In 2023, over $1.8 billion was drained from DeFi protocols through on-chain exploits. Most of those attacks were not silent. They left signals, moved through mempools. And also triggered unusual state changes. The problem was not a lack of data. The problem was the absence of real-time blockchain threat monitoring.
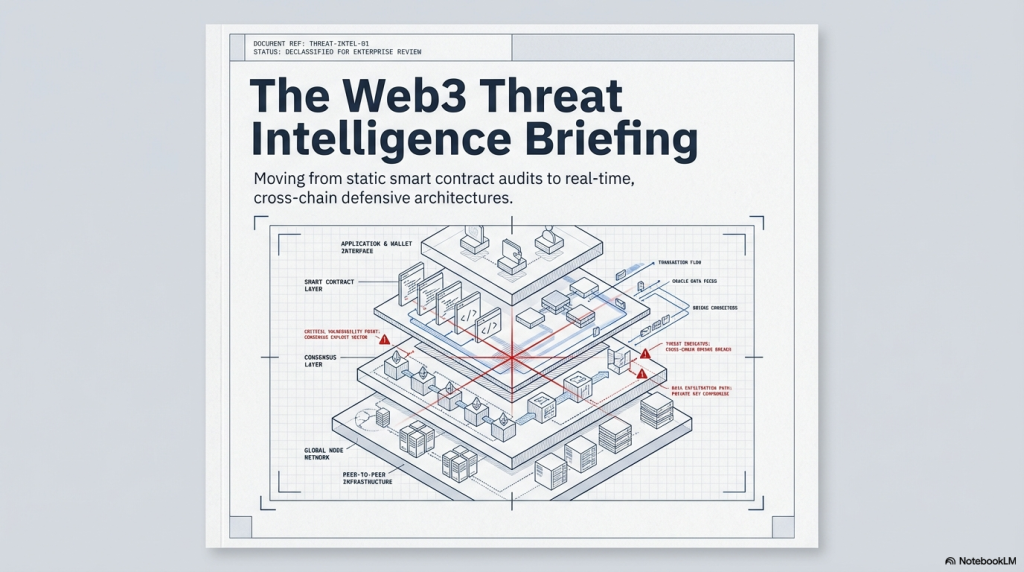
Flash loan attacks, reentrancy exploits, and oracle manipulation do not emerge without warning. They follow detectable patterns across transaction lifecycles. Yet most DeFi protocols still rely on static smart contract audits and post-mortem forensics. That approach is no longer sufficient. This blog breaks down the architecture, signals, and detection strategies required to protect DeFi protocols in live operational environments.
Why DeFi Is a Permanent Target
DeFi runs on open, composable, and permissionless infrastructure. This is its greatest strength. It is also its most exploited characteristic. An attacker can fork a mainnet environment, simulate an exploit locally, refine every step, and execute within hours. Traditional security teams cannot respond at that speed without automated monitoring infrastructure.
Three structural factors make DeFi uniquely vulnerable to persistent attacks.
- All contract logic is public. Attackers study your code before you finalise deployment.
- Transactions are irreversible. Drained funds rarely return without law enforcement involvement.
- Composability creates cascading risk. One vulnerable protocol can endanger every connected one.
This is why real-time blockchain threat monitoring is not a premium feature. It is a baseline security requirement for any DeFi protocol carrying meaningful value.
The DeFi Threat Landscape in 2025: What Has Changed
DeFi exploit mechanics have matured considerably over the last two years. Attackers no longer rely on brute-force approaches. They now combine multiple attack techniques within a single transaction bundle. This makes detection and post-deployment analysis far more complex than it was in 2022.
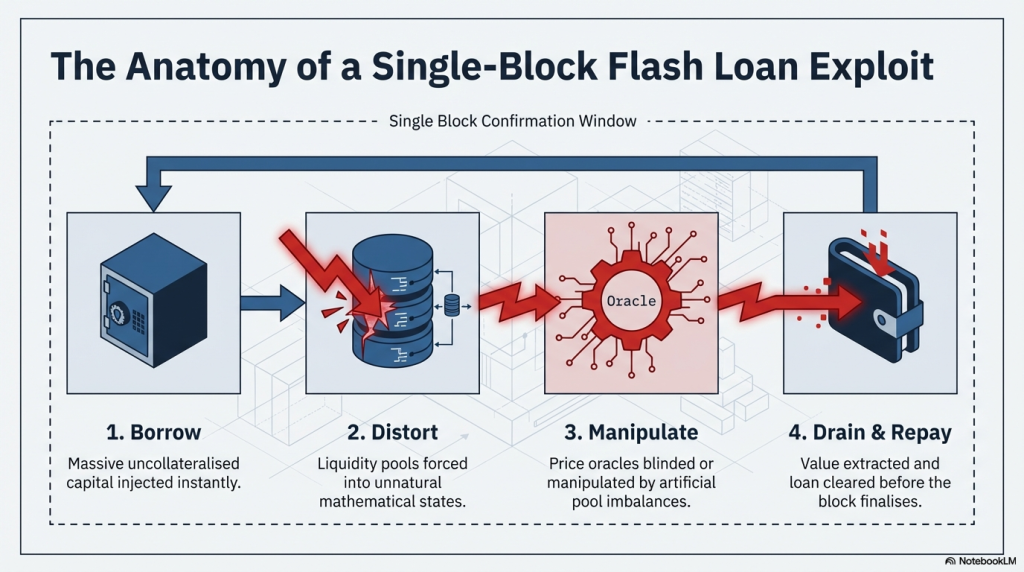
Flash Loan Attack Sequences
Flash loans allow borrowing millions without collateral within one transaction block. When combined with oracle manipulation or liquidity pool imbalances, they become precise extraction instruments. The Euler Finance exploit demonstrated this clearly. It combined flash loans with a donation mechanism flaw to drain over $197 million in a structured multi-step attack. Detecting this requires real-time monitoring of flash loan initiations, cross-pool reserve changes, and balance ratio deviations simultaneously.
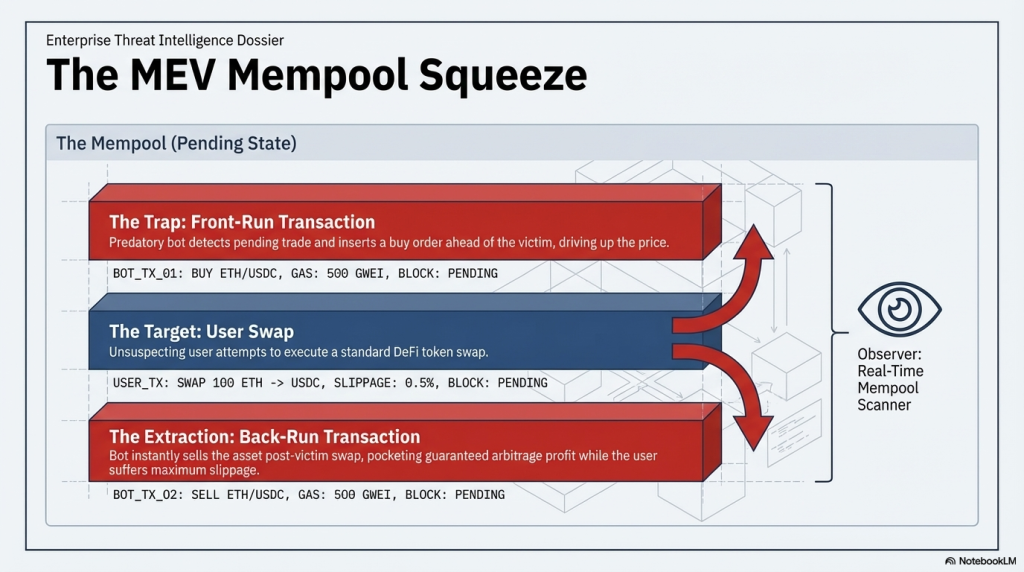
MEV Sandwich Attacks
Maximal Extractable Value attacks target pending transactions sitting in the mempool. A sandwich attack front-runs and back-runs a victim transaction to extract value through slippage. Detection requires mempool-level visibility and wallet clustering intelligence. These link bot activity to specific pending transaction sequences before confirmation.
Reentrancy and Cross-Protocol Callback Exploits
Reentrancy remains one of the most active vulnerabilities in DeFi, despite being one of the oldest known attack vectors. As protocols become more composable, callback sequences grow more complex. New reentrancy paths emerge in cross-protocol interactions that isolated contract reviews cannot anticipate. Runtime monitoring that tracks execution call depth and external call patterns can surface these anomalies before a complete exploit executes.
Governance Attack Vectors
In 2024, governance attacks became more structured and operationally patient. Attackers accumulate governance voting power through token borrowing or flash loans. They pass a malicious proposal and drain a protocol treasury within the execution window. Monitoring abnormal governance token velocity and proposal submission timing is now a core detection requirement for any DAO with significant treasury value.
What Real-Time Blockchain Threat Monitoring Actually Means
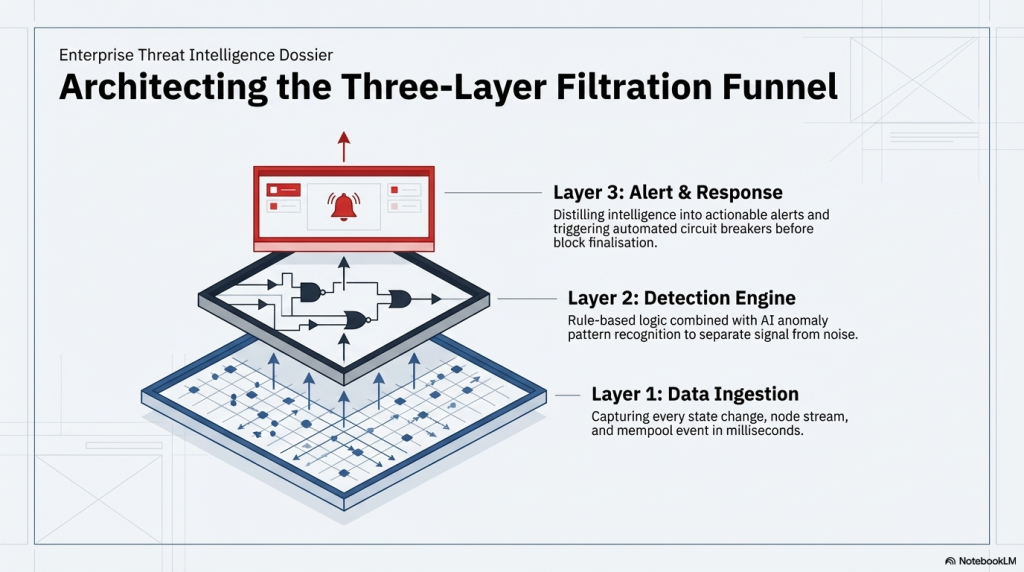
The term is often used loosely. Many vendors describe alert emails arriving after a transaction confirms as monitoring. That is not real-time threat monitoring. That is a post-confirmation notification system. Genuine real-time blockchain threat monitoring operates across three distinct layers.
| Layer | What It Monitors | Detection Speed |
| Mempool Layer | Unconfirmed transactions, front-running bots, suspicious calldata | Pre-confirmation |
| Transaction Layer | Confirmed event logs, state changes, call traces | Block-level |
| Behavioural Layer | Wallet clusters, historical patterns, entity risk scoring | Continuous |
Each layer serves a distinct function. Together, they form a complete detection architecture. Without the mempool layer, you miss pre-confirmation attack setups. Without behavioural analysis, you miss coordinated multi-wallet campaigns unfolding over days.
Key Detection Signals Every DeFi Protocol Must Watch
Effective detection begins with knowing which signals to prioritise. These are the highest-confidence indicators of in-progress or imminent DeFi exploits.
Abnormal Reserve Ratio Changes
Every AMM pool maintains a reserve ratio. Sudden imbalances within a single block indicate flash loan activity or price manipulation. Monitoring reserve deltas above a configured threshold across all liquidity pools surfaces these events immediately, before the attacker can exit the position.
Large Token Movements to New Wallets
Exploit proceeds almost always flow to freshly created wallets or mixer-adjacent addresses. Tracking large outflows from protocol contracts to first-time wallets provides a high-confidence post-extraction signal with significant forensic investigation value.
Cross-Protocol Interaction Spikes
Complex exploits route through multiple protocols within one transaction. Unusual cross-protocol call patterns within one transaction hash are a strong real-time attack indicator.
Governance Proposal with Rapid Vote Accumulation
When a governance proposal receives an unusual concentration of votes within a short time window, this warrants immediate review. Alert thresholds can be configured based on token velocity metrics and expected voting timelines for that specific protocol.
Unexpected Admin Function Calls
In some exploits, attackers trigger admin functions on compromised contracts. Monitoring for unexpected pause, upgrade, or ownership transfer calls is essential for high-value protocol contracts.
The Architecture of Effective On-Chain Threat Detection
Building a real-time threat detection system requires four interconnected technical components working in coordination.
Component 1: Event-Driven Alert Engine
Traditional polling systems check blockchain state at defined intervals. Event-driven systems react the moment a monitored condition triggers. This distinction is operationally significant. A 30-second polling delay is enough time for an attacker to complete a multi-step exploit sequence. Effective alert engines subscribe directly to on-chain events and evaluate alert conditions on each new event emission without waiting for the next polling cycle.
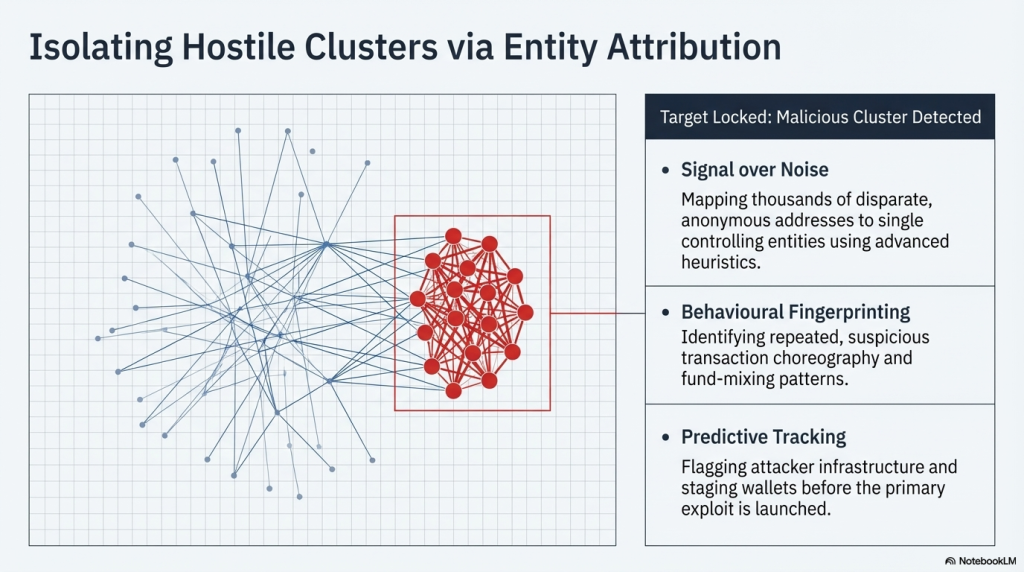
Component 2: Wallet Clustering and Entity Attribution
Individual wallet analysis is insufficient for modern DeFi attacks. Sophisticated attackers use coordinated wallet networks to distribute activity and obscure fund flow. Clustering algorithms group wallets by transaction patterns, funding sources, and historical interaction data. This builds entity-level risk profiles that persist across addresses. When a cluster associated with past exploit activity interacts with your protocol, the alert fires before any damage is done.
Component 3: Policy-Based Automated Containment
Detection without response capability is an incomplete system. Runtime monitoring must include the ability to trigger containment actions automatically. These actions include contract pause mechanisms, transaction blocking at the RPC layer, and emergency governance calls to multisig holders. The policy engine defines threshold conditions and response rules. When conditions are met, containment executes without requiring manual approval cycles.
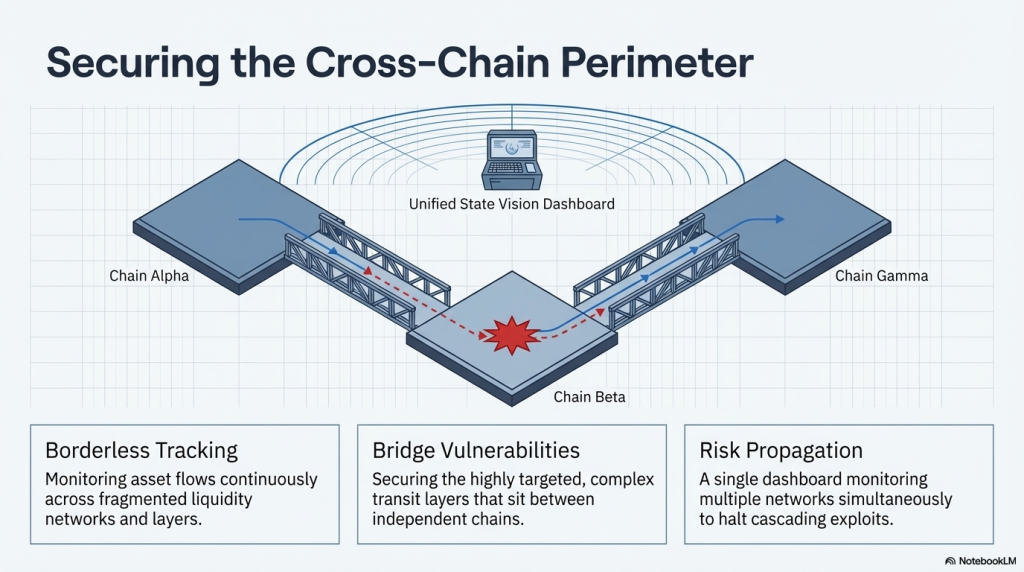
Component 4: Cross-Chain Visibility
DeFi protocols increasingly operate across Ethereum, Arbitrum, Optimism, Base, and other EVM-compatible networks. An exploit can begin on one chain and propagate through bridges to another. Single-chain monitoring creates detection blind spots that attackers actively exploit. Cross-chain threat monitoring aggregates signals across all connected networks into one unified detection layer.
SecureWatch: SecureDApp’s SecureWatch platform is built precisely on this architecture. It delivers event-driven alerting, wallet clustering intelligence, policy-based automated containment, and multi-chain monitoring in a single DevSecOps-integrated stack. DeFi protocols using SecureWatch configure custom security policies that trigger automated responses in real time, without waiting for a human in the loop.
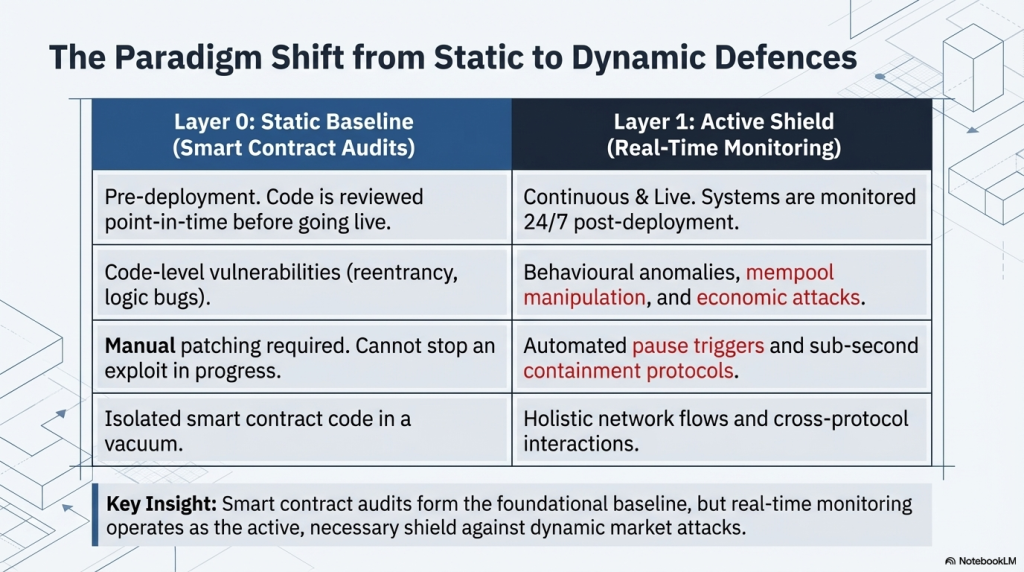
Monitoring vs Auditing: A Critical Distinction
Smart contract audits are essential. They are not sufficient on their own. An audit reviews code at a single point in time before deployment. It cannot detect runtime conditions, novel attack combinations, or vulnerabilities introduced through protocol upgrades after the audit is complete.
| Security Layer | Smart Contract Audit | Real-Time Monitoring |
| When it operates | Pre-deployment, one-time | Post-deployment, continuous |
| What it covers | Code logic, known vulnerability classes | Runtime behaviour, live transactions |
| Attack types detected | Static logic flaws | Flash loans, MEV, governance attacks |
| Response capability | None | Automated containment possible |
| Upgrade coverage | Requires re-audit | Continuous, automatic |
| Compliance support | Partial, point-in-time | Full operational compliance logging |
The answer is not a choice between auditing and monitoring. Both layers must operate together across the full security lifecycle. SecureDApp’s Solidity Shield covers the AI-powered pre-deployment audit layer. SecureWatch covers post-deployment runtime monitoring. Together, they protect a protocol from code review to live environment.
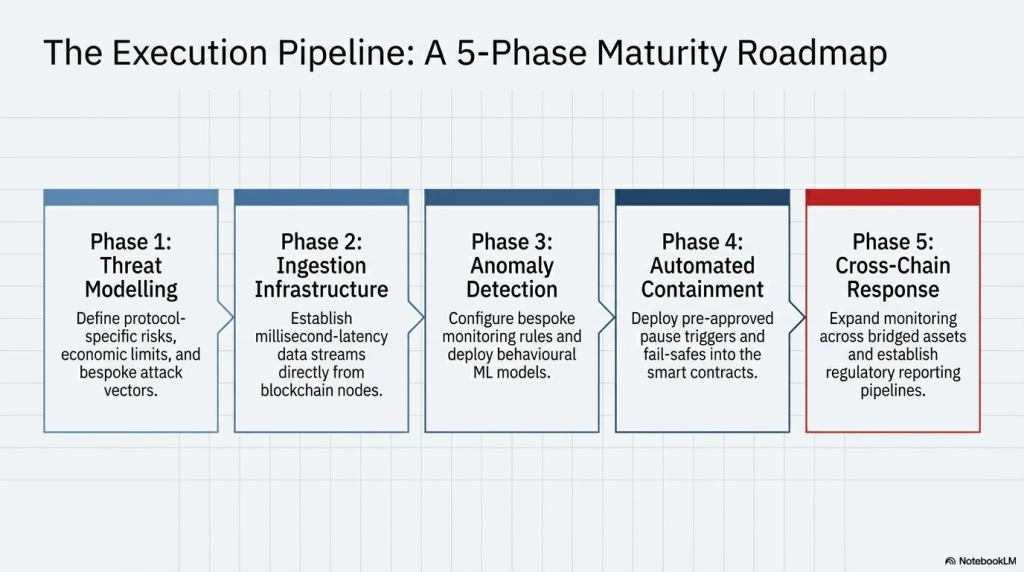
Implementation Roadmap for DeFi Protocols
Rolling out real-time on-chain threat monitoring does not require a complete infrastructure overhaul. A phased approach is practical and delivers security value from day one.
Phase 1: Instrument Core Contracts (Weeks 1 to 2)
Identify the highest-value contracts in your protocol. This includes treasury contracts, liquidity pool managers, and governance contracts. Instrument these with event subscriptions covering reserve changes, large transfers, access control calls, and governance interactions.
Phase 2: Configure Alert Policies (Weeks 2 to 3)
Define threshold conditions for each monitored event type. Set severity tiers covering low, medium, and critical alert classifications. Link critical alerts to automated containment actions, including contract pause, liquidity withdrawal limits, and emergency multisig triggers.
Phase 3: Integrate Wallet Intelligence (Weeks 3 to 4)
Connect wallet clustering and entity attribution to the alert engine. Flag all interactions from wallets linked to historical exploit activity. Establish a blocklist update cadence based on cross-protocol threat intelligence and forensic investigation outputs.
Phase 4: Extend to Cross-Chain Coverage (Month 2)
If your protocol operates on multiple chains, extend monitoring to cover all active chains and bridge contracts. Configure bridge monitoring to detect suspicious cross-chain fund movements at the earliest possible point in the transaction lifecycle.
Phase 5: Ongoing Governance and Policy Review
Conduct monthly policy reviews. Tune alert thresholds based on observed false positive rates and emerging attack patterns. Maintain a documented incident response playbook covering all alert severity tiers. This becomes critical during regulatory audits and post-incident reviews.
Regulatory Implications of Real-Time Threat Monitoring
DeFi protocols are facing increasing regulatory scrutiny across multiple jurisdictions simultaneously. Financial regulators in the EU, India, and the United States are progressively requiring crypto platforms to demonstrate active transaction monitoring and AML-aligned compliance postures. Real-time blockchain threat monitoring directly supports regulatory alignment in several measurable ways.
- Transaction monitoring logs provide audit-ready evidence for compliance review and regulatory reporting.
- Automated flagging of suspicious wallet activity supports FATF travel rule compliance requirements.
- Documented incident response workflows demonstrate operational risk management to regulators and institutional partners.
SecureDApp adds a further compliance dimension through SecureX-DID. As a registered Offline Verification Seeking Entity under UIDAI, SecureDApp can integrate Aadhaar-based offline KYC into enterprise and regulated-sector Web3 onboarding workflows. This is particularly relevant for Indian DeFi deployments and financial institutions entering the Web3 space.
What the Next 24 Months Look Like for DeFi Security
The DeFi attack surface is not shrinking. It is growing more complex and more cross-jurisdictional. Three trends will define the threat landscape through 2026 and into 2027.
AI-Assisted Attack Generation
Attackers are already using large language models to identify exploit paths in public contract code. Defensive AI monitoring will need to match this capability. Detection models trained on attack pattern datasets will become the primary automated defence layer for complex protocol environments.
Cross-Chain Exploit Propagation
As bridge infrastructure matures and liquidity deepens across chains, cross-chain exploits will become more frequent and technically sophisticated. Monitoring systems without native cross-chain visibility will face growing detection gaps that attackers will systematically exploit.
Conclusion
Regulators will begin requiring formal incident disclosure from DeFi protocols within defined time windows after an event occurs. Platforms without real-time monitoring infrastructure will be unable to meet these reporting standards. This creates significant operational and legal exposure for unmonitored protocols. Security platforms that generate legal-grade reports, such as SecureTrace’s blockchain forensic investigation engine, will become a baseline compliance asset rather than a premium add-on.
Frequently Asked Questions on Real Time Blockchain Threat Monitoring
It is the continuous automated surveillance of on-chain activity to detect anomalies and exploit signals as they occur. DeFi protocols need it because static audits cannot detect runtime exploits such as flash loan attacks and reentrancy sequences that execute within live transaction blocks.
An audit reviews code logic before deployment and identifies static vulnerabilities at a point in time. Real-time monitoring operates after deployment and detects threats during live protocol operation. Monitoring can also trigger automated containment responses that audits simply cannot provide.
With mempool-level monitoring and policy-based containment, it is possible to detect attack setups before they complete. This allows automated responses such as contract pause or transaction blocking, moving monitoring from a detection tool to an active prevention layer in many attack scenarios.
Protocols with large TVL, active governance, cross-chain bridges, and complex composable interactions carry the highest risk profile. AMMs, lending protocols, yield aggregators, and decentralised exchanges should treat real-time threat monitoring as a foundational security requirement, not an optional upgrade.
SecureWatch provides event-driven alerting, behavioural anomaly detection, wallet clustering intelligence, and policy-based automated containment in an integrated platform. It is designed for DevSecOps integration, allowing DeFi teams to configure custom security policies and trigger automated responses without manual intervention.



