
The Encryption You Trust Today Is Already Being Targeted
Somewhere right now, a well-funded adversary is downloading your encrypted data. They are not trying to break it today. They are storing it and waiting, patiently, for the day quantum computers become powerful enough to crack what protects it in seconds. Security researchers call this the “harvest now, decrypt later” strategy, and it is already happening at scale.
For Indian enterprises, this is not a distant threat scenario. It is a present-day risk that has a ticking clock attached to it. The very cryptographic systems that secure your banking transactions, government communications, enterprise VPNs, digital signatures, and API gateways were designed in an era when quantum computing was theoretical. That era is ending.
Post-quantum cryptography (PQC) is not just a buzzword circulating in global security conferences. It is a fundamental rethinking of how we protect data in a world where the computational rules are about to change. Indian organizations across BFSI, defence, healthcare, critical infrastructure, and regulated industries face a specific and urgent challenge: the window to migrate is narrower than most realize, and the cost of waiting is far higher than the cost of acting now.
This blog explores what PQC actually is, why the threat is real and imminent, what Indian enterprises face specifically, and how a structured approach to quantum-safe security with cryptographic agility can protect your organization for decades to come.
What Is Post-Quantum Cryptography and Why It Matters
To understand post-quantum cryptography, you first need to understand what current cryptography protects and why it is vulnerable.
Most of the internet’s security today runs on two foundational mathematical problems. The first is the difficulty of factoring large numbers, which underpins RSA encryption. The second is the hardness of solving the discrete logarithm problem, which forms the basis of elliptic curve cryptography (ECC) and the Diffie-Hellman key exchange. Classical computers, even the most powerful supercomputers on earth, would take millions of years to break these systems at standard key sizes.
Quantum computers operate on fundamentally different principles. They leverage quantum mechanical phenomena such as superposition and entanglement to process information in ways that classical machines cannot replicate. In 1994, mathematician Peter Shor developed an algorithm showing that a sufficiently powerful quantum computer could break RSA and ECC encryption in polynomial time rather than exponential time. In practical terms, that means what currently takes millions of years could take hours.
This is why post-quantum cryptography exists. PQC refers to cryptographic algorithms designed to be secure against attacks from both classical and quantum computers. These algorithms are built on different mathematical foundations, such as lattice-based problems, hash-based signatures, code-based cryptography, and multivariate polynomial systems, that remain computationally hard even for quantum machines.
Critically, in August 2024, the National Institute of Standards and Technology (NIST) finalized its first set of PQC standards. ML-KEM (formerly CRYSTALS-Kyber) for key encapsulation and ML-DSA (formerly CRYSTALS-Dilithium) for digital signatures are now official standards. This is the clearest signal yet from the global standards community that the quantum threat has moved from theoretical concern to actionable policy requirement.
For Indian enterprises, the NIST standardization creates both an obligation and an opportunity. The obligation is clear: critical systems that protect sensitive data for more than five to ten years must begin quantum-safe migration now. The opportunity is equally clear: organizations that establish cryptographic agility early will be better positioned as regulations inevitably mandate PQC compliance across sectors.
The Indian Enterprise Landscape: Why the Stakes Are Particularly High

India’s digital economy is growing at a pace that makes its security infrastructure increasingly high-value and high-visibility. The country processes hundreds of millions of UPI transactions daily. Its Aadhaar system holds biometric and demographic data for over 1.3 billion citizens. Defence and intelligence networks carry information with multi-decade sensitivity. Stock exchanges, insurance platforms, and core banking systems handle financial data that must remain confidential for generations.
Each of these systems depends on cryptographic algorithms that quantum computers will eventually break. The urgency for Indian enterprises comes from several compounding factors.
First, India’s regulatory environment is tightening. The Digital Personal Data Protection Act creates enforceable standards for data security. RBI, SEBI, and IRDAI are increasingly attentive to cryptographic hygiene in regulated entities. As global PQC standards mature, Indian regulators will follow with their own mandates. Organizations that begin PQC migration now will have a significant compliance advantage over those that wait for mandates to arrive.
Second, the geopolitical context amplifies the threat. India exists in a challenging neighbourhood with sophisticated state-sponsored cyber capabilities. Nation-state actors with access to harvest-now-decrypt-later strategies represent a specific and serious threat to Indian government networks, defence communications, and critical infrastructure. Data that is being intercepted today from Indian organizations may be decrypted in five to ten years when quantum capabilities mature.
Third, India’s enterprise modernization drive creates new cryptographic exposure. As organizations migrate to cloud infrastructure, hybrid work models, IoT deployments, and API-first architectures, the cryptographic surface area grows substantially. Each new integration point, each new device, and each new service layer adds to the crypto inventory that will need to be made quantum-safe.
Furthermore, the misconception that this is a problem for the future is itself the danger. Cryptographic migration is not a switch you flip overnight. It requires discovering and cataloguing every cryptographic asset in your environment, assessing their exposure, prioritizing migration based on data sensitivity and longevity, and systematically replacing vulnerable algorithms. For a mid-sized enterprise, this process typically takes three to five years. For large regulated organizations, it can take longer. The clock is running.
Understanding the Real Threat: Harvest Now, Decrypt Later

The harvest-now-decrypt-later attack model deserves a more detailed examination because it explains why the quantum threat is already active, even though large-scale quantum computers capable of breaking RSA-2048 do not yet exist.
Here is how the attack works in practice. An adversary with access to a telecommunications backbone, a compromised network device, or a passive interception capability collects encrypted traffic at scale. They store this traffic in their infrastructure. The encryption today is unbreakable by their classical systems. However, they are betting that within a decade, they will have access to quantum computing power sufficient to retroactively decrypt this stored traffic.
The data they are most interested in is exactly what Indian enterprises generate and transmit every day: long-lived financial records, legal communications, intellectual property, personal health data, authentication credentials, strategic business plans, and government policy deliberations. This type of data retains its value not just for months but for years and decades.
This is why the migration timeline matters so much. If your enterprise is protecting data that must remain confidential for ten or more years, the relevant question is not whether quantum computers will be powerful enough in 2030 to break current encryption. The question is whether the data you are generating today, with today’s encryption, can be compromised by adversaries who are already collecting it for future decryption.
For BFSI institutions, this concern is acute. Customer financial records, audit trails, regulatory filings, and strategic communications all have long-term sensitivity. For healthcare organizations, patient records contain permanently sensitive information. For defence and government entities, the classified data being protected today may be operationally critical for decades.
The harvest-now-decrypt-later threat means that PQC migration is not about preparing for a future risk. It is about addressing a risk that is materializing in the present, even if the full consequences will only become visible later.
What Cryptographic Agility Means and Why It Is the Foundation of Quantum-Safe Security
One of the most important concepts in the PQC conversation is cryptographic agility, sometimes called crypto-agility. Understanding this concept is essential because it shapes the entire approach to building a quantum-safe enterprise.
Cryptographic agility refers to the capability of a system to rapidly switch from one cryptographic algorithm to another without requiring architectural redesign. In a crypto-agile environment, cryptographic primitives are not hardcoded into applications. They are abstracted, policy-driven, and replaceable. This means that when a new algorithm needs to be adopted, whether because of a discovered vulnerability or a new regulatory requirement, the change can be made at a policy layer rather than requiring months of development work across dozens of systems.
This matters enormously in the PQC context for several reasons. First, PQC is still evolving. While NIST has standardized its first set of algorithms, additional algorithms are still being evaluated. The cryptographic community has not reached a final consensus on which algorithms will prove most robust over time. A crypto-agile system can adopt new algorithms as they are standardized without rebuilding the underlying infrastructure.
Second, the transition period will likely require hybrid encryption, a model that runs both classical and post-quantum algorithms simultaneously. This approach ensures that systems remain interoperable with legacy infrastructure that has not yet migrated while also maintaining quantum-resistant protection. A crypto-agile platform supports hybrid crypto natively, managing the complexity of running dual algorithms transparently.
Third, cryptographic agility reduces organizational risk from algorithm failures. If a PQC algorithm is found to have a previously unknown vulnerability, a crypto-agile system allows rapid replacement. Without agility, every application that implements the algorithm would need to be individually patched, a process that could take months in a large enterprise.
Building a cryptographic agility platform requires deep investment in infrastructure: a centralized policy engine that governs algorithm selection across all services, automated crypto discovery tools that identify vulnerable implementations, key management systems that support the new PQC key types and sizes, and audit logging capabilities that provide visibility into cryptographic operations across the enterprise.
This is precisely where a purpose-built PQC platform like QuantumVault provides transformative value. Rather than requiring enterprises to build these capabilities from scratch, QuantumVault provides a unified PQC governance platform that embeds cryptographic agility into the enterprise fabric from day one.
The QuantumVault PQC Suite: A Purpose-Built Platform for Quantum-Safe Enterprises

QuantumVault is built around a fundamental insight: the challenge of post-quantum migration is not purely technical. It is organizational, operational, and governance-driven. Enterprises do not just need better algorithms. They need a platform that makes those algorithms manageable, policy-driven, auditable, and agile across their entire digital environment.
The QuantumVault PQC Suite addresses this need comprehensively, providing a quantum-safe security platform designed specifically for regulated enterprises navigating the PQC transition.
PQC Discovery and Crypto Inventory Management
The starting point of any PQC migration is knowing what you have. Most enterprises have cryptographic assets distributed across hundreds or thousands of systems: TLS certificates, code signing keys, VPN tunnels, API authentication tokens, database encryption keys, and device identities. Many of these assets are managed in silos, documented inconsistently, and unknown to central security teams.
QuantumVault’s discovery capabilities scan the enterprise environment and build a comprehensive crypto inventory. This inventory identifies every instance of cryptographically protected communication or storage, classifies the algorithm and key strength in use, and flags assets that are vulnerable to quantum attacks. The result is a clear, actionable picture of the enterprise’s cryptographic risk posture, organized by business impact and remediation priority.
This capability alone dramatically accelerates the planning phase of PQC migration. Rather than relying on manual documentation or sampling-based assessments, security teams gain a real-time, continuously updated view of their cryptographic surface.
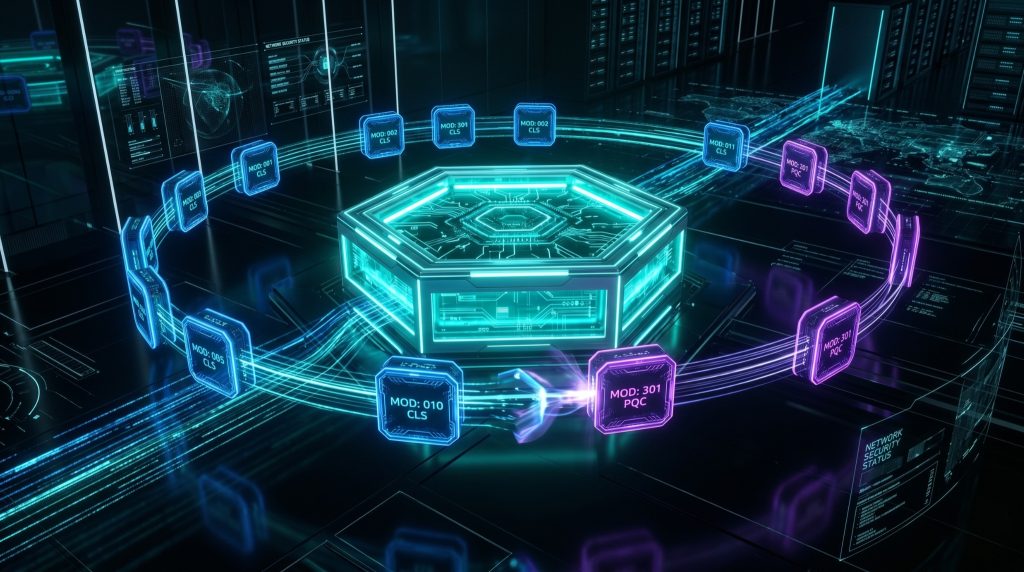
PQC Policy Engine for Algorithm Governance
Once the crypto inventory is established, the question becomes: how do you enforce the right algorithms across a complex, heterogeneous enterprise environment without creating friction or operational disruption?
QuantumVault’s PQC policy engine provides centralized algorithm governance. Security teams define cryptographic policies that specify which algorithms are approved, which are deprecated, and which hybrid combinations are acceptable during the transition period. These policies propagate automatically to all systems managed within the platform.
The policy engine supports graduated migration, allowing organizations to move different systems to quantum-safe algorithms at different speeds based on their risk profile and operational constraints. High-sensitivity systems handling financial transactions or health data can be prioritized for immediate PQC migration. Legacy systems that are scheduled for replacement can be managed with compensating controls while the migration timeline aligns with their upgrade cycle.
This policy-driven approach ensures that PQC migration is not a disruptive, all-at-once event but a controlled, auditable process that aligns with business operations.
Quantum-Safe Gateway for Network and API Security
Network traffic represents one of the largest attack surfaces for harvest-now-decrypt-later adversaries. Every TLS connection, every VPN tunnel, every API call that traverses potentially adversarial infrastructure is a potential interception point.
QuantumVault’s quantum-safe gateway extends PQC protection to network perimeters and API gateways. The gateway negotiates post-quantum key exchange for TLS connections, supporting hybrid key exchange mechanisms that combine ECDH with ML-KEM to maintain compatibility with classical systems while establishing quantum-resistant session keys.
For enterprises operating in regulated sectors, the quantum-safe gateway also provides the cryptographic policy enforcement point that regulators increasingly expect. Traffic that does not meet the defined cryptographic standards can be blocked, logged, or redirected based on policy, providing both security control and compliance evidence.
The PQC tunnel capability within QuantumVault secures site-to-site and remote access connections with quantum-resistant encryption. This is particularly relevant for enterprises with distributed operations, remote workforces, and multi-site architectures where VPN infrastructure forms a critical security boundary.
PQC Key Management for Quantum-Resistant Key Lifecycle
Post-quantum algorithms introduce new complexity in key management. PQC keys are larger than their classical counterparts, require different storage and handling protocols, and in some cases have different lifecycle considerations. Managing these new key types alongside existing classical keys during the hybrid transition period creates a key management challenge that traditional systems are not designed to handle.
QuantumVault’s PQC key management module is purpose-built for the hybrid quantum-safe security environment. It manages the full lifecycle of both classical and post-quantum keys, provides hardware security module (HSM) integration for high-security environments, and enforces key rotation policies that align with quantum security best practices.
The key management capability is deeply integrated with the policy engine, ensuring that key operations are automatically aligned with the enterprise’s cryptographic governance policies. When a policy change requires a key rotation or algorithm upgrade, the key management system executes the change in a coordinated, auditable manner.
PQC Signing Workflows for Document and Code Integrity
Digital signatures are a critical component of enterprise security that is often overlooked in PQC planning conversations. Code signing, document signing, firmware signing, and API payload authentication all rely on digital signature schemes that are vulnerable to quantum attacks.
QuantumVault’s PQC signing workflow capability integrates quantum-resistant signature algorithms into enterprise signing processes. ML-DSA, the NIST-standardized post-quantum signature algorithm, is supported natively, along with hybrid signing modes that maintain backward compatibility.
For regulated enterprises that rely on digital signatures for contract management, regulatory filings, audit reports, and compliance documentation, this capability ensures that signed artifacts maintain their integrity guarantees against quantum-capable adversaries. The signing workflow integrates with existing document management systems and code repositories, minimizing disruption to established processes while upgrading their cryptographic foundation.
PQC Collaboration and Device Security
As enterprise communication increasingly relies on digital collaboration tools and as device proliferation expands the IoT attack surface, the need for quantum-safe protection extends beyond servers and network infrastructure.
QuantumVault’s collaboration security capabilities bring PQC encryption to enterprise messaging, file sharing, and communication platforms. This ensures that sensitive communications, from board-level strategy discussions to client confidential exchanges, are protected against long-term interception.
Device security within the QuantumVault PQC Suite addresses the challenge of quantum-safe identity for endpoints, IoT sensors, industrial control systems, and edge devices. These devices typically have constrained resources but are increasingly critical to enterprise operations and often generate or handle sensitive data. QuantumVault supports lightweight PQC implementations suitable for resource-constrained environments, ensuring that device security does not become a gap in the quantum-safe enterprise architecture.
PQC Audit Logs and Compliance Reporting
PQC migration is ultimately a governance initiative as much as a technical one. Regulators, auditors, and board members need evidence that the migration is progressing according to plan, that cryptographic controls are functioning as intended, and that the enterprise can demonstrate quantum-safe security posture.
QuantumVault’s audit logging capability captures comprehensive records of cryptographic operations, policy changes, algorithm usage, and key lifecycle events. These logs are immutable, tamper-evident, and structured for regulatory reporting.
The compliance reporting module translates raw audit data into the formats required by Indian regulatory frameworks including RBI guidelines, SEBI cybersecurity regulations, and emerging data protection requirements under the DPDP Act. This dramatically reduces the compliance burden on security teams during both the migration phase and the ongoing operational phase of quantum-safe security.
The PQC Migration Journey: A Practical Roadmap for Indian Enterprises

Understanding PQC technology and having the right platform are necessary but not sufficient. Successful quantum-safe migration requires a structured approach that accounts for organizational complexity, operational constraints, and budget realities.
The migration journey typically unfolds in five phases.
Phase One: Discovery and Risk Assessment
The first phase focuses entirely on understanding the current cryptographic posture. Using QuantumVault’s discovery capabilities, security teams conduct a comprehensive inventory of all cryptographic assets. Each asset is assessed for quantum vulnerability, data sensitivity, and remediation urgency.
This phase produces the foundational artifact of the migration: the quantum risk register. This document maps every cryptographically protected system and data store to its quantum exposure level and provides the basis for prioritization decisions.
The discovery phase often surfaces surprises. Organizations frequently find cryptographic implementations in unexpected places: embedded in middleware, hardcoded in legacy applications, implemented inconsistently across microservices, or present in third-party components that the security team did not even know existed. The completeness of this discovery is directly related to the reliability of the subsequent migration planning.
Phase Two: Policy Design and Governance Framework
With the quantum risk register in place, the second phase establishes the governance framework for the migration. This involves defining the enterprise cryptographic policy, establishing the algorithm standards that will govern the quantum-safe environment, and designing the migration sequencing based on risk prioritization.
QuantumVault’s PQC governance platform provides the policy infrastructure that makes these decisions operational rather than theoretical. Policies are codified, versioned, and enforceable, ensuring that governance decisions are reflected consistently across all managed systems.
Phase Three: Hybrid Migration for High-Priority Systems
The third phase begins the actual migration, starting with the highest-priority systems identified in the quantum risk register. These typically include systems that protect data with long-term sensitivity, systems exposed to potential interception, and systems that support critical regulatory compliance functions.
The migration for each system follows a hybrid encryption model during the transition period. QuantumVault manages the complexity of running classical and post-quantum algorithms in parallel, ensuring continuity of operations and interoperability with systems that have not yet been migrated.
Phase Four: Systematic Rollout Across the Enterprise
With high-priority systems secured, the fourth phase extends quantum-safe security systematically across the enterprise. The PQC rollout is managed through QuantumVault’s policy engine, which coordinates migrations across different business units, geographic locations, and technology stacks.
This phase also addresses the integration challenges that arise when quantum-safe systems need to communicate with external partners, customers, or infrastructure providers that may be at different stages of their own PQC migrations. QuantumVault’s hybrid crypto capabilities are essential during this period, enabling secure communication across the mixed cryptographic landscape.
Phase Five: Continuous Monitoring and Crypto Agility Operations
PQC migration is not a project with a defined end date. It is a continuous operational capability. The fifth phase establishes the ongoing operational model for quantum-safe security, including continuous crypto inventory monitoring, policy-driven algorithm updates as standards evolve, and systematic review of the cryptographic risk posture.
QuantumVault’s continuous monitoring capabilities ensure that newly deployed systems are automatically evaluated for cryptographic compliance and that policy violations are detected and remediated in near real time. This operational continuity is what crypto agility looks like in practice.
Sector-Specific Considerations for Indian Enterprises

Different industries face distinct urgency levels and regulatory contexts in their PQC journey.
BFSI: Immediate Priority
Indian banks, NBFCs, insurance companies, and capital market institutions are subject to RBI, SEBI, and IRDAI oversight. Financial data has inherently long-term sensitivity. The harvest-now-decrypt-later threat is most acute in this sector. QuantumVault’s quantum-safe network and PQC key management capabilities are specifically designed for the operational demands of financial infrastructure, including high availability, low latency, and regulatory auditability.
Healthcare and Life Sciences: Patient Data Longevity
Patient health records, clinical trial data, and genomic information are among the most long-lived sensitive data types. A patient record created today may need to remain confidential for decades. Healthcare organizations using QuantumVault’s PQC platform can ensure that this data remains protected against the quantum threat throughout its full lifecycle.
Government and Defence: Classified and Long-Lived Information
Government communications and defence information represent the highest-sensitivity PQC use case. The NCIIPC and India’s national cybersecurity policy frameworks increasingly recognize the quantum threat. QuantumVault’s quantum-safe security platform, with its comprehensive audit capabilities and policy-driven governance, aligns with the requirements of government security frameworks.
IT and Technology Companies: Protecting IP and Customer Data
India’s massive IT services and product sector faces a dual PQC challenge. These organizations must protect their own intellectual property and internal communications while also providing quantum-safe security capabilities to their enterprise clients. QuantumVault enables IT organizations to build PQC competency both for internal use and as a value-added service offering.
Telecom and Critical Infrastructure: The Quantum-Safe Network Imperative
India’s telecommunications operators and critical infrastructure providers represent perhaps the most exposed category of organizations from a PQC perspective. Telecom networks carry enormous volumes of sensitive communications, and the operators of these networks are themselves both potential targets of harvest-now-decrypt-later attacks and potential vectors through which such attacks can be executed against their enterprise customers.
For telecom providers, the shift to quantum-safe network infrastructure is also a competitive differentiation opportunity. Enterprises that understand the quantum threat will increasingly demand quantum-safe connectivity from their service providers. QuantumVault’s PQC Suite provides the platform through which telecom operators can build and certify quantum-safe access services for enterprise clients.
Power grids, water treatment systems, transportation networks, and other critical infrastructure present a distinct PQC challenge: operational technology (OT) environments typically run on legacy systems with constrained resources and long replacement cycles. A five-year migration timeline may not accommodate the operational realities of infrastructure that was designed to run for twenty to thirty years. QuantumVault’s approach to PQC device security, with support for lightweight and resource-constrained implementations, addresses this challenge, enabling quantum-safe protection even in environments where full hardware replacement is not feasible in the near term.
Common Misconceptions About Post-Quantum Cryptography
Several persistent misconceptions slow enterprise action on PQC. Addressing them directly accelerates informed decision-making.
Misconception 1: Quantum computers powerful enough to break RSA do not exist yet, so there is no urgency.
This ignores the harvest-now-decrypt-later threat. Adversaries do not need quantum computers today if they are collecting data today for decryption later. The migration lead time required for large enterprises also means that waiting for imminent quantum capability is too late.
Misconception 2: PQC migration will break all existing systems.
A well-designed PQC migration using hybrid encryption and a cryptographic agility platform like QuantumVault preserves interoperability throughout the transition. Migration can be gradual, prioritized, and operationally transparent.
Misconception 3: This is a technology team problem, not a business leadership concern.
PQC migration affects data protection, regulatory compliance, customer trust, and long-term business continuity. It requires executive sponsorship, board awareness, and budget commitment. Security teams cannot drive this migration without business leadership support.
Misconception 4: Upgrading to the latest TLS version solves the quantum problem.
TLS 1.3 is an important security improvement but it still relies on classical cryptographic algorithms that are quantum-vulnerable. A quantum-safe upgrade requires replacing the underlying algorithms with PQC alternatives, which is precisely what QuantumVault enables.
Frequently Asked Questions (FAQs)
1. What is post-quantum cryptography (PQC) in simple terms? Post-quantum cryptography refers to a new generation of encryption algorithms designed to resist attacks from quantum computers. While today’s encryption can be broken by sufficiently powerful quantum computers, PQC algorithms are built on mathematical problems that remain hard even for quantum machines.
2. When will quantum computers be able to break today’s encryption? Most expert estimates suggest that cryptographically relevant quantum computers could emerge within the next ten to fifteen years, though some timelines are shorter. The harvest-now-decrypt-later threat means organizations should treat this as an immediate concern regardless of when full quantum capability arrives.
3. What is “harvest now, decrypt later” and why does it matter to Indian enterprises? This attack model involves adversaries collecting and storing encrypted data today, with the intention of decrypting it when quantum computers become available. Any sensitive data your organization generates now that needs to remain confidential for more than five to ten years is potentially at risk from this strategy.
4. What is cryptographic agility and why is it important? Cryptographic agility is the ability to swap cryptographic algorithms quickly without redesigning systems. It is important because the PQC landscape is still evolving, algorithm vulnerabilities can be discovered unexpectedly, and organizations need to respond to changing standards without major infrastructure rebuilds.
5. What does hybrid encryption mean in the PQC context? Hybrid encryption combines classical and post-quantum algorithms simultaneously. During the migration transition period, this approach maintains interoperability with systems that have not yet migrated to PQC while providing quantum-resistant protection for new and upgraded systems.
6. How long does a PQC migration typically take for an Indian enterprise? The timeline varies by organizational complexity, but most mid-to-large enterprises should plan for a three-to-five year migration journey. This reinforces the urgency of beginning the discovery and planning phases immediately.
7. What NIST PQC algorithms does QuantumVault support? QuantumVault’s PQC Suite supports the finalized NIST standards including ML-KEM (CRYSTALS-Kyber) for key encapsulation and ML-DSA (CRYSTALS-Dilithium) for digital signatures, along with additional algorithms under evaluation and hybrid modes for the transition period.
8. How does QuantumVault help with PQC compliance for RBI and SEBI regulated entities? QuantumVault provides audit logs, compliance reporting, and policy-driven governance that align with regulatory requirements. Its quantum-safe network and key management capabilities address the specific cryptographic controls expected by Indian financial regulators.
9. Is PQC migration disruptive to business operations? When managed through a cryptographic agility platform like QuantumVault, PQC migration can be operationally transparent. Hybrid encryption modes maintain interoperability during the transition, and policy-driven migration allows prioritization that minimizes disruption to critical systems.
10. What is the difference between quantum encryption and post-quantum cryptography? Quantum encryption (such as quantum key distribution or QKD) uses quantum mechanical phenomena to distribute cryptographic keys and relies on physics rather than mathematics for its security guarantees. Post-quantum cryptography, by contrast, uses classical computing but with new mathematical algorithms that resist quantum attacks. PQC is more practically deployable at enterprise scale and does not require specialized quantum hardware infrastructure.
11. How does QuantumVault handle the PQC key management challenge? QuantumVault’s PQC key management module handles the full lifecycle of both classical and post-quantum keys, integrates with HSMs, enforces automated rotation policies, and manages the complexity of operating dual-algorithm environments during the transition period.
12. Can QuantumVault integrate with existing enterprise security infrastructure? Yes. QuantumVault is designed to integrate with existing SIEM systems, identity providers, PKI infrastructure, and network security components. Its quantum-safe gateway and policy engine work alongside existing security controls rather than replacing them wholesale.
13. What is a PQC audit log and why does it matter? A PQC audit log provides an immutable, tamper-evident record of all cryptographic operations, policy changes, and algorithm usage within the managed environment. It provides the evidence trail that regulators, auditors, and internal governance teams require to validate quantum-safe security posture.
14. How does QuantumVault address PQC for remote access and VPN security? QuantumVault’s PQC tunnel capability applies post-quantum encryption to VPN and remote access connections. This ensures that remote workers and branch offices communicate through quantum-resistant channels, eliminating this common exposure point in the enterprise security perimeter.
15. What should Indian enterprises do first to start their PQC journey? The first step is a comprehensive cryptographic discovery and risk assessment using QuantumVault’s PQC discovery capabilities. Understanding your current cryptographic posture, identifying quantum-vulnerable assets, and building a quantum risk register provides the foundation for all subsequent migration planning and prioritization.
Conclusion: The Window to Act Is Now

The quantum threat to enterprise cryptography is not a future problem. It is a present-day risk with a migration timeline that demands immediate attention. Indian enterprises that secure long-lived sensitive data, operate in regulated sectors, or communicate across potentially adversarial network infrastructure cannot afford to treat PQC migration as a someday priority.
The evidence is clear. NIST has finalized PQC standards. Nation-state adversaries are harvesting encrypted data for future decryption. Regulatory frameworks are evolving toward mandating quantum-safe security. And the organizational complexity of enterprise-scale cryptographic migration means that starting later simply means finishing later, in a threat environment that grows more consequential with every passing year.
What separates organizations that successfully navigate this transition from those that do not is not simply awareness of the threat. It is having a structured approach, the right governance framework, and a platform purpose-built for the challenges of quantum-safe migration at enterprise scale.
QuantumVault’s PQC Suite provides exactly that foundation: a quantum-safe security platform that combines PQC discovery, policy-driven crypto governance, quantum-resistant network security, PQC key management, secure signing workflows, and continuous compliance monitoring into a unified, crypto-agile architecture designed for Indian enterprises operating in a quantum-threatened world.
The encryption that protects your most sensitive data today is being targeted. The question is not whether to act. The question is whether you will act before the window closes.


