Why Reactive Security No Longer Works in Web3
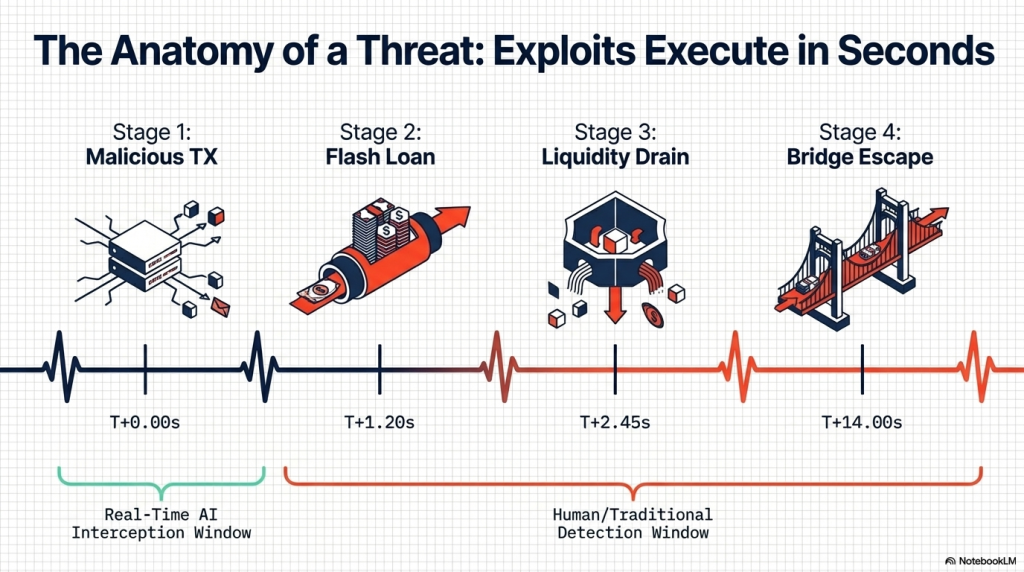
In 2023 alone, over $1.8 billion was lost to on-chain exploits globally. Flash loan attacks, rug pulls, and contract draining events most happened within minutes. By the time teams discovered the breach, funds were already bridged and tumbled. The average window between exploit initiation and complete fund movement is under four minutes. That is simply too small a window for any human-led response to catch. Most teams rely on a smart contract audit before launch and assume the job is done. But an audit is a point-in-time assessment of code. It tells you nothing about runtime behaviour.
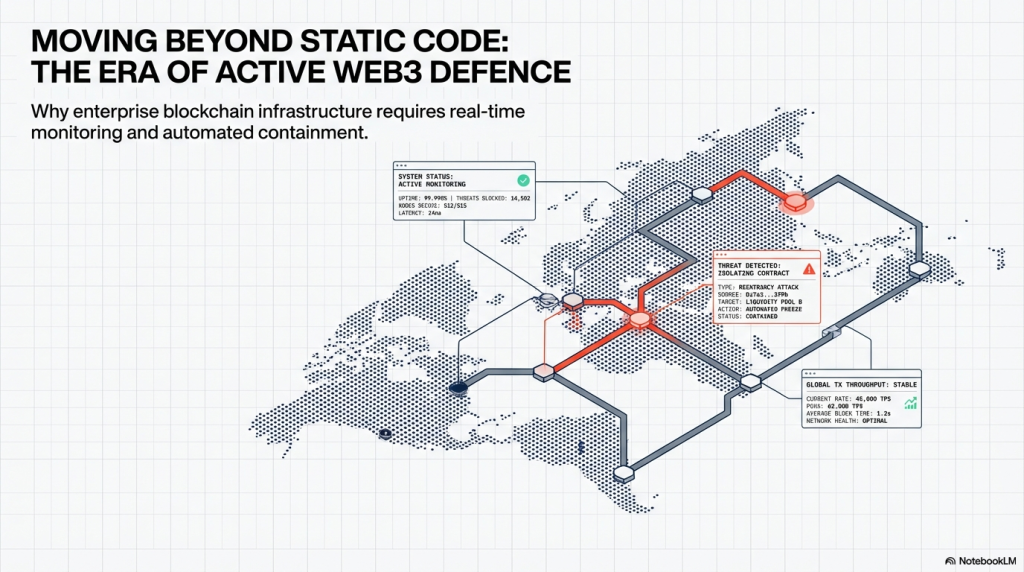
A contract can pass every audit standard and still be drained by a novel attack vector post-deployment. The problem is not a lack of audits. The problem is a complete absence of real-time visibility after deployment. Traditional Web2 security frameworks rely on perimeter defences firewalls, intrusion detection, and access control. Web3 has no such perimeter. Every deployed contract is publicly accessible and callable by any wallet. There is no login screen, no IP restriction, and no way to block a transaction before it lands on-chain. The only viable security model in Web3 is one that detects threats as they execute and responds automatically. This guide is your end-to-end implementation reference for real-time blockchain threat monitoring. We cover threat categories, monitoring architecture, tool selection, implementation steps, and enterprise compliance.
What Is Real-Time Blockchain Threat Monitoring?
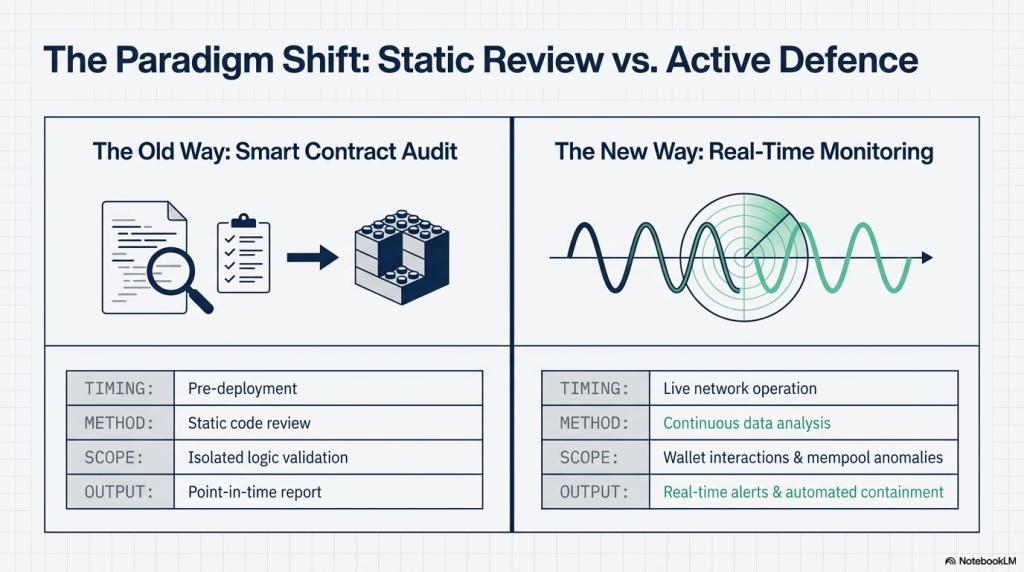
Real-time blockchain threat monitoring is the continuous surveillance of on-chain activity. It captures live transaction data, analyses behavioural patterns, and triggers alerts on detected anomalies. It operates at the network level watching every block, every wallet, every contract interaction. Unlike static analysis, it monitors dynamic behaviour as it happens not as it was written. This is fundamentally different from a smart contract security audit, which is pre-deployment. Monitoring is a post-deployment discipline active at every block, across every chain you operate on.
Audit vs Monitoring: Core Differences
| Parameter | Smart Contract Audit | Real-Time Monitoring |
| Timing | Pre-deployment | Post-deployment (continuous) |
| Scope | Code-level vulnerability detection | Behavioural and transactional anomalies |
| Response type | Findings report with fixes | Automated alerts and containment |
| Frequency | One-time or periodic | Every block, 24/7 |
| Primary value | Prevent weak code | Detect runtime exploits early |
Both are essential. Neither replaces the other. SecureDApp’s Solidity Shield addresses the audit layer detecting 150+ vulnerability classes before deployment. SecureWatch addresses the monitoring layer providing runtime anomaly detection with automated containment.
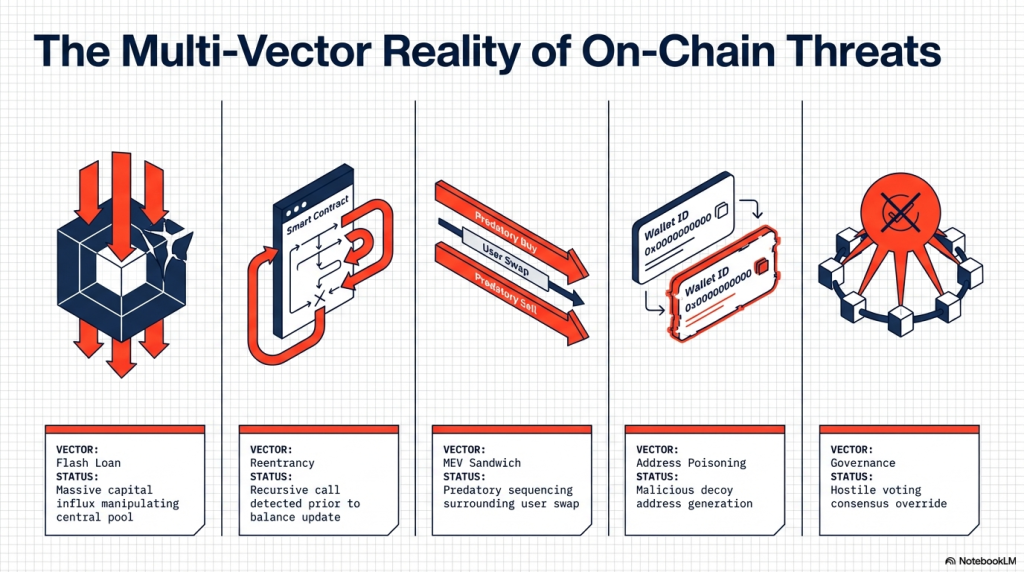
The On-Chain Threat Landscape You Are Monitoring For
Before building your monitoring stack, understand exactly what you are detecting. The attack landscape has evolved considerably and attackers are more sophisticated than ever.
1. Flash Loan Exploits
Attackers borrow enormous sums within a single transaction no collateral required. They manipulate price oracles, drain liquidity pools, and repay the loan all in one block. The Euler Finance hack in 2023 demonstrated how quickly $197 million can disappear. Detection requires mempool-level visibility before the transaction is confirmed.
2. Reentrancy Attacks
A vulnerable contract calls an external address before updating its own state variables. The attacker’s contract exploits this by calling back recursively, draining balances with each re-entry. The DAO hack in 2016 was a reentrancy attack $60 million lost in a single exploit. Monitoring for repeated recursive call patterns in short time windows can flag this early.
3. MEV and Sandwich Attacks
Maximal Extractable Value attacks occur when validators or bots reorder pending transactions. In a sandwich attack, a bot front-runs a large swap and back-runs it for guaranteed profit. MEV bots extracted over $1.3 billion from Ethereum users in 2023 alone. Mempool monitoring helps identify MEV bot activity before users are systematically drained.
4. Wallet Compromise and Address Poisoning
Attackers generate wallet addresses that closely mimic well-known wallets in appearance. Users copy the wrong address from transaction history and send funds to the attacker. Behavioural analytics tracking wallet interaction patterns over time can surface these anomalies.
5. Governance Manipulation
Malicious actors accumulate governance tokens rapidly to push through harmful proposals. They vote to drain treasury funds, modify protocol parameters, or install backdoor contracts. Monitoring sudden voting power concentration before a governance vote can trigger early warnings.
6. Oracle Manipulation
Price oracles feed external data like token prices into smart contracts. Manipulating oracle data even briefly allows attackers to execute favourable contract outcomes. Monitoring oracle price divergence from trusted external sources is a key detection signal.
The Architecture of a Real-Time Monitoring System
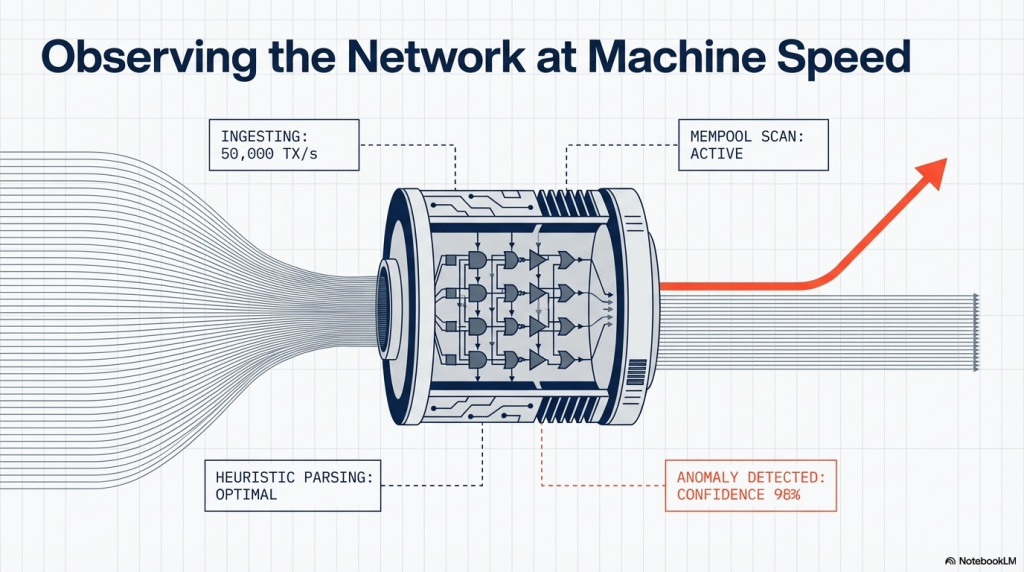
A production-grade monitoring system has four interdependent components. Each layer builds on the previous to create a complete threat intelligence pipeline.
Layer 1: Data Ingestion
Your monitoring system is only as good as the data flowing into it.You need access to transaction data both before confirmation and after it is finalised. There are three primary ingestion points for comprehensive on-chain coverage:
- Mempool monitoring — captures unconfirmed transactions before block inclusion
- Event log indexing — captures smart contract events from confirmed transactions
- State change tracking — monitors specific storage slot modifications in real time
- WebSocket subscriptions — for live block and transaction stream feeds from nodes
Most teams use a combination of managed RPC providers Alchemy, QuickNode, or Infura. For enterprise deployments, self-hosted archive nodes offer the best latency and data ownership. Cross-chain deployments require a separate ingestion pipeline for each supported network.
Layer 2: Rule Engine and AI Anomaly Detection
Raw transaction data has no intelligence without a detection layer processing it. This is where rule-based logic and AI/ML models work in tandem. Rule-based detection covers known, defined threat patterns:
- Large single-block token transfers exceeding a defined TVL percentage threshold
- Multiple failed transactions from the same sender address in rapid succession
- Privileged function calls pause, upgrade, transfer ownership from unapproved wallets
- Sudden withdrawal of more than a configurable percentage of pool liquidity
- Contract interactions involving newly deployed contracts with no prior history
AI-based anomaly detection covers emergent and previously unseen patterns:
- Behavioural deviations from a wallet’s established historical activity baseline
- Unusual clustering of wallet addresses acting in coordinated patterns
- Gas price anomalies consistent with front-running or MEV bot behaviour
- Token price oracle divergence beyond expected statistical ranges
- Cross-contract call graphs that resemble historical exploit patterns
The combination of rule-based and AI detection is what separates monitoring platforms from basic alert scripts. SecureWatch implements both layers with customisable security policies for enterprise teams.
Layer 3: Alert and Automated Response
Detecting a threat is only half the equation. Responding before damage is done is the other. Response mechanisms fall into two categories based on your risk tolerance and operational readiness.
Passive response alerting and notification only:
- Push notifications to security leads via Slack, PagerDuty, or email integrations
- Severity-scored dashboard alerts with full transaction context and wallet history
- Webhook triggers connecting to existing SIEM or incident management platforms
Active response automated containment:
- Contract pause mechanisms triggering automatically when thresholds are breached
- Policy-based transaction blocking for flagged wallet addresses
- Emergency fund transfer to a cold wallet when exploit indicators are confirmed
- Cross-chain propagation alerts to other deployments of the same protocol
Active response requires pre-built administrative controls inside the smart contract itself. This is why security architecture decisions must be made at the code layer not just post-deployment.
Layer 4: Forensic Intelligence and Reporting
After an incident, you need a complete reconstruction of what happened, when, and how. This means tracing the transaction thread from the initial exploit call to final fund destination. SecureTrace provides legal-grade forensic reporting, including wallet clustering and asset recovery pathways. Cross-chain tracing is particularly critical when funds are bridged to evade detection.
Step-by-Step Implementation: Building Your Monitoring Stack
Step 1: Define Your Threat Model
Before a single line of monitoring configuration is written, map your protocol’s threat surface.
Answer these foundational questions first:
- What smart contracts are live, and what assets do they control?
- Who are the privileged actors multisig wallets, governance contracts, admin addresses?
- What is the maximum tolerable loss threshold before emergency pause is required?
- Which chains is your protocol deployed on Ethereum, Arbitrum, Polygon, BNB Chain?
- What is the largest single transaction your protocol should ever legitimately process?
Document this threat model formally. It becomes the foundation of your entire rule set. Revisit and update this model every time your protocol adds a new feature or chain deployment.
Step 2: Set Up Your Data Infrastructure
Choose your blockchain data source based on chain coverage, latency, and operational requirements.
| Data Source | Best For | Latency | Cost Profile |
| Self-hosted full node | Enterprise, full data control | Very low | High infrastructure cost |
| Managed RPC (Alchemy/QuickNode) | Most DeFi teams | Low | Usage-based pricing |
| The Graph / Subgraphs | Indexed historical data queries | Medium | Generally low |
| Dedicated monitoring platform | Real-time AI + rule detection | Very low | SaaS subscription |
For most protocol teams, a managed RPC provider combined with a dedicated monitoring platform is optimal.
A dedicated platform like SecureWatch abstracts the infrastructure complexity while adding AI detection on top.
Step 3: Define Your Monitoring Rules and Alert Thresholds
Start with these foundational rules, then expand based on your specific threat model.
- Alert — Any transfer exceeding 5% of total contract TVL in a single transaction
- Alert — Privileged function call from a wallet not in the approved governance set
- Alert — More than three consecutive failed calls to the same function within 60 seconds
- Alert — Oracle price deviation of more than 10% within a single block
- Alert — Contract ownership transfer or proxy implementation upgrade initiated
- Alert — New contract deployment from a wallet that has interacted with your contract
- Critical — Flash loan borrow followed by pool interaction and repay in one transaction
- Critical — Reentrancy pattern detected same function called more than twice recursively
These rules should be version-controlled, reviewed by your security team, and updated quarterly. As your protocol evolves, your monitoring rules must evolve in parallel not lag behind.
Step 4: Integrate Automated Containment
A monitoring system without containment capability is an expensive alarm with no emergency stop. To enable effective automated containment, your smart contract needs these built-in controls:
- A pause function restricted exclusively to a monitoring oracle or designated multisig
- An emergency withdrawal mechanism protecting treasury funds when an exploit is confirmed
- Configurable daily transfer limits enforced at the contract level, not just the application layer
- Role-based access controls that can be revoked remotely if a privileged wallet is compromised
SecureWatch supports policy-based automated containment allowing teams to configure response playbooks that execute automatically when specific threat thresholds are crossed, without manual intervention.
Step 5: Build Cross-Chain Monitoring Coverage
Most protocols in 2025 are deployed across three or more chains simultaneously. A coordinated cross-chain attack can begin on one chain and drain assets on another within minutes. Your monitoring infrastructure must have simultaneous coverage across every chain you operate on. Cross-chain wallet clustering is particularly important the same attacker often uses different wallets per chain. A unified monitoring dashboard that aggregates alerts across chains is essential for enterprise security teams.
Step 6: Build and Test Your Incident Response Playbook
When a critical alert fires at 2:47 AM, your team cannot afford to improvise a response. Your incident response playbook must be documented, rehearsed, and accessible to every on-call team member.
A production-ready playbook defines:
- Escalation tiers based on alert severity informational, warning, high, and critical
- Named on-call security lead for each time zone shift with direct contact details
- Precise action sequence for a Severity 1 exploit in progress pause, communicate, trace
- External communication protocol when and how to inform users and partners publicly
- Post-incident forensic documentation process for legal and regulatory submissions
SecureTrace generates legal-grade forensic reports to support internal post-mortems and law enforcement filings. Having this reporting infrastructure ready before an incident is critical not after it happens.
Enterprise Considerations: Compliance and Regulatory Alignment
For enterprises operating in regulated sectors, real-time monitoring is increasingly a regulatory expectation. SEBI innovation sandboxes, RBI digital asset frameworks, IFSCA guidelines, and global AML standards require it. Exchanges, regulated DeFi platforms, and neo-banks cannot afford to operate without monitoring infrastructure. SecureDApp’s OVSE registration under UIDAI brings a critical compliance advantage for India-based enterprises. SecureX-DID enables enterprise-grade KYC integration using Aadhaar offline verification fully compliant with the Aadhaar Act, 2016.
This means organisations can onboard users with decentralised, privacy-preserving identity verification.
Zero-knowledge proofs allow selective disclosure verifying identity attributes without exposing raw PII.
| Compliance Requirement | SecureDApp Product | Capability |
| AML transaction monitoring | SecureWatch | Wallet clustering + behavioural anomaly detection |
| KYC for regulated onboarding | SecureX-DID | Aadhaar offline verification (OVSE-registered) |
| Forensic evidence for legal action | SecureTrace | Legal-grade transaction tracing reports |
| Smart contract risk assessment | Solidity Shield | 150+ vulnerability class pre-deployment audit |
Institutions including STPI, IFSCA, Broadridge, C3iHub, and IIT Dharwad already trust SecureDApp’s infrastructure. That institutional validation matters when presenting compliance posture to auditors and regulators. It is not just technical credibility it is regulatory legitimacy backed by formal UIDAI recognition.
Conclusion
The monitoring landscape is evolving rapidly and the trajectory is clear for teams planning ahead. Cross-chain composability is expanding the attack surface faster than most protocols can track. A single multi-chain exploit can span four networks and three bridges in under ten minutes. Monitoring must evolve to track threat propagation across chains not just flag per-chain anomalies. AI models trained on historical exploit data are getting meaningfully better at predicting novel patterns.
Zero-day exploits that have never been seen before can still exhibit behavioral signatures detectable by AI. The next generation of monitoring tools will shift from reactive alerting to predictive threat scoring. Regulatory bodies globally are moving toward mandatory on-chain transaction surveillance for licensed entities. The EU’s MiCA framework and India’s emerging VDA regulations both point in this direction. Protocols that invest in monitoring infrastructure today will have a significant compliance head-start.
Teams building monitoring and forensic capabilities now are building the compliance infrastructure that will be mandatory within 24 months. The investment compounds over time.
FAQ on Real Time Blockchain Threat Monitoring
It is the continuous, automated surveillance of on-chain transactions, contract states, and wallet behaviour. The goal is to detect and respond to threats as they execute not after funds are already gone.
No. Any protocol with deployed contracts and user funds at risk requires monitoring. The scale of monitoring rules and infrastructure grows with the protocol’s TVL and complexity but the need exists at every level.
Analytics tools provide data visibility and dashboards. SecureWatch delivers active threat detection with AI-powered anomaly scoring, policy-based automated containment, and enterprise alert integrations not just historical data browsing.
Not all, but it dramatically reduces the damage window. Most major exploits require several blocks to complete. Early detection enables automated containment before funds are fully drained or bridged.
Mempool monitoring captures transactions before block confirmation critical for detecting sandwich attacks and front-running. Event log monitoring analyses confirmed on-chain events for post-execution anomaly detection and forensic investigation.



