Identity has always been the first line of defense in enterprise security. Yet for decades, organizations have relied on centralized systems that concentrate risk, erode user privacy, and create single points of failure that attackers actively exploit. The emergence of Self-Sovereign Identity offers something fundamentally different: a model where individuals and organizations control their own credentials without depending on a central authority to validate who they are.
This is not a distant concept. Enterprises in financial services, healthcare, government, and Web3 are already deploying Self-Sovereign Identity infrastructure today. The question is no longer whether SSI is viable. The real question is how to implement it effectively without disrupting existing workflows, violating compliance mandates, or creating new attack vectors in the process.
This guide is designed for CTOs, CISOs, and architects who need a clear, practical framework for bringing SSI into production environments.
What Self-Sovereign Identity Actually Means for Enterprises
Self-Sovereign Identity is a model in which a user or organization owns, holds, and controls their digital identity credentials independently of any centralized registry. Instead of logging into a platform that holds your identity data on its servers, you carry cryptographically verifiable credentials in a digital wallet. Verifiers can confirm authenticity without contacting the issuer directly.
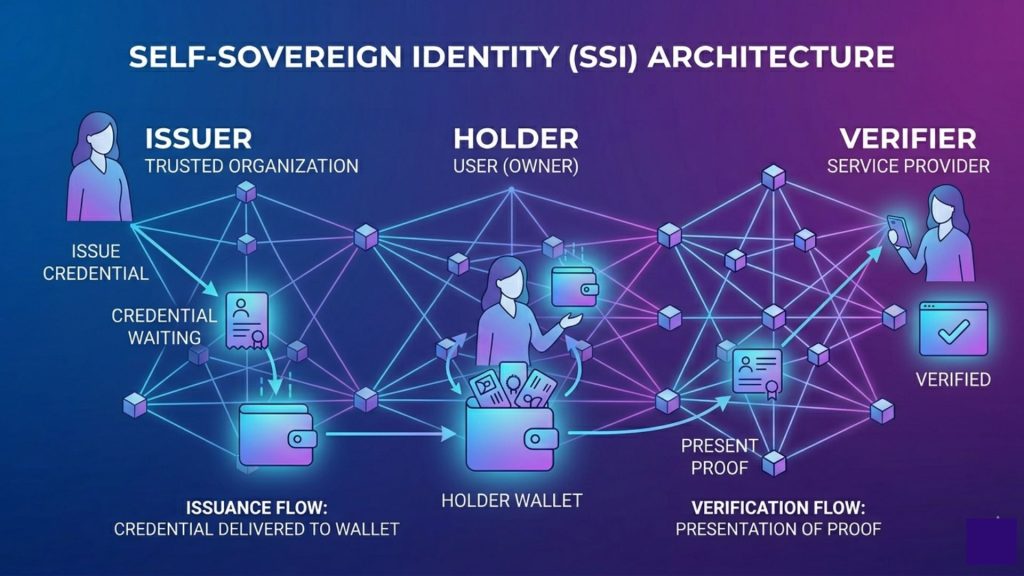
Three components form the backbone of SSI architecture:
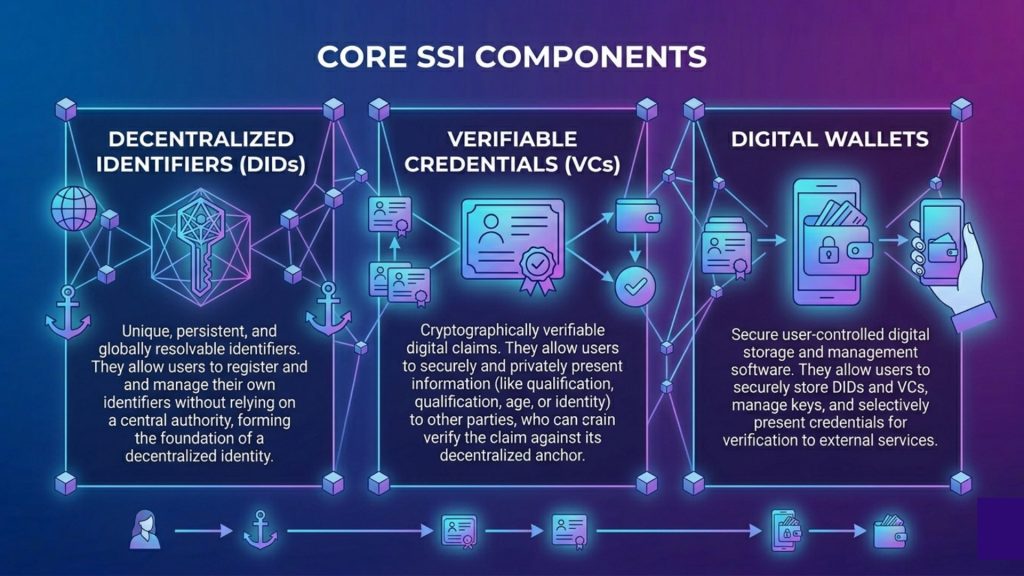
Decentralized Identifiers (DIDs): These are unique, globally resolvable identifiers anchored to a decentralized ledger or peer-to-peer system. A DID looks structurally similar to a URL but resolves to a DID Document that contains public keys and service endpoints. Critically, no single organization owns the namespace.
Verifiable Credentials (VCs): These are digitally signed, tamper-evident claims made by one party about another. An employer can issue a VC certifying employment status. A university can issue a VC confirming a degree. The holder stores these credentials and presents them selectively.
Digital Wallets and Agents: These are the software components that manage credential storage, cryptographic operations, and protocol-level communication. In enterprise environments, wallets may be managed by the organization on behalf of employees or by individuals on personal devices.
The key insight here is that verification happens cryptographically, not through a live database lookup. This fundamentally changes the trust model compared to federated identity systems like SAML or OAuth.
Why Centralized Identity Infrastructure Is a Growing Liability
Most enterprises still operate on identity frameworks built in the early 2000s. Active Directory, LDAP, SAML federations, and OAuth flows have served reasonably well, but they carry structural weaknesses that modern threat actors understand deeply.
Consider the attack surface: a central identity provider is not just a single point of failure, it is a high-value target. When a large identity provider is compromised, every relying party downstream is affected simultaneously. The 2020 SolarWinds breach illustrated this vividly. Attackers moved laterally across networks by exploiting trusted identity tokens, not by breaking encryption.
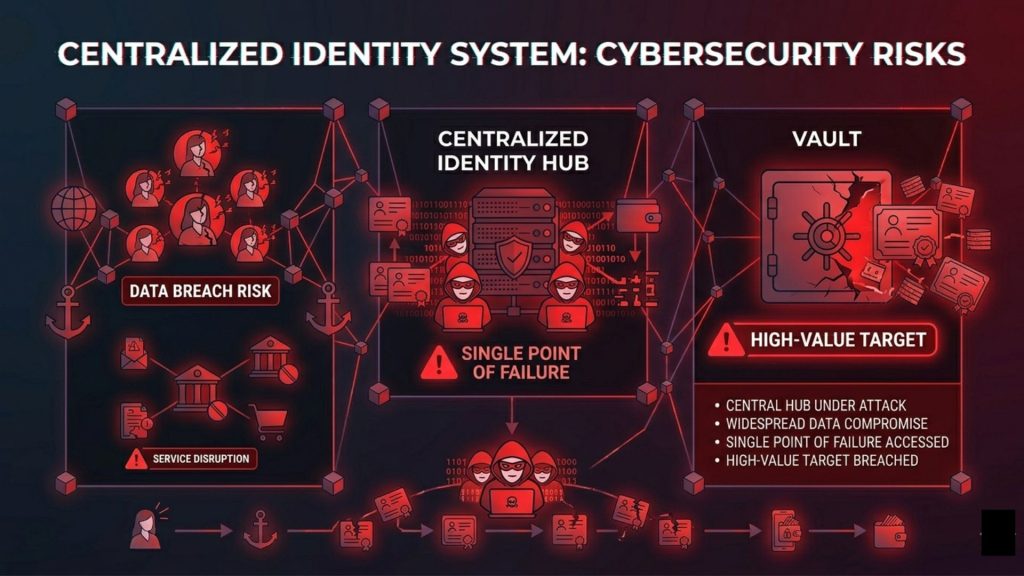
Beyond security, there is the compliance dimension. Regulations like GDPR in Europe, PDPB in India, and CCPA in California impose increasingly strict requirements around how personal data is stored, processed, and shared. Centralized identity databases create regulatory exposure almost by design. Every time a user authenticates, metadata is generated. Every time credentials are verified, data flows across organizational boundaries. SSI architectures shift this fundamentally by minimizing data sharing to only what is necessary for each transaction.
The third pressure point is user friction. Enterprise employees manage dozens of credentials across internal tools, partner portals, and cloud platforms. Password fatigue is real, and its downstream effects on security hygiene are well documented. SSI, when properly implemented, enables employees to authenticate once and carry verified credentials across any platform that supports the standard, without repetitive logins or centralized password vaults that represent yet another attack surface.
Core Standards Every Enterprise Team Must Understand
Before any implementation begins, your architecture team needs to be aligned on the standards landscape. SSI is not a single protocol. It is a family of interoperable specifications.
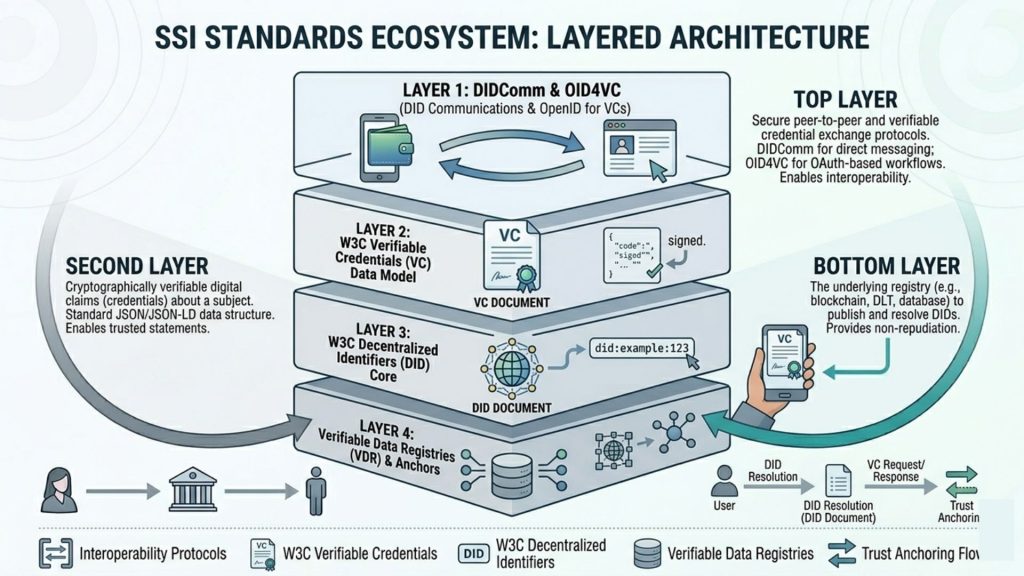
W3C DID Core Specification defines the data model and syntax for Decentralized Identifiers. This is the foundational layer. When you anchor a DID to a distributed ledger like Ethereum, Hyperledger Indy, or a blockchain-based trust registry, you are following this specification.
W3C Verifiable Credentials Data Model defines how credentials are structured, signed, and presented. Credentials can use JSON-LD or JWT formats, depending on your interoperability requirements. Enterprises dealing with cross-border compliance often prefer JSON-LD for its semantic richness.
DIF DIDComm Messaging provides the protocol layer for how SSI agents communicate. It enables encrypted, authenticated messaging between wallets without relying on centralized messaging infrastructure.
OpenID for Verifiable Credentials (OID4VC) is gaining significant momentum as it bridges SSI with existing OpenID Connect infrastructure. For enterprises that have already invested heavily in OIDC-based authentication, OID4VC provides a practical migration path.
EBSI (European Blockchain Services Infrastructure) is worth monitoring for enterprises operating in or with European partners. It provides a cross-border trust framework specifically designed for government and enterprise use cases.
Understanding which standards apply to your use case determines every architectural decision downstream, from wallet selection to ledger choice to credential schema design.
Designing Your SSI Architecture: A Phased Approach
Enterprises that have successfully deployed SSI share a common pattern: they started small, proved value in a contained use case, then expanded methodically. Organizations that tried to rearchitect their entire identity stack at once uniformly struggled.
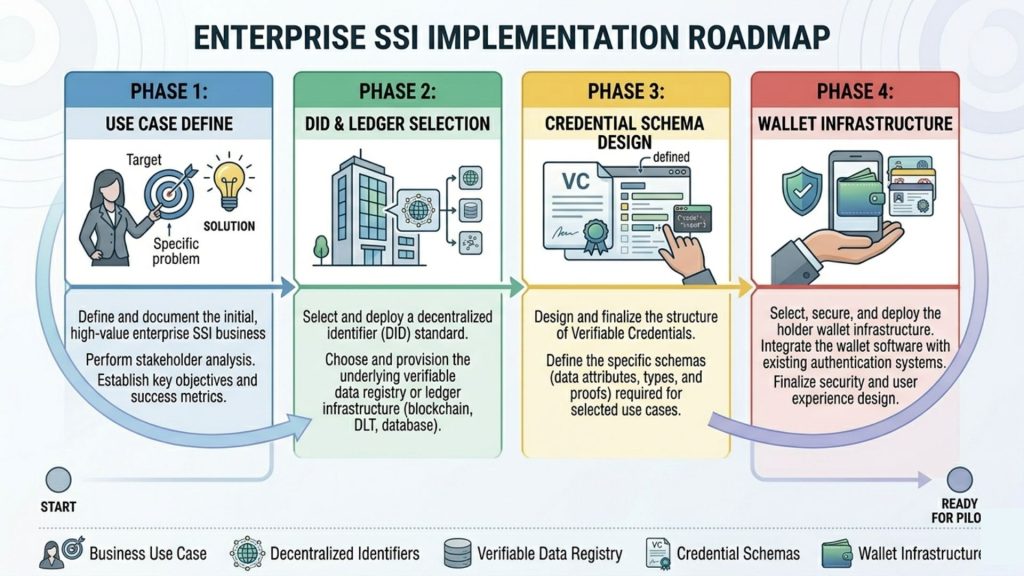
Phase 1: Define the Use Case and Trust Triangle
Every SSI deployment involves three roles: issuers, holders, and verifiers. Before writing a single line of code, your team needs to map these explicitly for the target use case.
A practical first use case for most enterprises is employee credential issuance. HR issues a verifiable credential attesting to employment status and role. The employee holds this in a corporate wallet. Internal systems, partner portals, or regulatory bodies can verify the credential without calling back to HR systems in real time.
This use case is valuable because it has clear boundaries, involves a controlled set of participants, and provides immediate operational value without requiring external ecosystem adoption.
Phase 2: Choose Your DID Method and Ledger
Not all DID methods are equal, and the wrong choice creates technical debt. Key considerations include:
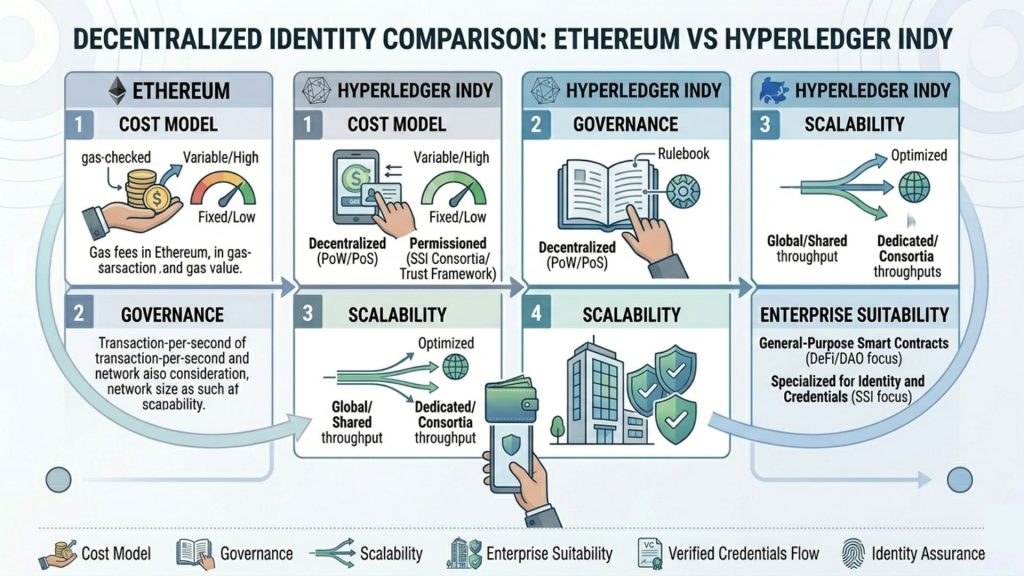
Write costs: Public blockchains like Ethereum incur gas fees per DID registration. For enterprise scale, this matters operationally. Hyperledger Indy, by contrast, is permission-based and purpose-built for identity, making it a popular choice for enterprise deployments.
Governance: Who controls the ledger? Public networks offer censorship resistance but limited governance control. Consortium ledgers offer more organizational control but require trust in the consortium.
Revocation support: Credentials get revoked. Your DID method must support efficient revocation without creating privacy leakage. Status List 2021, developed by the W3C Credentials Community Group, is currently the most practical revocation mechanism for enterprise deployments.
Resolution speed: DID resolution must be fast enough for real-time authentication flows. Cached resolvers and local DID documents help, but the base resolution latency of your chosen ledger matters.
Phase 3: Credential Schema Design
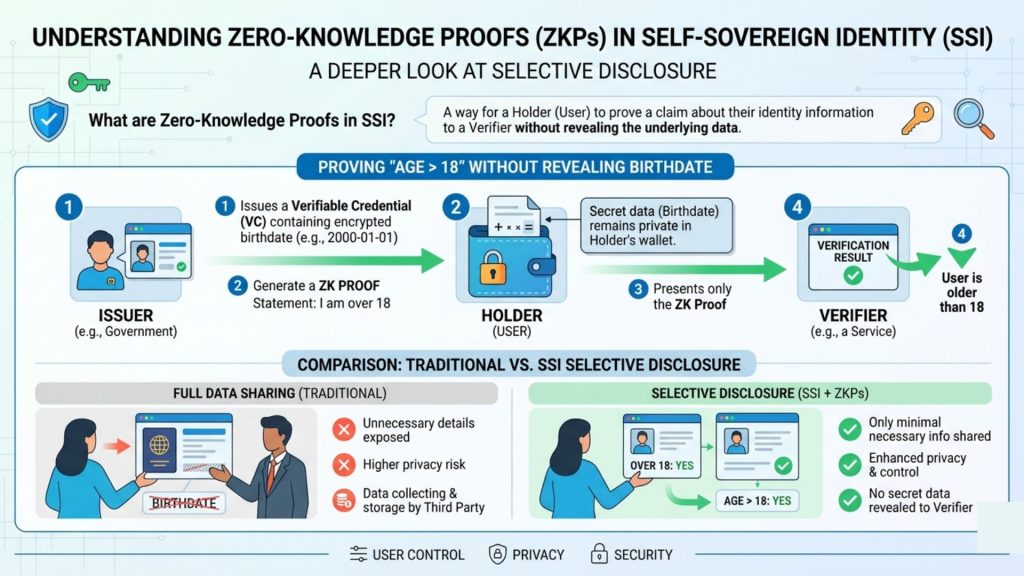
Poorly designed credential schemas create interoperability problems that compound over time. Schemas should be minimal, only including claims that are necessary for the verifier to fulfill their purpose. This is the principle of selective disclosure operationalized at the data model level.
Zero-knowledge proofs (ZKPs) take this further. With ZKP-enabled credentials, a holder can prove they satisfy a condition, such as being over 18, without revealing the underlying birthdate. For use cases involving sensitive personal data, ZKP support is increasingly a requirement, not a nice-to-have.
Phase 4: Wallet Infrastructure
Enterprise wallet decisions fall into two categories: organization-managed wallets deployed on behalf of users, and individual wallets held on personal devices.
Organization-managed wallets reduce user burden but centralize some custody. Individual wallets maximize user sovereignty but introduce device management complexity. A hybrid model, where the organization issues credentials but employees hold them in personal wallets, often provides the best balance for most enterprise environments.
When evaluating wallet solutions, assess cryptographic key management carefully. Hardware security module (HSM) integration, key recovery mechanisms, and multi-device synchronization are not optional features in enterprise deployments. They are operational requirements.
Identity Verification in Decentralized Environments: The SecureX DID Angle
As enterprises evaluate decentralized identity solutions, one of the more practically significant developments in the Indian market is the emergence of Secure X-DID, a decentralized identity solution developed by SecureDApp that has received OVIS SE certification from UIDAI, the Unique Identification Authority of India. This kind of regulatory recognition matters enormously for enterprise procurement, because it signals that the solution has passed scrutiny within a national identity framework, rather than operating purely in an unregulated experimental space.
For enterprises operating in regulated environments, this distinction is not trivial. A decentralized identity solution that exists outside any recognized certification framework creates compliance ambiguity. One that has been formally evaluated within an established trust framework provides a foundation that procurement and legal teams can work with.
The broader lesson here is that SSI adoption at enterprise scale requires solutions that bridge decentralized principles with regulatory acceptance. That intersection is where enterprise-grade decentralized identity infrastructure is actually being built.
Integration Patterns for Enterprise Environments
SSI does not replace your existing infrastructure overnight. The practical path forward involves integration patterns that allow SSI to coexist with and gradually supplant legacy identity systems.
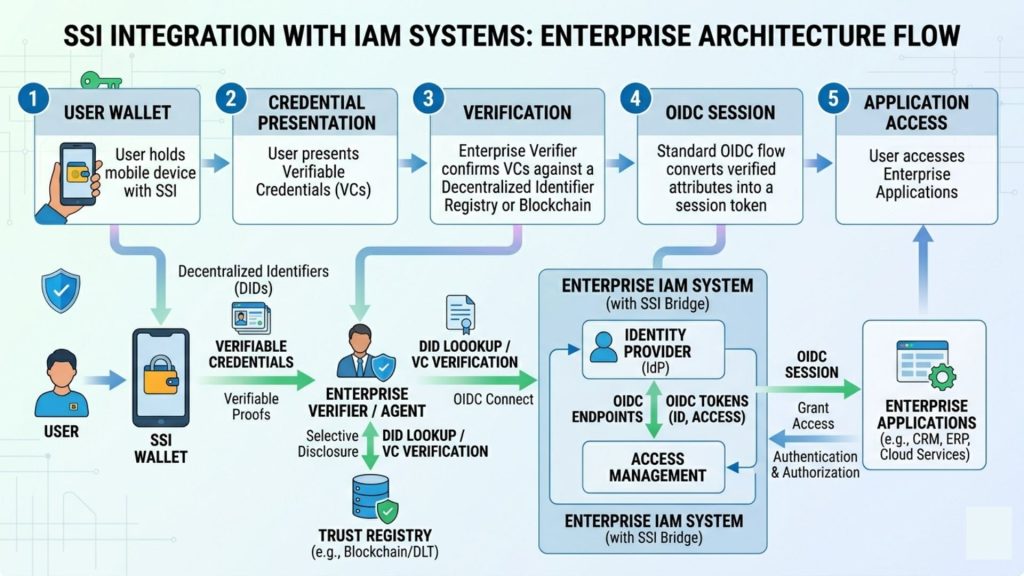
SSI as an Authentication Layer: SSI credentials can be integrated as an additional authentication factor into existing OIDC flows. A user presents a verifiable credential, the verifier confirms its cryptographic validity, and the result feeds into the existing session management system. This pattern requires minimal changes to downstream applications while introducing SSI at the authentication layer.
SSI for Cross-Organizational Trust: Partner ecosystems often struggle with identity federation across organizational boundaries. Each partner maintains its own identity system, and cross-org access requires complex trust agreements and federation configurations. SSI simplifies this significantly. An employee presents organization-issued credentials to a partner system, and verification happens cryptographically without requiring pre-established federation infrastructure.
SSI for KYC and Compliance Workflows: Financial services enterprises are exploring SSI as a mechanism for portable KYC. A user completes a KYC verification with one institution. That institution issues a verifiable credential attesting to the KYC result. The user can then present this credential to another institution, which can verify its authenticity and rely on the attested KYC without redoing the full process. This reduces onboarding friction while maintaining compliance audit trails.
SSI for Supply Chain Provenance: Enterprises with complex supply chains are using verifiable credentials to attest to product origin, certification status, and chain of custody. Each actor in the supply chain holds and presents credentials that verifiers in the next stage can confirm without relying on centralized registries.
Security Considerations That Often Get Overlooked
The decentralized architecture of SSI shifts some attack surfaces while introducing new ones. Enterprise security teams need to understand both dimensions.
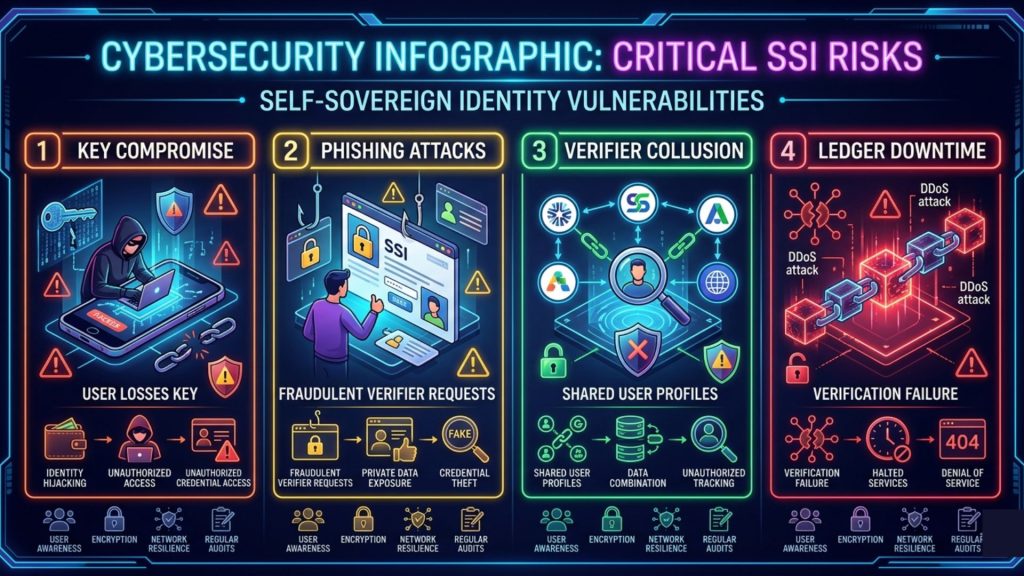
Key compromise is the critical threat. In SSI, private keys are the identity. If an employee’s private key is compromised, an attacker can present legitimate-appearing credentials until revocation occurs. Fast revocation infrastructure and clear incident response protocols for key compromise are therefore essential.
Verifier collusion creates correlation risk. If multiple verifiers share presentation data, they can correlate user activity across services even without access to a central identity database. Enterprises deploying SSI for their customers or employees should evaluate verifier data minimization policies carefully.
Phishing attacks target wallet interactions. A credential presentation flow can be spoofed to trick users into presenting credentials to malicious verifiers. User education and wallet-level anti-phishing mechanisms are necessary controls.
Ledger availability affects resolution. If your chosen DID ledger experiences downtime, DID resolution fails, and credential verification may not be possible. Enterprises need availability SLAs for their DID infrastructure, just as they do for any other critical authentication service.
Furthermore, as decentralized identity infrastructure grows more complex, the attack surface around credential issuance and wallet security warrants continuous monitoring. Solutions that provide real-time visibility into credential activity, anomaly detection, and chain-level forensic capability become operationally relevant as SSI deployments mature. This is the same principle that applies to smart contract security: pre-deployment verification matters, but runtime monitoring is what catches threats that static analysis misses.
Governance: The Non-Technical Barrier That Kills SSI Projects
Technical architecture is often not the hardest part of enterprise SSI implementation. Governance is.
Establishing a trust registry requires organizational decisions about who can be an issuer, what credential schemas are authoritative, and how disputes about credential authenticity are resolved. These are governance questions, not technical ones, and they require legal, compliance, and executive alignment that takes time to build.
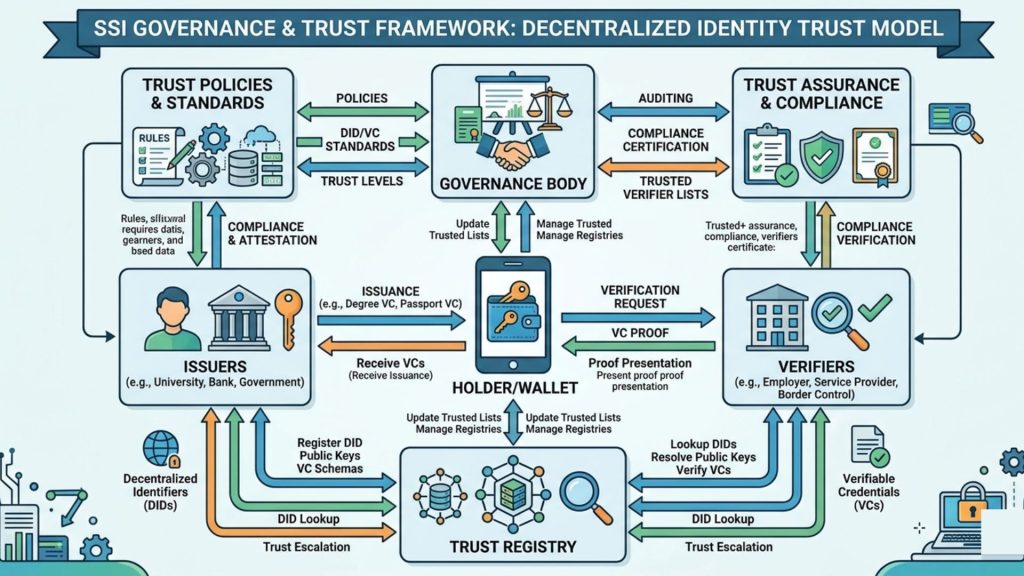
Enterprises that succeed with SSI typically establish a governance working group early, before technical architecture decisions are finalized. This group defines the trust framework: which organizations are recognized issuers, what schemas are standardized, what liability applies when a verifiable credential is found to be fraudulent, and how credential revocation is communicated.
For enterprises entering cross-industry or cross-border SSI ecosystems, aligning with existing governance frameworks like the Trust over IP (ToIP) Foundation’s layered governance model provides a useful starting point. Building from scratch introduces unnecessary risk and slows ecosystem adoption.
Measuring Implementation Success
Enterprise SSI projects need clear success metrics aligned to business outcomes, not just technical milestones.
Operational metrics worth tracking include credential issuance volume, verification latency, revocation response time, and wallet adoption rates among target user populations. These indicate whether the system is functioning as designed.
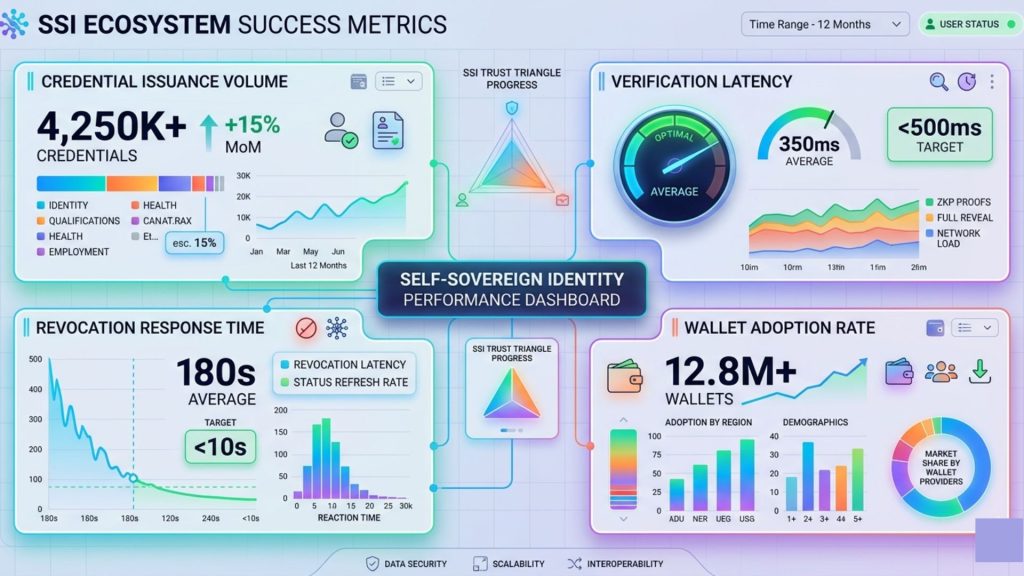
Business outcome metrics should include reduction in identity-related support tickets, decrease in phishing incident rates linked to authentication vulnerabilities, time-to-onboard reduction for new employees or partners, and compliance audit efficiency improvements.
Security metrics should capture key rotation frequency, failed verification rate anomalies, and revocation coverage for departing employees or expired credentials.
Tracking these consistently from early deployment creates the evidence base needed to justify broader rollout and continued investment.
What Enterprise Leaders Need to Know Going Into 2025 and Beyond
The SSI ecosystem is maturing quickly. Several developments are worth tracking closely.
The European Digital Identity Wallet initiative, mandated under eIDAS 2.0, requires EU member states to provide citizens with digital wallets by 2026. This is creating significant demand for SSI-compatible infrastructure across European enterprise ecosystems and has accelerated standards development noticeably.
In India, the digital identity landscape is evolving rapidly. UIDAI’s ongoing work with certified decentralized identity solutions signals a regulatory environment that is increasingly receptive to SSI-aligned architectures, particularly where privacy-preserving verification is valued.
The convergence of SSI with AI-driven systems is also worth monitoring. As automated systems increasingly make decisions based on digital identity data, the auditability and cryptographic verifiability that SSI provides becomes more operationally valuable. Knowing that a credential was issued by a specific authority, at a specific time, to a specific entity, and that it has not been revoked, provides a level of audit confidence that session-based authentication simply cannot match.
Conclusion
Self-Sovereign Identity represents a fundamental shift in how enterprises think about digital trust. It moves identity from a centralized service that organizations control to a distributed capability that individuals and entities hold directly. That shift has profound implications for security architecture, compliance posture, user experience, and cross-organizational collaboration.
The path to enterprise SSI is not a single leap. It is a phased progression from understanding the standards landscape to piloting a bounded use case, governing the trust framework, integrating with existing infrastructure, and gradually expanding as ecosystem adoption matures.
What makes this moment particularly significant is that the standards have stabilized, regulatory frameworks are actively recognizing SSI-aligned architectures, and enterprise-grade tooling has reached a level of maturity that makes production deployment practical rather than experimental.
Organizations that begin building SSI capability now are positioning themselves ahead of an identity paradigm shift that is already underway. Those that wait are building technical debt into an infrastructure layer that will become increasingly costly to modernize as the ecosystem around them evolves.
The implementation complexity is real, but manageable with the right architecture, the right governance approach, and the right tools. The starting point is simply deciding which use case to prove first.
Frequently Asked Questions
What is Self-Sovereign Identity in simple terms?
Self-Sovereign Identity is a model where individuals and organizations control their own digital credentials without relying on a centralized authority to store or validate their identity data. You hold your credentials; others verify them cryptographically.
How is SSI different from federated identity systems like SAML or OAuth?
Federated identity systems depend on a central identity provider that stores user data and validates it during every interaction. In contrast, SSI removes this dependency. Instead, issuers provide credentials once, users store them in their wallets, and verifiers check them directly using cryptographic proofs. As a result, no real-time call to the issuer is required.
What blockchain should enterprises use for SSI?
There is no single correct choice. For example, Hyperledger Indy works well for enterprise SSI because it was designed specifically for identity. On the other hand, Ethereum and similar public blockchains offer wider interoperability. Therefore, enterprises should choose based on governance needs, transaction costs, and ecosystem fit.
What is a Decentralized Identifier (DID)?
A DID is a unique identifier that an individual or organization fully controls without relying on a central authority. It links to a DID Document that contains cryptographic keys and verification methods. In simple terms, DIDs form the foundation on which verifiable credentials operate.
How does credential revocation work in SSI?
Revocation methods differ across implementations. For instance, Status List 2021 uses a bit-string hosted at a known URL to show whether a credential is valid. Meanwhile, zero-knowledge-based revocation improves privacy because it avoids revealing which exact credential was checked. As a result, users maintain better control over their data.
Is SSI compliant with GDPR?
SSI aligns well with GDPR principles such as data minimization, purpose limitation, and user control. However, challenges arise if systems store personal data directly on an immutable blockchain. To avoid this, most implementations keep personal data off-chain and store only cryptographic proofs on-chain. This approach ensures better compliance.
How do enterprises handle lost or compromised wallets?
Enterprises address this risk through structured recovery mechanisms. For example, they may use custodial recovery, threshold cryptography, or hardware-backed key storage. In addition, organizations must define clear incident response processes before deployment to handle key loss or compromise effectively.
What is the role of zero-knowledge proofs in enterprise SSI?
Zero-knowledge proofs allow users to prove a claim without exposing the underlying data. For example, an employee can prove access rights without revealing their job title. Similarly, a user can confirm age eligibility without sharing their birthdate. Therefore, ZKPs play a critical role in privacy-focused enterprise use cases.
How does SSI interact with existing IAM systems?
SSI does not replace IAM systems overnight. Instead, it integrates with them through standards like OID4VC, which connects SSI with existing OIDC infrastructure. Typically, organizations use SSI as an authentication layer while continuing to rely on existing systems for session management.
What is a verifiable credential schema, and why does it matter?
A schema defines the structure of a credential, including its fields, data types, and meaning. Strong and consistent schemas ensure interoperability between issuers and verifiers. Without proper governance, poor schema design can create fragmentation and reduce the overall effectiveness of SSI ecosystems.
How long does an enterprise SSI implementation typically take?
A focused pilot, such as employee credential issuance, usually takes three to six months from design to production. However, broader deployments involving multiple use cases and external partners can take twelve to twenty-four months. These rollouts typically follow a phased approach.
What governance structure does an SSI deployment require?
Every SSI deployment needs a clear trust framework. This framework defines who can issue credentials, which schemas are valid, and how disputes are resolved. To simplify this process, many enterprises adopt established models like those from the Trust over IP Foundation.
What are the main security risks in SSI systems?
The biggest risk is key compromise because private keys represent identity. In addition, systems may face risks such as verifier collusion, phishing attacks targeting wallets, and ledger availability issues. Therefore, strong key management and monitoring are essential.
Can SSI be used for machine-to-machine authentication?
Yes, SSI supports machine identities as well. Organizations can assign DIDs to systems and services, not just individuals. As a result, machines can present verifiable credentials during API calls or service interactions, offering stronger security than traditional API keys or shared secrets.



