spikes in gas usage on your contract can signal an ongoing attack like a reentrancy or flash loan exploit.
Protocol-Specific Events Any custom event emitted from your contracts that signals a critical state change like a governance proposal passing or a price oracle update.
Write this list down. It becomes the foundation of your monitoring logic.
Step 2: Choose Your Blockchain Monitoring Approach
There are two broad approaches to real-time blockchain monitoring.
Option A: DIY with RPC Nodes and Scripts You subscribe to a full or archive node (via Alchemy, Infura, QuickNode, or your own), write custom scripts to listen to events, and pipe alerts to Telegram, Slack, or PagerDuty. This gives you maximum control but requires technical depth. You will be writing and maintaining code.
Option B: Purpose-Built Security Platforms Platforms like SecuredApp offer out-of-the-box real-time monitoring built specifically for Web3 threat detection. They come with pre-configured threat signatures, anomaly detection, and alert systems so you spend time acting on threats, not building infrastructure to find them.
For most teams, Option B is the smarter starting point. You can layer in custom scripts later for edge cases.
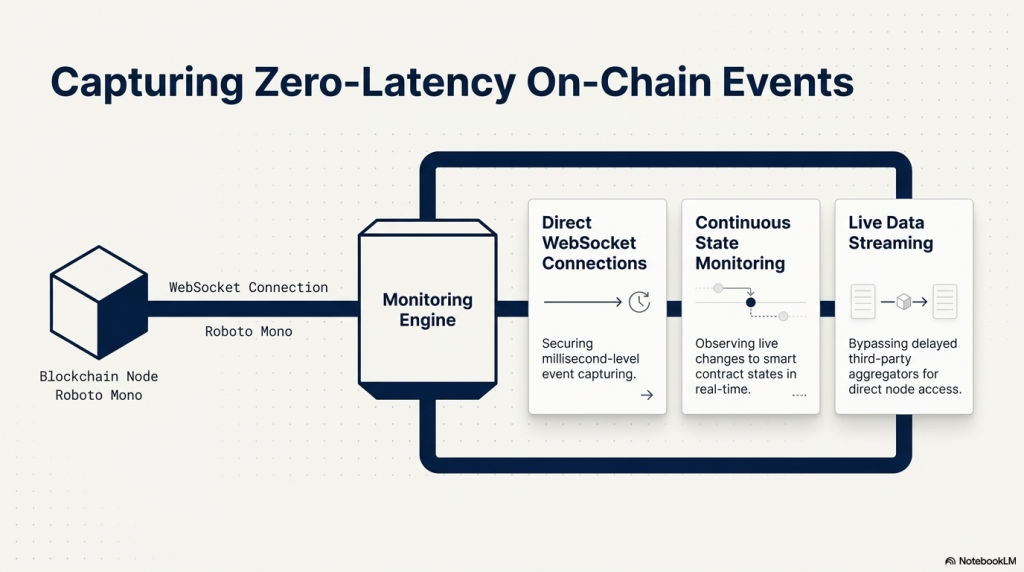
Step 3: Set Up Node Access for Real-Time Data
If you are going the DIY route or building custom layers on top of a platform, you need reliable node access first.
Here is how to do it:
3a. Sign up with a node provider Alchemy and QuickNode both offer free tiers. For production monitoring, pay for a dedicated endpoint. Shared endpoints have rate limits that break real-time pipelines.
3b. Enable WebSocket connections REST calls are for pulling data on demand. For real-time monitoring, you need WebSockets. They push data to you as it happens.
Here is a simple Node.js example using ethers.js:
const { ethers } = require("ethers");
const provider = new ethers.WebSocketProvider("wss://eth-mainnet.g.alchemy.com/v2/YOUR_KEY");
provider.on("block", async (blockNumber) => {
const block = await provider.getBlock(blockNumber, true);
console.log("New block:", blockNumber);
// Process transactions here
});
3c. Filter for relevant transactions Listening to every transaction on Ethereum is impractical at scale. Use event filters tied to your contract addresses.
const filter = {
address: "0xYOUR_CONTRACT_ADDRESS",
topics: [ethers.id("Transfer(address,address,uint256)")]
};
provider.on(filter, (log) => {
console.log("Transfer event detected:", log);
});
This way, you only receive data that is relevant to you.
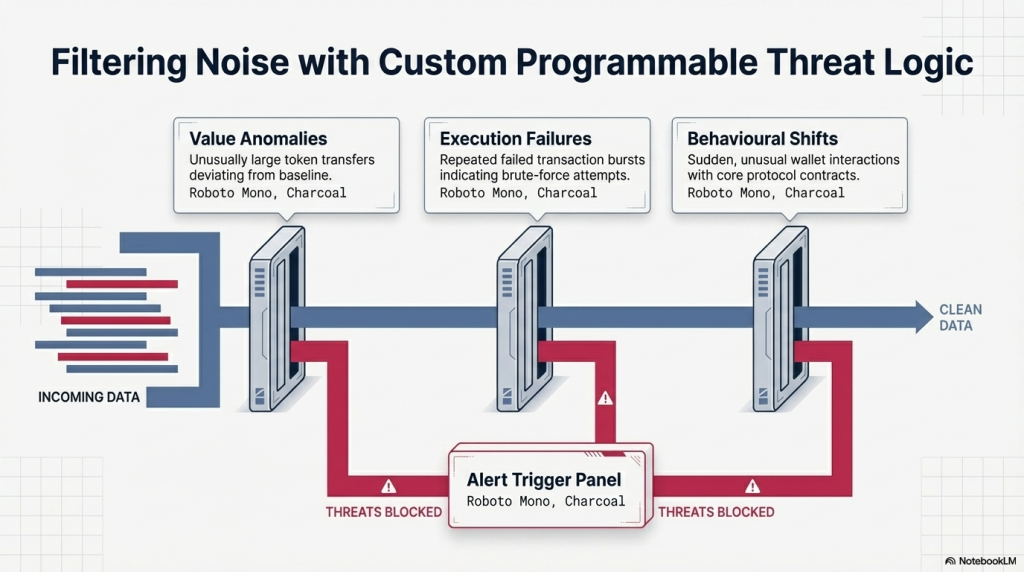
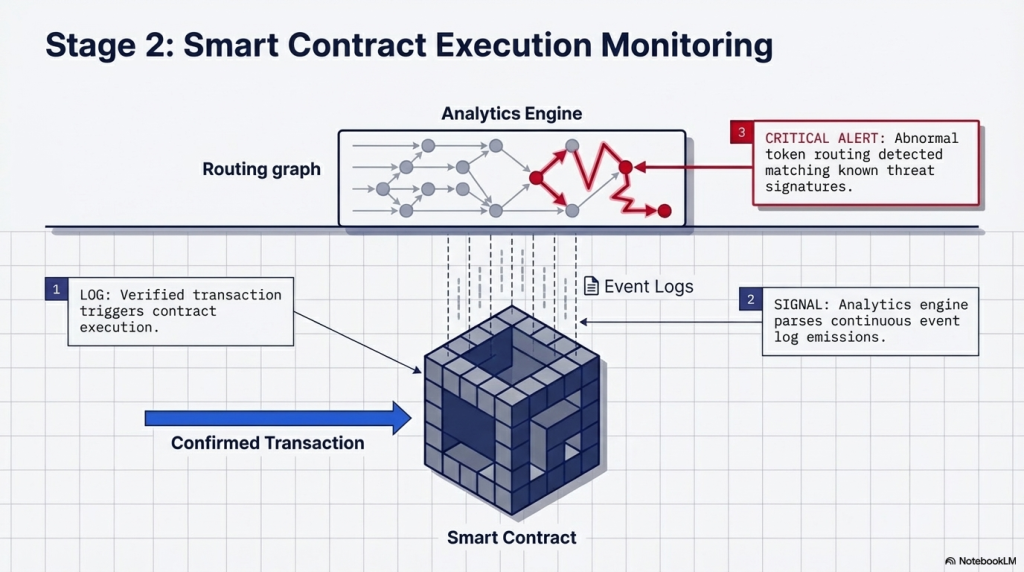
Step 4: Define Your Threat Detection Rules
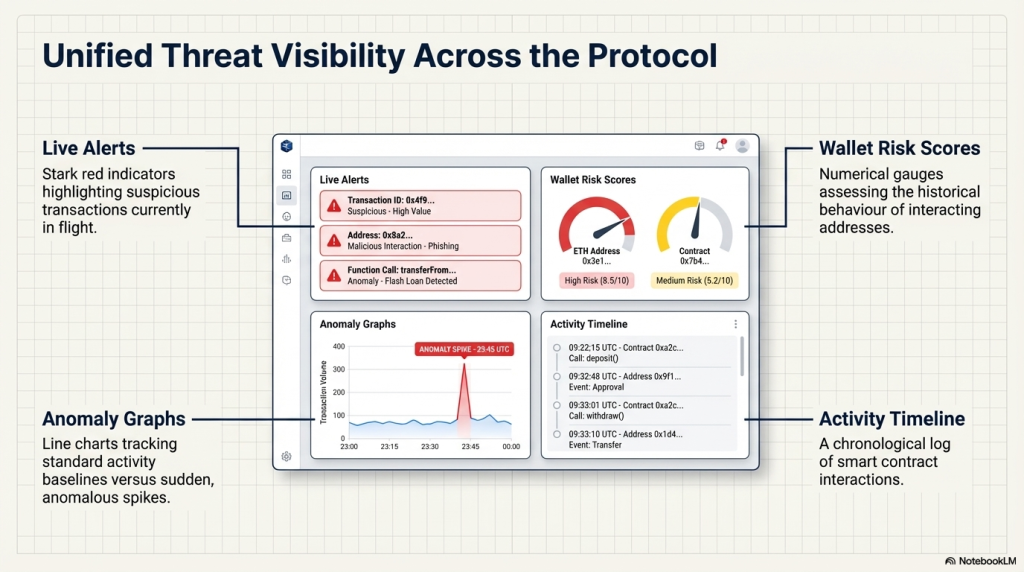
Raw data is not a threat alert. You need rules to turn transaction data into actionable signals. Think of rules as: “If X happens, notify me.” Here are the most important rule types to start with:
Large Value Transfers Any single outflow above a threshold you define say, more than 1 ETH or 10,000 USDC from a monitored wallet.
Admin Function Calls Any invocation of admin-only functions on your contracts. These should almost never happen unexpectedly.
Reentrancy Patterns Multiple calls to the same function within one transaction. This is the signature of a reentrancy attack.
Flash Loan Interactions Transactions that borrow massive amounts via Aave, dYdX, or similar and interact with your contracts in the same block.
Unverified Contract Interactions Your contract being called by an unverified or newly deployed contract with no prior transaction history.
Ownership Transfers Any call to transferOwnership on your contracts. This is a critical signal and almost always warrants immediate review.
If you are using SecuredApp’s smart contract monitoring suite, many of these rules come pre-built. You can also write custom detection logic through their rule engine tailoring alerts to your exact protocol architecture.
Step 5: Configure Real-Time Alert Channels
Detection without notification is useless. You need alerts going to the right people at the right time. Set up multiple channels:
Telegram Fast, reliable, and accessible on mobile. Use a bot that posts to a private security channel. Perfect for medium-priority alerts.
PagerDuty or OpsGenie For critical alerts that require immediate human response. These services can escalate via phone call if no one acknowledges an alert.
Slack Good for team-wide visibility and discussion. Less urgent than PagerDuty but better for collaboration context.
Email Useful for summaries and lower-priority notifications. Not suitable for real-time critical alerts.
For critical infrastructure, you want alerts in at least two channels. A Telegram message and a PagerDuty escalation is a solid baseline.
Make sure each alert includes: the transaction hash, the wallet or contract involved, the type of threat triggered, and a direct link to the explorer (Etherscan, BscScan, etc.).
Step 6: Integrate with a Blockchain Explorer API
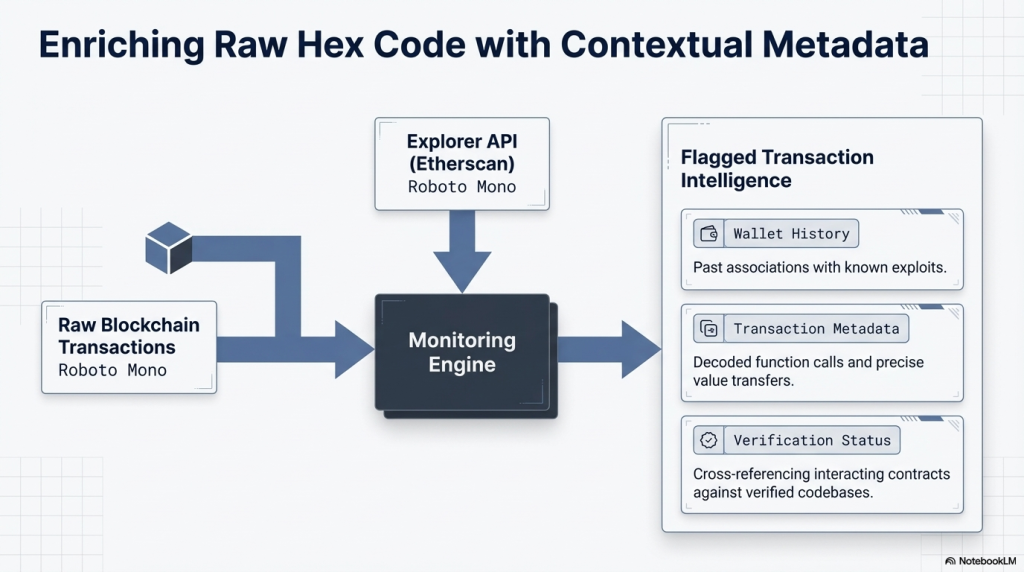
To enrich your alerts with context, integrate with block explorer APIs. Etherscan, for instance, lets you pull detailed transaction data programmatically:
curl "https://api.etherscan.io/api?module=account&action=txlist&address=0xYOUR_ADDRESS&startblock=0&endblock=99999999&sort=desc&apikey=YOUR_API_KEY"
This gives you the full transaction list for any address. You can use this to:
- Check if a suspicious caller has a history of malicious activity
- Verify if an address is flagged in your threat intel database
- Pull the bytecode of an unknown contract and flag it for manual review
On platforms like SecuredApp, this enrichment is built in. Each alert is automatically cross-referenced with known threat databases and flagged addresses.
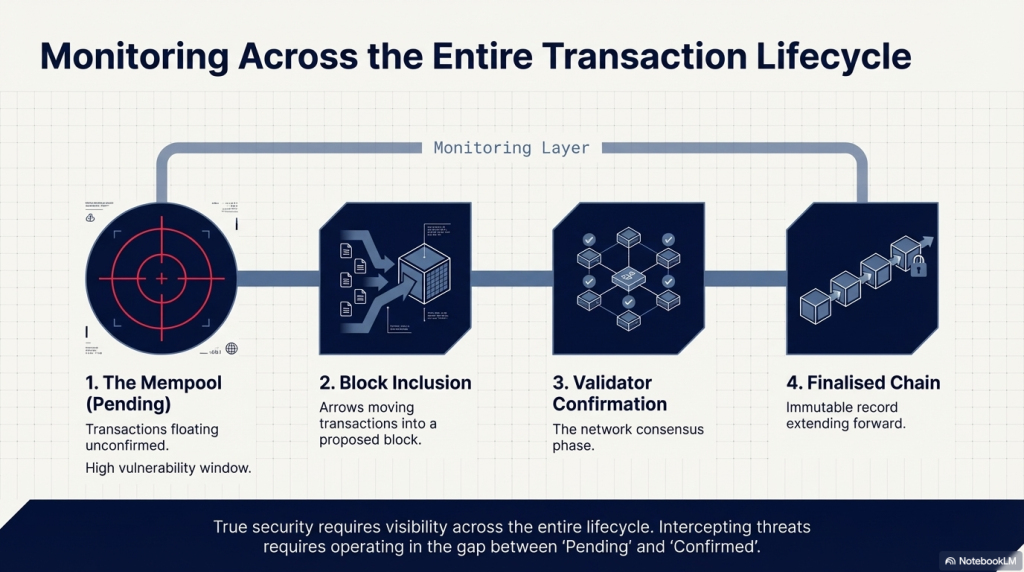
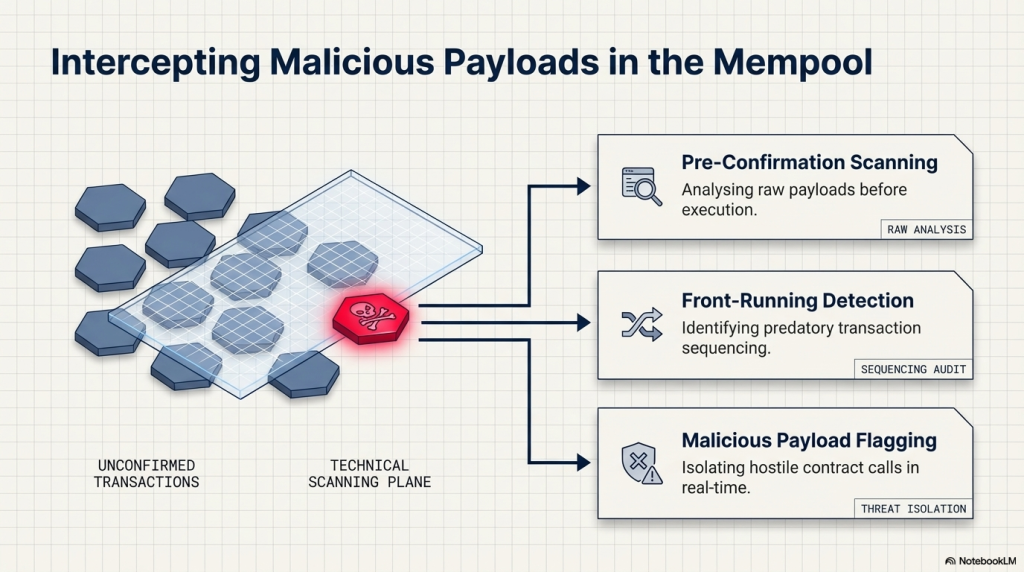
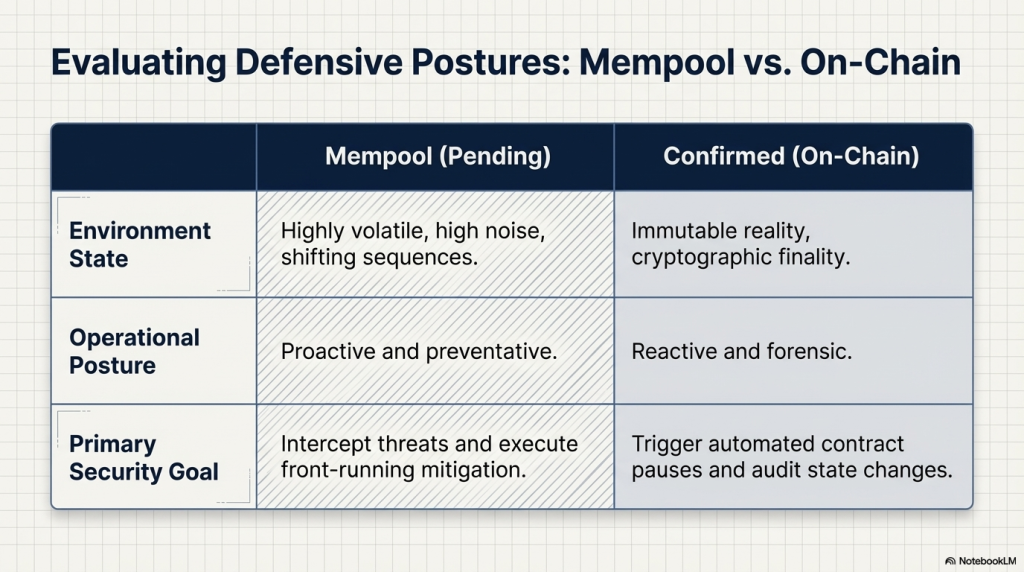
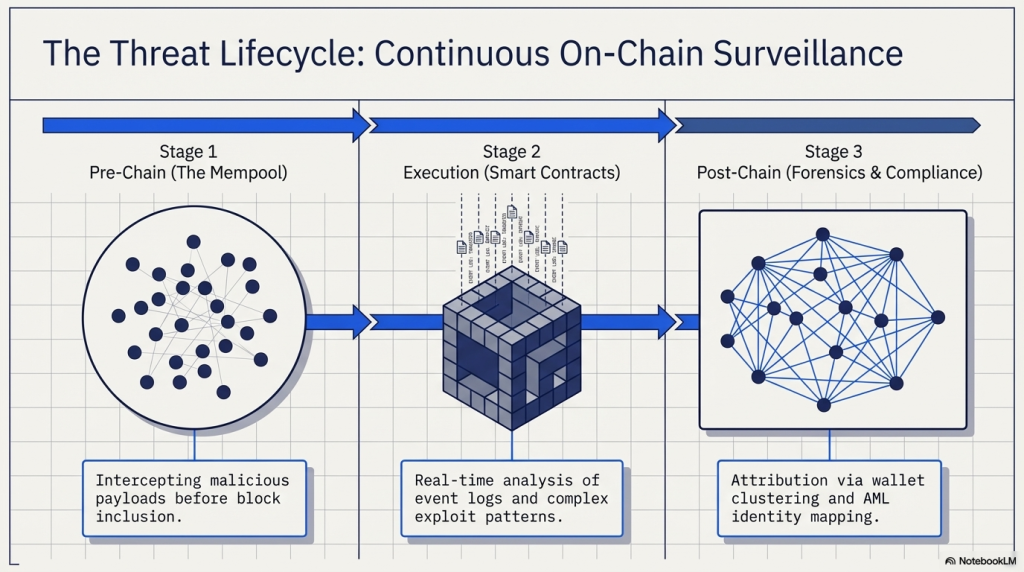
Step 7: Set Up Continuous Mempool Monitoring
Most monitoring systems catch threats after transactions are confirmed. But the real edge comes from monitoring the mempool the pool of pending, unconfirmed transactions.
Mempool monitoring lets you detect threats before they land on-chain.
This is especially valuable for:
- Detecting sandwich attack setups on AMMs
- Seeing if an attacker is probing your contract with test transactions
- Spotting large pending withdrawals from treasury wallets in advance
Here is a basic mempool listener using ethers.js:
provider.on("pending", async (txHash) => {
const tx = await provider.getTransaction(txHash);
if (tx && tx.to === "0xYOUR_CONTRACT") {
console.log("Pending tx targeting your contract:", tx);
// Run your threat logic here
}
});
Mempool monitoring requires a paid node plan on most providers. The latency advantage it offers is well worth the cost for high-value protocols.
Step 8: Test Your Monitoring System
Before you go live, you must validate that everything works. Do not assume it does. Test it deliberately.
Here is a testing checklist:
- Send a small transfer to a monitored wallet and verify the alert fires
- Call a monitored function on a testnet deployment and confirm the notification lands
- Simulate a large-value outflow above your threshold and check that escalation works
- Intentionally trigger a known rule and time how long it takes from on-chain confirmation to alert arrival
- Test your alert channels can all team members receive and acknowledge alerts?
Most teams skip this step and discover their monitoring was broken only when they actually need it. Run drills. Treat it like a fire drill regularly and seriously.
Step 9: Build a Response Playbook
Monitoring tells you something is wrong. Your response playbook tells your team exactly what to do next.
Without a playbook, even the best alert is just an anxiety-inducing notification.
Your playbook should cover, at minimum:
For a Suspected Exploit in Progress:
- Who gets notified first (on-call security lead)
- Whether to pause the contract (if that function exists)
- How to assess the scope of damage in real time
- When and how to communicate with users publicly
- Who has the authority to initiate emergency actions
For a Suspicious Admin Call:
- Verify the transaction initiator against known signer lists
- If unrecognised, escalate immediately
- Review recent key management activity
For Unusual Token Outflows:
- Check if it matches any scheduled activity or known operations
- If not, freeze further actions and investigate
SecureDApp’s incident response tools integrate directly with monitoring alerts to help teams coordinate response workflows. Each alert can be linked to a specific response track, so team members know exactly what to do from the moment a notification arrives.
Step 10: Maintain and Evolve Your Monitoring Setup
Blockchain protocols evolve. Threat patterns evolve. Your monitoring should too.
Schedule a monthly review of:
- Active monitoring rules — are they still relevant to current contract logic?
- Threshold values — have transaction sizes or norms changed since you last reviewed?
- Alert channels — are the right people still in the right notification groups?
- New threat patterns — have there been recent exploits in your protocol category you should add detection for?
The DeFi landscape changes fast. A monitoring setup that was solid six months ago may have gaps today. Treat maintenance as a non-negotiable part of your security programme.
How SecureDApp Strengthens Real-Time Blockchain Threat Monitoring
Building custom monitoring infrastructure from scratch is possible. But for most Web3 teams, the cost in time, engineering resources, and ongoing maintenance is significant.
SecureDApp offers a purpose-built platform for blockchain security monitoring designed specifically for the threats Web3 teams actually face.
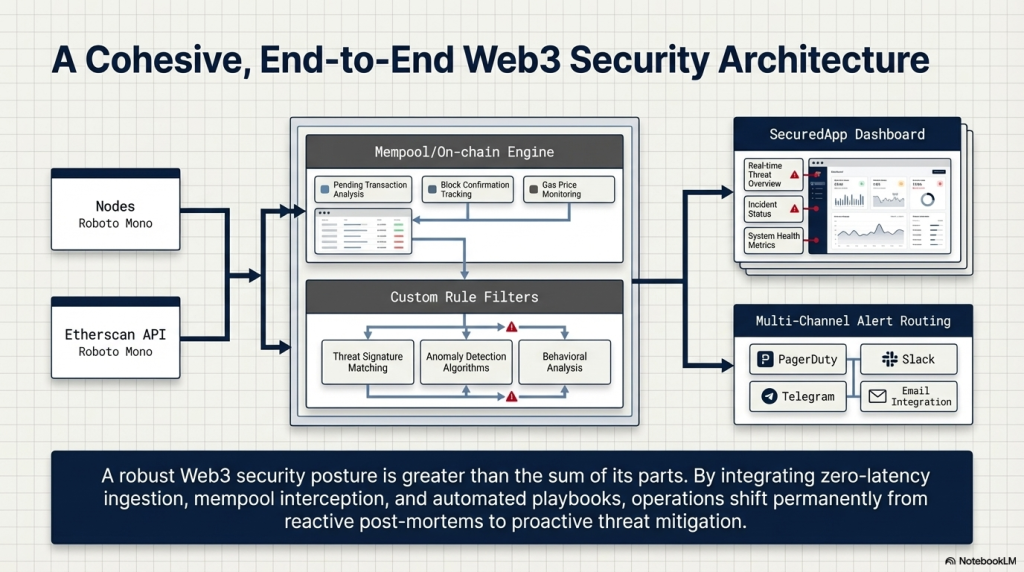
Key capabilities include:
Smart Contract Monitoring Continuous on-chain surveillance of your deployed contracts with pre-built detection for common attack patterns including reentrancy, flash loan abuse, ownership hijacking, and more.
Wallet and Treasury Surveillance Real-time tracking of treasury wallets, deployer addresses, and multi-sig accounts with instant alerts on unusual activity.
Threat Intelligence Integration Alerts are automatically enriched with context from threat databases so you know not just that something happened, but whether it is linked to known malicious actors.
Incident Response Coordination Built-in workflows that connect alerts to response playbooks, so your team moves from detection to action without fumbling.
SecuredApp is trusted by Web3 protocols across DeFi, NFTs, and infrastructure layers. If you want real-time blockchain threat monitoring without building it all yourself, SecuredApp is worth evaluating as your security layer.
Common Mistakes to Avoid
Monitoring too broadly without prioritising Watching everything creates alert fatigue. Define what actually matters first.
Using shared RPC endpoints for production monitoring Rate limits and latency on shared endpoints will cause you to miss events. Use dedicated endpoints.
Not testing alerts before you need them Test regularly. Do not discover your alerts are broken during an actual incident.
Relying on a single alert channel Channels fail. Diversify across at least two notification systems for critical alerts.
Skipping mempool monitoring for high-value protocols On-chain monitoring alone catches threats after they land. Mempool monitoring gives you advance warning. For any protocol holding significant value, this is not optional.
Having no response playbook Detection without a defined response plan is incomplete. Write the playbook before you need it.
Summary
Real-time blockchain threat monitoring is one of the highest-leverage investments you can make in Web3 security.
Here is the full step-by-step recap:
- Define exactly what you need to monitor contracts, wallets, events, tokens
- Choose your approach DIY scripting or a purpose-built platform like SecuredApp
- Set up reliable WebSocket node access for real-time data feeds
- Define threat detection rules tailored to your specific protocol
- Configure alerts across multiple channels Telegram, PagerDuty, Slack
- Integrate with block explorer APIs to enrich alerts with context
- Add mempool monitoring to catch threats before they confirm
- Test your entire monitoring pipeline thoroughly before going live
- Write a response playbook so your team knows what to do when an alert fires
- Review and update your setup regularly as your protocol and the threat landscape evolve
The difference between a protocol that survives an attack and one that does not often comes down to how fast they detected and responded. Start monitoring today.
Frequently Asked Questions
On-chain monitoring watches transactions after they are confirmed and written to the blockchain. Mempool monitoring watches pending transactions before they are confirmed. Mempool monitoring gives you advance warning sometimes seconds to minutes earlier which can be critical in fast-moving attack scenarios. For high-value protocols, using both together is strongly recommended.
Costs vary widely depending on your approach. A basic DIY setup using a free-tier node provider and open-source scripts can start near zero, though it requires significant engineering time. Dedicated node plans typically start at $50 to $200 per month depending on throughput. Purpose-built security platforms like SecuredApp have paid plans based on protocol size and monitoring scope. The right answer depends on your protocol’s value at risk versus the cost of engineering time to build in-house.
Yes. Most modern monitoring frameworks and security platforms support multi-chain monitoring. If you have contracts or wallets on Ethereum, BSC, Polygon, Arbitrum, and other EVM chains, you can set up unified monitoring across all of them. SecuredApp, for instance, supports monitoring across multiple EVM-compatible chains from a single dashboard. Non-EVM chains like Solana require separate tooling or a platform that explicitly supports them.
With a well-configured setup using dedicated WebSocket nodes, alerts can arrive within 5 to 15 seconds of a transaction being confirmed on-chain. Mempool monitoring can alert you even before confirmation. Alert delivery speed also depends on your notification channel Telegram and PagerDuty deliver within seconds, while email may have delays. Always test and measure your end-to-end alert latency so you know exactly what to expect.
The single most common mistake is not testing the monitoring pipeline before they actually need it. Teams set up alerts, assume they are working, and only discover the configuration was broken when a real incident occurs. The second most common mistake is having no response playbook detecting an attack means nothing if your team does not know what actions to take in the first 15 minutes. Both problems are easy to fix: run regular alert drills and write your playbook in advance



