The Web3 security market has a quality problem. As demand for smart contract security audits has grown, so has the number of firms claiming to provide them. Some of these firms deliver rigorous, expert-level reviews that genuinely protect protocols. Others deliver thin automated scans wrapped in professional-looking reports, collecting substantial fees while providing minimal real protection.
The stakes make this distinction critically important. If you hire the wrong firm, you may launch your protocol believing it has been thoroughly reviewed when it has not. That false confidence can lead to decisions, including moving faster, handling more user funds, and marketing security credentials, that amplify the damage when a vulnerability is eventually exploited.
This guide identifies the specific red flags that separate credible audit firms from those that are not equipped to protect your protocol. Recognize these signals before you sign a contract, not after.
Red Flag 1: No Publicly Available Audit Reports
Legitimate audit firms have a public track record. They publish their reports, with client permission, as evidence of their methodology and depth. If a firm cannot point you to a library of previous public audits, you have no basis for evaluating what their work actually looks like.
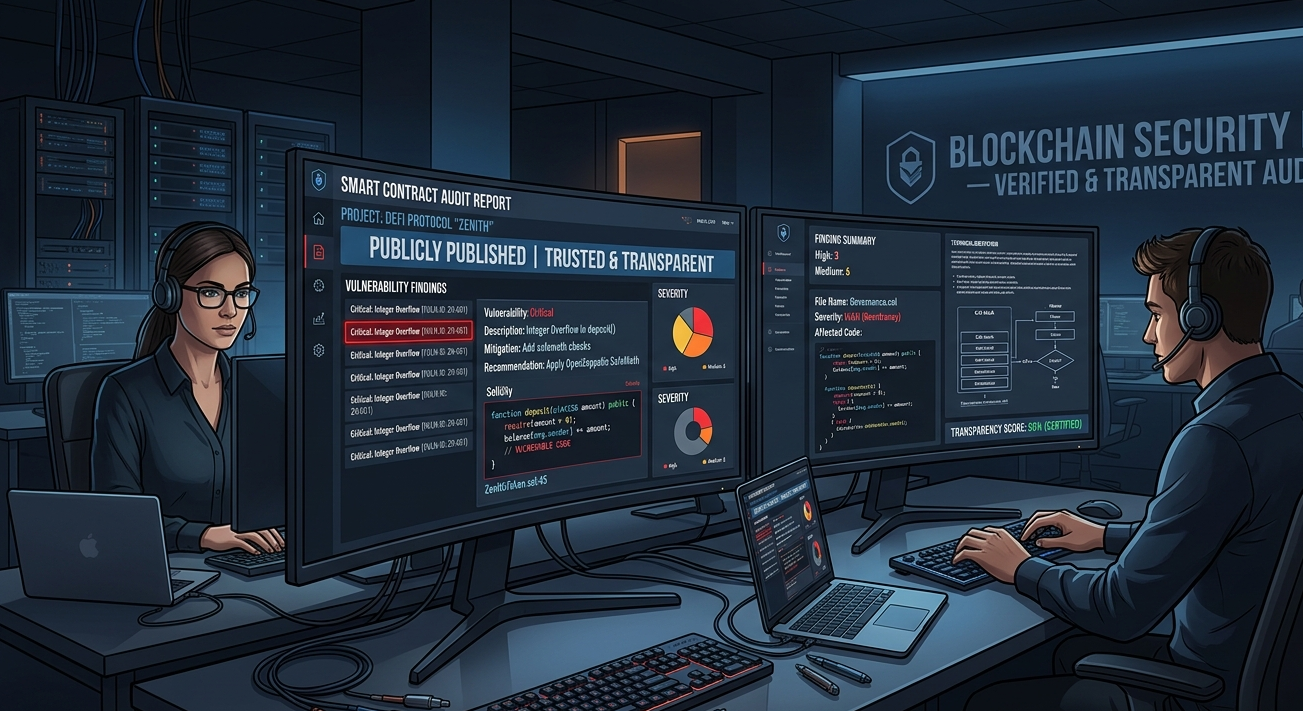
This is not just about transparency for its own sake. Published reports allow you to evaluate specific findings, understand how the firm classifies vulnerabilities, assess the quality of their remediation guidance, and determine whether their experience is relevant to your protocol type.
A firm that has been operating for any meaningful length of time without publishable reports either has not done meaningful work or has consistently failed to produce reports clients are willing to make public. Neither is encouraging.
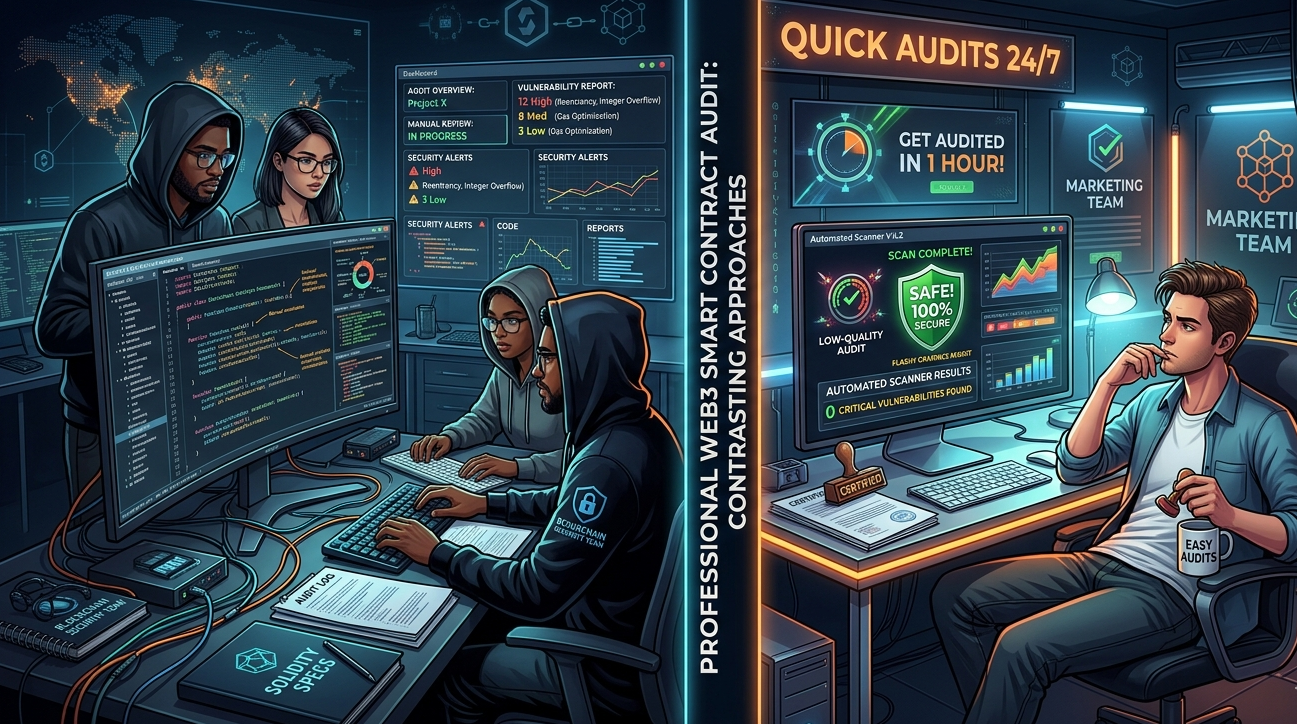
Red Flag 2: Unusually Fast Turnaround Claims
A thorough smart contract security audit of a complex DeFi protocol takes time. Experienced auditors need time to develop a mental model of your system, trace execution paths, consider edge cases, and think carefully about economic attack vectors. Shortcuts in this process mean vulnerabilities get missed.

If a firm promises to audit a complex, multi-contract system in 48 to 72 hours, they are describing an automated scan, not a manual audit. Automated scans have value, but they are not a substitute for expert human review. A firm that conflates the two, whether deliberately or through genuine confusion about methodology, cannot be trusted with complex security work.
Reasonable timelines for thorough manual review start at three to five days for simple contracts and scale upward with complexity. Any firm that consistently promises significantly faster delivery is telling you something important about their actual process.
Red Flag 3: Vague Methodology Descriptions
When you ask an audit firm to describe their methodology, you should receive a specific, technically credible answer. They should be able to tell you which tools they use, how manual review is structured, what expertise the assigned auditors have, and how they specifically approach the type of protocol you have built.
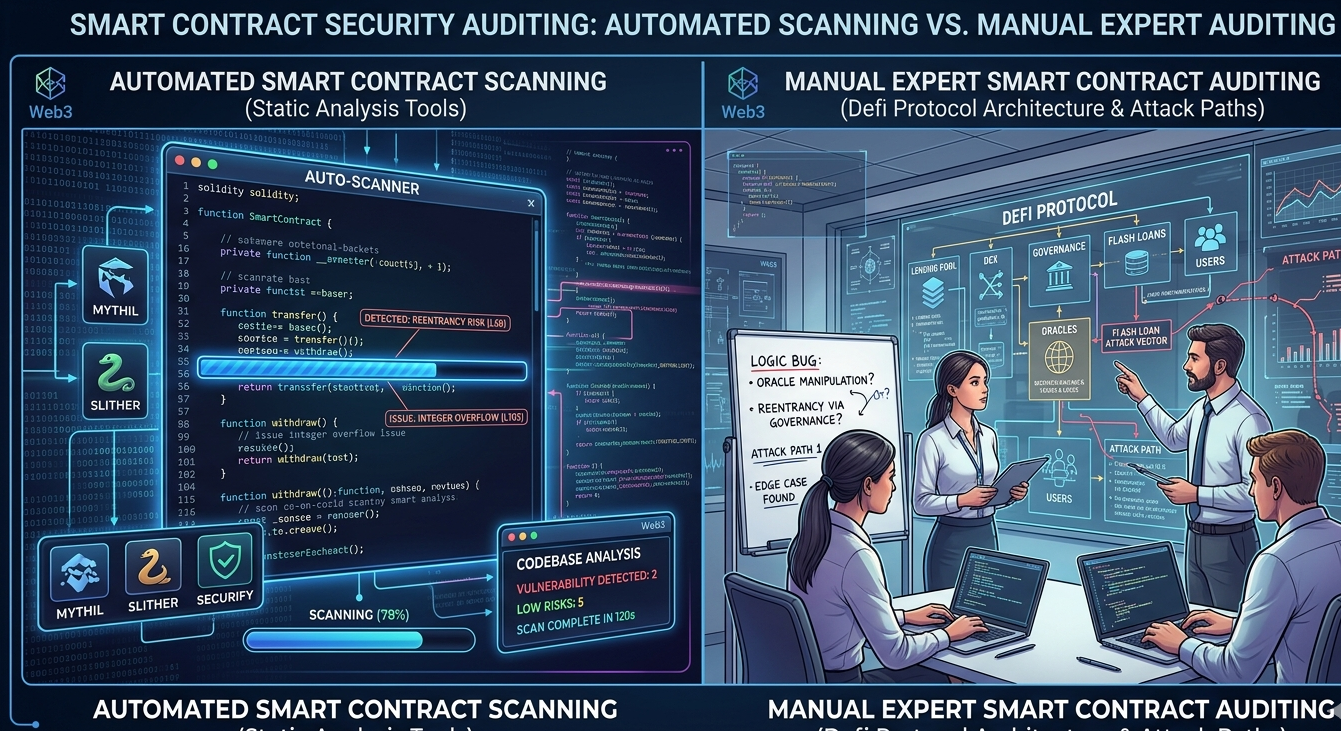
Vague answers like ‘we use industry-leading tools and processes’ or ‘our team is highly experienced in blockchain security‘ are not methodology descriptions. They are marketing language. A firm that cannot explain specifically how they will audit your code is unlikely to audit it effectively.
Push for specifics in every pre-engagement conversation. Ask what tools they use. Ask how they handle DeFi economic attack modeling. Ask how they approach upgrade proxy security. Specific questions reveal specific capability gaps.
Red Flag 4: Guaranteed Clean Reports
No legitimate auditor can guarantee a clean report before reviewing your code. If a firm suggests or implies that your contracts will pass their review before they have examined them, they are signaling that their review is not designed to find vulnerabilities. It is designed to produce the outcome you want.
This pattern sometimes emerges as a sales tactic. The implicit promise is that working with this firm will result in a clean report that you can publish. The reality is that a clean report from a non-rigorous firm provides no actual security. It provides a document that looks like security.
A firm that approaches every engagement with genuine skepticism and rigorous standards will sometimes deliver findings that are difficult to hear. That is exactly what you need. The auditors most likely to protect your protocol are the ones who look hardest for what is wrong.
Red Flag 5: No Remediation Review Included
An audit report without follow-up remediation review is significantly less valuable than one that includes it. The report identifies vulnerabilities. The remediation review confirms that those vulnerabilities have been correctly fixed.
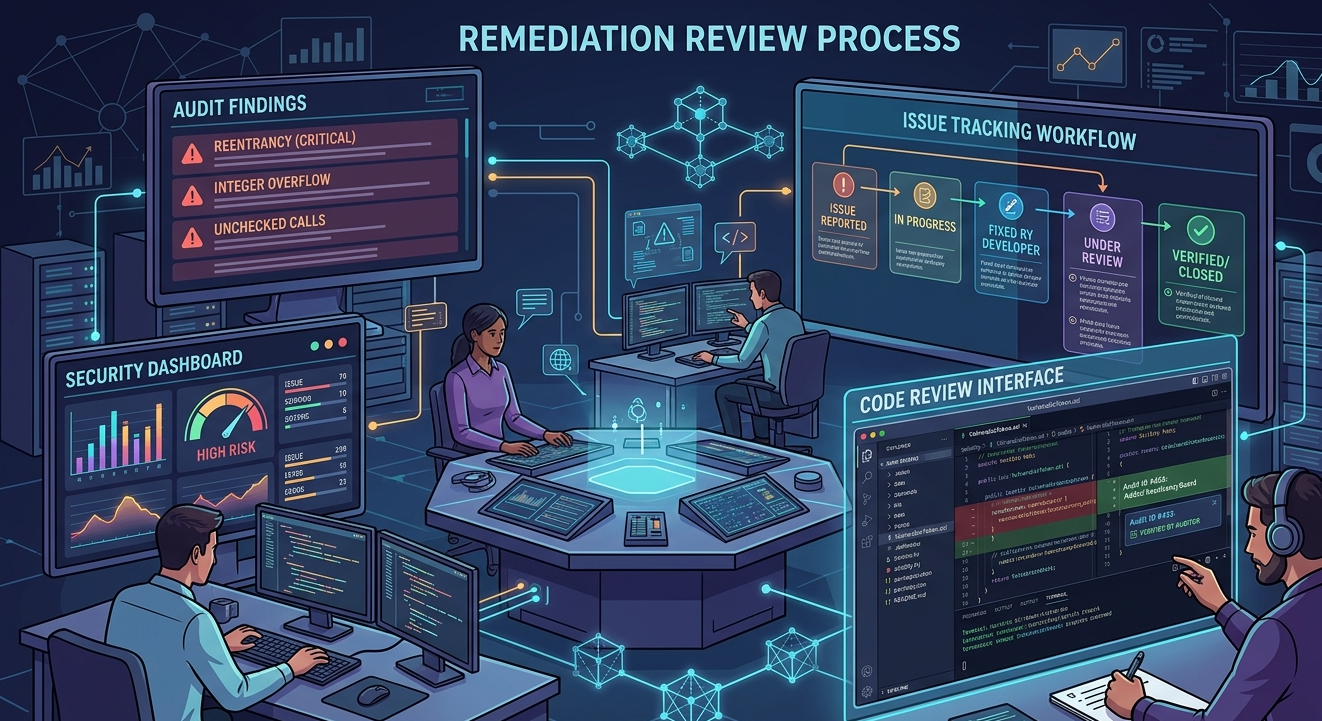
Firms that deliver a report and consider the engagement closed at that point are leaving a critical gap. Your developers may implement fixes that do not fully address the reported vulnerability. Without a qualified auditor verifying the fix, you have no reliable confirmation that the issue was actually resolved.
Ask every firm whether remediation review is included in the base price or charged separately. Understand how many rounds of remediation review are available. A single round may not be sufficient for protocols with significant findings.
Red Flag 6: No Discussion of Scope
Scope definition should be a substantive conversation between you and the audit firm before the engagement begins. If a firm accepts your scope description without pushback, questions, or suggestions, they are either not paying attention or not experienced enough to identify gaps.
Experienced auditors will ask questions. They will want to understand which contracts interact with each other, whether there are upgrade mechanisms, what external dependencies exist, and whether there are any components you are tempted to exclude from scope. They should push back on exclusions that represent meaningful risk.
A firm that rubber-stamps whatever scope you propose is optimizing for client satisfaction, not security. In smart contract security, those two things are sometimes in tension, and the right firm knows how to navigate that tension responsibly.
Red Flag 7: Overemphasis on Certifications and Partnerships
Certifications, partnerships, and award logos on a firm’s website can be genuine quality signals or pure marketing. The question is whether the firm can back those credentials with substance.
If a firm leads with certifications and struggles to articulate specific technical depth, that is a red flag. Certificates do not audit code. Auditors do. Ask to speak with the specific auditors who will be assigned to your project. Evaluate their expertise directly.
This is also relevant for firms that lead with the number of projects they have audited rather than the quality and depth of those audits. Volume is not a quality metric. A firm that has produced a thousand thin reports has not proven anything useful about their ability to find the vulnerabilities that matter most.
Red Flag 8: Pressure to Sign Quickly
Legitimate audit firms are busy. They have queue times. What they do not do is pressure you to sign immediately before you have had time to evaluate their proposal, review their track record, and ask your questions.
Aggressive sales tactics in the audit market, artificial scarcity claims, limited-time pricing, or urgency pressure are signals that the firm’s primary concern is closing the contract. Their secondary concern, if it exists at all, is the quality of the work.
Take the time you need to evaluate any firm properly. The few days you spend on due diligence are trivially cheap compared to the consequences of choosing the wrong partner.
Red Flag 9: Reports That Are Heavy on Formatting, Light on Depth
If a firm shares sample reports with you before engagement, read them carefully. A quality audit report provides specific, technically detailed descriptions of each vulnerability. It references exact file names, line numbers, and function names. It explains the execution path that leads to the vulnerability. It describes the conditions required for exploitation. It provides specific, technically sound remediation guidance.
Reports that are long on visual design, badge graphics, and generic security commentary but short on technical specificity are telling you something important. They are the output of a process optimized for looking thorough, not for being thorough.
The most valuable report you will ever receive might be an unglamorous document full of difficult findings described in precise technical language. That document is worth far more than a beautifully formatted report with no critical findings.
Protecting Your Protocol From the Start
The best time to build smart contract security into your protocol is before you ever engage an audit firm. Solidity Shield from SecureDApp gives development teams continuous automated vulnerability detection throughout the development process, not just at the end.
By maintaining security visibility at every stage of development, you arrive at the formal audit phase with a stronger codebase. Common patterns are already resolved. Your audit budget focuses on the complex logic and architectural issues that require expert human judgment. And you have documentation of your security practice that adds credibility to the audit process itself.
Choosing the right audit firm is essential. But building smart contract security into your development practice from day one is what makes that audit genuinely effective.
Frequently Asked Questions
What should I do if I have already hired a firm that shows these red flags?
Do not cancel immediately, but do increase your verification. Ask for more detailed methodology explanations. Review their draft findings carefully. Consider engaging a second firm for a limited targeted review of your most critical contracts. Make your decision about future engagements based on the quality of the work they actually deliver.
Are red flags different for large versus small audit firms?
The red flags are largely consistent across firm sizes. A large firm with a strong brand can still deliver shallow work. A small firm with exceptional talent can deliver outstanding depth. Evaluate based on specific evidence of capability, not on size or reputation alone.
How do I verify that a firm’s published reports reflect their real methodology?
Read the reports technically. Look for findings that demonstrate genuine logical understanding rather than pattern recognition. Look for clear descriptions of exploit paths, economic attack modeling, and substantive remediation guidance. Surface-level reports are relatively easy to identify once you know what depth actually looks like.
Is it worth getting a second opinion audit from a different firm?
For high-value protocols, yes. Multiple independent audits on the same codebase consistently produce different findings. The overlap and the differences are both valuable. What one auditor misses, another may catch. The incremental cost of a second audit is often small relative to the incremental coverage it provides.
How does Solidity Shield help me avoid needing to rely on potentially unqualified auditors?
Solidity Shield gives you direct visibility into your codebase’s vulnerability profile throughout development. When you arrive at a formal audit already having addressed the automated detection findings, you can evaluate an audit firm’s manual review quality more effectively, because you have a baseline against which to compare their findings.



