Blockchains were built to be trustless. But trust and security are not the same thing.

A trustless system means you don’t have to rely on a third party to validate transactions. It does not mean the system is immune to attack. If anything, the removal of traditional gatekeepers creates a different kind of exposure, one that many teams underestimate until it’s too late.
In the past two years alone, the blockchain and DeFi ecosystem has lost over six billion dollars to hacks, exploits, and fraud. The majority of these incidents shared one uncomfortable truth: the threat was present on-chain before the damage became irreversible. The problem wasn’t the absence of a security audit. It was the absence of real-time blockchain threat monitoring after deployment.

This guide explores what blockchain threat monitoring actually means, why traditional security approaches fall short, what to monitor, how detection systems work, and what a mature monitoring posture looks like for teams building in Web3 today.
Why Blockchain Security Cannot Be Static
Ask most development teams about their security strategy and the answer is predictable: they commissioned an audit before launch. That’s a reasonable starting point. A smart contract audit is a controlled, point-in-time review of code logic. It can surface vulnerabilities in how a contract is written.
What it cannot do is monitor the blockchain once that contract is live.
After deployment, the threat landscape shifts. Contract logic may interact with external protocols in ways that weren’t anticipated. Governance mechanisms can be manipulated. Liquidity can be withdrawn in coordinated patterns designed to drain pools. Flash loan attacks can restructure on-chain state within a single block. None of these scenarios are code bugs. They are runtime behaviors.
This is the gap that real-time blockchain threat monitoring is designed to close. Not to replace audits, but to pick up where audits end.
Think of it this way: audits examine what the contract says it will do. Monitoring watches what it actually does, continuously, in production.
The Anatomy of an On-Chain Threat
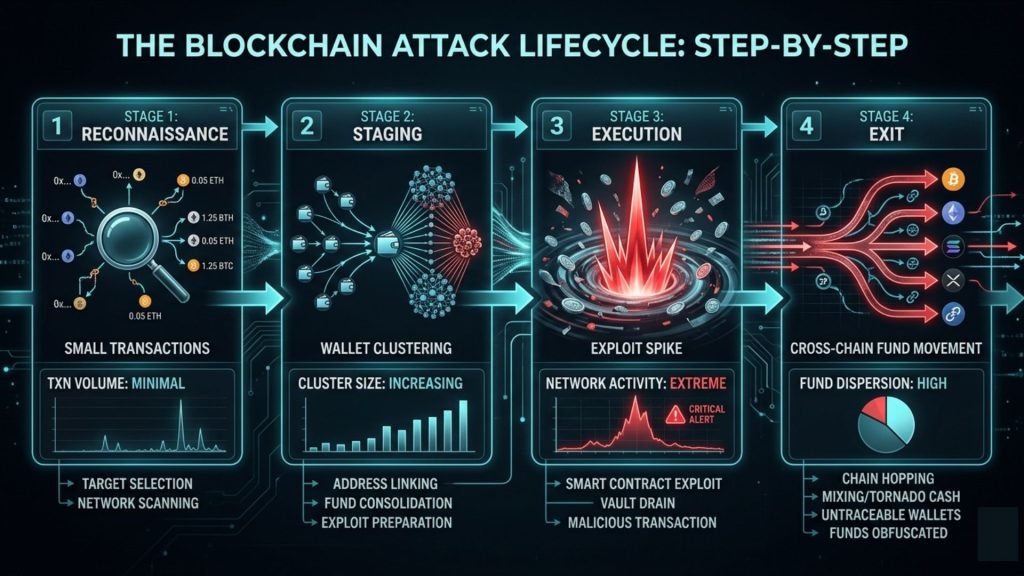
To build an effective monitoring strategy, you first need to understand how on-chain threats actually behave. They rarely announce themselves. Most sophisticated attacks unfold in stages, and the early signals are subtle.

Stage 1: Reconnaissance
Attackers study the target. They probe contract interfaces, test edge cases, and observe how the protocol responds to specific inputs. On-chain, this often looks like a series of small, unusual transactions, nothing alarming individually, but meaningful when viewed as a pattern.
Stage 2: Staging
Before executing an attack, the adversary prepares. This might involve positioning assets, acquiring governance tokens, or setting up multi-hop transaction paths. Wallet clustering and fund movement analysis can surface these preparations, but only if someone is actively watching.
Stage 3: Execution
The attack itself may take seconds. Flash loan attacks, reentrancy exploits, and price oracle manipulations can complete within a single block. At this stage, reactive security has almost no window to act.
Stage 4: Exit
Stolen assets are moved through mixing protocols, bridged to other chains, or converted. Forensic work is possible here, but financial damage has typically already occurred.
The clear implication is this: effective blockchain security requires detection in stages one and two, not three and four. That demands continuous, intelligent monitoring of on-chain activity.
What Real-Time Blockchain Threat Monitoring Actually Covers
The phrase gets used loosely, so it’s worth being specific. A complete real-time blockchain threat monitoring system operates across several distinct layers.
Transaction Pattern Analysis
At the most fundamental level, monitoring means observing every transaction that touches a protocol, including those involving connected contracts and liquidity sources. Abnormal patterns, unusual volume spikes, repeated small transactions probing contract limits, or unexpected function calls, should trigger alerts.
Smart Contract Behavior Monitoring
Beyond individual transactions, a contract’s aggregate behavior over time tells a deeper story. Is state being modified in ways that diverge from expected patterns? Are privilege escalation functions being called? Have administrative controls been invoked outside of normal governance processes? These are the questions contract-level monitoring tries to answer continuously.
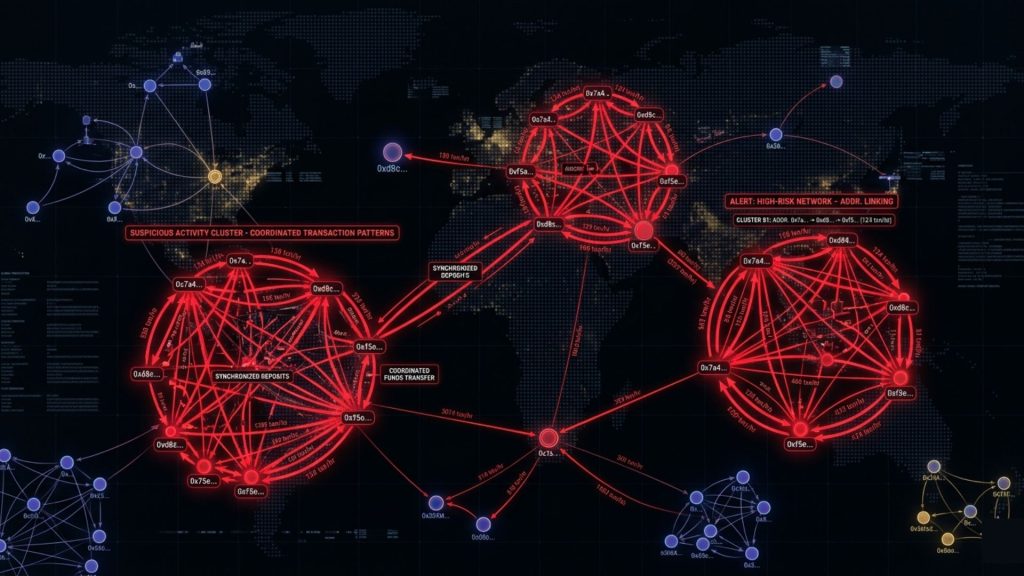
Wallet and Address Intelligence
Many attacks are coordinated across multiple wallets. Monitoring isolated addresses misses this. Effective systems maintain context about address clusters, track wallets previously linked to exploits, and flag interactions with known high-risk entities. This is particularly relevant for protocols that allow open participation.
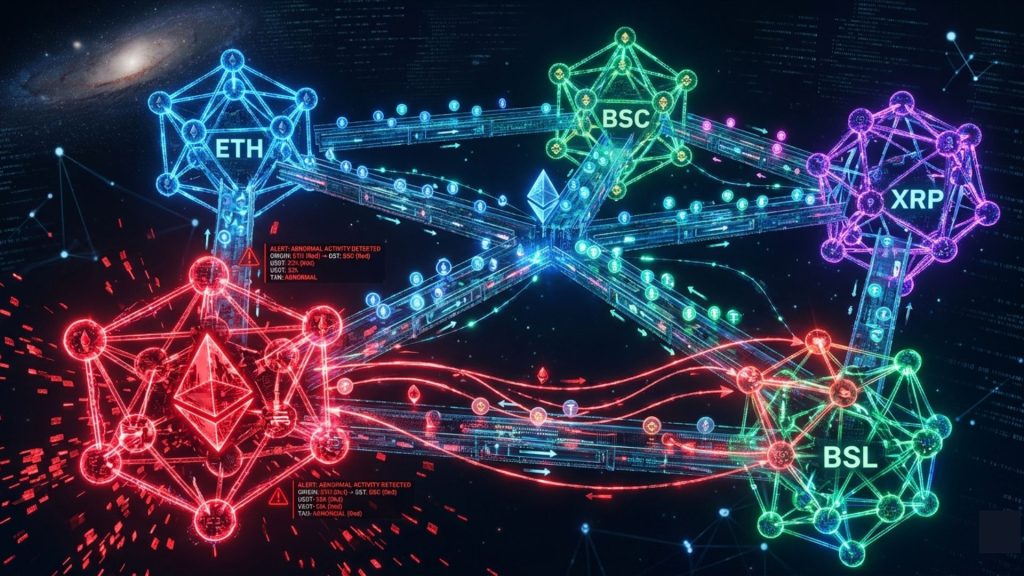
Cross-Chain and Bridge Activity
As multi-chain deployments become more common, threat surfaces expand across bridge protocols and cross-chain messaging layers. An attack may originate on one chain and manifest on another. Monitoring must account for this connectivity or it will miss an entire class of threats.
Governance and Access Control Events
Governance attacks are among the more insidious vectors in DeFi. They unfold over time through token accumulation, proposal manipulation, and voting coordination. Monitoring governance activity, including unusual quorum patterns and concentrated voting behavior, is essential for protocols with on-chain governance.
The Role of AI in Threat Detection
Early blockchain monitoring tools were essentially rule engines. You defined a threshold, such as alerting when a withdrawal exceeds a certain value, and the system fired when that rule triggered. These systems have value, but they have limits.
Rules require someone to anticipate the threat in advance. Novel attack patterns, by definition, don’t match existing rules.

AI-driven threat detection addresses this by learning from on-chain behavioral data rather than relying on pre-defined conditions. Machine learning models can identify anomalies that deviate from established norms without needing an explicit rule for every scenario. They can also reduce false positive rates, a practical concern since alert fatigue is real in any security operation.
More advanced systems combine multiple detection layers: signature-based detection for known threat patterns, statistical anomaly detection for unusual behavior, and graph analysis for identifying coordinated activity across address clusters.
The combination matters. Any single approach has blind spots. Layered detection is how mature systems achieve meaningful coverage.
From Detection to Response: Why Alerts Alone Are Not Enough
Here is a question worth sitting with: if your monitoring system fires an alert at 2 AM during an ongoing exploit, what happens next?
For many teams, the honest answer is: someone wakes up, assesses the situation, and by the time a human decision is made, the window has closed.

This is why the response layer of a monitoring system matters as much as the detection layer. The speed of on-chain attacks has fundamentally changed what effective response requires. In many cases, manual intervention is simply not fast enough.
Automated mitigation capabilities have emerged to address this gap. Systems that can pause contracts, freeze suspicious transactions, or trigger circuit breakers under defined threat conditions can act within the block time windows that matter. This doesn’t eliminate the need for human oversight, but it creates a buffer between detection and damage.
SecureWatch, developed by SecureDApp, incorporates a feature called AutoPause precisely for this reason. When anomalous activity triggers a defined threshold, AutoPause can automatically halt suspicious contract activity, giving the security team time to investigate before losses compound. For protocols where time-sensitive response is critical, that capability can be the difference between a contained incident and a catastrophic loss.
Building a Monitoring Architecture: Key Decisions
For teams moving from ad hoc alerting toward a structured monitoring program, several architectural decisions shape the outcome.
Coverage Scope
Define exactly what you’re monitoring. Your deployed contracts are the obvious starting point, but the scope should extend to integrated protocols, liquidity sources, and bridge connections. Incomplete coverage creates blind spots that sophisticated attackers will find.
Alert Tiers and Escalation
Not every anomaly is a critical threat. A useful alert hierarchy separates informational signals from low-severity warnings, from high-priority incidents requiring immediate response. Without this structure, security teams spend significant time on noise and miss the signals that matter.
Response Playbooks
Every alert tier should have a corresponding response protocol. Who gets notified? What actions are pre-authorized? At what threshold does automated mitigation engage? Defining these workflows in advance is what allows teams to respond coherently under pressure.
Data Retention and Forensics
Monitoring isn’t only about real-time response. Historical on-chain data supports post-incident investigation, regulatory reporting, and threat intelligence. Systems should retain enriched data in formats that support forensic analysis, not just raw transaction logs.
A Practical Scenario: What Monitoring Catches in the Real World
Consider a mid-size DeFi lending protocol operating across two chains. During a weekend evening, a series of transactions begins moving liquidity from one pool in small, staggered increments, distributed across fourteen wallets that had never previously interacted with the protocol.
No single transaction exceeds the alert thresholds set by the team. No known malicious address is flagged. By the rules-based system the protocol had in place, nothing is amiss.

An AI-based monitoring layer tells a different story. The pattern of wallet clustering, the timing distribution of the transactions, and the deviation from normal pool utilization curves all register as anomalous. An alert fires. The team investigates and identifies what appears to be a coordinated liquidity positioning play, consistent with preparation for a price oracle manipulation attack.
The protocol pauses relevant contracts, verifies the assessment, and communicates with its community before any exploit is executed. The threat is neutralized not through better code, but through better visibility.
This scenario isn’t hypothetical in design. It reflects the operational reality that teams with continuous monitoring infrastructure encounter regularly. The threat was real. The difference was observation capacity.
Compliance, Regulation, and On-Chain Monitoring
The regulatory environment around blockchain and digital assets is evolving rapidly. In most major jurisdictions, including the EU under MiCA, the US under developing FinCEN and SEC frameworks, and increasingly in Asia-Pacific markets, crypto businesses are being held to AML and transaction monitoring standards previously reserved for traditional financial institutions.

Real-time blockchain threat monitoring intersects with compliance in important ways. On-chain transaction monitoring can support AML screening by identifying wallet interactions with sanctioned addresses, mixer protocols, or jurisdictions subject to restrictions. It also creates the audit trails that regulators increasingly expect.
For protocols targeting institutional users or operating in regulated markets, compliance-capable monitoring is moving from a best practice to a baseline expectation. SecureDApp’s services include crypto compliance and AML support, designed to help Web3 businesses meet these obligations without building compliance infrastructure from scratch.
Common Gaps in Existing Monitoring Programs
Even teams that have invested in monitoring often have significant blind spots. The most common include:
Monitoring only deployed contracts, not the broader ecosystem they interact with. A vulnerability in an integrated oracle or liquidity source can compromise your protocol even if your own code is clean.
Relying exclusively on off-chain alerting without on-chain mitigation capability. This creates response latency that sophisticated attackers will exploit.

Neglecting governance monitoring. Some of the most damaging attacks in DeFi history have been governance-layer exploits that unfolded over days or weeks without triggering standard transaction alerts.
Treating monitoring as a set-and-forget configuration rather than an evolving program. Threat patterns change. Monitoring systems need to be updated as protocols evolve and as new attack vectors emerge.
Finally, a gap that’s less technical and more organizational: unclear ownership of monitoring outputs. If nobody is responsible for reviewing alerts and driving response, even a sophisticated monitoring system provides limited protection.
What Mature Blockchain Security Looks Like
The most security-mature teams in Web3 treat security as a continuous operational function, not a project milestone. The mindset shift matters as much as the tools.
Practically, mature blockchain security combines pre-deployment audit coverage with post-deployment continuous monitoring, clear incident response protocols, regular threat model reviews as the protocol evolves, and a feedback loop where monitoring data informs future development decisions.

This is not about spending more on security for its own sake. It’s about recognizing that in a permissionless, programmable financial system, the cost of a single major incident dwarfs the investment in prevention.
SecureDApp was built around this operational view of blockchain security. The product lineup spanning smart contract auditing through Solidity Shield, continuous on-chain monitoring through SecureWatch, transaction investigation through SecureTrace, and identity security through Secure X-DiD reflects an integrated approach to the full security lifecycle. Teams can engage individual products where they need them or adopt a broader security framework depending on their maturity and risk profile.
Getting Started: A Practical First Step
If your team has deployed contracts and doesn’t currently have real-time monitoring in place, the first step doesn’t have to be a complete architecture overhaul.
Start by defining your most critical contracts and the specific behaviors that would constitute a threat to each one. Unusual withdrawal volumes, unexpected function calls, wallet interactions with known high-risk addresses, and abnormal governance activity are all reasonable starting points.
From there, evaluate whether your current tooling can provide coverage against those scenarios. If it can’t, that gap defines your immediate monitoring priority.
Real-time blockchain threat monitoring is not a feature you add when you have time. For any protocol managing meaningful user funds or sensitive on-chain logic, it is a foundational security requirement. The question isn’t whether threats exist. They do, and they’re finding protocols that aren’t watching.
Conclusion
Blockchain security has matured significantly from its early days of ad hoc audits and manual incident response. The sophistication of on-chain attacks has forced a corresponding evolution in how teams think about security operations.
Real-time blockchain threat monitoring is at the center of that evolution. It doesn’t replace audits or governance best practices. It completes the picture by providing the continuous observability that post-deployment security demands.
The teams building in Web3 that will avoid the next wave of high-profile exploits are not necessarily the ones with the best code. They’re the ones watching carefully enough to catch what the code can’t prevent.
Frequently Asked Questions
What is real-time blockchain threat monitoring?
It is the continuous observation of on-chain activity to detect threats, anomalies, and attacks as they occur rather than after damage has been done. This includes monitoring smart contracts, wallet behavior, transaction patterns, and governance activity in real time. Unlike periodic reviews, real-time monitoring runs around the clock, capturing behavioral signals that would otherwise go unnoticed until it is too late to act.
Why isn’t a smart contract audit sufficient for blockchain security?
An audit reviews code before deployment. It cannot monitor runtime behavior after launch. Most significant exploits in DeFi history occurred in deployed contracts that had already been audited. The audit confirmed the code was sound at a specific point in time. What it could not do was watch how that code behaved once real users, real liquidity, and real adversaries started interacting with it. Continuous monitoring addresses the gap audits leave behind by observing the contract in its live environment every single day.
What types of threats does real-time monitoring detect?
Effective monitoring can detect flash loan attacks, reentrancy exploits, governance manipulation, abnormal liquidity movements, price oracle manipulation attempts, and coordinated activity across multiple wallets. Beyond these known categories, AI-driven systems can also flag emerging patterns that don’t yet have a name, simply because they deviate from established behavioral norms. This is particularly valuable as attackers continuously evolve their methods to avoid signature-based detection.
How does AI improve blockchain threat detection?
AI-based detection learns from behavioral data rather than relying on predefined rules. It can identify novel attack patterns that don’t match known signatures and reduce false positive rates, making alerts more actionable. Traditional rule-based systems require someone to anticipate every possible threat scenario in advance. AI removes that limitation by learning what normal looks like and surfacing anything that meaningfully deviates from it, even when the deviation has never been seen before.
What is AutoPause and how does it help?
AutoPause is a feature within SecureWatch that can automatically pause suspicious contract activity when a threat threshold is reached. It provides automated mitigation capability within the block-time windows where manual response is simply too slow. When an exploit is unfolding in seconds, waiting for a human to wake up, assess the situation, and authorize a response is not a realistic defense. AutoPause bridges that gap by acting immediately when defined conditions are met, giving the security team time to investigate before losses compound further.
Do I need monitoring even if my contracts are small or low-volume?
Yes. Attackers frequently target smaller protocols precisely because they assume lighter security coverage is in place. Threat actors actively conduct reconnaissance to find unmonitored deployments. A low-volume protocol with unmonitored contracts is not a low-risk target. It is often a preferred one. Volume is not the primary risk factor. Visibility is. A small protocol with strong monitoring is meaningfully safer than a larger one operating blind.
How does blockchain threat monitoring support AML compliance?
On-chain monitoring can screen wallet interactions against sanction lists, flag transactions involving mixer protocols, and create the audit trails that satisfy AML reporting requirements in regulated markets. As regulators in the EU, US, and Asia-Pacific tighten expectations around crypto transaction monitoring, having a documented, continuous monitoring program is increasingly becoming a baseline compliance requirement rather than an optional enhancement. Protocols serving institutional users or operating in regulated jurisdictions should treat this capability as essential.
What is the difference between transaction monitoring and smart contract monitoring?
Transaction monitoring observes individual transactions for anomalous patterns, such as unusual volumes, suspicious wallet interactions, or timing irregularities. Smart contract monitoring goes a level deeper. It tracks the aggregate behavioral state of deployed contracts over time, including function call patterns, state changes, access control events, and privilege escalation activity. Both layers are necessary. Transaction monitoring catches surface-level anomalies while smart contract monitoring reveals structural threats that only become visible when behavior is analyzed over time.
How should teams handle alerts from monitoring systems?
Alerts should be tiered by severity with clearly defined escalation paths for each tier. High-priority alerts should trigger pre-defined response playbooks so teams are not making judgment calls under pressure. Automated mitigation should be pre-authorized for specific high-severity conditions where response speed is critical. Without this structure, even the best monitoring system generates noise that security teams struggle to act on consistently. The playbook is what turns an alert into a coordinated response.
What does a multi-chain monitoring strategy look like?
It requires coverage across every chain where contracts are deployed, including monitoring of cross-chain bridge interactions and messaging protocols. Threats increasingly originate on one chain and execute on another. An attacker may position assets on Chain A, execute on Chain B, and exit through a bridge back to Chain A. Isolated single-chain monitoring misses this entire class of attack. Multi-chain monitoring connects these dots by maintaining visibility across the full deployment surface.
Is continuous monitoring expensive to maintain?
The cost of continuous monitoring is consistently lower than the cost of a single significant exploit. Beyond direct financial loss, a major incident carries reputational damage, user attrition, regulatory scrutiny, and recovery costs that dwarf any monitoring investment. Platforms like SecureWatch are designed to make continuous monitoring operationally feasible for Web3 security teams without requiring teams to build and maintain custom infrastructure from scratch.
What is the difference between SecureWatch and Solidity Shield?
Solidity Shield is SecureDApp’s smart contract audit product for pre-deployment vulnerability detection. It examines code logic before a contract goes live. SecureWatch is the continuous post-deployment monitoring system that watches contract behavior in production. They address different and complementary phases of the security lifecycle. Solidity Shield tells you the code is sound before launch. SecureWatch tells you what is actually happening after launch. Together they provide coverage across the full contract lifecycle.
Can monitoring prevent attacks entirely?
Not entirely. Attacks that execute within a single block before detection systems can respond fall outside what any monitoring solution can stop after the fact. However, monitoring catches the preparation stages that precede most sophisticated attacks, enables pre-emptive response before execution, and triggers automated mitigation that limits damage when attacks do occur. The goal is not perfection. It is reducing the window of exposure and minimizing the blast radius when threats materialize.
How often should monitoring configurations be reviewed?
Monitoring configurations should be reviewed whenever the protocol changes, when new threat intelligence emerges about attack vectors relevant to your architecture, and on a regular scheduled basis regardless of whether changes have occurred. Threat patterns evolve constantly. A configuration that provided strong coverage six months ago may have meaningful gaps today. Treating monitoring as a living program rather than a static setup is what keeps coverage relevant over time.
What is the first step for a team new to blockchain threat monitoring?
Define your critical contracts and identify the specific behaviors that would signal a threat to each one. Unusual withdrawal volumes, unexpected function calls, wallet interactions with known high-risk addresses, and abnormal governance activity are all reasonable starting points. Use that analysis to evaluate whether your current tooling provides coverage against those scenarios. Where it does not, that gap defines your immediate monitoring priority. Start focused, get coverage right on what matters most, and expand scope from there.



