In 2023, a major European financial services firm discovered that a significant portion of its customer identity data had been sitting in a vendor database it had not actively monitored in over fourteen months. The vendor had been breached. The company’s response? A costly forensic engagement, regulatory notifications, and a six-figure fine under GDPR.
The identity problem in enterprise environments is not new. What is new is the regulatory environment surrounding it, the sophistication of attacks targeting centralized identity stores, and the fact that organizations now have a credible architectural alternative: self-sovereign identity.
Self-sovereign identity for enterprises is not a philosophical concept or a blockchain thought experiment. It is a production-ready infrastructure model that fundamentally restructures how organizations handle user credentials, customer onboarding, employee verification, and regulatory compliance. This guide walks through the complete picture, from architecture to deployment to regulatory alignment, written for decision-makers who need to evaluate this shift seriously.
Section 1: Why the Current Identity Model Is Breaking
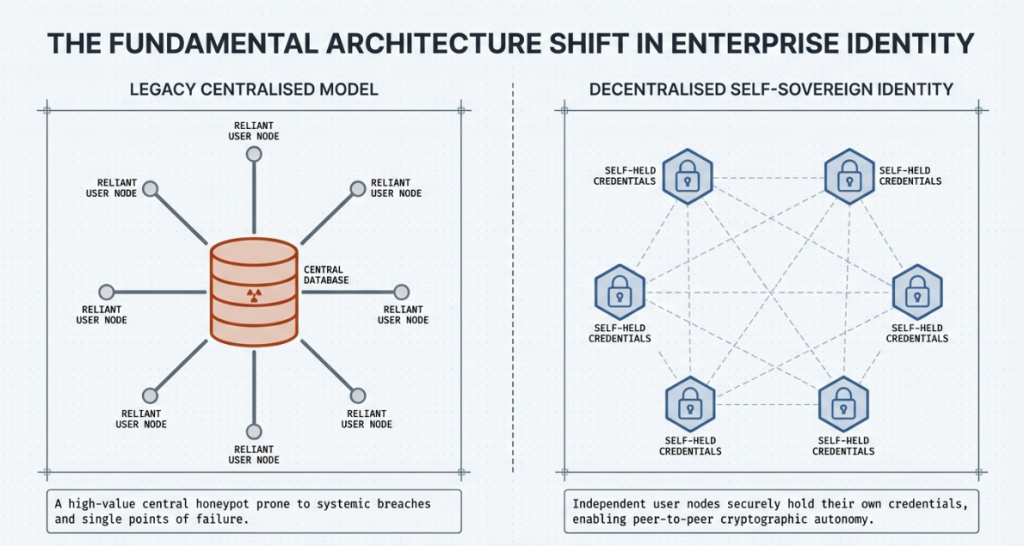
Enterprises today operate on what security architects call a “hub-and-spoke” identity model. The organization sits at the center, controlling identity data for everyone it interacts with: employees, customers, partners, and contractors. Every verification, every credential check, every onboarding flow routes through systems the organization owns or rents from an identity provider.
This model has three structural problems that compound each other.
The aggregation problem.
When you centralize identity data for millions of users, you create a high-value target. Every centralized identity store is, by definition, a honeypot. The larger the store, the more attractive it becomes to adversaries. Breaches of centralized identity databases do not just expose passwords. They expose behavioral patterns, device fingerprints, biometric templates, and transaction histories. The damage from these breaches is disproportionate to the actual data stolen, because the data can be correlated across breach datasets over time.
The compliance cost problem.
Privacy regulations across major jurisdictions now require organizations to minimize the personal data they collect, store, and process. GDPR in Europe, DPDP in India, CCPA in California, and PDPA in Singapore all carry the same underlying logic: organizations should not hold user data they do not strictly need. But the current identity model is structurally incompatible with data minimization. You cannot both control identity and minimize personal data collection. The two objectives are in tension by design.
The interoperability problem.
A user who has completed KYC at one institution cannot take that verification with them to another institution. Every organization re-verifies from scratch. This is expensive for businesses and deeply frustrating for users. It also creates repeated data exposure events, because every re-verification sends personal data across multiple systems.
Self-sovereign identity addresses all three of these problems at the architectural level. Not through policy changes or better encryption of existing systems, but by restructuring who holds identity data in the first place.
Section 2: What Self-Sovereign Identity Actually Means
The phrase “self-sovereign identity” carries ideological weight in the decentralized community, but for enterprise purposes, it is more useful to understand it as a set of concrete technical standards and infrastructure components that allow identity to be user-held rather than institution-held.
The core components are:
Decentralized Identifiers (DIDs).
A DID is a globally unique identifier that is cryptographically controlled by its owner. Unlike an email address or a social security number, a DID does not require a central authority to issue or maintain it. The controller of a DID proves ownership through cryptographic key pairs. The DID itself is anchored to a verifiable data registry, which can be a blockchain or a distributed ledger, or in some implementations, a web-based endpoint.
The W3C DID specification became an official recommendation in 2022, which means there is now a standards body backing this infrastructure. This matters enormously for enterprise adoption, because procurement and legal teams require standards alignment before approving new infrastructure components.
Verifiable Credentials (VCs).
A Verifiable Credential is a digitally signed attestation issued by one party about another. Think of it as the digital equivalent of a notarized document, except the signature can be verified cryptographically without contacting the issuing authority at the moment of verification. A university can issue a credential attesting to a degree. A regulator can issue a credential attesting to a KYC clearance. A healthcare provider can issue a credential attesting to a clinical certification. The holder stores these credentials in a digital wallet. When they need to prove something, they present the relevant credential. The verifier checks the cryptographic signature and the issuer’s DID. No central database is queried. No personal data is transmitted beyond what is strictly necessary.
Zero Knowledge Proofs.
This is where self-sovereign identity moves from interesting to genuinely powerful for compliance-sensitive applications. Zero knowledge proofs allow a holder to prove a specific claim about their credential without revealing the underlying data. A user can prove they are over 18 without revealing their date of birth. They can prove they hold a valid KYC clearance without revealing which financial institution issued it. They can prove they are a licensed professional in a given jurisdiction without revealing their full license record.
For regulated industries, this capability is not a luxury. It is a direct response to data minimization requirements. Verification without data transfer is exactly what regulators are pushing organizations toward.
Digital Wallets.
The holder’s credentials are stored in a digital wallet, which can be an application on a mobile device, a browser extension, or a hardware security module for high-assurance contexts. The wallet manages the cryptographic keys associated with the holder’s DID and handles credential presentation flows. Enterprise wallet infrastructure differs from consumer wallet applications primarily in how keys are managed, how credentials are backed up, and how the wallet integrates with existing enterprise systems like HR platforms, access management tools, and compliance dashboards.
Section 3: The Technical Architecture in Detail
Understanding self-sovereign identity at the architectural level requires mapping the flow between four roles: the issuer, the holder, the verifier, and the verifiable data registry.
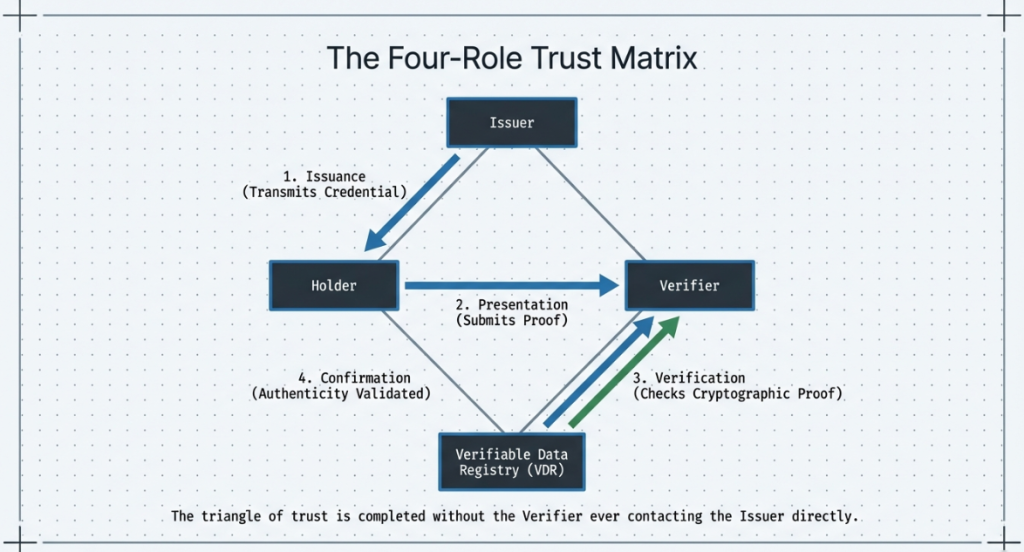
The Issuer.
Any organization that has authority to make a claim about a person or entity can be an issuer. A bank that has completed AML checks on a customer can issue a KYC credential. A government agency can issue a national identity credential. An enterprise HR department can issue an employment credential. The issuer signs the credential using its DID-associated private key, which allows any verifier to confirm the issuer’s identity and the credential’s integrity without calling back to the issuer in real time.
The Holder.
The individual or entity about whom the credential makes claims. After receiving a credential from an issuer, the holder stores it in their digital wallet. The holder controls what they share, with whom, and when. Critically, the holder can choose to share only specific claims from a credential, not the full credential. This selective disclosure capability, enabled by cryptographic primitives like Merkle tree-based validation, is what makes the architecture genuinely privacy-preserving rather than privacy-theater.
The Verifier.
Any organization that needs to confirm a claim. In an enterprise context, this might be an exchange verifying regulatory compliance before allowing trading, an employer verifying professional certifications, or a platform verifying age or residency. The verifier sends a presentation request to the holder, specifying what claims they need. The holder’s wallet generates a Verifiable Presentation, which is a package containing the relevant claims from relevant credentials, signed by the holder’s private key. The verifier checks the presentation against the issuer’s public key, retrieved from the verifiable data registry.
The Verifiable Data Registry.
This is the infrastructure that allows issuers’ public keys and DID documents to be discoverable and tamper-evident. Blockchain-based registries are common because they provide immutability and decentralized control. However, the W3C DID specification deliberately does not mandate a specific registry type. Some implementations use public blockchains like Ethereum or Hyperledger Fabric. Others use decentralized web infrastructure like IPFS. Still others use web-based DID methods that do not require a blockchain at all. Enterprise architects need to evaluate registry choices based on performance requirements, regulatory jurisdiction, and existing infrastructure.
The Merkle Tree Validation Model
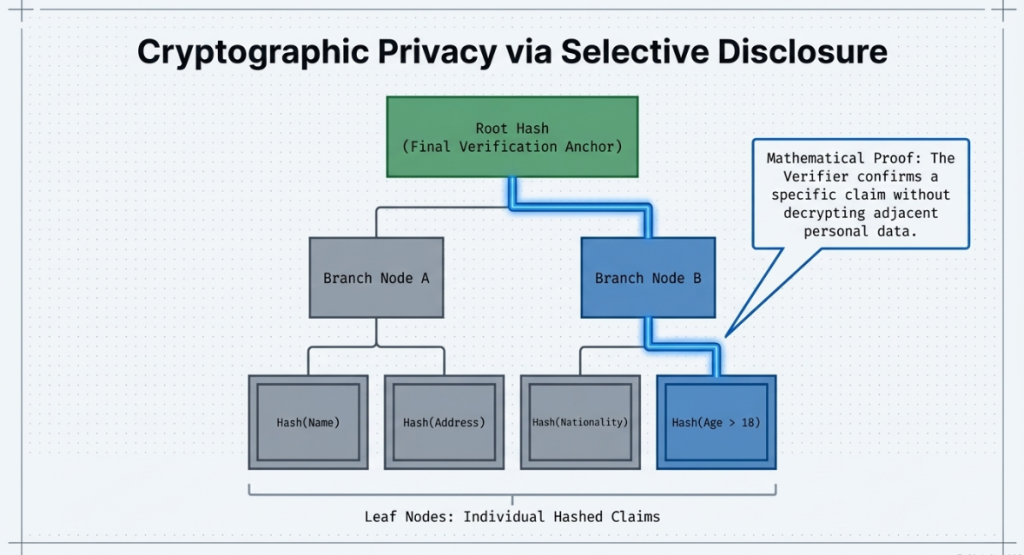
SecureDApp’s SecureX-DID implements Merkle-based validation as a core component of its credential architecture. This deserves explanation because it is the mechanism that enables selective disclosure without zero-knowledge proof overhead in contexts where full ZKP computation is not required.
In a Merkle tree-structured credential, each claim within the credential is hashed individually and arranged in a tree structure. The root hash represents the entire credential. When a holder wants to disclose only specific claims, they provide the relevant leaf hashes and the sibling hashes needed to reconstruct the path to the root. The verifier can confirm that the disclosed claims are genuine parts of the signed credential without seeing the other claims. The cryptographic guarantee is strong. The computational overhead is modest. This makes it suitable for high-throughput enterprise verification flows.
Integration with Existing Enterprise Identity Infrastructure
A common concern during SSI evaluation is whether adopting this architecture requires replacing existing identity systems. In most enterprise deployments, it does not. SSI functions as an additional credential layer that sits alongside or on top of existing infrastructure.
For organizations running traditional IAM systems, SSI typically integrates at the authentication and credential verification layer. A user might authenticate to an internal system using their existing credentials, but prove their identity to an external partner using a verifiable credential from their enterprise wallet. The internal identity management system can act as an issuer, generating credentials that are stored in employee wallets and used for external verification scenarios.
This hybrid approach significantly reduces deployment risk and allows organizations to introduce SSI for specific high-value use cases without requiring a full infrastructure migration.
Section 4: SSI versus Traditional IAM
The comparison between self-sovereign identity and traditional Identity and Access Management systems is not straightforward, because they address overlapping but distinct problems. The confusion often comes from treating them as direct substitutes when they are better understood as complementary architectures with different primary use cases.
| Dimension | Traditional IAM | Self-Sovereign Identity |
|---|---|---|
| Data custody | Organization holds user data | User holds own credentials |
| Verification model | Centralized database query | Cryptographic proof verification |
| Cross-organization portability | Limited, requires federation agreements | Native, by design |
| Privacy compliance posture | Data minimization requires significant retrofitting | Data minimization is architecturally native |
| Breach impact | Credential store compromise affects all users | No centralized store to breach |
| Onboarding friction | Re-verification required at each organization | Re-use of existing verified credentials |
| Regulatory alignment | Depends on configuration and policy | Aligned with GDPR, DPDP, CCPA by design |
| Implementation complexity | Well-understood, mature tooling | Newer ecosystem, growing tooling maturity |
| Biometric risk | Biometric templates stored centrally | Biometric verification local to device |
The table above is not an argument that SSI replaces IAM. It is an illustration of where each architecture has structural advantages. Traditional IAM excels at managing access control within a defined organizational boundary. SSI excels at managing identity across organizational boundaries, particularly when privacy compliance and interoperability are primary concerns.
For an enterprise running a regulated onboarding process, a customer-facing KYC flow, or a cross-border professional verification workflow, SSI provides capabilities that traditional IAM architectures cannot replicate without significant additional infrastructure.
Section 5: The Regulatory Alignment Story
One of the strongest arguments for enterprise SSI adoption is regulatory alignment. As data protection regimes tighten globally, organizations are discovering that their existing identity infrastructure requires expensive retrofitting to achieve compliance. SSI, by contrast, is structurally aligned with the direction regulators are pushing.
GDPR and data minimization.
Article 5 of GDPR requires that personal data be collected only for specified, explicit, and legitimate purposes, and that data collected be adequate, relevant, and limited to what is necessary in relation to the purposes for which they are processed. SSI’s selective disclosure model is a direct technical implementation of this principle. When an organization uses SSI-based verification, it receives only the specific claims it needs. It does not receive or store the full credential. The data minimization requirement is met by the architecture itself, not by organizational policy.
The right to erasure GDPR’s right to erasure is notoriously difficult to implement in systems that have copied user data across multiple databases and log systems. With SSI, the issuing organization does not hold the user’s credential. The user holds it. If a user revokes a credential and the issuer marks it as revoked in the registry, no erasure process is required across the verifier’s systems because the verifier never stored the full credential in the first place.
India’s DPDP Act.
The Digital Personal Data Protection Act, which came into force in 2023, carries similar data minimization requirements and places significant obligations on what the act calls “data fiduciaries.” Organizations handling personal data for verification purposes face substantial compliance costs under this framework. SSI’s architecture reduces these costs by reducing the volume of personal data the verifying organization ever handles.
The UIDAI OVSE Registration Factor.
SecureDApp operates as a registered Offline Verification Seeking Entity under the Unique Identification Authority of India, governed by the Aadhaar Act 2016. This registration is not a marketing credential. It is a structural compliance asset with direct implications for enterprise deployments in India and for multinational organizations operating in the Indian market.
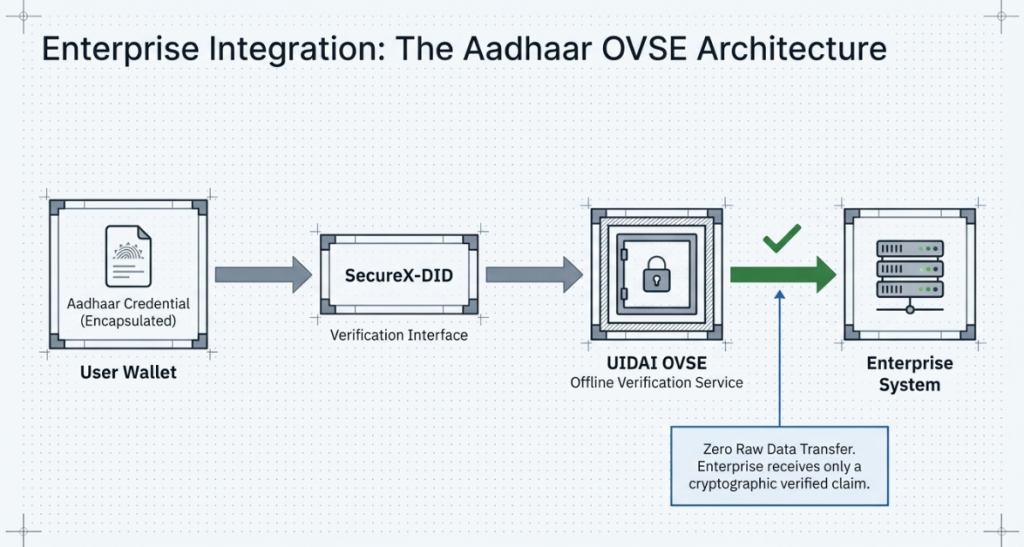
Being registered as an OVSE means SecureX-DID can integrate Aadhaar-based offline verification workflows within the formal regulatory framework. This is significant because Aadhaar represents one of the largest biometric identity databases in the world, with over 1.3 billion enrolled identities. Enterprises building KYC workflows for the Indian market face a fundamental question: how do you verify against Aadhaar in a way that is both effective and compliant? The OVSE registration provides a formal, regulated pathway for doing this using offline verification methods, which means the biometric data never leaves the user’s control during the verification process.
This creates a capability that is genuinely rare in the SSI ecosystem: a self-sovereign identity infrastructure provider with formal integration capability into a national biometric identity system, operating within the regulatory framework of that system.
AML and KYC Integration.
Anti-money laundering compliance presents a specific challenge for SSI architectures, because AML regulations in most jurisdictions require organizations to maintain records of their verification processes. This can appear to conflict with SSI’s data minimization principles, but the conflict is resolvable.
In an SSI-based KYC flow, the verifier receives a verifiable presentation containing the relevant claims. The verifier can record that a verification occurred, what claims were verified, who the issuer was, and the timestamp, without storing the underlying personal data. The credential itself, containing the full personal data, remains with the user. Audit trails can be maintained for regulatory purposes while adhering to data minimization for the personal data itself. This architecture satisfies AML record-keeping requirements while substantially reducing personal data storage obligations.
Section 6: Enterprise Implementation Roadmap
Moving from evaluation to deployment requires a structured approach. Enterprise SSI deployments that fail typically do so not because of technical limitations but because of poor integration planning, underestimated change management requirements, or attempting too broad an initial scope.
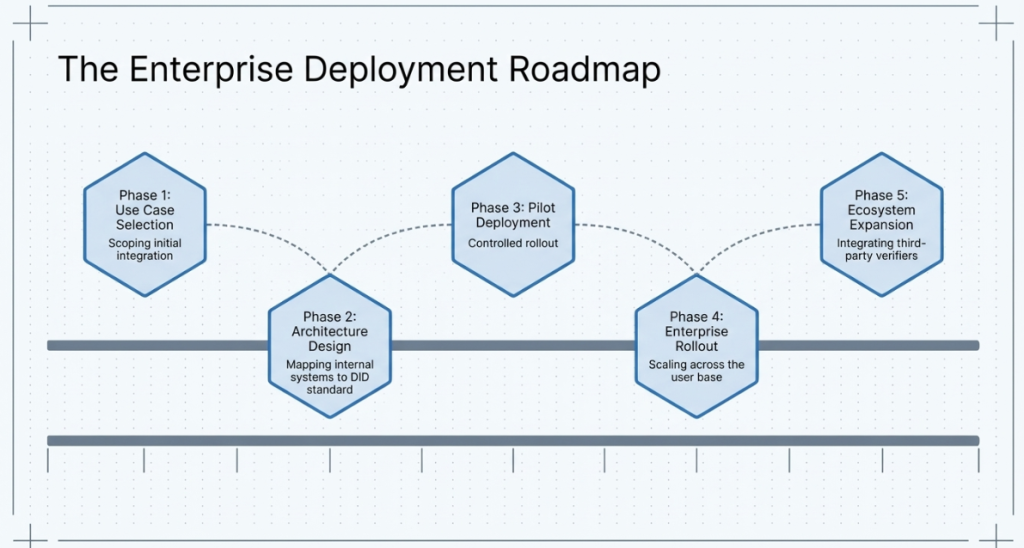
Phase 1: Use Case Identification and Prioritization (Weeks 1 to 6)
Not all enterprise identity workflows are equally suitable for SSI as an initial deployment. The strongest candidates for early deployment share specific characteristics: they involve cross-organizational verification, they have significant compliance overhead under current methods, and they are relatively self-contained so that integration dependencies are manageable.
Common high-value initial use cases include employee credential verification for contractor onboarding, customer KYC flows in regulated financial services, professional license verification for healthcare or legal services, and supplier compliance verification in complex supply chains.
The selection of the initial use case determines the technical integration requirements, the regulatory considerations, and the change management scope. It also determines the ROI model, which is critical for securing continued organizational commitment.
Phase 2: Infrastructure Evaluation and Selection (Weeks 4 to 10)
Infrastructure selection covers four decision areas: the DID method, the registry type, the wallet solution, and the integration architecture.
DID method selection depends on the jurisdiction, the performance requirements, and the existing technical infrastructure. Enterprises with existing Hyperledger deployments often find Hyperledger Indy or Hyperledger AnonCreds to be natural starting points. Enterprises operating globally across multiple jurisdictions may prefer DID methods that are registry-agnostic or that support multiple registry backends.
Registry selection involves evaluating public versus permissioned ledger options. Public blockchains offer decentralization and broad interoperability but introduce governance complexity. Permissioned ledgers like Hyperledger Fabric offer greater control and performance predictability but require consortium governance agreements.
Wallet solutions for enterprise contexts differ significantly from consumer SSI wallets. Enterprise wallets must integrate with existing HR systems, access management platforms, and compliance tooling. Key management is particularly critical: enterprise wallet infrastructure must support backup and recovery models that do not depend on individual users maintaining their own private keys, because employee turnover and device loss are operational realities.
Phase 3: Integration Architecture Design (Weeks 8 to 14)
The integration architecture connects the SSI credential layer to existing enterprise systems. Key integration points include the identity provider layer, the HR information system, the access management system, and the compliance and audit logging infrastructure.
For organizations using SecureX-DID, the integration architecture leverages a blockchain authentication layer that sits between the credential presentation layer and existing enterprise systems. This layer handles credential verification, maps verified claims to internal identity attributes, and feeds verification events to audit logs. The architecture is designed to minimize changes to existing downstream systems, which is the primary driver of deployment speed and risk reduction.
Phase 4: Pilot Deployment and Measurement (Weeks 12 to 20)
The pilot deployment should be scoped to the selected initial use case with a defined user population. Measurement during the pilot focuses on three areas: technical performance (verification latency, error rates, wallet adoption friction), compliance outcomes (data minimization compliance, audit log completeness, regulatory alignment), and business impact (onboarding time reduction, compliance cost reduction, user experience improvement).
The pilot period is also when integration issues surface and are resolved before broad deployment. Expect integration complexity to be higher than estimated, particularly at the interfaces between the SSI credential layer and existing identity management systems.
Phase 5: Organizational Scale and Ecosystem Expansion (Months 5 to 18)
After pilot validation, the deployment expands to additional use cases and user populations. At this stage, the ecosystem question becomes critical: SSI’s value compounds when multiple organizations within an ecosystem recognize each other’s credentials. Enterprises that successfully expand their SSI deployments typically do so in partnership with industry consortia, regulatory bodies, or sector-specific trust frameworks that govern cross-organizational credential recognition.
Section 7: The SecureX-DID Architecture in Context
SecureX-DID is SecureDApp’s enterprise self-sovereign identity infrastructure product. Understanding its positioning requires placing it within SecureDApp’s broader security stack.
SecureDApp is not an identity company that also does some blockchain work. It is a layered Web3 security infrastructure provider whose four products address the complete security lifecycle for blockchain-adjacent enterprise operations. Solidity Shield handles pre-deployment smart contract auditing. SecureWatch provides real-time runtime threat detection and containment. SecureTrace handles post-incident forensic investigation. SecureX-DID provides identity and compliance infrastructure.
This positioning matters for enterprise buyers because identity is not an isolated function. An enterprise deploying SSI infrastructure for KYC onboarding is also a potential target for identity-based attacks, smart contract vulnerabilities in DeFi integrations, and post-incident investigation needs. A vendor whose identity infrastructure is integrated with runtime monitoring and forensic capability provides a substantially more coherent security posture than a point-solution identity provider.
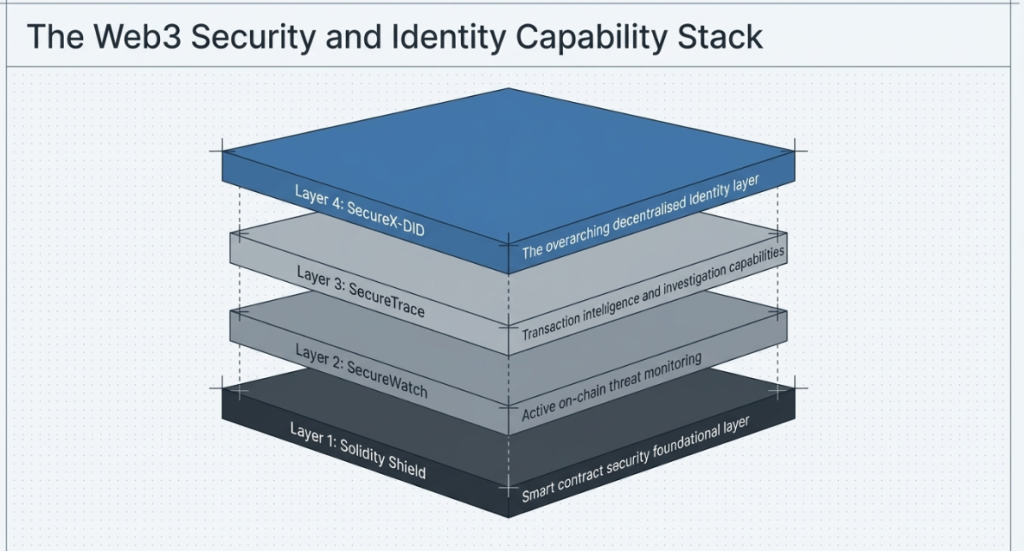
For the identity layer specifically, SecureX-DID implements the W3C DID and Verifiable Credentials specifications with four additional capability layers:
Zero-Knowledge Proof verification.
ZKP is not always necessary, but for high-sensitivity claims (regulatory status, biometric matching, age verification), it provides the strongest privacy guarantee. SecureX-DID integrates ZKP-based claim verification for scenarios where even selective disclosure of credential metadata would be problematic.
Merkle-based validation for selective disclosure.
For verification flows that require multiple discrete claims without full ZKP overhead, Merkle tree-based credential structures allow efficient selective disclosure with strong cryptographic guarantees.
Blockchain authentication layer.
The blockchain authentication layer provides tamper-evident logging of verification events without storing the underlying personal data. This creates a compliance-friendly audit trail that satisfies regulatory record-keeping requirements while preserving the data minimization properties of the broader architecture.
UIDAI OVSE integration capability.
For deployments in India or serving Indian users, the Aadhaar offline verification integration provides a regulated, privacy-preserving pathway for incorporating national biometric identity verification into SSI-based onboarding flows.
Platforms like SecureX-DID operationalize this architecture by providing enterprise integration tooling, consortium governance support, and compliance reporting infrastructure that reduces the organizational complexity of moving from SSI evaluation to production deployment.
Section 8: Enterprise ROI Analysis
The business case for self-sovereign identity in enterprise deployments rests on four primary value drivers.
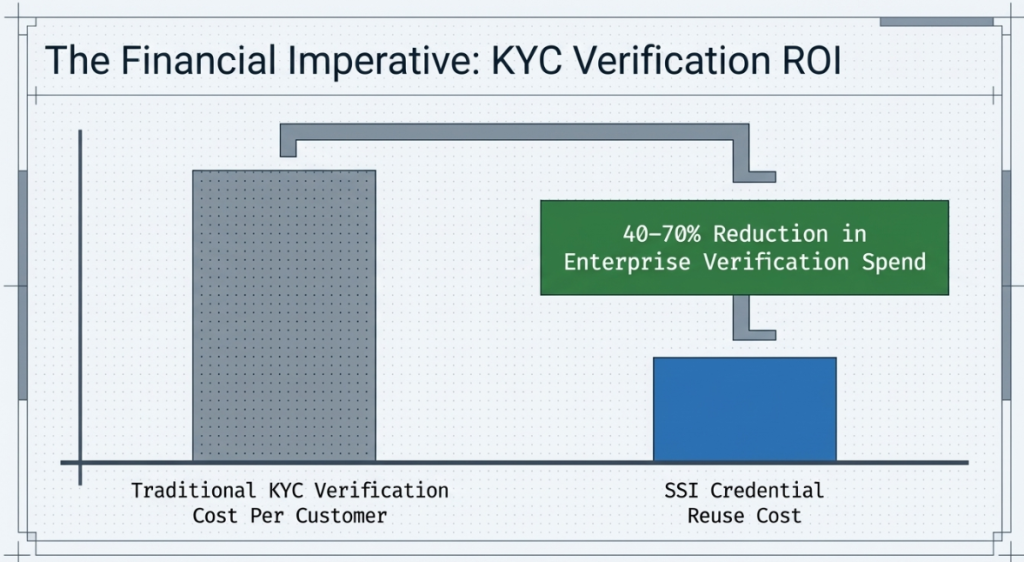
KYC and onboarding cost reduction.
In regulated financial services, the cost of a full KYC onboarding for a single customer ranges from $20 to over $100. And this depending on the jurisdiction and the complexity of the verification required. When a customer has already completed KYC at another institution and can present a verifiable credential attesting to that clearance, the verifying institution can reduce its own verification cost substantially. The exact reduction depends on the trust framework governing credential recognition, but industry pilots across Europe and Southeast Asia have demonstrated cost reductions of 40% to 70% for credential-reuse scenarios versus full re-verification.
Compliance cost reduction.
Organizations currently bear significant ongoing costs for maintaining compliance with data protection regulations as they apply to their identity data stores. These costs include data mapping exercises, data subject request handling, breach notification obligations, and the technical infrastructure required to manage data retention and deletion. SSI’s architectural data minimization reduces these costs by reducing the volume of personal data the organization needs to manage. The reduction is structural: when you do not receive and store personal data in the first place, you do not incur the compliance costs associated with managing it.
Breach impact reduction.
The financial impact of an identity data breach includes regulatory fines, breach notification costs, identity monitoring services for affected individuals, reputational damage, and customer churn. The average cost of a data breach involving personal identity data has risen consistently, reaching averages well above $4 million per incident in financial services contexts. SSI does not eliminate breach risk, but it eliminates the specific risk of centralized identity data store compromise, because no such store exists for the personal data handled through SSI flows.
Operational efficiency improvement.
Enterprise onboarding workflows that currently involve manual document collection, manual verification, and manual data entry into internal systems can be substantially automated when the onboarding process accepts verifiable credentials. The credential presentation and cryptographic verification steps can be fully automated. The data entry step is eliminated because the verified claims flow directly into the relevant internal systems.
Section 9: Addressing Common Enterprise Objections
“Our industry regulators haven’t approved SSI workflows.”
This objection reflects a misunderstanding of the regulatory landscape. Regulators do not typically pre-approve specific technical architectures. What they require is that organizations demonstrate compliance with substantive obligations: identity verification, record-keeping, data minimization, and so on. SSI architectures can satisfy these obligations. The work is in demonstrating that to regulators through documentation, compliance mapping, and sometimes regulatory engagement. Several jurisdictions, including the EU through its eIDAS 2.0 framework and India through its DPDP framework, are actively building regulatory structures that recognize SSI-based verification. Early movers who establish SSI workflows now are better positioned for these regulatory environments.
“We can’t control the security of credentials our customers hold.”
This objection conflates credential security with credential validity. The security of the holder’s wallet is the holder’s responsibility, as it is with any physical identity document. The organization’s concern should be whether a presented credential is genuine and currently valid, and cryptographic verification of the issuer signature plus real-time revocation registry checks address both of these concerns. An invalid credential, whether because it was revoked or because it was fraudulently constructed, fails cryptographic verification. The organization does not need to control the wallet to maintain confidence in verification outcomes.
“The SSI ecosystem is too fragmented for practical interoperability.”
This was a stronger objection three years ago than it is today. The W3C DID Core Recommendation, the Verifiable Credentials Data Model 2.0 specification, and the work of initiatives like the Trust Over IP Foundation have created meaningful standardization at the protocol layer. Interoperability between SSI implementations has improved substantially. That said, ecosystem fragmentation at the trust framework layer remains a real challenge. Organizations building SSI deployments need to engage with the relevant industry consortium or trust framework. This is important for their sector to ensure their credentials will be recognized by intended verifiers. This is a governance and business development challenge more than a technical one.
“We’ve invested heavily in our existing IAM infrastructure.”
As discussed in the comparative analysis section, SSI is not a replacement for existing IAM infrastructure in most deployment scenarios. It is an additional capability layer that addresses cross-organizational identity scenarios that existing IAM is not designed to handle well. The appropriate framing is not “SSI versus our existing IAM investment” but “what new capabilities does SSI enable that our existing IAM investment cannot provide.”
Section 10: Forward-Looking Perspective
Several technical and regulatory developments in the next three to five years will shape how enterprise SSI deployments evolve.
eIDAS 2.0 and the European Digital Identity Wallet.
The European Union’s revised eIDAS regulation, which entered into force in 2024, mandates that EU member states provide digital identity wallets to their citizens by 2026. These wallets will be able to hold government-issued credentials and will be usable for both public and private sector authentication across the EU. For enterprises operating in European markets, this creates a mandated SSI-compatible credential infrastructure that significantly reduces the ecosystem adoption challenge. By 2027, enterprises that have invested in SSI-compatible verification infrastructure will be positioned to accept government-issued verifiable credentials from European customers as a matter of course.
The convergence of AI identity verification with SSI.
AI-based biometric identity verification has grown rapidly as an onboarding technology. The combination of AI verification with SSI credential issuance creates a powerful workflow: AI verifies the user’s biometric identity and documents once, an issuer generates a verifiable credential attesting to the verification outcome, and the user can subsequently reuse that credential for any verifier who trusts the issuing organization’s verification methodology. This combination is more privacy-preserving than AI verification alone, because the credential can be presented to subsequent verifiers without re-transmitting the biometric data.
Zero-trust architecture integration.
The zero-trust security model, now adopted as a foundational framework by major enterprise security programs, has natural alignment with SSI principles. Zero trust requires continuous verification of identity, context, and access rights rather than assuming trust based on network location. SSI provides a credential mechanism for continuous identity verification that is independent of network perimeter assumptions. As zero-trust implementations mature, SSI is likely to become a primary identity credential mechanism for enterprises that want to extend zero-trust principles to cross-organizational contexts.
Regulatory convergence on data minimization.
The global trajectory of data protection regulation is clearly toward stronger data minimization requirements and greater individual control over personal data. GDPR was an early and strong expression of this direction. India’s DPDP Act, Brazil’s LGPD, and sector-specific frameworks in financial services and healthcare are all moving in the same direction. Organizations that adopt SSI architecture now are building infrastructure that aligns with the regulatory direction, reducing future compliance retrofitting costs.
Quantum resistance in credential cryptography.
Current SSI implementations rely on cryptographic primitives that are vulnerable to sufficiently powerful quantum computers. While quantum computers capable of breaking current elliptic curve cryptography are not yet operational, the National Institute of Standards and Technology in the United States finalized post-quantum cryptographic standards in 2024. Enterprise SSI deployments with long time horizons should evaluate the quantum resistance roadmaps of their chosen infrastructure providers. SecureX-DID’s development roadmap addresses post-quantum credential cryptography as a future capability, reflecting the need to maintain long-term credential integrity.
Conclusion: The Decision Framework
Self-sovereign identity for enterprises has moved beyond the proof-of-concept stage. Organizations now deploy it in production across regulated financial services, healthcare, education, and government sectors globally. Industry bodies have stabilized the standards. Regulators are aligning frameworks. Technology providers continue maturing the tooling. Enterprises can now clearly demonstrate ROI.
Enterprise leaders evaluating SSI should not ask whether the technology is ready. They should ask whether their organization can capture the early-mover advantage in its sector’s trust ecosystem.
Organizations that move first in their sector to establish SSI-based credential issuance anchor the trust ecosystem. Sector peers accept their credentials. Their verification workflows set the benchmark against which compliance teams measure performance. Their integration decisions shape governance structures and influence how the trust framework evolves.
Organizations that delay adoption wait until regulatory mandates or competitive pressure force implementation. They then absorb the cost of late adoption under compressed timelines. History demonstrates this pattern. When industries adopted TLS for web security, SWIFT gpi for cross-border payments, and SAML for federated identity, late adopters incurred significantly higher direct implementation costs and substantial opportunity losses.
Organizations can execute a phased strategy by starting with a high-value use case, proving measurable ROI, and expanding systematically. Technology partners now provide the required infrastructure, including W3C-compliant DID and VC implementations, ZKP-enabled selective disclosure, Merkle-based credential validation, and UIDAI-registered Aadhaar integration capabilities through platforms such as SecureX-DID.
The strategic window to establish identity infrastructure leadership in the Web3 and enterprise blockchain ecosystem remains open. Leaders who act decisively can define their sector’s trust architecture before competitors do. leadership in the Web3 and enterprise blockchain ecosystem is open. It will not remain open indefinitely.
Frequently Asked Questions on self-sovereign identity
Self-sovereign identity allows users to control their own digital credentials through a secure wallet. Instead of relying on a central identity provider, SSI enables direct cryptographic verification between issuer and verifier, with the user actively approving what data gets shared.
Yes. Organizations can verify cryptographically signed claims instead of storing raw personal data. They can maintain audit trails, run revocation checks, and demonstrate regulatory compliance through structured verification logs aligned with KYC and AML obligations.
Zero-knowledge proofs allow users to prove specific claims such as age, residency, or regulatory status without revealing underlying personal data. Enterprises typically use ZKPs for high-sensitivity use cases and selective disclosure for standard verification flows.
SecureX-DID integrates Aadhaar-based offline verification under registration with the Unique Identification Authority of India as an Offline Verification Seeking Entity (OVSE). This enables enterprises to incorporate privacy-preserving Aadhaar verification into SSI onboarding workflows while remaining compliant with the Aadhaar Act 2016.



