Introduction: The Question Every Protocol Founder Gets Wrong
Most Web3 teams pick a security approach the same way they pick a cloud provider. They go with what they already know. That instinct is expensive. In 2024 alone, over $2.3 billion was lost to blockchain exploits. A significant portion of those losses hit projects that had done audits. They had off-chain security in place. Yet the funds still walked out the door, one transaction at a time. The real problem is not whether you have security. It is whether your security can see what is happening on-chain, in real time, before the damage compounds.
This blog compares on-chain transaction monitoring against off-chain security measures. We break down the mechanics, the gaps, the use cases, and where each approach breaks down under pressure. By the end, you will know exactly what your protocol needs, and why real-time blockchain threat monitoring is no longer optional for serious Web3 operations. Think of it this way. Off-chain security is the lock on your front door. On-chain monitoring is the CCTV inside the house. You need both. But if someone is already inside moving your valuables, only one of them is useful right now.
What Is On-Chain Transaction Monitoring?
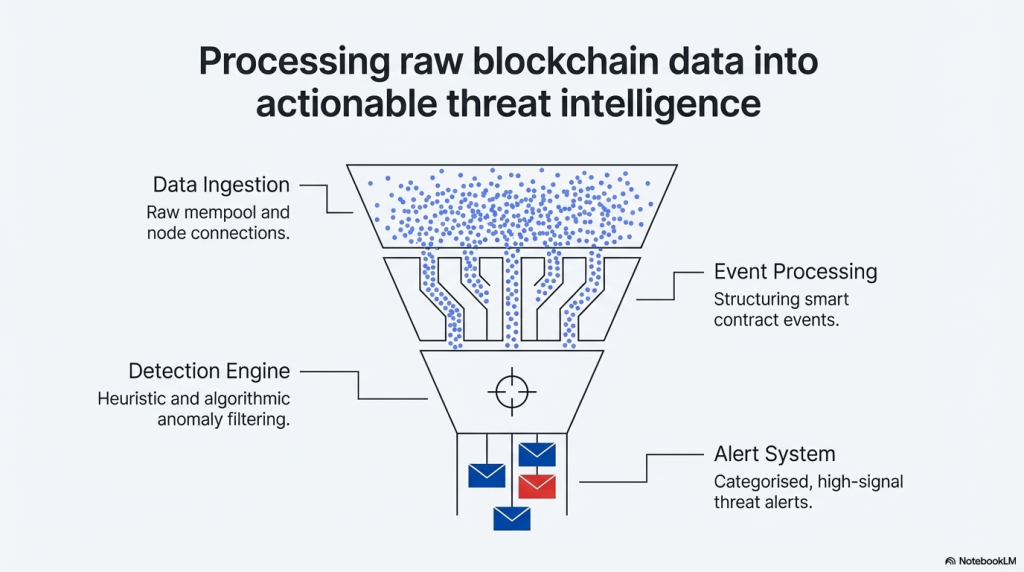
On-chain monitoring means watching the blockchain itself. Every transaction, every state change, every contract interaction is inspected as it happens. It operates at the level of the network. Not logs. Not reports. The actual chain.
What it covers:
- Live transaction flow analysis across wallets and contracts
- Mempool surveillance before transactions are confirmed
- Smart contract event detection and behavioural anomaly flagging
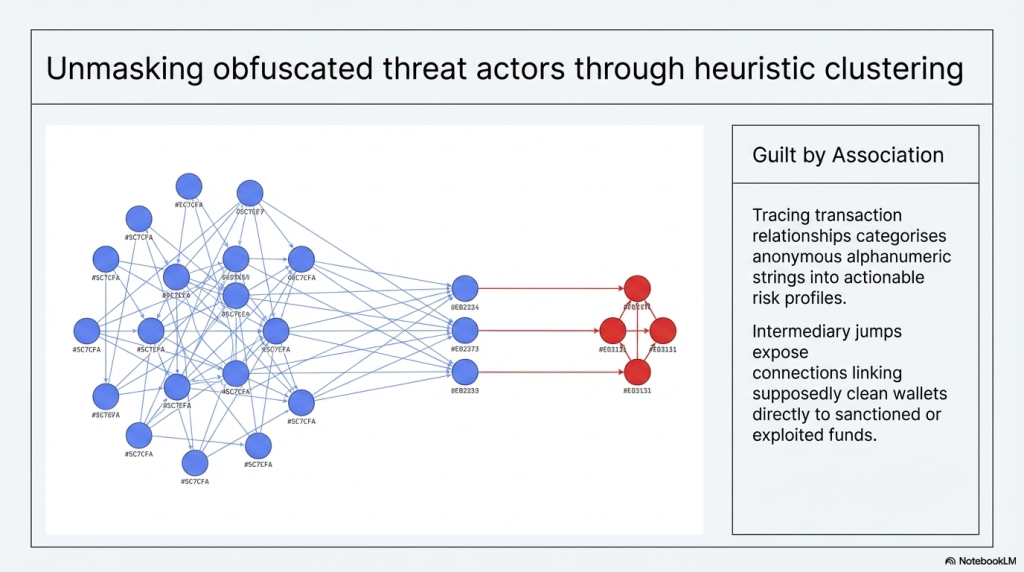
- Wallet clustering to detect coordinated attack patterns
- Flash loan detection and MEV activity tracking
- Automated policy-based responses like contract pause mechanisms
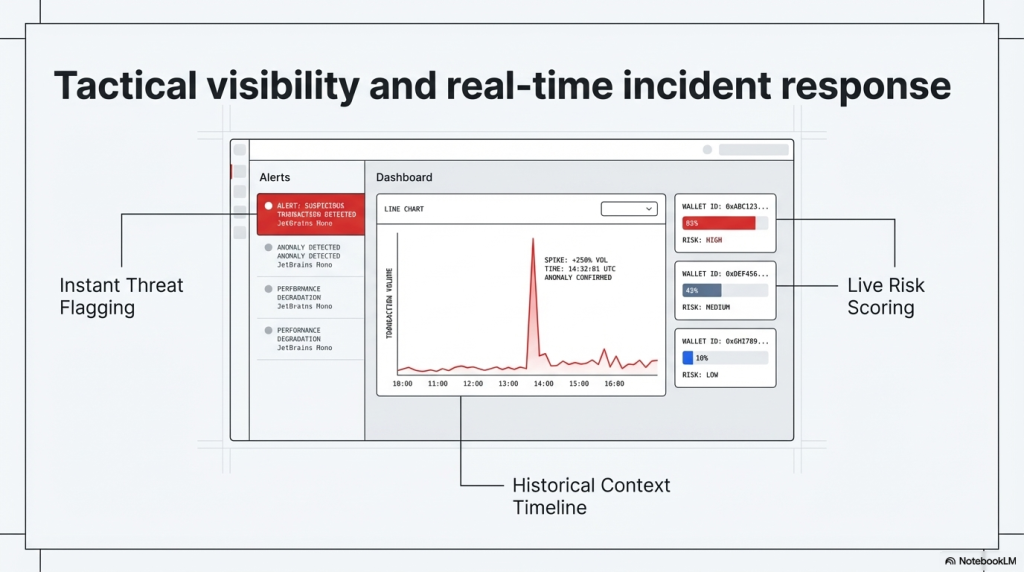
On-chain monitoring does not wait for humans to notice something is wrong. It is event-driven. The moment an anomaly crosses a detection threshold, an alert fires, or an automated response triggers. This is fundamentally different from traditional security. It does not review history. It interprets the present.
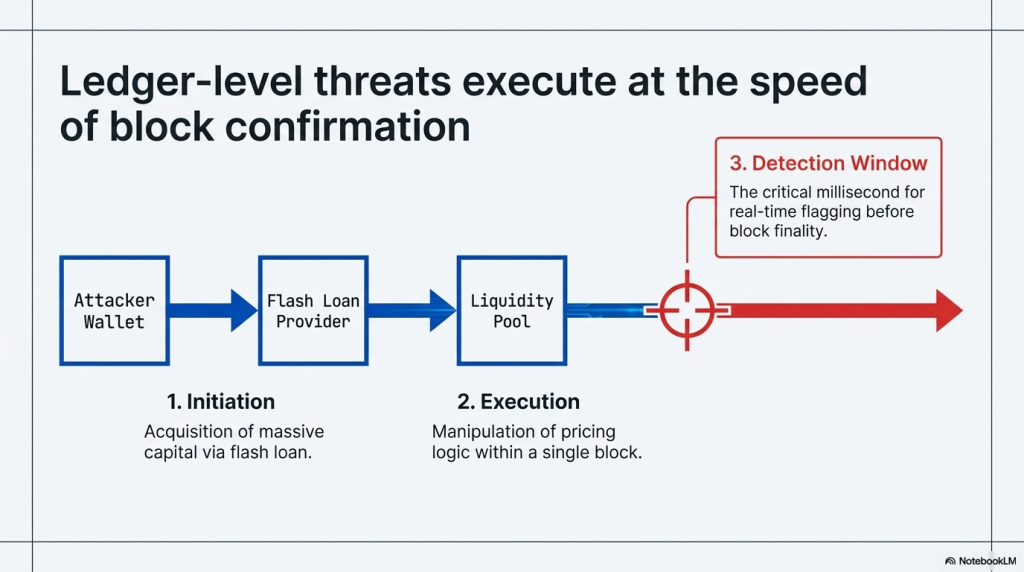
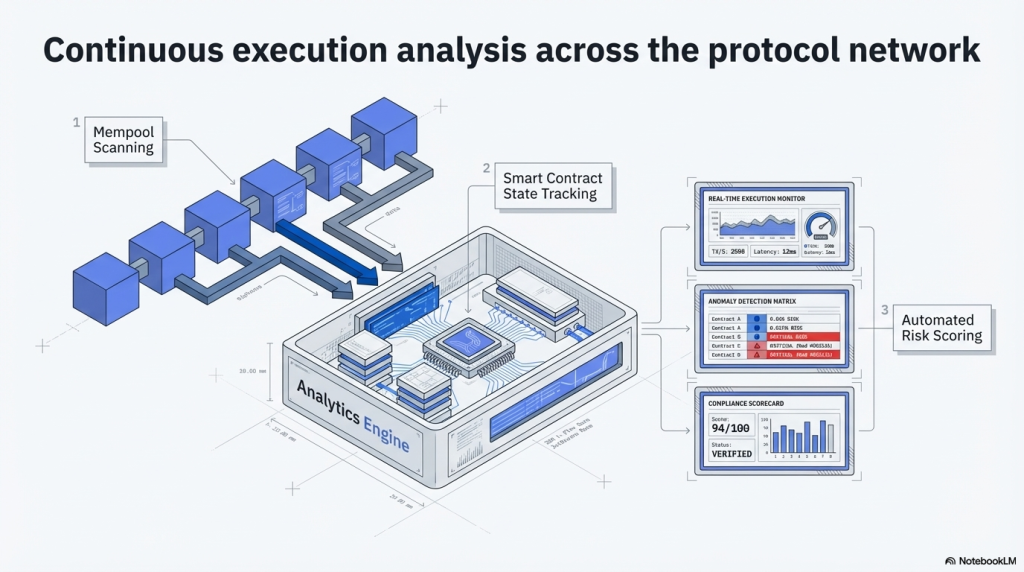
The monitoring layer operates across two time frames. Pre-confirmation monitoring watches the mempool, where transactions sit before miners or validators pick them up. This is where sandwich attacks and front-running bots operate. Post-confirmation monitoring watches finalised state changes, tracking how balances, approvals, and contract storage shift block by block. Together, these two views give a complete picture of what is happening on a live network. No audit can replicate that level of visibility.
What Are Off-Chain Security Measures?
Off-chain security covers everything that happens outside the blockchain itself. It is a broad category. It includes smart contract audits before deployment, penetration testing of frontend interfaces, API security, server-side authentication, private key management, and operational security protocols for teams.
What it covers:
- Pre-deployment code audits (manual and AI-assisted)
- Infrastructure and server security
- Frontend and API vulnerability testing
- Wallet custody and private key management
- Internal access controls and team security hygiene
- Post-incident log review and forensic reporting
Off-chain security is largely preventive and retrospective. It works hard before the protocol launches and after something goes wrong. The gap, as we will explore, is the window in between.
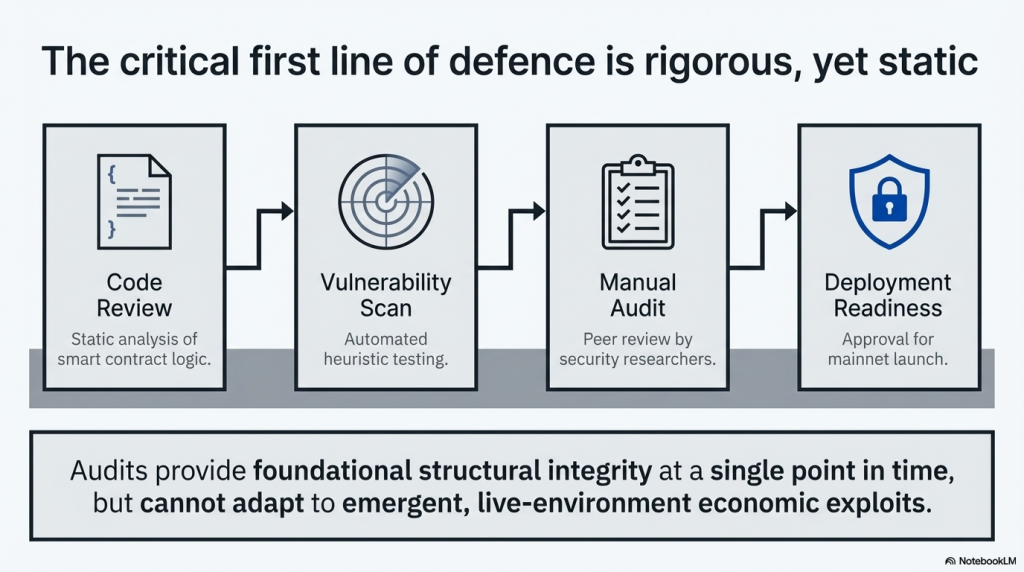
It is worth noting that off-chain security has improved considerably with AI tooling. Automated vulnerability scanners, fuzzing frameworks, and formal verification tools have raised the quality of pre-deployment code review significantly. But every one of those tools is still working on a static snapshot of code, not on live network behaviour. That distinction is everything when the threat is dynamic.
The Core Architectural Difference
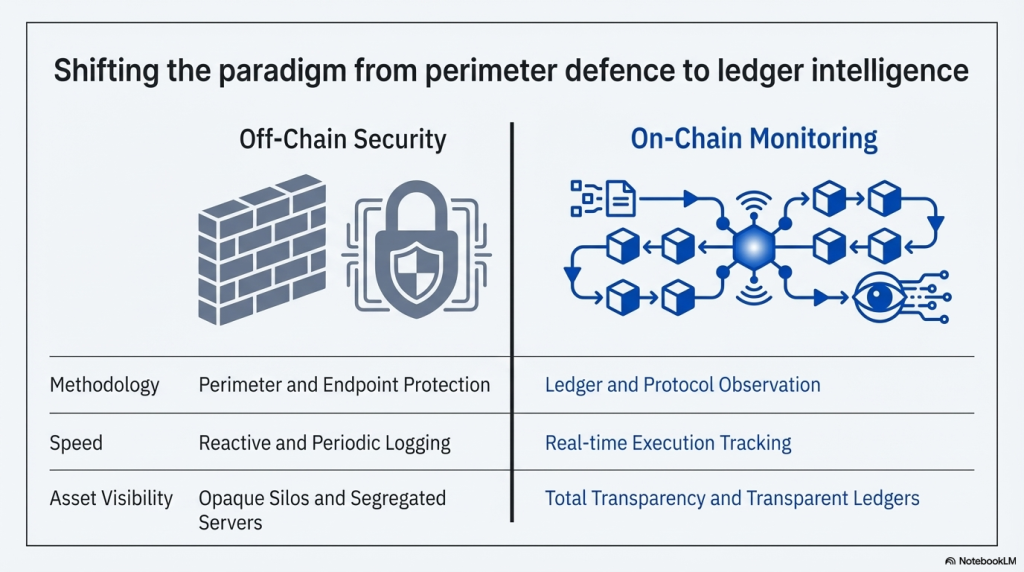
Understanding the gap between these two approaches requires looking at where each operates in the attack timeline.
| Dimension | On-Chain Monitoring | Off-Chain Security |
|---|---|---|
| When it operates | During live transactions | Before deployment / after incidents |
| What it watches | Blockchain state and events | Code, servers, access controls |
| Response type | Real-time automated alerts | Manual review and patching |
| Threat coverage | Runtime exploits, flash loans, MEV | Code vulnerabilities, infrastructure attacks |
| Blind spots | Off-chain infrastructure attacks | Live on-chain exploit execution |
| Speed | Milliseconds to seconds | Hours to days |
| Primary value | Containment and detection | Prevention and investigation |
Neither approach is complete without the other. But the order of priority matters enormously in a blockchain threat context.
Where Off-Chain Security Falls Short
Off-chain security is necessary. But it has structural limitations that on-chain threats exploit directly.
The Post-Deployment Blind Spot
An audit tells you whether the code was safe at the time of review. It cannot account for the state of the blockchain when your contract is live and interacting with hundreds of other protocols. DeFi composability means your audited contract can be used as a weapon. It can be combined with a flash loan from Protocol A and a price oracle from Protocol B to drain your liquidity. No audit catches that combination. It is a runtime attack. It requires runtime defence.
Static Analysis Cannot Model Dynamic Threats
Off-chain tools inspect code in isolation. They do not simulate adversarial transaction sequences against live market conditions. MEV bots do not care about your audit report. Sandwich attackers do not check your penetration test results. These threats are purely on-chain, purely dynamic, and purely invisible to traditional security tooling.
Reactive Response Timeline
When something breaks, off-chain investigation begins after the fact. Logs are pulled. Transactions are traced. A report is written. By then, funds have moved across multiple hops. Mixers have been activated. Recovery becomes forensic archaeology, not active defence.
According to incident data from major blockchain security firms, the average time between exploit initiation and detection using traditional methods ranges from several hours to multiple days. Real-time blockchain threat monitoring compresses that to seconds. The difference in that detection window is often the difference between a recoverable incident and a total loss. DeFi liquidity can be drained in a single block. A flash loan exploit that took months of planning can execute and complete in under 15 seconds. Off-chain review cycles are simply not built to respond at that speed.
Where On-Chain Monitoring Has Limits
On-chain monitoring is not a complete solution either. Understanding its limitations is what makes the comparison honest.
Infrastructure Attacks Stay Invisible
If an attacker compromises your team’s private key, that is an off-chain security failure. The resulting transaction might look entirely legitimate on-chain. Monitoring tools cannot flag a valid signature from a stolen key. This is why off-chain access control and key management remain non-negotiable.
Frontend and API Exploits
Most end users interact with your protocol through a frontend. DNS hijacking, malicious JavaScript injection, or API endpoint spoofing are off-chain attacks. They can drain users before a single on-chain anomaly is detected. The 2022 Badger DAO attack involved a compromised frontend that inserted malicious contract addresses into user transactions. On-chain, each transaction looked signed and approved. The attack was entirely off-chain in origin.
Smart Contract Logic Errors
Some vulnerabilities exist at the logic level and do not produce anomalous on-chain patterns. A flawed access control function might be executed entirely within the expected parameters of normal operation. Only a thorough code audit catches that class of bug. This is the strongest argument for keeping off-chain auditing as a foundation of any security programme. On-chain monitoring assumes the contract is logically sound and watches for abnormal runtime behaviour. It cannot patch a logic flaw that was never anomalous to begin with.
Novel Attack Vector Coverage
On-chain monitoring is only as good as its detection rules and anomaly models. A truly novel attack that has never been seen before may not trigger existing alert thresholds until significant damage has already occurred. This is why continuous rule updates, threat intelligence feeds, and AI model retraining are critical parts of any real-time monitoring programme.
Head-to-Head: Real-Time Blockchain Threat Monitoring vs Traditional Security
Let us make the comparison concrete across the scenarios that matter most.
Flash Loan Attacks
Off-chain security response: An audit might flag reentrancy risks or price oracle dependencies. However, the specific flash loan path used in an attack is often a novel combination of multiple legitimate functions.
On-chain monitoring response: SecureWatch, SecureDApp’s real-time threat detection layer, identifies anomalous loan-borrow-repay sequences within the same block. Policy-based containment can pause contracts automatically before the exploit completes.
Winner: On-chain monitoring, by a significant margin.
Smart Contract Reentrancy Bugs
Off-chain security response: AI-powered audit tools like Solidity Shield scan for reentrancy patterns across 150+ vulnerability classes. This is where pre-deployment auditing genuinely saves protocols.
On-chain monitoring response: Monitoring can detect repeated external calls but may not flag every novel reentrancy path in real time without pre-configured detection rules.
Winner: Off-chain security, specifically AI-assisted audit.
Wallet Compromise
Off-chain security response: Hardware wallets, multi-signature setups, and key rotation policies are the correct defence layer. This is fundamentally an access control problem.
On-chain monitoring response: Unusual transaction volumes or destination addresses from a known wallet can trigger alerts. But monitoring cannot prevent a valid signature from being used.
Winner: Off-chain security, specifically key management. But on-chain monitoring provides early warning signals.
Coordinated Economic Attacks
Off-chain security response: Audits do not model multi-protocol economic strategies. Penetration testing rarely simulates adversarial DeFi composability.
On-chain monitoring response: Wallet clustering intelligence identifies groups of addresses acting in coordination. Cross-contract transaction graph analysis reveals orchestrated attack sequences before they complete.
Winner: On-chain monitoring.
Post-Incident Fund Tracing
Off-chain security response: Traditional forensic tools help piece together server logs and API records. But blockchain data is the primary evidence layer.
On-chain monitoring response: Forensic-grade tools like SecureTrace from SecureDApp perform auto transaction thread tracing, wallet cluster detection, and legal-grade reporting from on-chain data.
Winner: On-chain forensic capability.
The Regulatory Dimension
Compliance requirements are beginning to reflect the reality that on-chain visibility is not optional for regulated entities. Financial regulators across multiple jurisdictions are pushing for transaction monitoring obligations that parallel those existing in traditional banking. The Financial Action Task Force’s Travel Rule applies to virtual asset service providers and requires transaction-level identity and flow tracking. This cannot be satisfied by off-chain logging alone. It requires on-chain transaction monitoring that captures counterparty data at the blockchain level.
SecureDApp operates as a registered Offline Verification Seeking Entity (OVSE) under the Unique Identification Authority of India, governed by the Aadhaar Act of 2016. This positions SecureDApp not only as a technical security provider but as a regulatory-aligned infrastructure partner. For enterprise clients in regulated sectors, this distinction matters when selecting a monitoring provider. As regulatory frameworks around blockchain assets mature, the ability to demonstrate continuous on-chain oversight will become a compliance prerequisite, not just a security best practice.
The Case for a Unified Security Stack
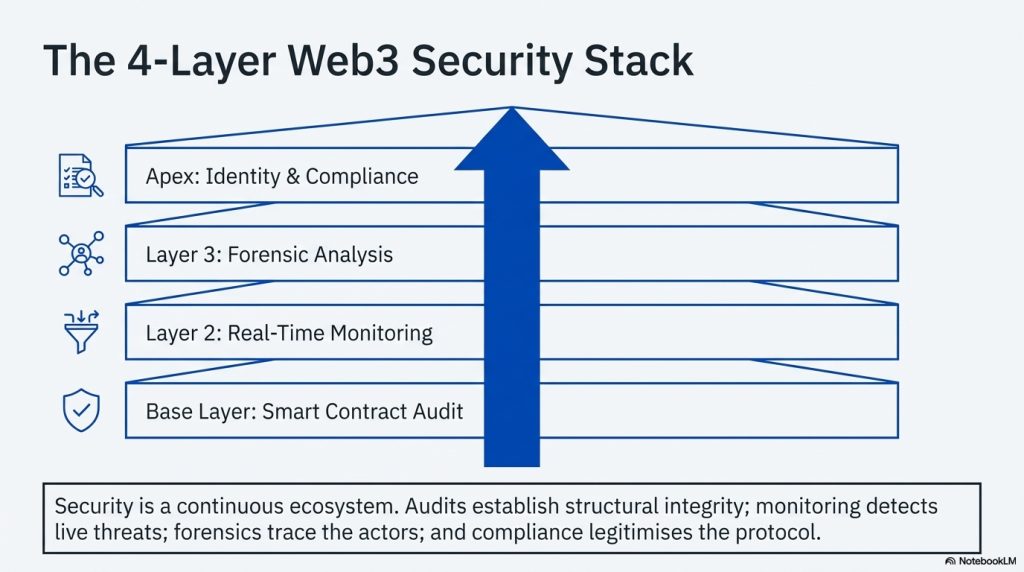
The versus framing of this blog serves an analytical purpose. In practice, the most resilient protocols use both approaches in a layered model. Here is what that looks like in production:
Layer 1: Pre-deployment (Off-Chain) AI-powered smart contract auditing eliminates known vulnerability classes before code goes live. SecureDApp’s Solidity Shield covers 150+ vulnerability patterns with sub-minute analysis for complex contracts.
Layer 2: Runtime detection (On-Chain) Once deployed, SecureWatch provides continuous behavioural anomaly detection, wallet clustering, and event-driven alerts. Automated containment policies can pause contract functions in response to detected anomalies.
Layer 3: Post-incident investigation (On-Chain + Off-Chain) When an incident occurs, SecureTrace combines on-chain transaction graph analysis with off-chain forensic reporting to support asset recovery and legal proceedings.
Layer 4: Identity and compliance (Hybrid) SecureX-DID integrates decentralised identity infrastructure with UIDAI-recognised Aadhaar verification for enterprise onboarding workflows.
This four-layer architecture reflects how serious enterprise security works. No single approach is sufficient. But the sequencing and the allocation of monitoring resources must weight on-chain detection higher as DeFi complexity increases.
What the Data Tells Us
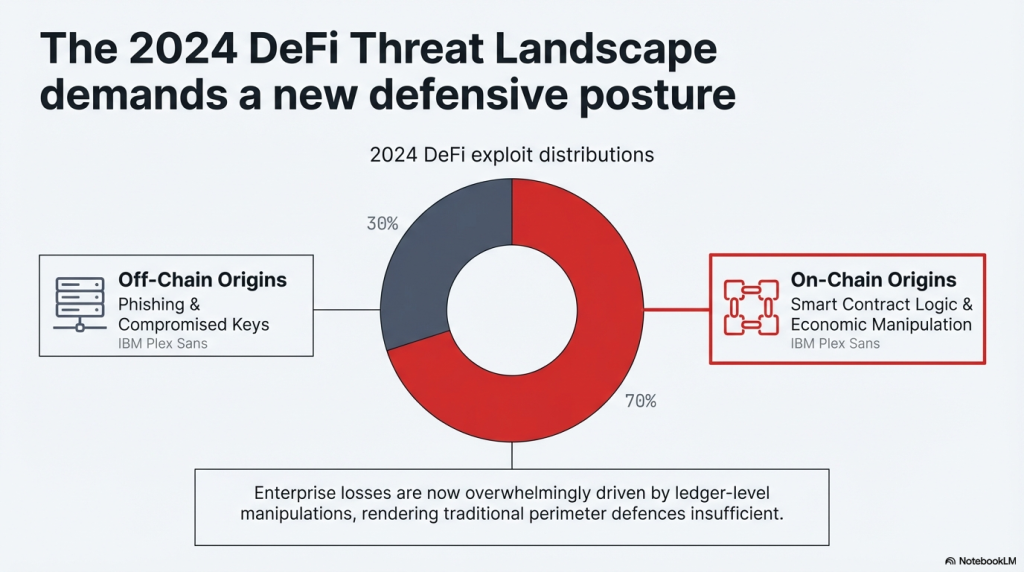
Let us look at where blockchain losses actually originate to understand which security layer matters most. According to research across major exploit databases:
- Over 60% of DeFi exploits involve runtime manipulation of smart contract state. These are on-chain attacks.
- Flash loan attacks accounted for a disproportionate share of exploit value in 2023 and 2024. These are dynamic, on-chain attacks.
- Price oracle manipulation relies entirely on transaction-level execution. Again, on-chain.
- Front-running and MEV extraction are mempool-level attacks. Invisible to off-chain tools.
What is equally telling is the recovery rate. Protocols with active on-chain monitoring in place at the time of an incident recovered or contained funds at a significantly higher rate than those relying only on post-incident investigation. The monitoring layer changes the economics of responding to an exploit. Speed of detection directly determines how much of the attack surface the response team can shut down.
The breakdown is clear. The majority of value lost in Web3 security incidents originates from attacks that only on-chain monitoring can detect in time to respond. Pre-deployment auditing reduces the attack surface. It does not eliminate runtime risk. Real-time blockchain threat monitoring is the layer that covers the gap.
Enterprise Implementation Considerations
For organisations evaluating which approach to prioritise, the decision framework should factor in:
Protocol type: DeFi protocols with liquidity pools face higher runtime risk. Auditing alone is insufficient. On-chain monitoring is critical.
Transaction volume: Higher volume creates more signal for anomaly detection. Large exchanges benefit significantly from real-time wallet clustering and behavioural analytics.
Regulatory jurisdiction: Regulated entities in financial services need both on-chain transaction audit trails and off-chain compliance reporting. Both layers are required.
Team operational capacity: Automated containment reduces dependence on 24/7 human monitoring. For smaller teams, policy-based response automation in platforms like SecureWatch makes on-chain protection operationally viable.
Incident history: Protocols that have experienced exploits have specific attack signatures that can be encoded into monitoring rules. Historical off-chain forensic analysis feeds better on-chain detection logic.
The Future of Blockchain Security Architecture
The industry is moving towards real-time, event-driven security by design. Several trends are accelerating this shift. Cross-chain protocol activity is increasing. Single-chain monitoring is becoming insufficient. Platforms need to track threat propagation across multiple networks simultaneously. An attacker who drains liquidity on Ethereum and bridges funds to an L2 within minutes requires a monitoring layer that sees across both chains without delay.
AI anomaly detection is improving in precision. Reducing false-positive rates is critical for operational adoption. As models improve, automated containment becomes more reliable. Regulatory obligations are expanding. Travel Rule compliance, AML monitoring, and transaction reporting requirements are pushing enterprise clients towards platforms that combine technical detection with regulatory reporting.
Zero-knowledge proof systems are also entering the monitoring space. They allow for compliance verification without exposing sensitive transaction data, a capability that will become increasingly important as privacy-preserving protocols grow in institutional use. The distinction between on-chain and off-chain security is becoming less about choosing one and more about designing a stack where both layers are tightly integrated. Real-time blockchain threat monitoring becomes the nervous system of that stack, with off-chain security providing the structural framework around it.
Conclusion
Off-chain security protects against what you can see before deployment and investigate after an incident. It is essential. But it operates outside the window where most value is actually lost. On-chain monitoring watches the attack as it unfolds. It does not ask whether the code was theoretically safe. It asks whether this specific transaction sequence, in this specific market state, at this specific moment, matches a threat pattern. And it responds in seconds.
The most honest answer to the on-chain versus off-chain question is this: you need both, but you need to be clear about what each one actually does. Off-chain tools protect the code and the infrastructure. On-chain monitoring protects the capital in motion. Conflating the two is how protocols end up with excellent audit reports and empty treasuries. For protocols handling real capital, the question is not whether to monitor on-chain activity. The question is whether you are doing it continuously, automatically, and with the detection depth to catch novel attack patterns before they complete.
That is the standard that real-time blockchain threat monitoring is built to meet. If you are building or securing a Web3 protocol, evaluate your security stack against that standard. Pre-deployment auditing is the floor. Continuous on-chain monitoring is the ceiling you need to reach.
Frequently Asked Questions on Real-Time Blockchain Threat Monitoring
On-chain monitoring watches live blockchain transactions and smart contract state in real time. Off-chain security covers pre-deployment code audits, server infrastructure, and access control. Both are necessary, but they protect different layers of your protocol.
No. An audit reviews code before deployment. It cannot detect runtime attacks like flash loan exploits, price oracle manipulation, or MEV extraction, as these depend on live blockchain conditions. Real-time monitoring is required for runtime protection.
It detects flash loan attacks, reentrancy execution sequences, coordinated wallet activity, MEV and sandwich attacks, abnormal contract interaction patterns, and unusual fund movement velocities across wallets and protocols.
No. Any protocol handling user funds benefits from on-chain monitoring. Automated containment policies reduce the need for large security teams, making real-time monitoring operationally viable for mid-sized DeFi projects and exchange platforms.
SecureDApp offers a four-layer security stack: Solidity Shield for AI-powered pre-deployment auditing, SecureWatch for real-time on-chain threat detection and automated containment, SecureTrace for blockchain forensic investigation, and SecureX-DID for enterprise identity and compliance infrastructure.



