When a blockchain exploit happens, the clock starts immediately.
Funds move. Wallets rotate. Bridges get crossed. Within hours, stolen assets can be fragmented across dozens of addresses, converted into different tokens, and pushed through mixing protocols designed to sever the transaction trail. By the time most teams realize what happened, the attacker has already built significant distance between the initial exploit and the current location of the funds.
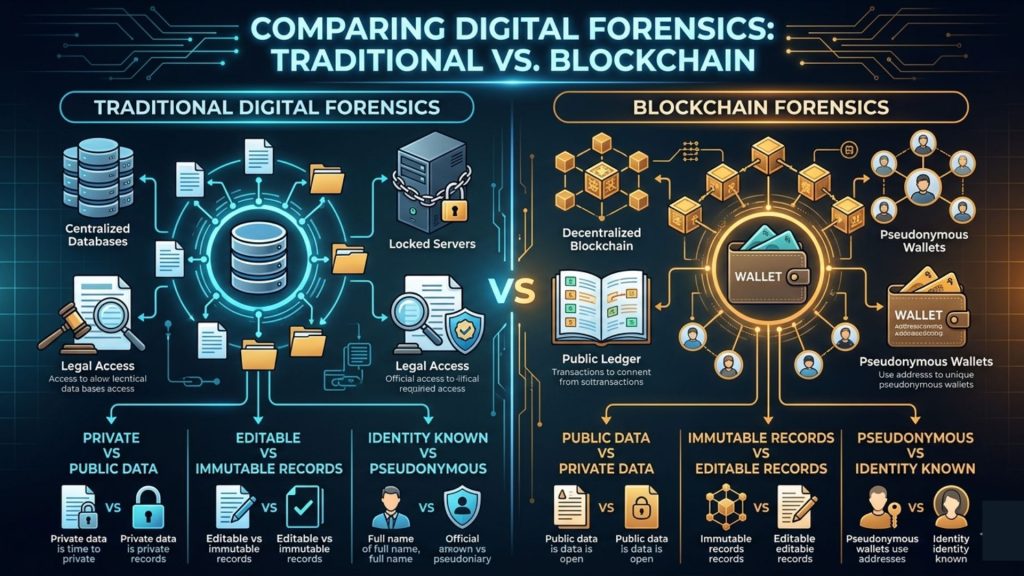
This is the environment in which a blockchain forensic investigation operates. Unlike traditional financial fraud, where evidence typically sits in centralized databases accessible through legal process, blockchain forensics works in a system that is public but pseudonymous. Every transaction is recorded permanently. Not all of it is easy to interpret, attribute, or act on.
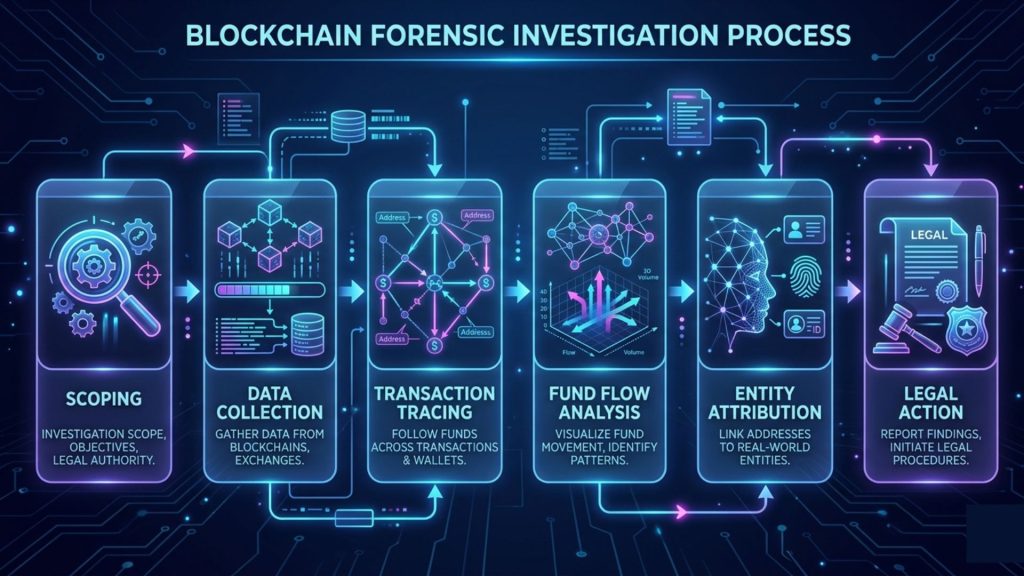
A well-conducted blockchain forensic investigation combines on-chain data analysis, fund flow tracing, entity attribution, behavioral pattern recognition, and in many cases, coordination with exchanges and regulatory bodies. This guide walks through that process from start to finish, covering the methodology, the tooling, the legal dimensions, and the factors that determine whether an investigation produces outcomes that actually matter.
What a Blockchain Forensic Investigation Actually Involves
There is a widespread misconception that blockchain forensics is simply a matter of following transactions on a block explorer. In straightforward wallet compromise cases, a basic trace is useful. In the cases that carry real financial and legal consequence, the investigation is considerably more involved.
A proper blockchain forensic investigation goes well beyond reading transaction hashes. It reconstructs the full sequence of events surrounding an incident, identifies every address involved at each stage, attributes those addresses to real-world entities where possible, and builds a documented evidentiary chain that can support legal proceedings, regulatory reporting, or insurance claims.
The scope varies significantly depending on the nature of the incident. A private key compromise has a different investigative profile than a smart contract exploit. A rug pull differs from a flash loan attack. A governance manipulation differs from both. Each category involves distinct transaction patterns, different timeframes, and different evidence priorities.
Insight: Blockchain forensics is not just about tracing where funds went. It is about reconstructing why they moved, how the attacker operated, and what evidence can be preserved before the trail deteriorates through mixing, bridging, or liquidation.
Understanding the incident type before committing to an investigative approach saves time and significantly improves the quality of findings. Investigators who apply a generic methodology regardless of incident type consistently miss the signals that would have mattered most.
Before You Begin: Scoping the Investigation
Every effective blockchain forensic investigation starts with a clearly defined scope. Jumping into transaction tracing without establishing what you are trying to answer is one of the most costly mistakes teams make under the pressure of an active or recent incident.
Define the Incident Boundaries
Start by identifying the time window of the incident as precisely as possible. Most blockchain exploits have a discrete start point, which is the first anomalous transaction, and a clear endpoint, which is the final fund movement or the block at which the attacker’s visible activity ceased. Anchoring your investigation to specific block heights gives you a manageable dataset and prevents the scope from expanding without direction.
Identify the Entry Points
Determine which contracts, wallets, or functions were involved. For smart contract exploits, this typically means identifying the exploited function and the contract address. And for wallet compromises, it means identifying the compromised address and the first unauthorized transaction. For governance attacks, it means mapping the full proposal and voting transaction sequence.
Establish the Investigation Objectives
Clarify upfront what the investigation needs to produce. Is the goal to recover funds? To identify the attacker for law enforcement referral? Or to satisfy an insurance claim? To produce a credible post-mortem for users and stakeholders? Each objective shapes which evidence you prioritize and how findings need to be documented.
Without clear objectives, investigations tend to expand indefinitely as analysts follow interesting threads that don’t ultimately serve the outcome anyone needs.
Phase 1: On-Chain Data Collection and Preservation
Blockchain data is immutable, which gives forensic investigations a significant structural advantage over traditional digital forensics. The transaction record cannot be altered after the fact. However, the context surrounding that record, including off-chain interface logs, communications, and exchange data, is not immutable and should be preserved as early as possible.
Collect the Full Transaction History
Export the complete transaction history for all addresses identified in your initial scope. Importantly, include internal transactions and token transfers, not just native currency movements. A significant portion of fund flows in DeFi incidents happen through ERC-20 transfers and internal contract calls that don’t appear in standard transaction lists on most explorers.
Pay close attention to transaction timing relative to block timestamps. Coordinated attacks frequently involve transactions submitted in rapid succession or within a single block. Timing patterns can reveal intentionality and coordination that individual transaction analysis would miss entirely.
Map the Smart Contract Interactions
For contract-level exploits, reconstruct the exact sequence of contract calls. Identify which functions were invoked, in what order, with what parameters, and what state changes resulted from each call. This sequence forms the technical core of the exploit narrative and establishes the basis for understanding both what happened and how it was engineered.
Decoding contract interactions requires ABI data for the contracts involved. When contracts are unverified, investigators may need to work with bytecode-level analysis or function signature databases to identify the methods being called.
Preserve Event Logs
Smart contract event logs are frequently the richest source of investigative data in DeFi incidents. Events such as Transfer, Approval, Swap, Borrow, and protocol-specific custom events capture the semantic meaning of what was happening at each stage of the attack. Collect and timestamp all relevant event logs from the incident window before moving to the analysis phase.
Phase 2: Transaction Tracing and Fund Flow Analysis
With data collected, the investigative focus shifts to mapping where funds actually moved. This is the phase most people associate with blockchain forensics, and it is where the real complexity begins.
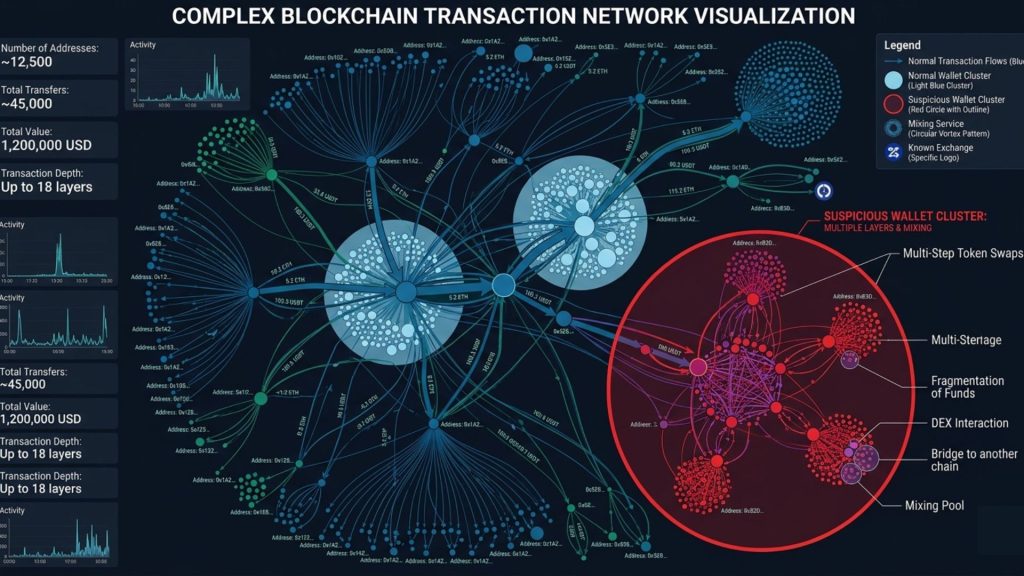
Build the Transaction Graph
Construct a directed graph of address-to-address fund flows starting from the point of the exploit and following assets forward through time. Each node in the graph represents a wallet address or contract. Each edge represents a transaction or token transfer. The objective is to trace stolen assets from their origin through every intermediate address to their current location or the point at which they were liquidated.
In practice, attackers rarely move funds in a straight line. Expect to see assets split across multiple addresses, consolidated and re-split, and routed through protocols specifically chosen to complicate tracing. Systematic enumeration of every branch in the graph, even the ones that appear to dead-end, is what separates thorough investigations from superficial ones.
Identify Address Clustering Patterns
Address clustering is a technique for grouping addresses that are likely controlled by the same entity. Common indicators include addresses funded from the same source, addresses that transact together consistently, addresses with similar creation timing, and addresses that participate in the same coordinated transaction sequences.
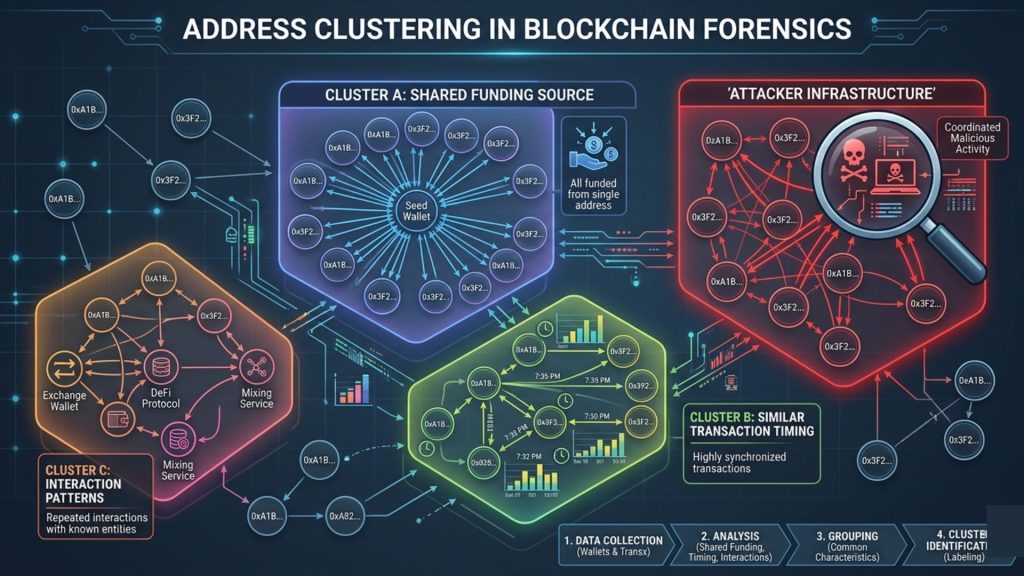
Clustering expands the investigative picture beyond individual addresses to the broader wallet infrastructure the attacker used. This often surfaces preparation activity, test transactions, and additional addresses that were involved in the attack but weren’t immediately visible from the initial trace.
Track Cross-Chain Movements
Modern attacks frequently involve cross-chain fund movements through bridge protocols. When funds cross chains, the investigative trail doesn’t end, but it does shift to a different blockchain requiring different tooling and data sources. Tracking cross-chain movements means identifying bridge deposit transactions, matching corresponding withdrawal events on the destination chain, and continuing the trace from there.
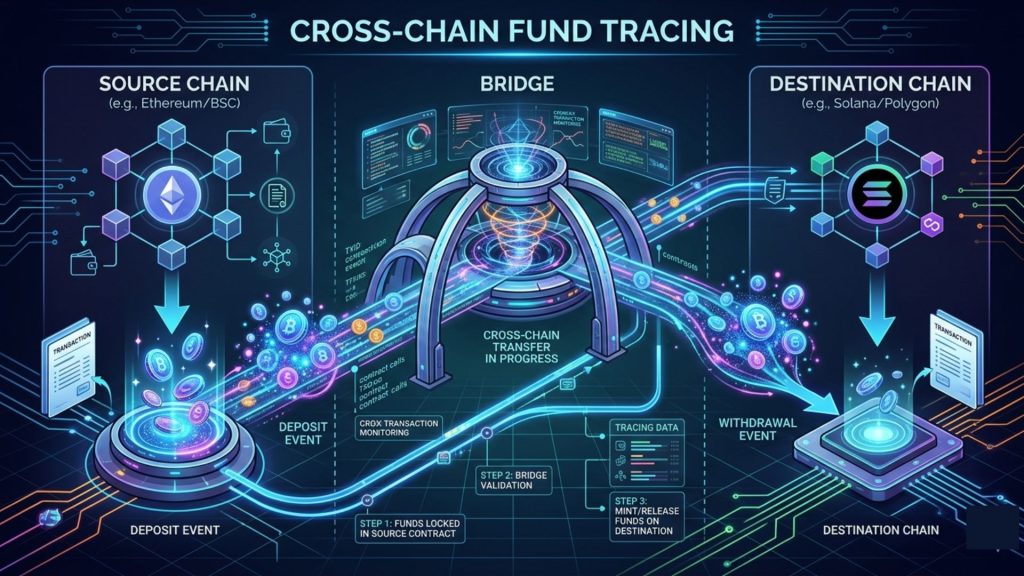
Insight: A fund trace that stops at a bridge is an incomplete investigation. Cross-chain tracing is a baseline competency for any serious blockchain forensic investigation in 2026. Attackers use bridges specifically because they know many teams cannot follow them there.
Phase 3: Entity Attribution and Identity Investigation
Tracing funds reveals where assets went. Attributing addresses to real-world entities is the dimension that enables legal action and actual fund recovery. These are distinct activities that require different methods and different data sources.
Exchange and Custodian Interactions
When traced funds reach a centralized exchange or custodian, the investigative path intersects with entities that hold verified identity data. Identifying the specific deposit address and the timestamp of that deposit creates the evidentiary basis for a legal request or law enforcement referral that may ultimately identify the account holder behind the wallet.
This step requires careful documentation. Exchanges almost universally require a formal legal process before disclosing account information. The forensic investigation provides the on-chain evidence necessary to initiate and support that process.
On-Chain Behavioral Signals
Even without KYC data, on-chain behavioral patterns often yield meaningful attribution signals. Wallet activity prior to the incident, participation in specific protocols, governance voting history, NFT holdings, and social coordination patterns can collectively build a behavioral profile that either points to a known entity or narrows the attribution field meaningfully.
In a notable portion of cases, attackers reuse infrastructure. A wallet that participated in a previous exploit, or that interacted with a known entity address before the attack, can provide attribution threads not visible from the attack transactions alone.
Off-Chain Intelligence Correlation
Effective entity attribution frequently incorporates off-chain signals alongside on-chain data. These include IP addresses captured through protocol interfaces where the attacker may have interacted, social media patterns correlated with the incident timing, dark web intelligence about the attack, and coordination signals visible in public community channels.
This correlation work sits at the intersection of blockchain forensics and traditional digital investigation. The strongest attribution cases combine on-chain evidence with at least some corroborating off-chain signal.
The Tooling That Makes Blockchain Forensic Investigation Possible
A blockchain forensic investigation is only as effective as the tools and data infrastructure supporting it. The right tooling reduces the time required to trace complex fund flows and surfaces patterns that manual analysis would miss.
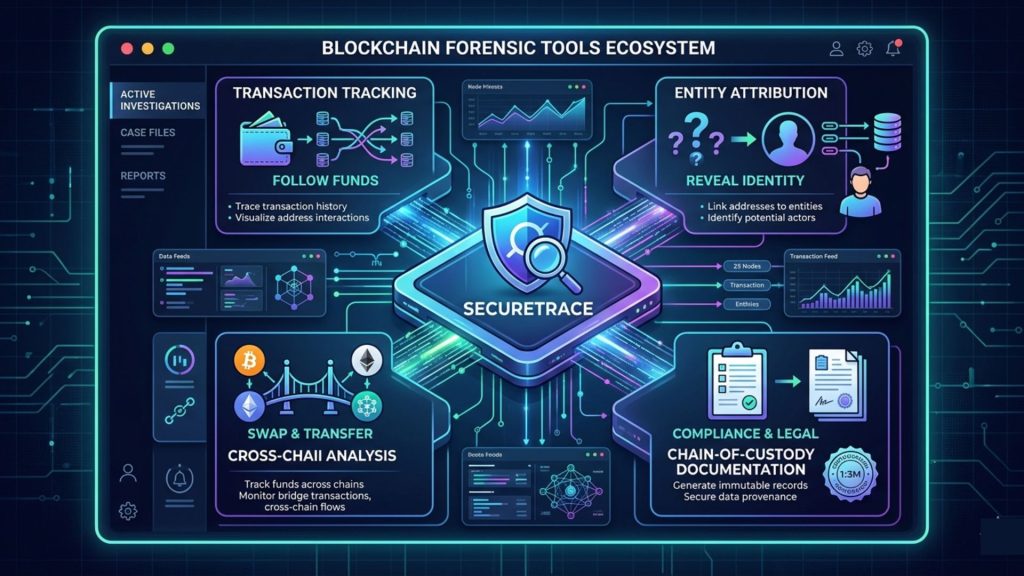
Transaction Tracing and Visualization Platforms
Dedicated blockchain investigation platforms provide graph-based visualization of transaction flows, automated address clustering, and entity labeling databases that identify known exchange addresses, mixer protocols, and flagged wallets. These capabilities significantly accelerate the fund tracing phase compared to working manually through block explorers.
Smart Contract Replay and Analysis Tools
For contract-level exploits, tools that can decode transaction calldata, trace internal calls, and reconstruct contract state at specific block heights are essential. Understanding exactly how a contract was exploited requires replaying the attack transaction against the state of the contract at the time it occurred.
Monitoring Data as Forensic Evidence
This is an insight that many teams overlook until after an incident has already occurred. Continuous monitoring systems that record on-chain activity in real time generate forensic-grade data as a byproduct of their normal operation. When an incident happens, that historical monitoring data becomes a primary evidence source for the investigation.
SecureTrace, SecureDApp’s transaction tracking and blockchain forensics tool, is built specifically for this kind of investigation work. It provides structured transaction tracking, chain-of-custody documentation, and data outputs designed to support both internal post-mortems and external legal proceedings. For teams that also run SecureWatch for continuous on-chain monitoring, the pre-incident behavioral data captured by SecureWatch adds significant investigative depth that would otherwise be unavailable.
The practical implication is clear: teams that operate continuous monitoring before an incident are in a fundamentally stronger investigative position than teams that begin collecting data only after the fact.
Cross-Chain Tracing Infrastructure
Given the frequency of cross-chain fund movements, investigation infrastructure needs to cover multiple chains natively. Tools that require entirely separate workflows for each chain create friction and increase the risk of losing the trail at a bridge handoff, which is precisely where attackers want to disappear.
A Practical Scenario: What a Blockchain Forensic Investigation Looks Like
Consider a mid-size lending protocol that detects unusual withdrawal activity on a weekend evening. Within forty minutes, approximately three million dollars in user funds have been extracted through a sequence of flash loan interactions that manipulated the collateral valuation mechanism.
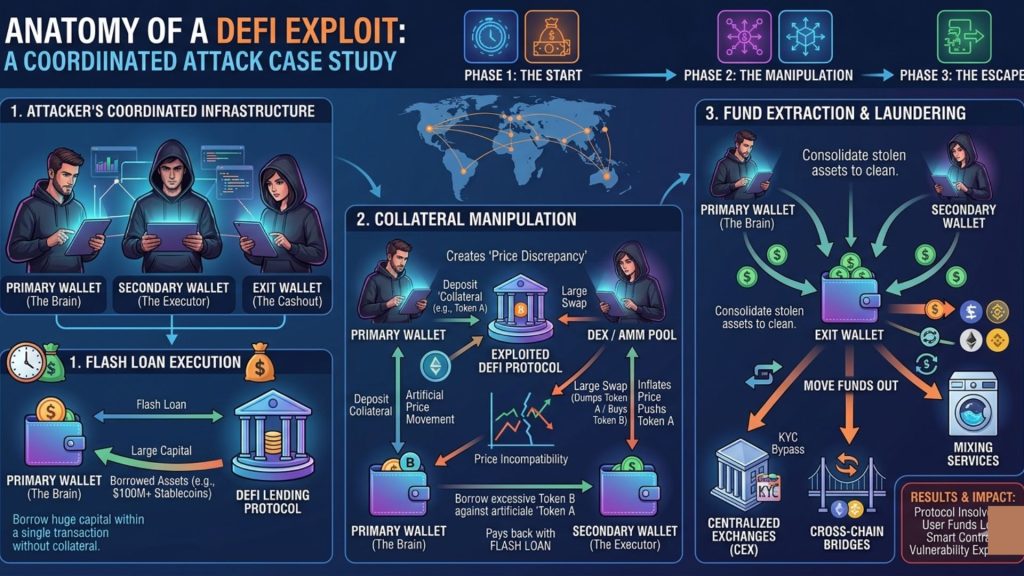
The security team initiates a forensic investigation the following morning. Their first priority is scoping: identify the exact block where anomalous activity began, map every contract and function involved, and establish which addresses participated in the attack sequence.
Transaction tracing reveals that the attacker operated three wallets in concert. The primary wallet executed the flash loan sequence. A secondary wallet pre-positioned the collateral assets used in the price manipulation. A third wallet received the extracted funds immediately after the attack completed.
Following the fund flow forward, the investigation team traces assets through two intermediate wallets before a portion reaches a centralized exchange deposit address. The remainder enters a cross-chain bridge to a secondary network.
On the destination chain, the trace continues. The bridged funds consolidate with assets from a separate wallet that had been funded several weeks earlier, suggesting the attacker had built infrastructure in advance of the attack. Eventually, a meaningful portion reaches another exchange deposit address on the secondary chain.
The investigation produces two documented exchange referrals with full on-chain evidence packages, a complete technical reconstruction of the exploit mechanism, and a behavioral profile of the attacker’s wallet infrastructure. Law enforcement is engaged with the evidentiary package. Fund recovery negotiations begin with both exchanges.
This is what a well-executed blockchain forensic investigation produces. Not a guarantee of recovery, but the maximum possible investigative leverage from the available evidence.
The Legal and Regulatory Dimension
Blockchain forensics increasingly intersects with formal legal process and regulatory compliance. Understanding this intersection shapes how investigations are conducted and documented from the very beginning.
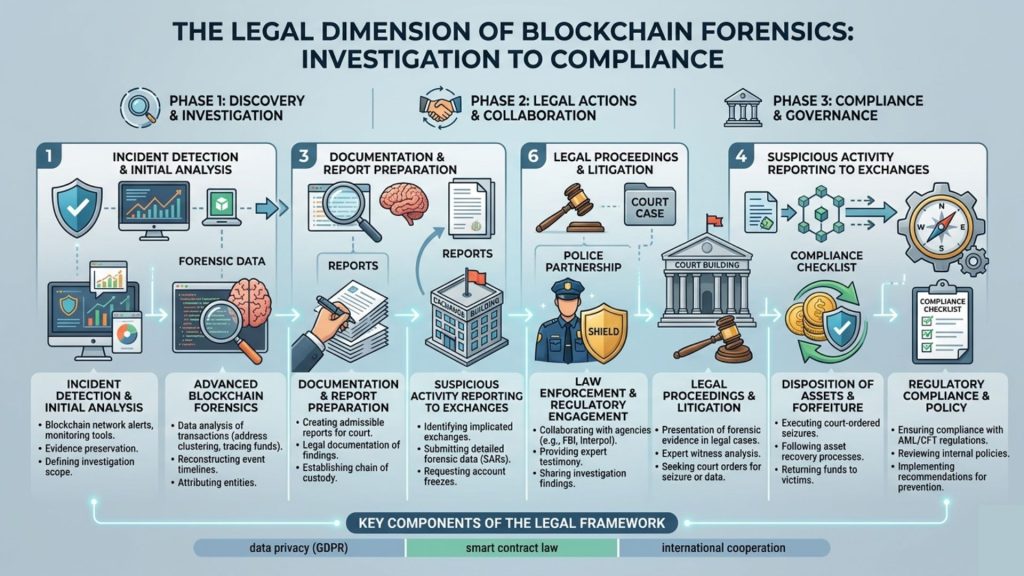
Evidence Standards
Forensic findings must meet strict evidence standards to support legal action. Investigators need to maintain a clear chain of custody for all collected data, apply reproducible methodologies that others can independently verify, and produce reports that can withstand scrutiny from opposing legal counsel.
When investigators treat blockchain forensics purely as a technical exercise and ignore evidentiary requirements, they often generate findings that fail to hold up in legal proceedings.
Regulatory Reporting Obligations
In regulated markets, significant blockchain incidents often trigger mandatory reporting to financial regulators, data protection authorities, or law enforcement agencies. Teams must understand these obligations and their timelines as part of incident response planning, not as an afterthought.
Forensic findings also play a critical role in AML and compliance reporting. Protocols that maintain strong compliance infrastructure, including those using crypto compliance and AML services, position themselves far better to meet these obligations. They already operate the monitoring systems and follow the documented processes that regulators expect.
Law Enforcement Engagement
Law enforcement agencies have significantly improved their ability to handle blockchain cases in recent years. Agencies across the US, EU, UK, and Asia-Pacific now operate dedicated crypto investigation units with strong blockchain forensic capabilities. When teams provide a well-documented forensic package, they increase the chances of meaningful cooperation.
Timing plays a critical role. Teams that engage law enforcement early, while transaction trails remain active and exchange referrals can still be executed achieve better outcomes than those that wait for a fully completed internal investigation.
Common Challenges in Blockchain Forensic Investigations
Even well-resourced investigations encounter serious obstacles. Understanding the most common ones allows teams to plan around them rather than lose momentum when they appear.
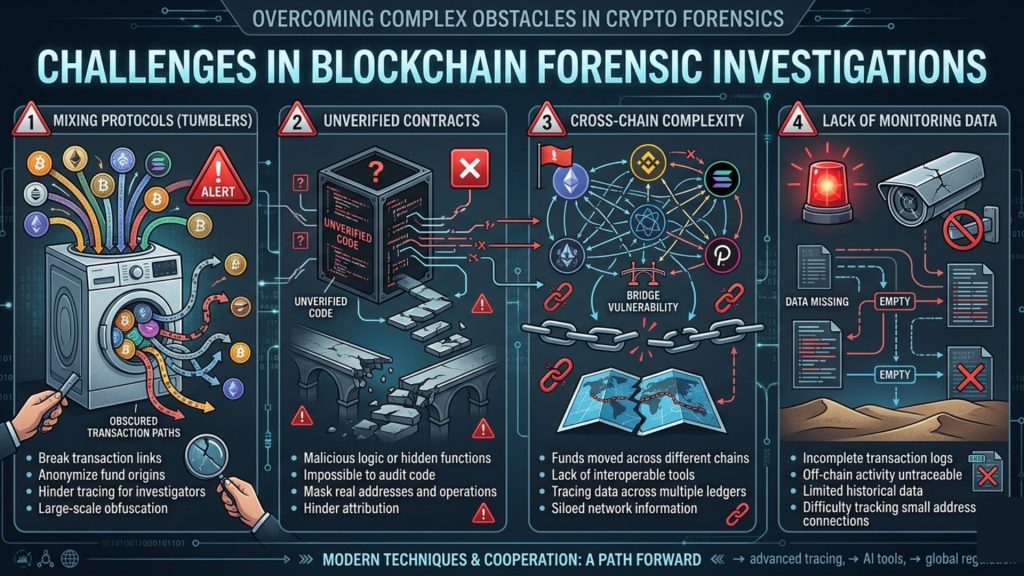
Mixing and Privacy Protocols: When stolen funds pass through mixing services or privacy coins, the transaction trail becomes significantly harder to follow. Mixing does not make transactions invisible, but it substantially increases analytical complexity and may shift evidence quality from definitive to probabilistic.
Unverified Contracts: When exploit activity involves contracts without verified source code, decoding transaction interactions requires working from bytecode or function signature matching. This is time-intensive and introduces uncertainty that needs to be clearly documented in investigation findings.
Scope Creep and Investigative Fatigue: Complex investigations generate large volumes of data. Without disciplined scope management, teams can spend weeks following interesting leads that don’t serve the original investigation objectives. Regular progress checkpoints and a clear primary output help maintain focus.
Absence of Pre-Incident Monitoring Data: Perhaps the most limiting constraint is investigating an incident when no continuous monitoring data was captured before the attack. Without behavioral baselines, investigators lack the context to identify preparation activity, assess whether the attack was targeted or opportunistic, or reconstruct how the attacker identified the vulnerability. This gap is one of the strongest arguments for continuous monitoring as a standard operational practice, not a reactive response tool.
Conclusion
A blockchain forensic investigation is a structured discipline that requires clear methodology, appropriate tooling, and a realistic understanding of what on-chain evidence can and cannot establish in both technical and legal contexts.
The teams that achieve the best outcomes from blockchain forensics are the ones that prepared before the incident. They have monitoring infrastructure generating pre-incident behavioral data. Also, they have documented incident response protocols and pre-defined investigation workflows. They know which tools they will deploy and have existing relationships with the exchanges and law enforcement agencies they may need to engage quickly.
For protocols building that forensic readiness posture, SecureTrace provides the transaction tracking and investigation infrastructure that makes structured forensic work possible. For teams that also run SecureWatch for continuous on-chain monitoring, the combination delivers both the pre-incident behavioral coverage and the post-incident tracing capability that a complete forensic investigation requires.
Blockchain forensics does not guarantee fund recovery. But it gives you the strongest possible investigative position, and the documented evidence to pursue every available legal, regulatory, and negotiated avenue when it matters most.
Frequently Asked Questions
What is a blockchain forensic investigation?
It is a structured process of analyzing on-chain data to reconstruct what happened during a blockchain incident, trace the movement of funds, attribute addresses to real-world entities where possible, and produce documented findings that support legal action, regulatory reporting, or fund recovery efforts.
How is blockchain forensics different from traditional digital forensics?
Traditional digital forensics works with data stored on devices or in centralized systems. Blockchain forensics works with publicly recorded but pseudonymous transaction data on distributed ledgers. The evidence is permanent and cannot be altered, but attributing it to real-world identities requires additional investigative layers that go beyond the on-chain record itself.
What is the first step in a blockchain forensic investigation?
Scoping. Before tracing any transactions, define the incident boundaries using specific block heights, identify all entry points, and clarify what the investigation needs to produce. Without clear scope, investigations lose focus and produce findings that are less actionable for the people who need to act on them.
Can stolen blockchain funds actually be recovered?
Recovery is possible but not guaranteed. The most effective path involves tracing funds to centralized exchanges, engaging those exchanges with documented forensic evidence, and coordinating with law enforcement to compel disclosure of account holder information. Early action significantly improves recovery odds before exchanges process withdrawals or accounts are closed.
What makes cross-chain tracing particularly difficult?
When funds move through a bridge, investigators must match deposit and withdrawal events across two different chains and continue the trace on the destination chain using potentially different tooling and data sources. Attackers use bridges specifically because many investigation teams lack the cross-chain tracing capability to follow them.
What is address clustering in blockchain forensics?
It is a technique for grouping wallet addresses likely controlled by the same entity, based on signals like shared funding sources, consistent transaction patterns, similar creation timing, and coordinated transaction sequences. It expands the investigative picture to the broader wallet infrastructure an attacker used, not just the addresses directly visible in the attack.
How does continuous monitoring help forensic investigations?
Monitoring systems that record on-chain activity before an incident generate behavioral data that becomes primary evidence in a post-incident investigation. This pre-incident data reveals preparation activity, establishes behavioral baselines, and provides investigative context that dramatically improves findings compared to starting data collection only after an attack has occurred.
What is SecureTrace and how does it support forensic investigations?
SecureTrace is SecureDApp’s transaction tracking and blockchain forensics tool. It provides structured transaction tracking, chain-of-custody documentation, and investigation-ready data outputs that support both internal post-mortems and external legal proceedings in blockchain security incidents.
When should law enforcement be engaged during a blockchain investigation?
As early as possible. Engaging law enforcement while the fund trail is fresh and exchange deposit addresses are recent significantly improves the likelihood of productive cooperation. Waiting until the internal investigation is fully complete often means the window for effective exchange action has already closed.
What evidence standards do blockchain forensic findings need to meet?
Findings intended to support legal proceedings require documented chain-of-custody for all collected data, reproducible methodology that can be independently verified, and reports structured to withstand scrutiny from opposing legal counsel. Treating forensics as purely a technical exercise without considering evidentiary standards consistently produces findings that cannot be used in the legal proceedings they were intended to support.
How do mixing protocols complicate a blockchain investigation?
Mixing protocols significantly complicate transaction tracing by obscuring the link between input and output addresses. They do not make transactions invisible, but they require specialized analytical techniques and substantially increase the time required to maintain a coherent fund trace. Evidence quality may become probabilistic rather than definitive when mixing protocol interactions are involved.
What is the difference between SecureTrace and SecureWatch?
SecureWatch is SecureDApp’s continuous on-chain monitoring platform focused on real-time threat detection and automated mitigation during active threats. SecureTrace is the transaction tracking and forensics tool focused on investigation work following an incident. They address different phases of the security lifecycle and deliver the most value when used in combination.



