On-Chain Transaction Monitoring vs Off-Chain Security Measures: Which…
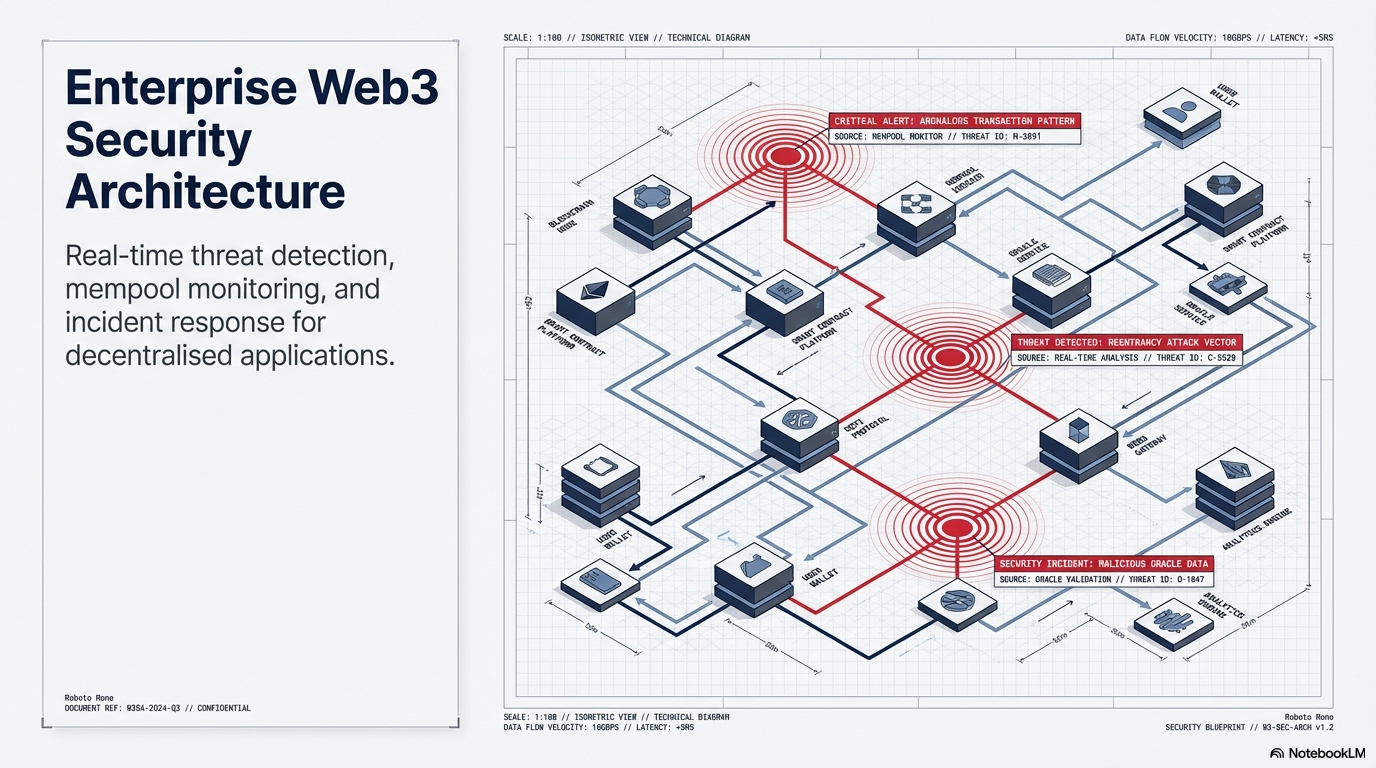
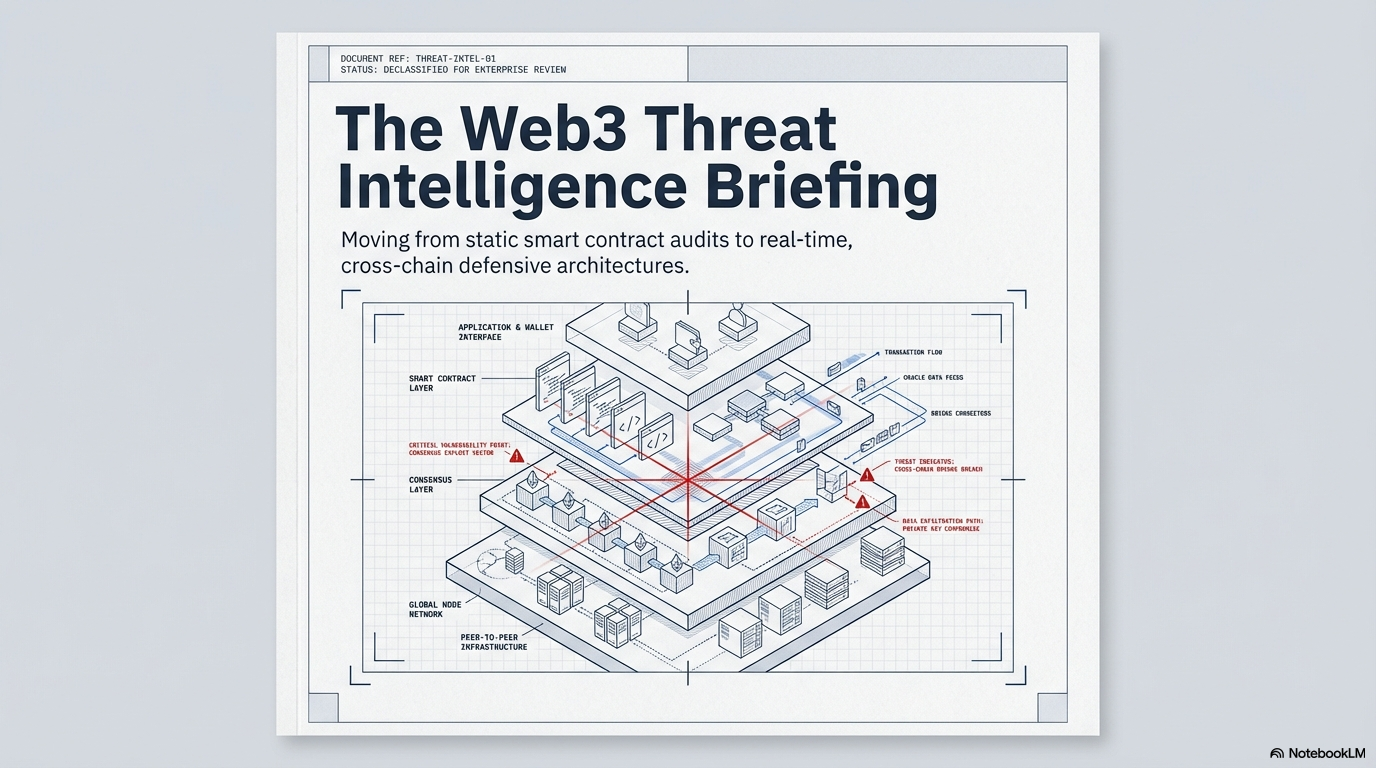
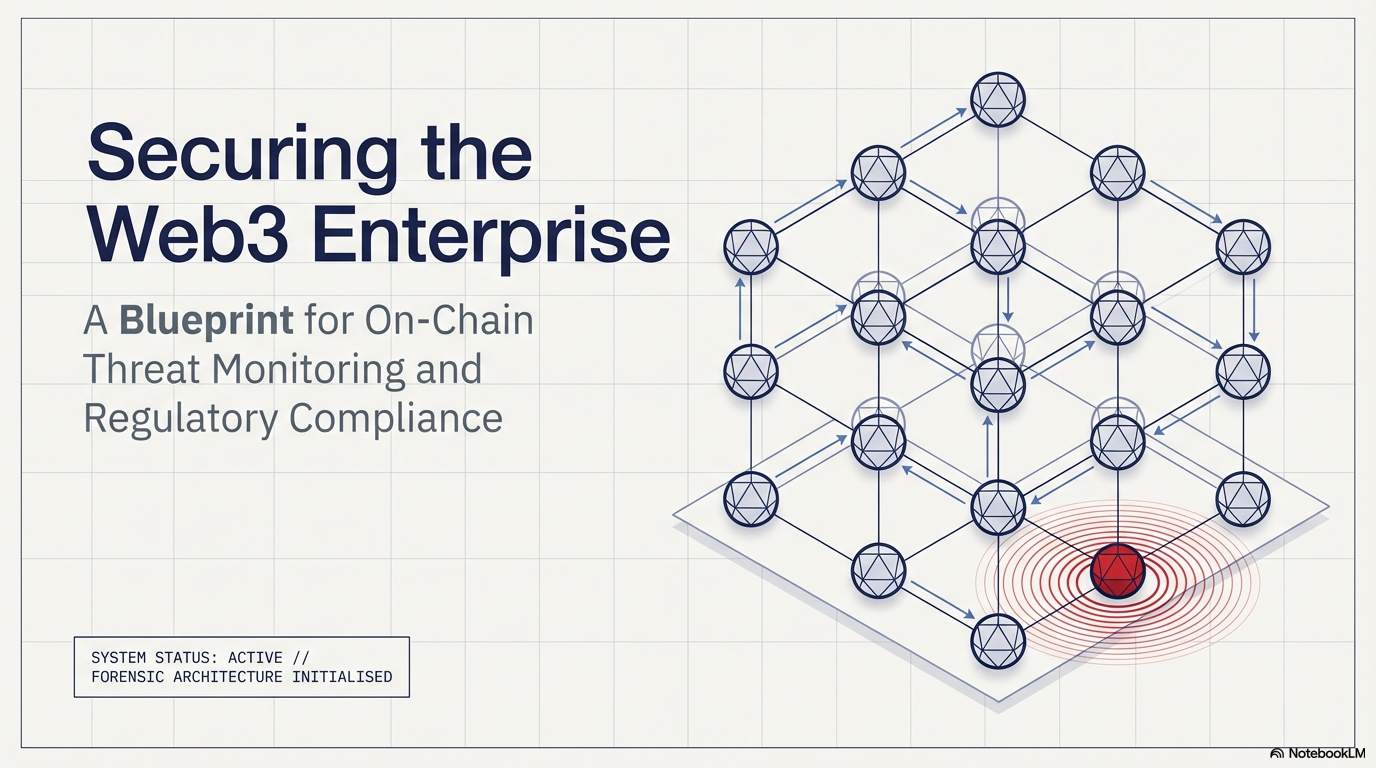
Introduction: The Question Every Protocol Founder Gets Wrong Most Web3 teams pick a security approach the same way they pick a cloud provider. They go with what they already know. That instinct is expensive. In 2024 alone, over $2.3 billion…