Introduction: The Security Problem No One Talks About Enough
Staking pools are quietly becoming the backbone of Proof-of-Stake blockchain networks. Millions of dollars in validator rewards flow through them every single day. But here is the uncomfortable truth most pool operators do not say out loud: most staking pools are dangerously under-monitored.
A smart contract can look perfectly clean during an audit. A validator node can pass all pre-deployment checks with flying colours. Yet the moment real funds start flowing through the system, the threat landscape changes completely. Adversaries are not waiting. They are watching every transaction, every validator rotation, every reward distribution in real time.
If your pool is not watching back with the same intensity, you are already behind.
This is where real-time blockchain threat monitoring becomes not just useful but absolutely essential. It is the difference between catching an exploit in its first block and reading about your protocol in a post-mortem thread the next morning.
What Makes Staking Pools a Unique Attack Surface

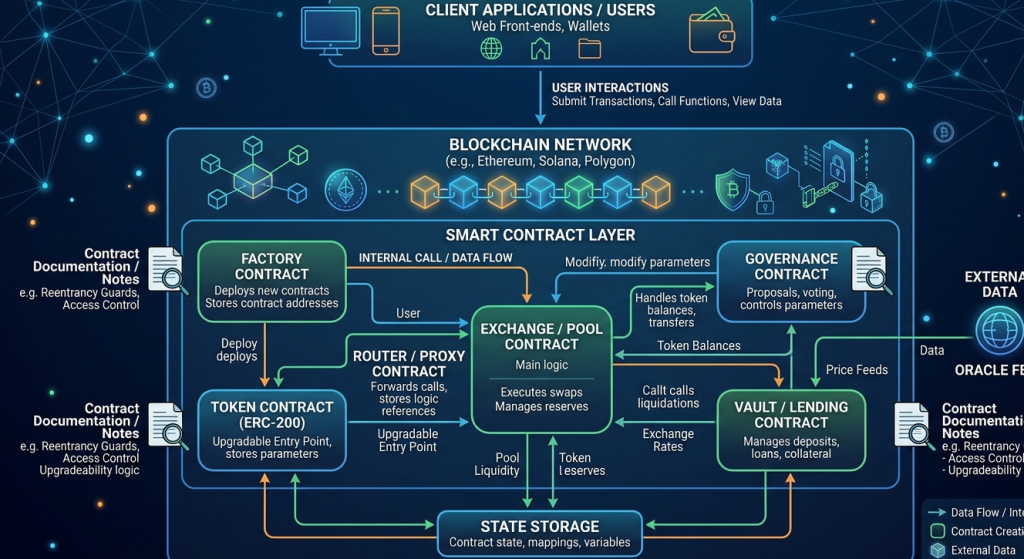
Staking pools are not ordinary DeFi protocols. They carry a very specific risk profile that sets them apart from simple swap contracts or lending markets.
Continuous fund exposure: Unlike a lending pool where funds sit idle between borrows, staking pools have funds perpetually locked and active. There is no downtime window for security teams to breathe.
Multi-party validator coordination: Many pools coordinate dozens or even hundreds of validators. Each validator key represents a separate attack vector that can be targeted individually.
Time-sensitive reward logic: Most pools have complex on-chain reward distribution logic tied to epoch boundaries. Exploit windows are sometimes only a few seconds wide but can drain entire reward reserves.
Long-term lock mechanics: Withdrawals are often delayed by unbonding periods. This means that if a user’s funds are compromised, recovery is structurally constrained by the protocol itself.
Cross-chain complications: Many modern staking pools operate across multiple chains or use liquid staking derivatives. Every bridge, every wrapped token, every cross-chain message is an additional surface.
Understanding this unique attack surface is the first step. The second step is building monitoring that actually matches this threat profile.
Why Traditional Security Audits Are Not Enough

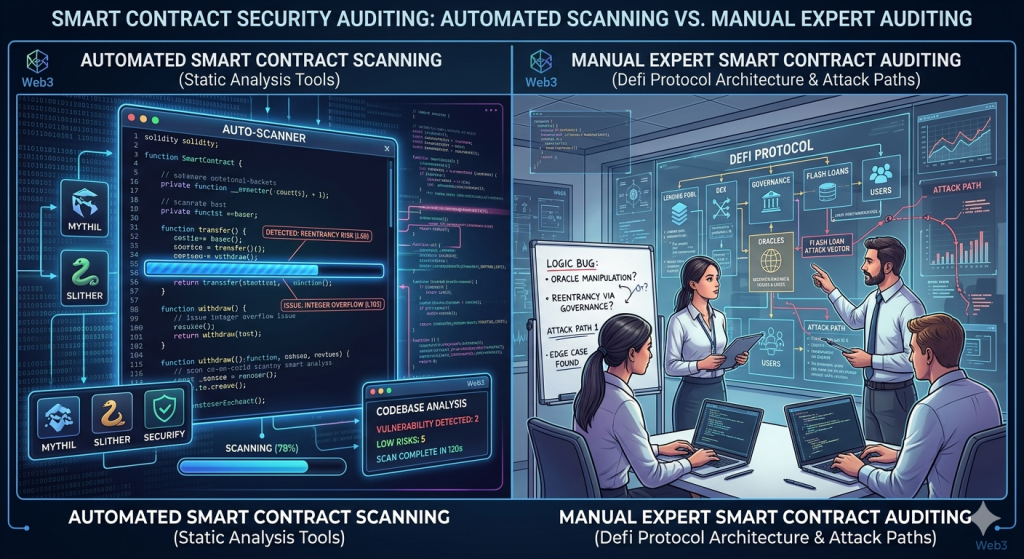
Let us be very clear. Audits are necessary. They are a foundational layer of any serious security programme. But they are a point-in-time assessment. They tell you whether your code was safe on the day someone reviewed it.
They do not tell you:
- Whether a validator key has been silently compromised since deployment
- Whether a new governance proposal is about to pass that will change reward parameters maliciously
- Whether an attacker is front-running your reward distribution transactions right now
- Whether on-chain data shows unusual slashing events targeting your validators
Audits are like a medical check-up. Valuable, necessary, but not a substitute for a continuous health monitor. Real-time blockchain threat monitoring is that continuous monitor. It fills the gap between “the code was safe yesterday” and “what is happening to my pool right now.”
The Anatomy of Real-Time On-Chain Monitoring for Staking Pools

Effective monitoring for staking pools is not just running a block explorer in a browser tab. It involves several interconnected layers working simultaneously.
1. Validator Performance and Slashing Surveillance
Every validator in your pool should be monitored for attestation performance, proposal duties and slashing events. A sudden drop in attestation rate is not just a performance metric. It is an early signal of a potential key compromise or infrastructure failure.
Slashing events need instant alerts. Not hourly summaries. Not daily digests. Instant alerts. Because once slashing begins, the damage compounds with every epoch that passes without intervention.
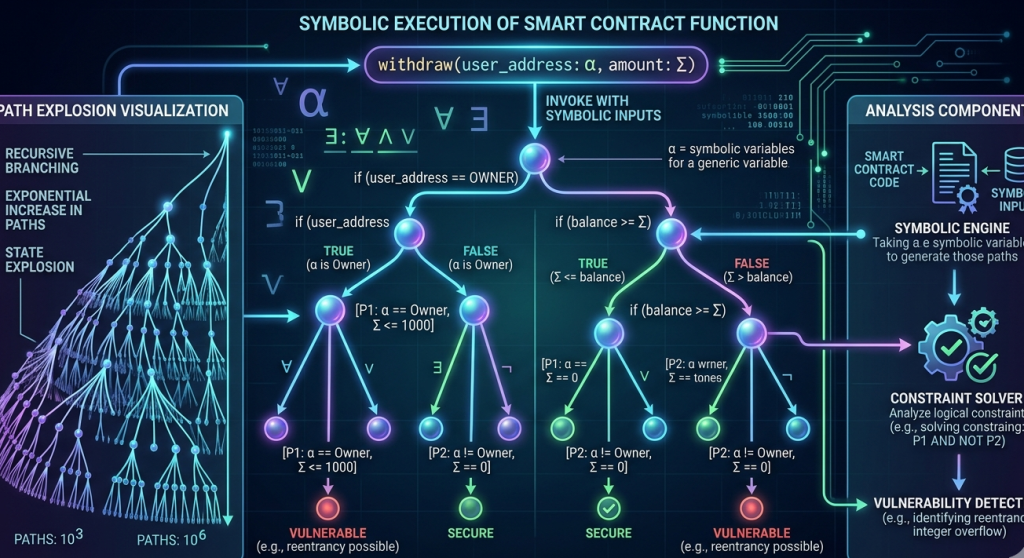
2. Smart Contract State Anomaly Detection
Your staking contract’s internal state should be watched for deviations from expected behaviour. This includes monitoring for unexpected changes in reward accumulators, unusual spikes in deposit or withdrawal volumes, and any changes to privileged addresses such as owner or admin roles.
If someone changes the fee recipient address at 3 AM on a weekend, your monitoring system should wake up your security team before that address collects a single satoshi in rewards.
3. Mempool and Front-Running Detection
Front-running in staking pools is subtle but very real. Attackers can monitor your reward distribution calls in the mempool and insert their own transactions to extract value. Real-time mempool monitoring helps identify sandwich attacks, gas price manipulation and unusual transaction ordering that targets your pool specifically.
4. Governance and Parameter Change Monitoring
On-chain governance is a double-edged sword. It gives communities control but also creates a vector for malicious proposals. Every governance vote that could affect your pool’s parameters, fee structure, or withdrawal logic needs to be tracked from the moment it is submitted.
A proposal with a short voting window and significant parameter changes deserves immediate attention, not a notification three days later.
5. Liquidity and Reserve Health Tracking
For pools issuing liquid staking tokens, the peg between the derivative and the underlying asset is a critical health signal. Any deviation beyond acceptable bounds warrants investigation. Automated monitoring can track these ratios block by block and trigger alerts before a depeg becomes a crisis.
Common Attack Vectors Targeting Staking Pools
Understanding what you are monitoring for is as important as having the monitoring in place. Here are the most prevalent threat patterns seen across staking protocol exploits.
Reentrancy on withdrawal logic: Poorly structured withdrawal functions remain one of the most common vulnerabilities. An attacker repeatedly re-enters the withdrawal function before the state is updated, draining funds in a single transaction chain.
Oracle manipulation for reward calculations: If your pool uses an external price oracle to calculate stETH or similar derivative values, that oracle is a target. Manipulating the price feed even briefly can distort reward distributions significantly.
Validator key exfiltration: Infrastructure-level attacks targeting validator key storage are increasingly sophisticated. Private key theft at the infrastructure layer bypasses smart contract security entirely.
Malicious contract upgrades: Upgradeable proxy patterns are common in staking protocols. An attacker who gains control of the upgrade key can replace your entire contract logic with a malicious implementation in a single transaction.
Flash loan-amplified governance attacks: An attacker borrows a massive amount of governance tokens, votes on a malicious proposal in the same block, and returns the loan. Effective real-time monitoring can flag unusual governance participation spikes in time for emergency intervention.
How SecureDApp Approaches Staking Pool Security
SecureDapp has been at the forefront of blockchain security infrastructure since the early days of DeFi. Our approach to staking pool security goes beyond the checklist model. It is built around the principle that security is a continuous process, not a milestone.
SecureWatch is our real-time blockchain threat monitoring platform. It is purpose-built for protocols that cannot afford gaps in their threat visibility. For staking pools specifically, SecureWatch provides block-by-block surveillance of validator behaviour, smart contract state changes and on-chain fund movements.
Our AI-powered threat detection engine does not just alert on known attack patterns. It learns the normal behaviour of your specific pool and flags deviations that no static ruleset would catch. This is critical for staking pools where the attack surface evolves with every governance change and every new validator onboarded.
We also offer smart contract auditing that goes deeper than standard code review. Our audit methodology includes simulation-based attack testing and economic exploit modelling specific to staking mechanics. We have audited staking protocols operating across Ethereum, BNB Chain, Polygon and several emerging L2 networks.
For protocols that want a complete security layer, our SecureScore framework gives your staking pool a continuous, publicly visible security rating. This is not just good for your team’s peace of mind. It is increasingly being used by institutional stakers to decide which pools they will trust with their assets.
If you are running a staking pool today without a real-time monitoring layer, reach out to SecureDapp. The conversation is worth having before an incident forces it.
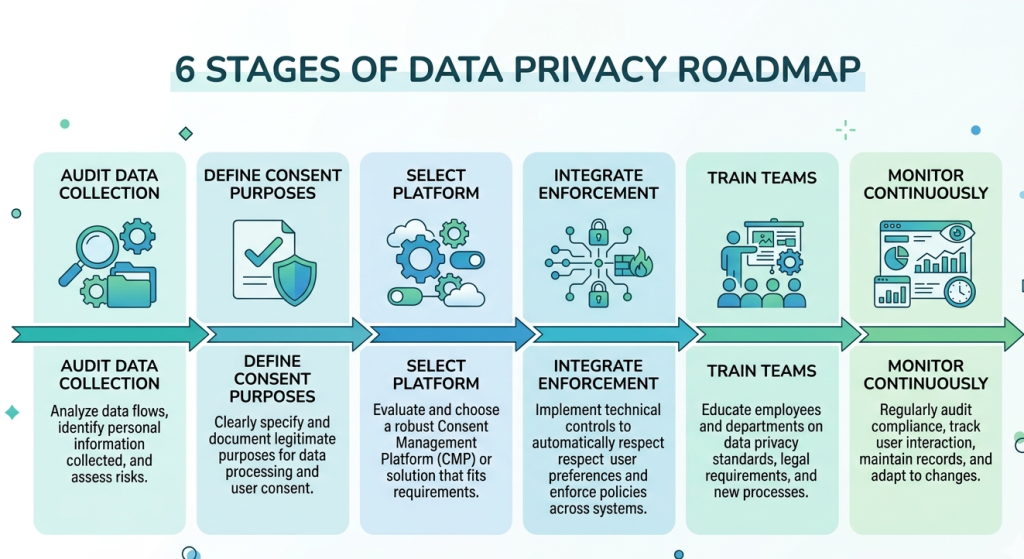
Building a Real-Time Monitoring Stack: Practical Framework

Here is a practical framework that staking pool operators can use to evaluate their monitoring maturity.
Level 1: Basic Event Logging Your contracts emit events. You are collecting them. You have basic alerts for large withdrawals and contract pauses. This is the minimum viable bar. Most protocols are here.
Level 2: Threshold-Based Alerting You have defined normal ranges for key metrics. Withdrawals above X ETH trigger an alert. Validator attestation rates below Y percent send a notification. You have coverage for the obvious attack vectors. This is where serious teams should aim immediately.
Level 3: Contextual Anomaly Detection Your monitoring system understands the context of what normal looks like for your pool specifically. It can distinguish between a legitimate large withdrawal from a whale and an unusual drain pattern. Alerts include enriched context, not just raw event data. This is where SecureDapp’s SecureWatch operates.
Level 4: Predictive Threat Intelligence Your system correlates on-chain data with off-chain threat signals. It watches mempool data, tracks known attacker addresses and integrates threat intelligence feeds. You are not just reacting. You are anticipating. This is the gold standard for high-value pools.
Most teams jump from Level 1 to trying to build Level 4 and burn out. The pragmatic path is methodical progression through each level with the right tooling and partners at each stage.
The Cost of Getting This Wrong
Let us look at the numbers honestly. The biggest staking pool exploits in recent years have not been small. Hundreds of millions of dollars have been lost to attacks that real-time monitoring could have caught or significantly limited.
More importantly, the reputational cost almost always exceeds the financial cost. A staking pool that suffers a significant exploit does not just lose the stolen funds. It loses the deposits of users who leave after the incident. It loses future institutional stakers who view the incident as a disqualifying event. It loses the trust that takes years to build and minutes to destroy.
The investment in real-time blockchain threat monitoring is not a cost centre. It is yield protection. It is the mechanism that allows your pool to keep operating, keep growing and keep competing in an increasingly crowded and scrutinised market.
Regulatory and Institutional Considerations

The regulatory environment around staking is evolving rapidly in 2025. Several jurisdictions are now requiring staking service providers to demonstrate security controls that include continuous monitoring as a condition of operation.
Institutional stakers, including sovereign wealth funds and pension funds now exploring on-chain yield, are conducting detailed security due diligence before committing assets. A real-time monitoring programme with documented alert response procedures is increasingly a prerequisite for institutional participation, not a nice-to-have.
SecureDapp’s security certificates and audit reports are structured to satisfy institutional due diligence requirements. Our documentation is designed to answer the questions that compliance and risk teams actually ask, not just the questions that developers think they will ask.
Key Metrics Every Staking Pool Should Monitor in Real Time
Here is a concrete list of metrics that every serious staking pool security programme should be tracking on a continuous basis.
Validator metrics: Attestation rate, proposal inclusion rate, slashing events, activation and exit queue activity, balance changes beyond expected rewards.
Contract metrics: Total value locked changes, reward accumulator values, admin role holder addresses, upgrade proxy implementation address, fee parameter values.
Transaction metrics: Large deposit or withdrawal events, unusual gas patterns in pool transactions, failed transaction spikes, interaction with known malicious addresses.
Governance metrics: New proposal submissions, voting participation rates, quorum progress on active proposals, time-to-execution on passed proposals.
Derivative metrics (for liquid staking pools): Staked token peg ratio, minting and burning rate, secondary market liquidity depth, oracle price deviations.
If your current monitoring setup does not cover all of these consistently, there are gaps in your threat visibility. Every gap is an opportunity that attackers are trained to find.
Incident Response: What Happens When Monitoring Fires an Alert
Real-time monitoring is only as valuable as the response it triggers. An alert that no one acts on is worse than no alert because it creates false confidence.
Every staking pool should have a documented incident response playbook that is triggered when monitoring detects a threat. At a minimum, this playbook should define the following.
Who gets alerted and through which channels when a critical alert fires. What the first ten minutes of response look like, including who has authority to pause the contract if necessary. What constitutes a critical, high, medium and low severity event. How post-incident analysis is conducted and documented.
SecureDapp offers incident response consulting for staking protocols that want to build and test their playbooks against realistic attack simulations. Having a playbook that has never been tested is only marginally better than having no playbook at all.
Conclusion: Monitoring Is Not Optional Anymore

The staking ecosystem has grown too large, too complex and too valuable for passive security approaches to be acceptable. Real-time blockchain threat monitoring is not an advanced feature for well-resourced teams with big budgets. It is a baseline requirement for any pool that takes its responsibility to stakers seriously.
The tools exist. The expertise exists. The only question is whether pool operators will build this capability before they need it in an emergency or only after.
SecureDapp is here to help staking pools build security programmes that match the seriousness of what they are protecting. From smart contract audits to continuous on-chain monitoring with SecureWatch to incident response support, we offer end-to-end security infrastructure for the protocols that the next generation of finance is being built on.
Do not wait for an incident to make this a priority. Visit securedapp.io to learn how we can help protect your staking pool today.
Frequently Asked Questions
Real-time blockchain threat monitoring means continuously watching your staking pool’s on-chain activity, including validator performance, smart contract state changes, fund movements and governance actions, to detect threats the moment they appear rather than after damage is done.
An audit is a point-in-time code review. It tells you if your contract was safe when it was reviewed. On-chain monitoring is continuous surveillance of what is actually happening to your live protocol in every block. Both are necessary and complement each other.
It cannot guarantee zero exploits, but it dramatically reduces the window in which an attack can operate unchallenged. Many major exploits drain funds over multiple transactions across several blocks. Early detection can limit losses significantly and sometimes stop attacks entirely.
Start with alerts for large withdrawals, admin role changes, contract pause events, validator slashing events and significant changes in total value locked. These cover the highest-probability, highest-impact events and are the minimum viable monitoring baseline.
SecureWatch provides block-by-block surveillance tailored to staking protocol mechanics. It monitors validator behaviour, smart contract state, governance activity and fund movements with AI-powered anomaly detection. It alerts your team with contextual information so you can respond immediately rather than investigating a raw alert.



