Here is a misconception that has cost organizations and individuals dearly. Most people who entered Web3 believed blockchain was anonymous. They were completely wrong. Blockchain is, in fact, one of the most transparent financial ledgers ever created. Every transaction is recorded permanently, publicly, and in sequence. Furthermore, anyone with the right tools can trace money across wallets, chains, and exchanges with remarkable precision.
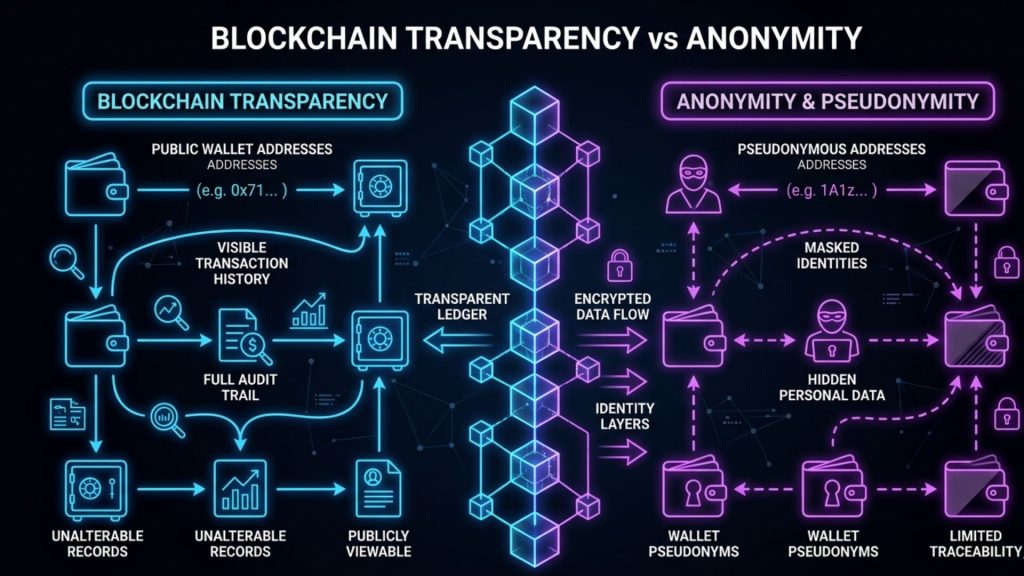
That transparency cuts both ways. On one hand, it is what makes blockchain forensics not only possible but increasingly powerful. On the other hand, it is also why regulators, exchanges, law enforcement agencies, and enterprise security teams are investing heavily in on-chain analysis capabilities. The ledger does not forget. The question is simply whether someone is reading it carefully.
So what exactly is blockchain forensics? How does a blockchain investigation actually work? And more importantly, what does it mean for a CTO, CISO, or Web3 founder building products and protocols in this space?
This guide covers all of it. From the foundational mechanics of transaction tracing to real-world crypto fraud detection scenarios, from the technical methodology behind on-chain analysis to the compliance obligations under AML crypto frameworks, you will walk away with a clear and practical understanding of how blockchain forensics operates and why it matters deeply for your organization.
What Is Blockchain Forensics and Why Does It Matter Right Now
Most disciplines evolve slowly. Blockchain forensics is not one of them. In just a few years, it has moved from a niche law enforcement tool to a core operational requirement for exchanges, DeFi protocols, enterprise Web3 teams, and compliance departments globally.
Blockchain forensics is the discipline of investigating, analyzing, and interpreting on-chain data to trace cryptocurrency movements, identify illicit actors, support legal proceedings, and enforce regulatory compliance. It draws from cryptography, data analytics, network science, and financial intelligence. Together, these disciplines allow investigators to reconstruct the financial story hidden inside a blockchain.
For years, this was a capability available only to a handful of specialized firms. Chainalysis, Elliptic, and a few others served large exchanges and government agencies. However, the landscape has changed dramatically. DeFi protocols, NFT markets, cross-chain bridges, and Layer 2 networks have created a far more complex transaction environment than existed even three years ago. Meanwhile, illicit on-chain activity has grown in both volume and sophistication, with billions moving annually through mixers, privacy coins, and multi-hop laundering schemes designed specifically to defeat simple analysis.
As a result, blockchain forensics is no longer optional. It is a core security and compliance function for any serious organization operating in Web3.
Three Forces Accelerating the Shift
First, regulatory pressure is intensifying globally. The Financial Action Task Force Travel Rule now requires virtual asset service providers to transmit sender and recipient information alongside transactions. The EU’s Markets in Crypto-Assets regulation extends similar obligations to a broad range of digital asset businesses. In India, the Financial Intelligence Unit mandates exchange registration and AML compliance with specific monitoring requirements.
Second, the threat environment is escalating rapidly. Crypto fraud has evolved well beyond simple rug pulls. Today’s attacks involve sophisticated multi-stage operations using flash loans, oracle manipulation, and deliberate cross-chain fund movement designed to obscure the money trail. Consequently, reactive security is no longer sufficient.
Third, institutional adoption brings institutional accountability. Banks, investment funds, and enterprise Web3 builders cannot afford to be connected to illicit funds, even unknowingly. Therefore, due diligence now routinely includes on-chain screening of wallets and counterparties before any significant transaction or partnership.
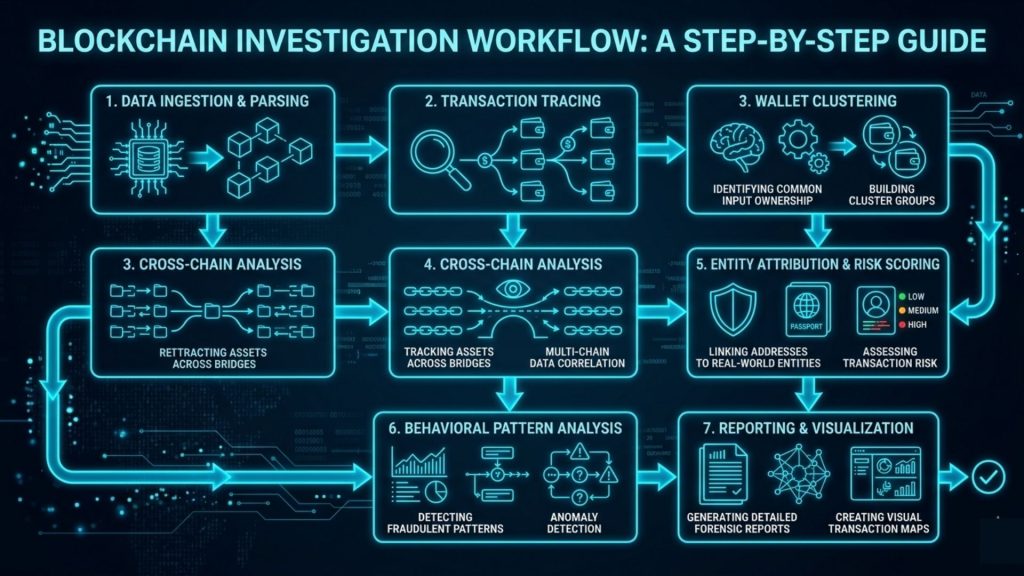
How Blockchain Investigations Work: The Core Methodology
Understanding blockchain forensics requires understanding how a blockchain investigation is actually structured. There is no single universal method. However, most professional investigations follow a process built around four core activities. Each one builds on the previous, creating a layered and reliable investigative framework.
Transaction Graph Analysis
Here is where every serious blockchain investigation begins. Every blockchain transaction creates a direct link between input and output addresses. When you map these links across hundreds or thousands of transactions, you create what forensic analysts call a transaction graph. Think of it as a network map showing exactly how funds moved across wallets over time.
Transaction graph analysis is the backbone of any blockchain investigation. By following funds from a known source wallet, investigators can determine where money went, which intermediate wallets were used as layering stops, and where funds ultimately settled. Moreover, the public nature of the blockchain means this data is available to anyone with the right tools, without requiring a subpoena or court order.
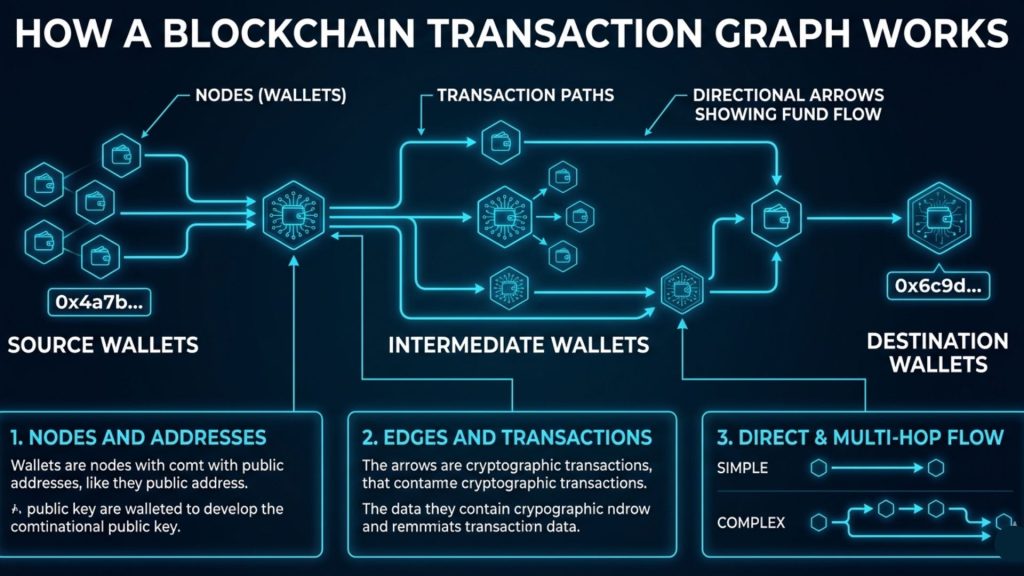
Consider a concrete example. A DeFi protocol is drained of four million dollars through a flash loan attack. The attacker controls Wallet A, which immediately receives the stolen funds. Within hours, the attacker splits the funds across ten newly created wallets, waits 48 hours, and then begins routing funds toward a centralized exchange for conversion. A competent blockchain forensics team can map this entire transaction graph, identify the destination exchange wallets, and coordinate with the exchange to freeze the funds before the attacker completes the cash-out. This is transaction tracing in action, and it illustrates precisely why speed and tooling both matter.
Cluster Analysis and Address Attribution
One of the most powerful techniques in crypto forensics is cluster analysis. Most users and threat actors control multiple wallets simultaneously. Because of how cryptocurrency transactions work, however, wallets controlled by the same entity tend to leave detectable fingerprints across the blockchain.
The most widely used clustering technique is the Common Input Ownership Heuristic, or CIOH. When a transaction combines inputs from multiple addresses into a single transaction, it strongly suggests those input addresses are controlled by the same entity. The logic is simple: signing all inputs simultaneously requires access to all the corresponding private keys. Therefore, multiple co-signing addresses almost certainly belong to the same wallet owner.
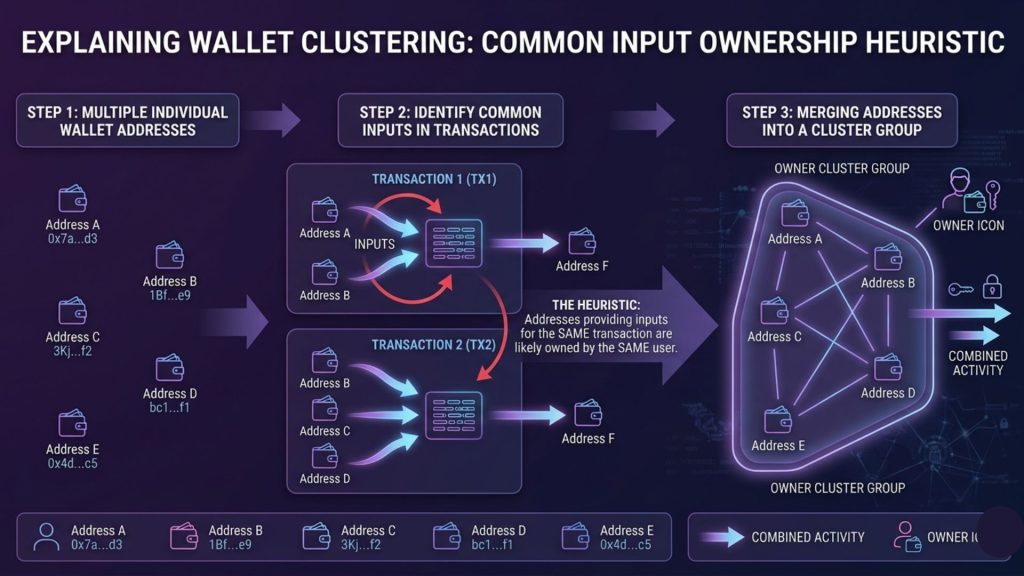
By applying CIOH and related heuristics at scale, forensic investigators can group thousands of seemingly unrelated wallet addresses into entity clusters. Once a cluster is identified, linking even a single address in that cluster to a known entity often de-anonymizes all associated wallets simultaneously. This is one of the most common ways sophisticated attackers eventually expose themselves: a single consolidation transaction, months after the original attack, connects an anonymous wallet to a previously attributed address and unravels the entire concealment effort.
Furthermore, leading blockchain forensics firms maintain enormous databases of labeled addresses. Exchange hot wallets, known mixer entry points, sanctioned wallets, darknet market addresses, and ransomware payment wallets are all tagged and continuously updated. When traced funds touch a labeled address, the investigation gains an anchor point that can dramatically accelerate the remaining analysis.
On-Chain Behavioral Pattern Recognition
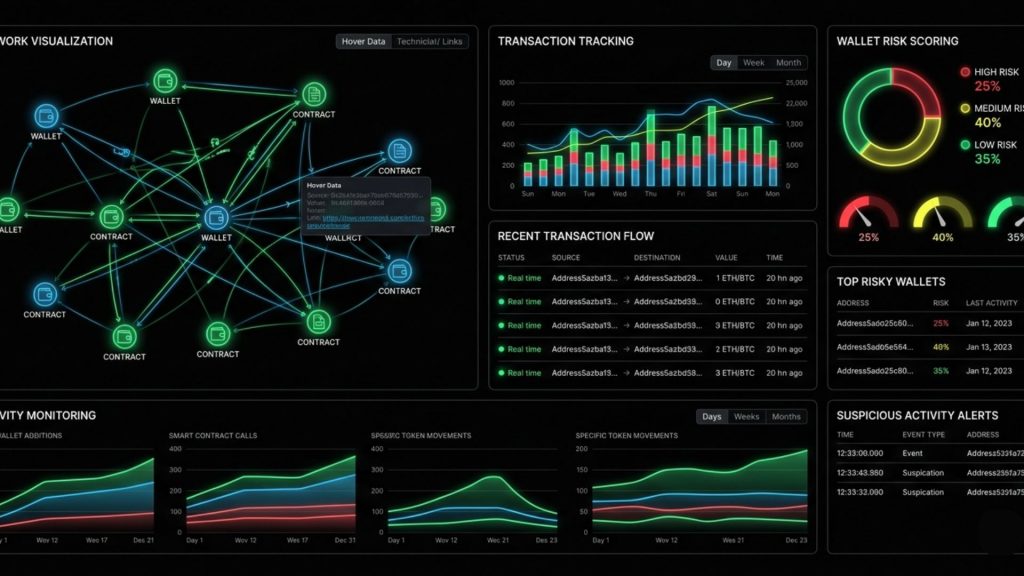
Beyond tracing individual transactions, mature on-chain analysis involves recognizing behavioral patterns that signal specific types of activity. These patterns help distinguish normal user behavior from suspicious or illicit fund flows, even when no individual transaction is obviously problematic on its own.
For example, a wallet that receives small amounts from hundreds of different addresses simultaneously often indicates mixer output. A wallet with no prior transaction history that suddenly receives a large sum immediately following a protocol exploit is an immediate red flag. A rapid sequence of transfers across newly created wallets with zero prior activity strongly suggests a layering operation, which is the second stage of the classic money laundering cycle: placement, layering, and integration.
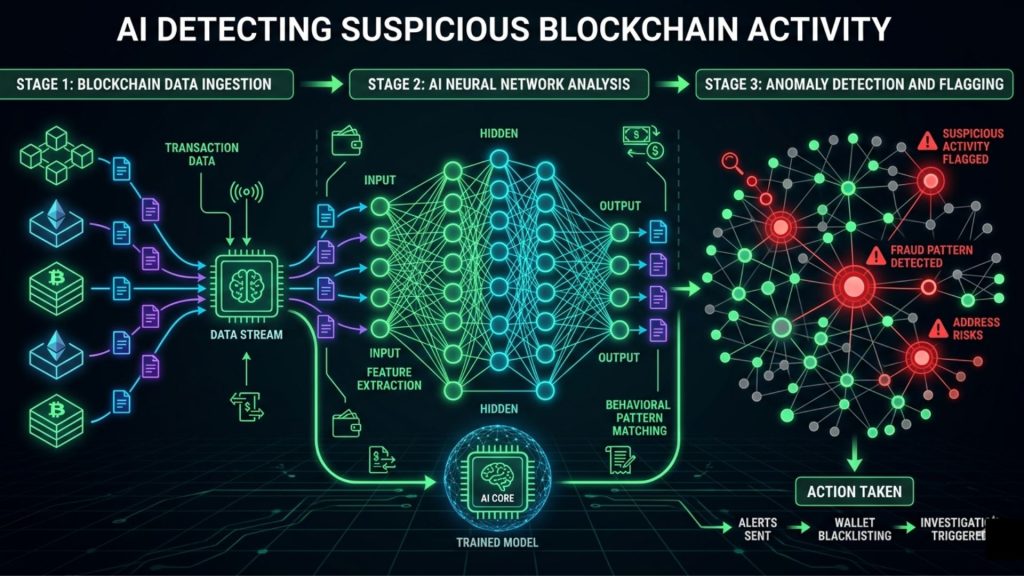
Pattern recognition is also where machine learning increasingly plays a valuable role. Modern blockchain forensics platforms use graph neural networks and anomaly detection models trained on labeled datasets of known illicit behavior. These models can surface suspicious wallets and transaction patterns far faster than manual review. However, it is important to note that pattern recognition generates investigative leads. Skilled human analysis converts those leads into actionable and defensible intelligence.
Cross-Chain and Off-Chain Intelligence Integration
Blockchain forensics does not stop at the chain boundary, and experienced investigators know this well. Increasingly, threat actors use cross-chain bridges to move funds between networks, hoping investigators lose the trail when assets hop from Ethereum to Avalanche or from BNB Chain to Solana.
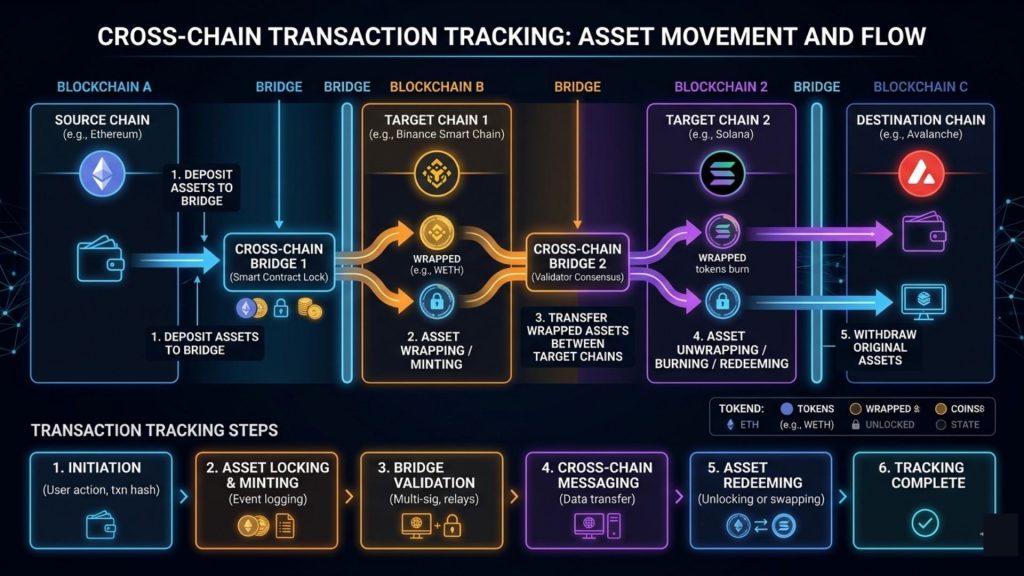
Modern blockchain investigation methodology therefore includes cross-chain tracking. When funds move through a bridge, forensic tools can often reconcile input and output amounts across the two networks and continue following the money. This is not always straightforward, particularly with privacy-preserving bridges, but the capability is improving rapidly as investigators develop network-specific expertise.
Off-chain intelligence integration is equally important. IP address data from blockchain nodes, exchange KYC records obtained via legal process, social media metadata, forum intelligence, and dark web market data all feed into comprehensive blockchain investigations. On-chain analysis tells you where the money went. Off-chain intelligence tells you who was actually behind those wallets.
The Anatomy of Crypto Fraud Detection
Knowing how money moves is one thing. Knowing how fraud looks on-chain is another. Crypto fraud detection is one of the most urgently practical applications of blockchain forensics, and it is relevant to any organization that handles, processes, or builds with cryptocurrency.
Smart Contract Exploits and Fund Tracking
Smart contract exploits are among the most damaging and most common events in Web3. When a protocol is drained through a vulnerability, the forensic challenge is immediate: funds move within minutes of the attack, and sophisticated attackers frequently have escape routes pre-planned before they execute.
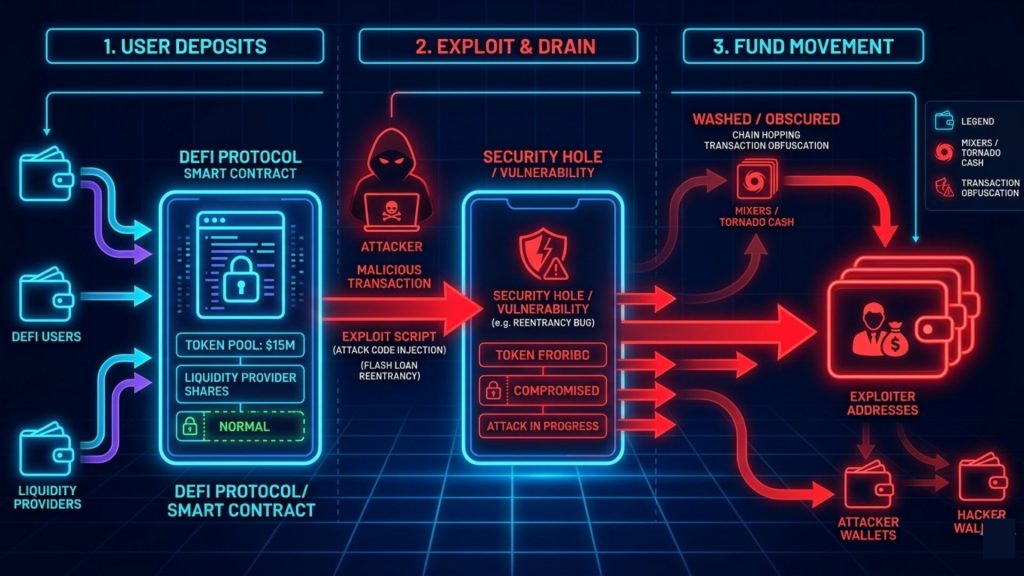
Effective crypto fraud detection in this context demands real-time monitoring of on-chain activity. The moment unusual fund flows are detected from a protocol’s treasury or liquidity pool, investigators need to begin transaction tracing immediately. Speed is not merely helpful. It is often the difference between partial recovery and total loss. Funds that reach a centralized exchange before alerts are issued can sometimes be frozen at the exchange level. Funds that enter a mixer or cross a bridge into a privacy-preserving network become significantly harder to track and almost impossible to recover without law enforcement involvement.
This is precisely why proactive monitoring matters more than reactive response. Organizations that wait for an exploit to complete before beginning any investigation are already many steps behind. The most effective crypto forensics frameworks involve continuous monitoring of smart contract interactions and wallet behavior, with automated alerts firing the moment anomalous patterns appear.
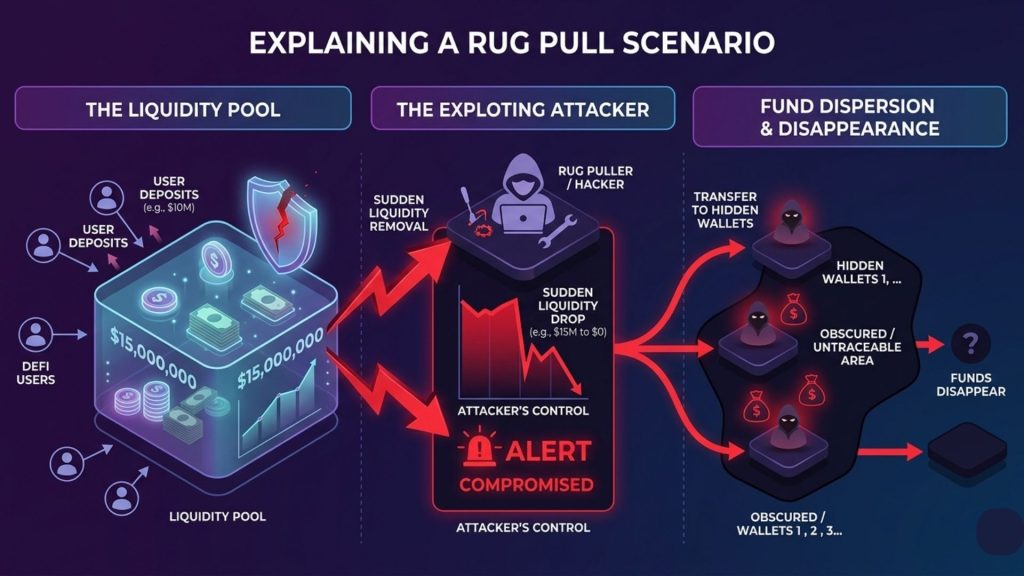
Rug Pulls and Exit Scam Detection
Rug pulls are a persistent and deeply damaging form of crypto fraud. Project founders quietly drain liquidity or treasury funds after attracting investor capital and then disappear. The on-chain signature of a rug pull is often identifiable in retrospect. Increasingly, however, blockchain forensics tools can flag early warning signals before the event occurs.
Common on-chain precursors to a rug pull include heavily concentrated token distribution among founder-controlled wallets, rapid accumulation of liquidity tokens in the days before a drain, and test transactions sent to known mixing services. By continuously monitoring token contract deployer wallets and their associated addresses, on-chain analysts can sometimes identify rug pull preparation days in advance. Moreover, if the same deployer wallet has been connected to prior fraudulent projects, that historical connection provides a powerful early warning signal.
After a rug pull occurs, blockchain investigation is essential for legal recourse and exchange intervention. Tracing stolen funds across wallets provides the evidentiary basis for civil litigation and, in many jurisdictions, criminal prosecution. Without that on-chain trail, victims have almost no recourse.
Mixer and Tumbler Analysis
Mixers and tumblers are services specifically designed to obscure the transaction history of cryptocurrency. They pool funds from multiple depositors and return equivalent amounts from pooled reserves, breaking the direct link between the original source and the eventual destination.
For many years, mixers were treated as nearly forensically impenetrable. That assumption has been significantly revised. Advances in blockchain forensics have produced techniques including amount correlation, timing analysis, and cross-referencing of mixer entry and exit patterns that allow investigators to de-anonymize mixer usage with meaningful success rates in specific scenarios. These techniques are particularly effective against simpler mixer services and against users who make common operational mistakes.
Additionally, the OFAC sanctioning of Tornado Cash in 2022 sent a clear signal to the industry: using sanctioned mixing services carries direct legal risk regardless of intent. For organizations conducting AML crypto compliance, screening for mixer exposure in incoming transactions has therefore become a standard part of counterparty due diligence.
NFT and Token Fraud on the Blockchain
Blockchain forensics extends well beyond ETH and BTC transfers. NFT markets have been heavily exploited for wash trading, money laundering, and outright fraud. On-chain analysis in the NFT context involves tracking token transfer histories, identifying circular trading patterns between related wallets, and spotting royalty manipulation schemes where project insiders inflate sales volume to attract outside buyers.
Token forensics involves tracing newly deployed token contracts from deployer addresses, analyzing distribution patterns for insider concentration, and monitoring for coordinated dump behavior from founder wallets after liquidity events. Both NFT and token forensics are growing rapidly in importance as regulators increase scrutiny of these markets for potential AML and securities violations.
Blockchain Compliance: What Organizations Are Actually Required to Do
Here is where theory meets obligation. Understanding blockchain forensics from an investigative perspective is valuable. However, for most organizations reading this, the more immediate concern is compliance. Specifically, what are you actually required to do, and what does non-compliance cost you?
The answer varies by jurisdiction. Nevertheless, several themes are consistent across the most significant regulatory frameworks globally.
Know Your Transaction (KYT) Obligations
Traditional AML compliance centers on Know Your Customer, or KYC. In the crypto context, this extends to Know Your Transaction, or KYT. Financial institutions and virtual asset service providers are increasingly required not only to verify customer identity but to monitor the on-chain behavior of those customers’ wallets and flag transactions involving high-risk counterparties.
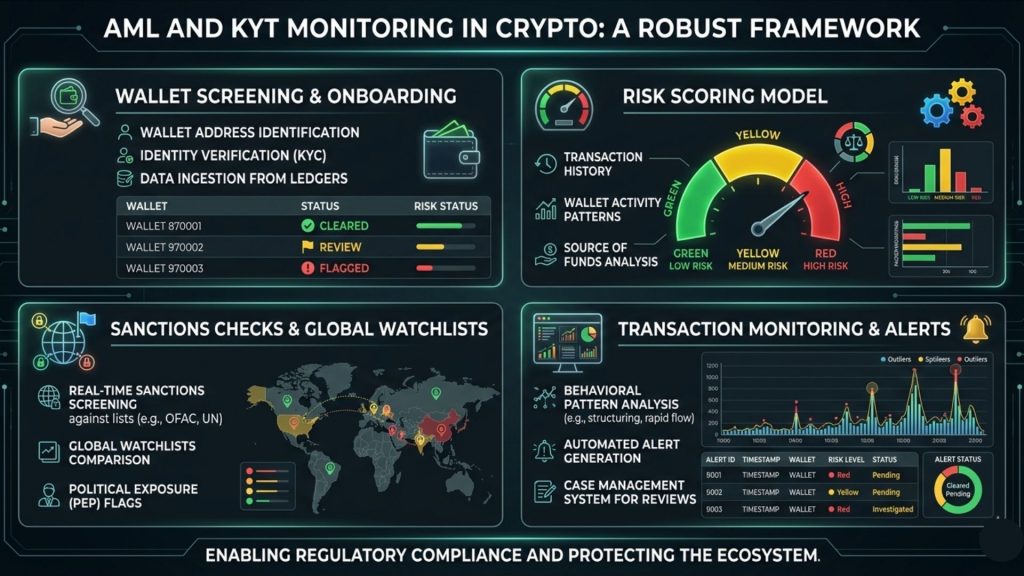
KYT involves continuous wallet screening against sanctions lists, known illicit address databases, and risk-scored address clusters. Every incoming and outgoing transaction should be assessed for exposure to wallets associated with darknet markets, ransomware campaigns, exchange hacks, fraud schemes, and OFAC-sanctioned entities. For a crypto exchange, this is a regulatory baseline. For a DeFi protocol or Web3 application, it is increasingly an expectation from institutional counterparties even where direct legal obligation may remain unclear.
The Travel Rule and Cross-Border Information Sharing
The FATF Travel Rule requires virtual asset service providers to collect and transmit originator and beneficiary information alongside cryptocurrency transactions above defined thresholds. This mirrors the longstanding Travel Rule in traditional finance, which requires banks to share transaction metadata across borders.
Implementing Travel Rule compliance in a blockchain context is technically non-trivial. The pseudonymous nature of blockchain wallets means that identifying counterparty VASPs automatically requires integration with cross-industry registries and dedicated Travel Rule solution providers. Importantly, blockchain forensics capabilities are a prerequisite for robust Travel Rule compliance. Before transmitting information about a transaction, organizations need confidence in both the identity of the counterparty VASP and the risk profile of the specific wallet involved.
Sanctions Screening and Real-Time Wallet Monitoring
Beyond transaction monitoring, organizations with meaningful blockchain exposure need to implement sanctions screening that specifically covers cryptocurrency wallet addresses. The OFAC SDN list now includes hundreds of crypto addresses, and this number continues to grow. Transacting with a sanctioned address, even unknowingly, can result in serious enforcement action.
Real-time sanctions screening should therefore be integrated directly into transaction processing pipelines. Any transaction involving a flagged address should be blocked, reviewed, and reported where regulations require it. At scale, this process cannot be manual. It requires automated on-chain analysis tools with continuously updated sanctions database integration and reliable alert mechanisms.
Adverse media monitoring adds another important layer, tracking public reports of fraud, hacks, or regulatory action connected to known wallet addresses and protocols. Organizations that incorporate this intelligence into their screening programs have significantly better visibility into emerging risks before they crystallize into direct exposure.
From Capability to Execution: How SecureTrace Supports Blockchain Investigations
Most organizations building in Web3 understand the need for blockchain forensics in principle. The challenge, consistently, is execution. Building an in-house on-chain analysis capability from scratch requires significant investment: blockchain data infrastructure, labeled address databases, forensic tooling, skilled analysts, and ongoing maintenance as the on-chain environment evolves.
For many teams, particularly those growing quickly or operating under resource constraints, that investment is not yet feasible. Yet the need does not wait.
This is where SecureTrace, developed by SecureDApp, addresses a practical and specific gap. SecureTrace is purpose-built for transaction tracing, blockchain forensics, and investigation support. Rather than requiring organizations to build proprietary forensic infrastructure internally, SecureTrace delivers on-chain analysis capabilities that would otherwise be available only to large exchanges, government agencies, and specialized forensic firms.
In practical terms, SecureTrace enables organizations to trace fund flows across wallets and transactions, identify wallet clusters associated with known threat actors, screen addresses against sanctions lists and labeled databases, generate investigation-quality reports for legal or regulatory use, and monitor ongoing transaction activity for anomalous patterns that warrant immediate review.
Consider what this means for specific roles. A CISO at a crypto exchange dealing with a suspicious large withdrawal has the transaction tracing capability to map where those funds originated, whether they carry exposure to illicit sources, and whether the deposit should be held for further review. A Web3 founder whose protocol has been exploited can use SecureTrace to begin tracking stolen assets immediately, building the evidentiary record while the trail is still fresh.
Notably, SecureTrace is designed specifically for the forensic use case rather than general monitoring. The quality of address attribution, the depth of transaction graph analysis, and the reliability of investigation reports all directly affect legal and regulatory outcomes. That specificity of purpose matters when results need to hold up under scrutiny.
SecureTrace is part of SecureDApp’s broader blockchain security ecosystem, which also includes smart contract auditing through Solidity Shield and continuous threat monitoring through SecureWatch. For blockchain forensics and investigation specifically, SecureTrace is the purpose-built solution.
Advanced On-Chain Analysis Techniques
The core techniques covered so far represent the foundation. However, mature on-chain analysis encompasses several additional methods that experienced practitioners apply in more complex or nuanced investigations. Understanding these techniques helps CTOs and CISOs evaluate the true depth of any forensics capability, whether built internally or sourced from a third party.
Dust Attack Analysis
Dusting attacks involve sending tiny amounts of cryptocurrency to a large number of wallets. The attacker’s goal is de-anonymization. If the wallet holder later spends the dust amount by combining it with other funds in a new transaction, the attacker can apply clustering heuristics to link that wallet to other addresses in the holder’s broader portfolio.
For organizations managing large numbers of operational wallets, understanding dust attacks and implementing dust control policies is both a security hygiene measure and a forensically important practice. Specifically, avoiding the spending of unrecognized dust inputs prevents the inadvertent exposure of address clusters to external observers who may be actively attempting to map ownership.
DeFi Protocol-Level Forensics
DeFi introduces forensic challenges that simply do not exist in simple wallet-to-wallet transfer environments. A single DeFi attack can span dozens of smart contract interactions across multiple protocols, all compressed into a handful of consecutive blocks. The transaction graph of a sophisticated flash loan exploit, for example, may involve a lending protocol, an automated market maker, a price oracle, and a bridge, all within the same transaction bundle.
Protocol-level forensics requires understanding the specific smart contract logic of each protocol involved. An investigator needs to know what a legitimate Uniswap liquidity provision looks like on-chain versus a sandwich attack versus a flash loan arbitrage exploit. Without that contextual knowledge, transaction tracing in DeFi produces an incomplete or potentially misleading picture. This is one of the most technically demanding areas of blockchain forensics, and consequently one where deep specialization delivers measurably better results than generic blockchain analysis tools.
Layer 2 and Sidechain Investigations
As Ethereum Layer 2 networks such as Arbitrum, Optimism, and zkSync grow in adoption, and as sidechains like Polygon carry increasingly significant transaction volumes, blockchain forensics must extend effectively to these environments. This is not automatic. Layer 2 forensics is inherently more complex than Layer 1 analysis.
Some Layer 2 networks batch multiple transactions together, which complicates individual transaction attribution. Others use validity proofs or optimistic rollup mechanisms that affect how transaction data is available and verifiable on-chain. Additionally, the bridge between Layer 1 and Layer 2 is itself a forensically critical point. Tracking funds as they deposit into or withdraw from a bridge often confirms the continuity of a money trail across network layers, which is essential for maintaining a defensible investigative record.
Behavioral Fingerprinting Across Wallets
Beyond clustering, experienced investigators apply behavioral fingerprinting techniques to identify consistent patterns across seemingly unrelated wallets. These patterns include characteristic transaction timing, consistent gas price behavior, recurring transaction amounts, and preferred exchange deposit addresses. When multiple wallets share several of these behavioral characteristics, it creates a probabilistic case for shared ownership even without direct clustering evidence. This technique is particularly valuable in cases where adversaries have deliberately avoided consolidation transactions specifically to prevent CIOH-based clustering from working against them.
Building an Internal Blockchain Forensics Capability
For larger organizations with significant exposure to digital assets, building some degree of internal blockchain forensics capability is a strategic investment worth making. This does not mean duplicating what specialized firms provide. Rather, it means developing the organizational ability to engage intelligently with on-chain data, interpret findings accurately, and act quickly when situations demand it.
What a Minimum Viable Capability Looks Like
At a minimum, a Web3 organization should be able to independently query blockchain data for any wallet or transaction relevant to its operations. It should be able to interpret a basic transaction graph without fully relying on third-party interpretation for every decision. It should screen counterparty wallets before significant transactions or partnership integrations. And it should understand the output of forensic reports produced by external specialists clearly enough to act on them without delay.
These capabilities require investment in three areas. First, tooling: access to blockchain indexing tools and labeled address databases. Second, training: building analyst-level competency in at least one or two dedicated team members. Third, process: integrating on-chain checks into both security incident response workflows and compliance review procedures so they happen automatically rather than on an ad-hoc basis.
When to Engage External Forensic Specialists
Even well-resourced organizations with internal capabilities should engage external forensic specialists in several specific situations. These include incidents that require legal-quality evidence for court proceedings or regulatory submissions, cases where the complexity of the money trail exceeds internal team capacity, and scenarios where regulatory reporting requires independently validated expert analysis.
Additionally, pre-incident retainer agreements with forensic providers are increasingly common among mature Web3 security programs. Having a provider and workflow already established before an incident occurs dramatically reduces response time when speed is critical. For organizations using SecureTrace, this means the tooling, the data access, and the reporting pipeline are all in place before the situation arises where they are urgently needed.
Documentation, Chain of Custody, and Legal Defensibility
One consistently overlooked aspect of blockchain forensics in organizational practice is documentation. For any investigation that may have legal or regulatory implications, maintaining a clear chain of custody for blockchain evidence is essential and non-negotiable.
This means documenting the data sources used in the investigation, the specific methodology applied at each analytical stage, the tools and tool versions used, and the reasoning behind key investigative decisions. Courts and regulators increasingly need to understand not just what blockchain evidence shows, but precisely how it was obtained and interpreted. Organizations that invest in proper forensic documentation practices are significantly better positioned when investigations progress to formal legal proceedings.
AML Crypto: The Regulatory Landscape in Detail
Blockchain compliance and AML crypto obligations are converging faster than most organizations anticipated. Teams that treat these as separate concerns will find themselves caught between escalating regulations and inadequate technical capabilities at exactly the wrong moment.
FATF Guidance and the Global Baseline
The FATF Recommendations, specifically Recommendation 15 regarding new technologies, establish the global baseline for AML obligations in the crypto sector. FATF’s detailed guidance explicitly includes DeFi platforms and NFT marketplaces within its scope, depending on the degree of centralized control or profit extraction involved in their operation.
FATF also introduced the concept of the sunrise issue, acknowledging that Travel Rule compliance requires coordinated adoption across jurisdictions to function effectively. Nevertheless, FATF has been explicit that phased implementation does not mean indefinite non-compliance. Organizations should be moving toward Travel Rule-capable infrastructure regardless of whether their immediate jurisdiction has formally mandated it, because the regulatory direction is unambiguous.
Regional Variations Across India, EU, and the United States
In India, the Financial Intelligence Unit has mandated registration and AML compliance for crypto exchanges. The framework draws significantly from existing banking AML requirements, including transaction monitoring, suspicious transaction reporting, and record-keeping obligations that align closely with international standards.
In the European Union, MiCA and the Transfer of Funds Regulation together create a comprehensive framework for crypto-asset service providers. The TFR extends Travel Rule obligations to crypto transactions and applies to all transfers involving EU-regulated CASPs regardless of transaction size. This is more stringent than the FATF baseline and reflects the EU’s broader push toward comprehensive crypto regulatory clarity.
In the United States, FinCEN has treated crypto exchanges as money service businesses for years, requiring full Bank Secrecy Act compliance including AML programs, suspicious activity reports, and currency transaction reports. Recent regulatory signals indicate increasing scrutiny of DeFi platforms and non-custodial wallet interactions, suggesting the compliance perimeter will continue to expand in the near term.
The common thread across all three jurisdictions is the expectation of effective transaction monitoring. Regulators are not simply asking for a written AML policy. They want operational evidence that the policy functions in practice. That operational evidence requires blockchain forensics capability.
Suspicious Transaction Reporting in the Crypto Context
Filing a suspicious transaction report in the crypto context requires considerably more than identifying an unusual transaction amount. Regulators increasingly expect reports to include on-chain evidence: wallet addresses, transaction hashes, fund flow summaries, connections to known risk indicators, and a clear narrative of the on-chain activity that triggered the report.
Producing this quality of report without blockchain forensics capability is nearly impossible at scale. Organizations that invest in on-chain analysis tooling are in a structurally stronger position to meet reporting obligations accurately, efficiently, and in a format that regulators find useful and actionable.
Real-World Scenarios: Blockchain Forensics in Practice
Theory is valuable. But concrete scenarios make the stakes real. The following three scenarios illustrate how blockchain forensics operates across different organizational contexts and risk situations.
Scenario 1: Exchange Handles a High-Risk Deposit
A mid-sized crypto exchange receives a large deposit from a wallet that has never transacted with the exchange before. The compliance team runs the wallet through their AML screening tool and receives a high-risk alert. The wallet has indirect exposure to a known ransomware payment address through two intermediate wallet hops.
Using transaction tracing, the compliance team maps the full path from the ransomware wallet to the depositing wallet. They determine that the depositing wallet received funds that are two degrees of separation from ransomware proceeds, with no direct contact with any sanctioned address. However, the risk score is sufficient to trigger a manual review and a temporary hold on the deposit pending additional verification.
The team files a suspicious activity report with the relevant financial intelligence unit, documents the on-chain evidence trail, and requests supplementary KYC documentation from the depositing customer. The customer provides documentation that is inconsistent with the transaction profile and volume. Consequently, the relationship is terminated, the hold is maintained, and the on-chain evidence package is preserved for any follow-on investigation.
Without blockchain forensics, this suspicious deposit would have cleared unnoticed. With it, the exchange protected itself from regulatory exposure, contributed intelligence to broader law enforcement efforts, and demonstrated the kind of operational AML effectiveness that regulators expect to see.
Scenario 2: Post-Exploit Investigation on a DeFi Protocol
A DeFi lending protocol is drained of eight million dollars through a price oracle manipulation attack. Within minutes of the exploit completing, the attacker begins moving funds across intermediate wallets. The protocol’s security team engages a forensics provider immediately.
Using on-chain analysis, the investigation team traces the stolen funds across seven intermediate wallets, identifies a cross-chain bridge used to move assets from Ethereum to Arbitrum, and tracks the funds to a specific exchange deposit address on the destination chain. The entire trace is completed and communicated to the exchange within 45 minutes of the exploit.
The exchange freezes the deposit. Approximately 2.3 million dollars is recovered before the attacker can complete the withdrawal. The remaining funds had already been moved, but the full on-chain transaction trail provides sufficient evidence for law enforcement to initiate a formal investigation.
This scenario illustrates two principles clearly. Speed matters enormously in post-exploit blockchain investigation. And the quality of the forensic trail built in real time directly determines how much can ultimately be recovered. Organizations that have forensic tooling already integrated into their incident response workflows respond faster and recover more.
Scenario 3: Pre-Integration Due Diligence for a Web3 Partnership
A Web3 startup is evaluating a significant partnership with a new liquidity provider. Before completing the integration and moving any capital, the CTO requests on-chain due diligence on the provider’s primary wallets and deployer addresses.
The analysis reveals that several wallets associated with the provider have historical interactions with addresses flagged in connection with a previous DeFi exit scam from 18 months earlier. The connections are not direct, but the behavioral pattern is consistent with a team that previously operated a fraudulent project under different branding, reused infrastructure between projects, and reactivated dormant wallets for the new initiative.
The startup declines the partnership based on the on-chain findings. Three months later, the liquidity provider executes a rug pull on a different protocol, draining approximately six million dollars from liquidity providers who had not conducted similar due diligence.
This scenario demonstrates clearly that blockchain forensics is not only a reactive discipline. Used proactively, on-chain analysis is a powerful tool for due diligence, risk management, and building genuine trust in an ecosystem where traditional reputation verification often fails.
The Future of Blockchain Forensics: What Comes Next
Several technological and regulatory developments will shape blockchain forensics significantly over the next few years. Organizations that understand these trends will be better prepared to adapt their capabilities before the environment shifts beneath them.
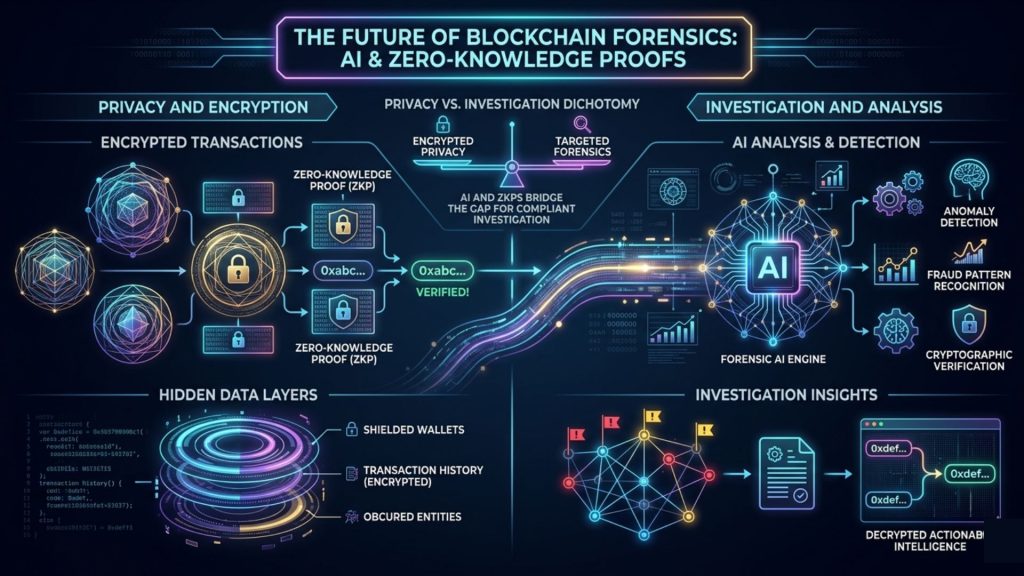
Zero-Knowledge Proofs and the Privacy Challenge
Privacy-enhancing technologies built on zero-knowledge proofs present genuine and growing challenges to traditional blockchain forensics methods. When transaction amounts and addresses are cryptographically hidden, transaction graph analysis loses its primary input data. ZK-based systems like those used in Zcash or emerging zkSync privacy features are becoming more capable, and their adoption is likely to increase.
However, the forensic community is not standing still. Research into timing analysis, behavioral fingerprinting, and side-channel analysis of ZK systems is ongoing and producing results. Furthermore, regulatory pressure on privacy-preserving assets has already led major exchanges to delist coins like Monero, effectively reducing their liquidity and therefore their practical utility for large-scale laundering. The long-term dynamic between privacy technology and forensic capability will be one of the defining tensions in blockchain security over the next decade.
AI-Augmented On-Chain Analysis
Machine learning is already transforming blockchain forensics at the data processing layer. The next phase involves AI systems capable of not just flagging suspicious patterns but generating investigation narratives, suggesting follow-up analytical queries, and synthesizing on-chain and off-chain intelligence automatically. This will dramatically lower the cost and increase the speed of blockchain investigation, making forensic-grade analysis accessible to a much broader range of organizations. Moreover, AI augmentation will shift analyst time from data processing toward interpretation and decision-making, which is where experienced human judgment adds the most value.
Regulatory Technology and Forensics Convergence
The convergence of regulatory technology and blockchain forensics is accelerating. Organizations will increasingly need forensics capabilities that are natively integrated with their compliance reporting pipelines rather than siloed as separate investigation tools. Forensic output needs to flow directly into suspicious activity report filing systems, sanctions screening databases, and risk scoring engines without manual re-entry or format conversion.
SecureTrace’s positioning within SecureDApp’s broader security ecosystem reflects this direction. Forensic investigation capability that connects to the wider organizational security and compliance stack, rather than operating as a standalone point solution, is increasingly what mature organizations need and what regulators expect to see.
Conclusion: Blockchain Forensics Is Now a Core Organizational Capability
Blockchain forensics began as a specialized tool for law enforcement agencies investigating crypto-related crime. It has become a core organizational capability for any team operating seriously in the digital asset space. The distinction matters because it changes where in the organizational hierarchy this capability needs to sit and who is ultimately responsible for it.
For CTOs, the message is direct: your technical infrastructure needs to include the ability to trace, investigate, and document on-chain activity. This is simultaneously a security function, a compliance function, and increasingly a business risk function. Furthermore, the two cannot be separated, because a single unscreened transaction can trigger both a security incident and a regulatory enforcement action at the same time.
For CISOs, blockchain forensics changes your incident response posture fundamentally. When an exploit occurs, the first 60 minutes of on-chain investigation can determine whether stolen funds are recovered or lost permanently. You need the tooling, the process, and ideally the third-party relationships in place before the incident happens, not after it.
For Web3 founders, blockchain forensics is increasingly part of your trust infrastructure. Institutional investors, enterprise partners, and regulators will ask whether your protocol operates in a demonstrably clean, compliant on-chain environment. The ability to answer yes with on-chain evidence, not just a written policy, is becoming a genuine market differentiator.
SecureTrace by SecureDApp provides the transaction tracing and investigation support infrastructure to make these capabilities operational across the spectrum of Web3 organizations. As on-chain activity grows in both volume and complexity, the organizations that invest in blockchain forensics today will be the ones best positioned to navigate the investigations, compliance obligations, and trust requirements of tomorrow.
The blockchain is transparent. The question has never been whether the evidence exists. The question is whether your organization has the capability to read it clearly, quickly, and defensibly.
Frequently Asked Questions About Blockchain Forensics
1. What is blockchain forensics?
Blockchain forensics is the investigation and analysis of on-chain data to trace cryptocurrency transactions, identify illicit activity, support legal proceedings, and enforce AML compliance. It combines transaction tracing, cluster analysis, behavioral pattern recognition, and cross-chain tracking to reconstruct how funds moved and who controlled the wallets involved.
2. How does transaction tracing work in a blockchain investigation?
Transaction tracing maps the path of funds from a source wallet through intermediate addresses to a final destination. Investigators follow transaction inputs and outputs across the public blockchain ledger, building a graph of wallet connections and fund movements. This graph forms the evidentiary foundation for both legal proceedings and compliance reporting.
3. Is blockchain really traceable if it is pseudonymous?
Yes. Blockchain is pseudonymous, not anonymous. Every transaction is permanently and publicly recorded. With clustering techniques, labeled address databases, and behavioral analysis, forensic investigators can often de-anonymize pseudonymous wallets with a high degree of confidence. The transparency of the ledger is precisely what makes blockchain forensics effective.
4. What is on-chain analysis and how does it differ from blockchain forensics?
On-chain analysis refers broadly to extracting and interpreting data recorded on a blockchain. Blockchain forensics is a specific subset focused on investigation, evidence gathering, and compliance. All blockchain forensics uses on-chain analysis, but not all on-chain analysis is forensic. General market analytics, for instance, also relies on on-chain data without any investigative intent.
5. What are the main AML obligations for crypto organizations?
Key AML crypto obligations include KYC procedures, Know Your Transaction monitoring, sanctions screening of wallet addresses, suspicious transaction reporting, Travel Rule compliance for fund transfers, and record-keeping requirements. Specific requirements vary by jurisdiction but converge around FATF standards globally.
6. What is the FATF Travel Rule and how does it apply to crypto?
The FATF Travel Rule requires virtual asset service providers to transmit sender and recipient information alongside cryptocurrency transactions above defined thresholds. Implementing this in a blockchain context requires counterparty identification infrastructure and blockchain forensics tools to assess transaction risk before any data is transmitted.
7. Can mixers defeat blockchain forensics entirely?
Not entirely. While mixers significantly complicate transaction tracing, forensic techniques including amount correlation, timing analysis, and pattern recognition can de-anonymize mixer usage in specific scenarios. Additionally, using sanctioned services like Tornado Cash carries direct legal risk, which has reduced their adoption among actors seeking regulatory cover.
8. What is crypto fraud detection and what does it cover?
Crypto fraud detection encompasses the identification of exploits, rug pulls, wash trading, market manipulation, NFT fraud, and other illicit on-chain activities. It combines real-time transaction monitoring, smart contract behavior analysis, wallet screening, and anomaly detection to surface suspicious activity as early as possible in the attack lifecycle.
9. How does cross-chain investigation work in blockchain forensics?
Cross-chain investigation tracks funds as they move through bridges between different blockchain networks. Investigators reconcile deposit and withdrawal amounts across chains, apply network-specific tracing methods, and use multi-chain labeled address databases to maintain the fund trail across network boundaries without losing attribution continuity.
10. What is cluster analysis in blockchain investigation?
Cluster analysis groups wallet addresses that are likely controlled by the same entity. The Common Input Ownership Heuristic groups wallets that co-sign transaction inputs. Once a cluster is identified, attributing any single address in the cluster to a known entity can de-anonymize all associated addresses simultaneously, making it one of the most powerful techniques in crypto forensics.
11. What should Web3 founders do proactively for blockchain compliance?
Web3 founders should implement wallet screening for counterparties, integrate on-chain monitoring into protocol operations, document responses to suspicious activity, understand their regulatory classification under applicable VASP definitions, and build forensic capability into incident response planning before incidents occur rather than scrambling to assemble it after the fact.
12. How is DeFi forensics different from standard blockchain investigation?
DeFi forensics requires understanding smart contract logic, protocol architecture, and complex multi-step transaction patterns specific to each protocol. A single DeFi attack can span dozens of smart contract interactions across multiple protocols in one block. This level of complexity demands deeper technical expertise than tracing simple wallet-to-wallet transfers across a single chain.
13. What evidence does blockchain forensics produce for legal proceedings?
Blockchain forensics produces transaction histories, wallet cluster maps, fund flow diagrams, risk assessments, and investigation reports that document methodology and findings. For legal proceedings, maintaining chain of custody, documenting data sources, and applying reproducible methodology are essential for producing evidence that courts and regulators will accept without challenge.
14. What is SecureTrace and how does it support blockchain forensics?
SecureTrace is SecureDApp’s purpose-built blockchain forensics and transaction tracing product. It enables organizations to trace on-chain fund flows, screen wallet addresses against sanctions and illicit activity databases, identify clusters associated with known threat actors, and generate investigation-quality reports for legal and compliance use.
15. How is blockchain forensics evolving with technologies like ZK proofs?
Zero-knowledge proof systems that hide transaction data present growing challenges to traditional transaction tracing. However, forensic research into timing analysis and behavioral fingerprinting continues to develop applicable techniques for these environments. Simultaneously, regulatory pressure is reducing the practical liquidity of the most privacy-preserving assets, limiting their utility for large-scale laundering in regulated markets.



